
In today's rapidly changing healthcare landscape, the importance of managing sensitive patient data and ensuring regulatory compliance cannot be overstated. With the stakes higher than ever, local IT support companies such as Cyber Solutions Inc. provide tailored services that not only confront the unique challenges faced by medical facilities but also bolster operational efficiency and enhance cybersecurity measures.
As healthcare organizations increasingly contend with rising cyber threats and stringent regulations, one pivotal question emerges: how can partnering with a local IT provider fundamentally transform their IT support approach and ultimately safeguard patient care?
This partnership is not merely beneficial; it is essential for navigating the complexities of modern healthcare security.
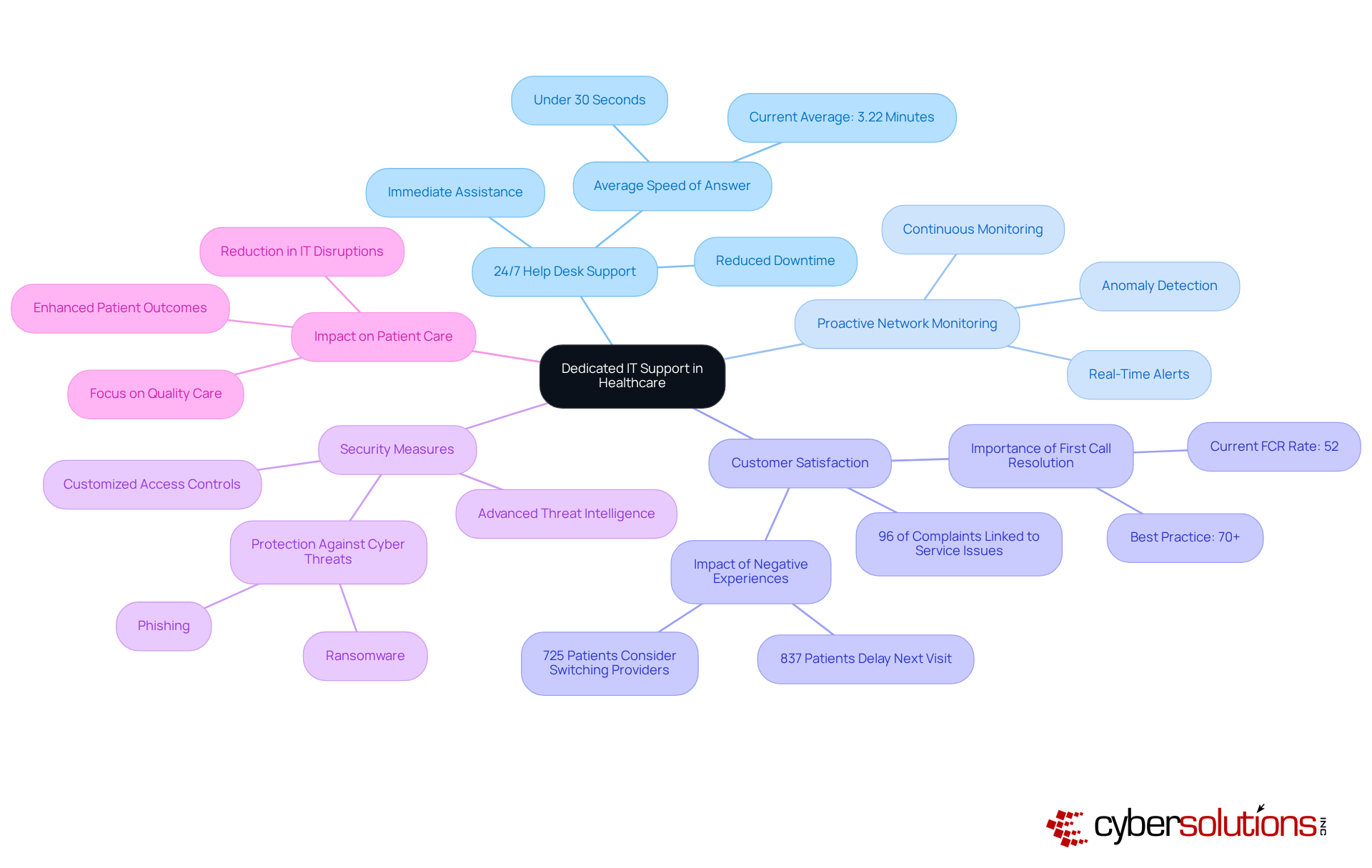
In today's digital landscape, the importance of IT support cannot be overstated. Cyber Solutions Inc. excels in providing personalized IT assistance tailored to the unique requirements of diverse sectors, particularly by collaborating with a partner in the medical field. Their comprehensive offerings—24/7 help desk support, network management, and data backup solutions—are crucial for maintaining operational efficiency and security. With 92% of medical providers reporting at least one cyberattack in the past year, the need for robust cybersecurity measures has never been more critical.
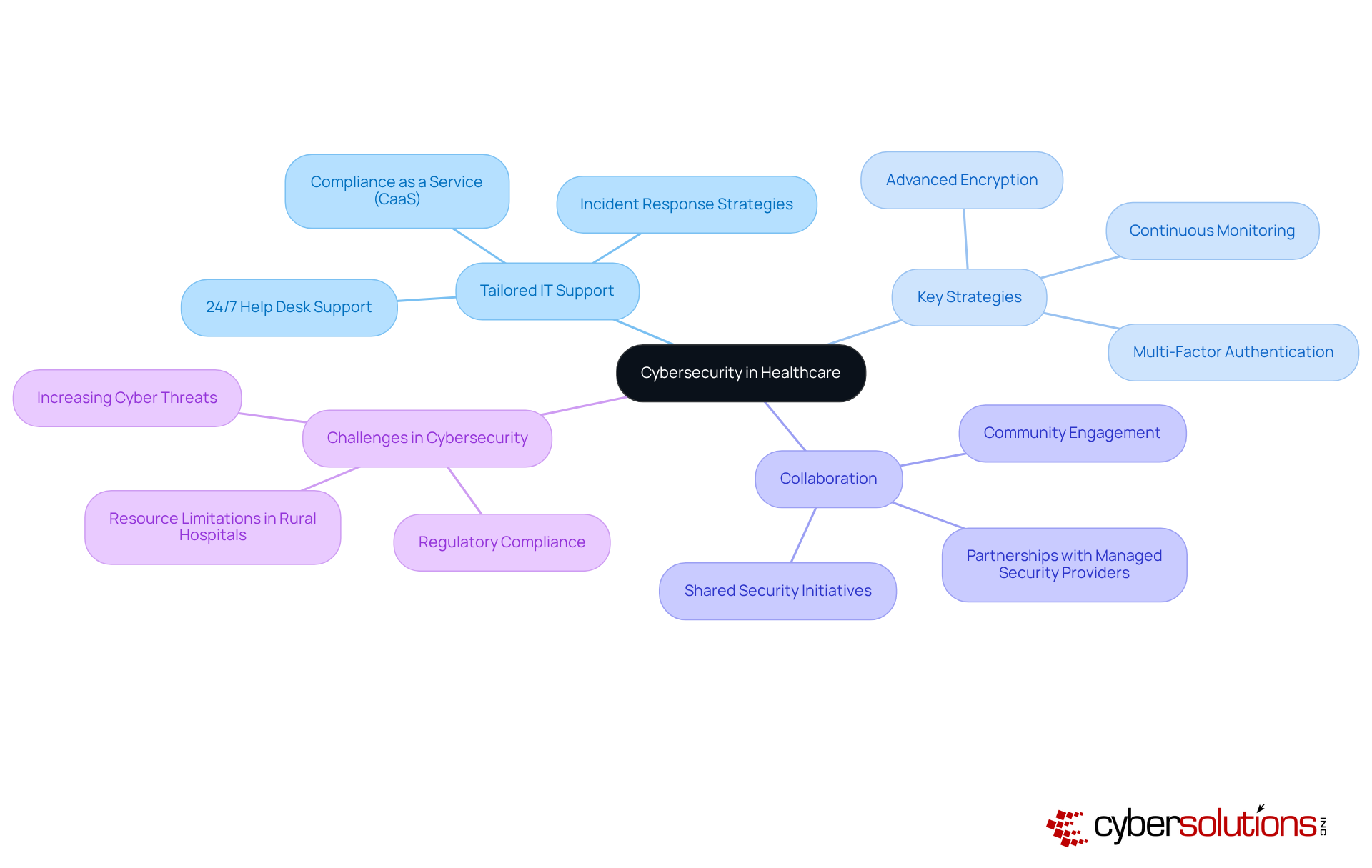
Cyber Solutions understands the distinct challenges that medical service providers face, including strict regulatory requirements and the necessity for continuous service availability. By implementing strategies such as advanced encryption, multi-factor authentication, and continuous monitoring, Cyber Solutions enhances security and compliance, positioning itself as a trusted partner in the healthcare sector. Their solutions incorporate strong protocols to ensure entities meet the highest standards of data protection. Proactive risk management identifies and addresses vulnerabilities to protect health information (PHI), while customized reporting and audit assistance prepare entities for audits.
As Jason Griffin, Managing Director of Digital Health/IT Strategy and Cyber Practice, emphasizes, 'Collaboration is key to strengthening rural hospitals’ cybersecurity defenses because no single entity can tackle these challenges alone.' This cooperative approach not only mitigates risks but also enhances operational efficiency, allowing medical entities to focus on delivering quality patient care. Additionally, as Cam Sivesind notes, tailored solutions are essential for medical institutions to navigate compliance complexities effectively.
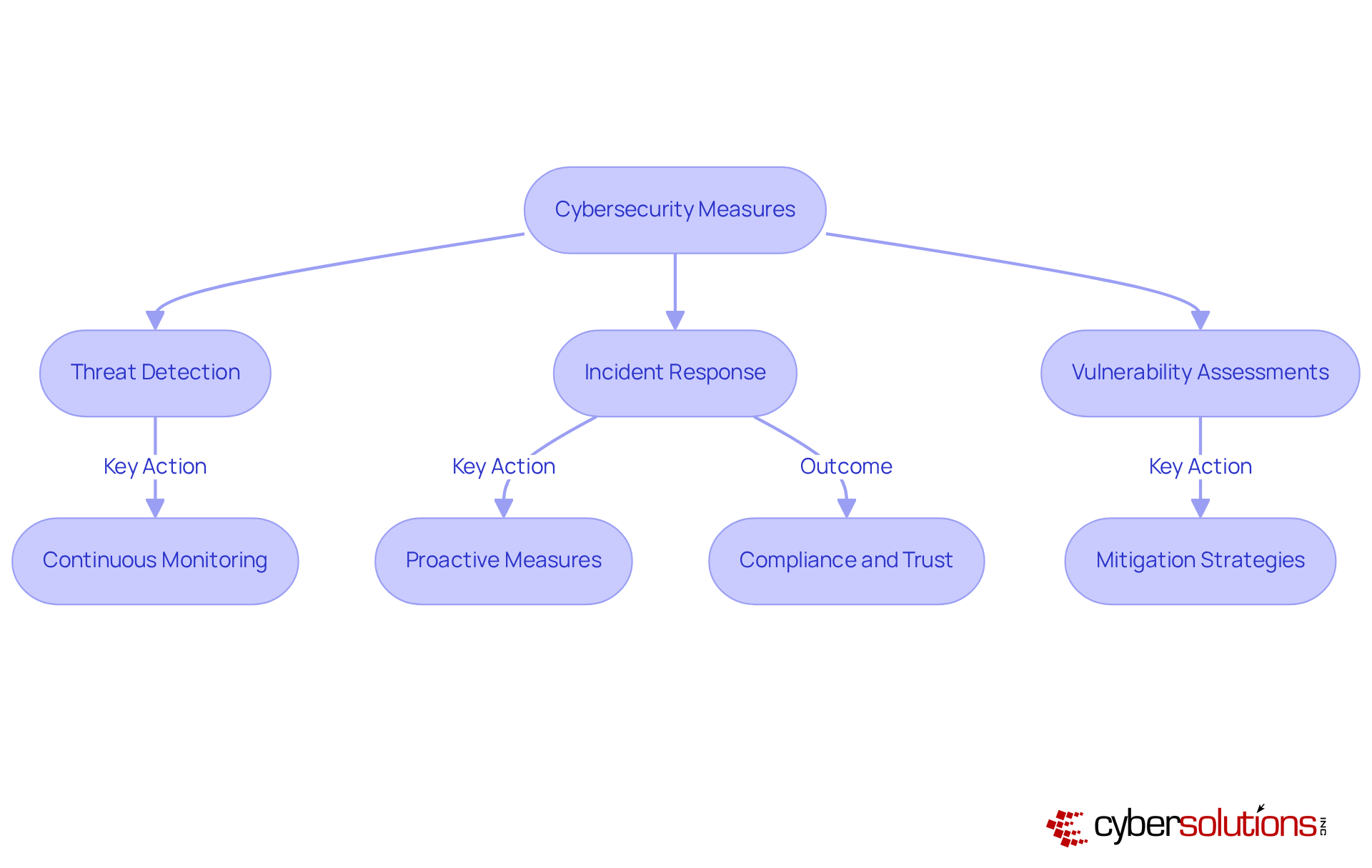
Key strategies for enhancing cybersecurity in healthcare include:
By prioritizing these measures, healthcare organizations can bolster their defenses against the ever-evolving landscape of cyber threats.
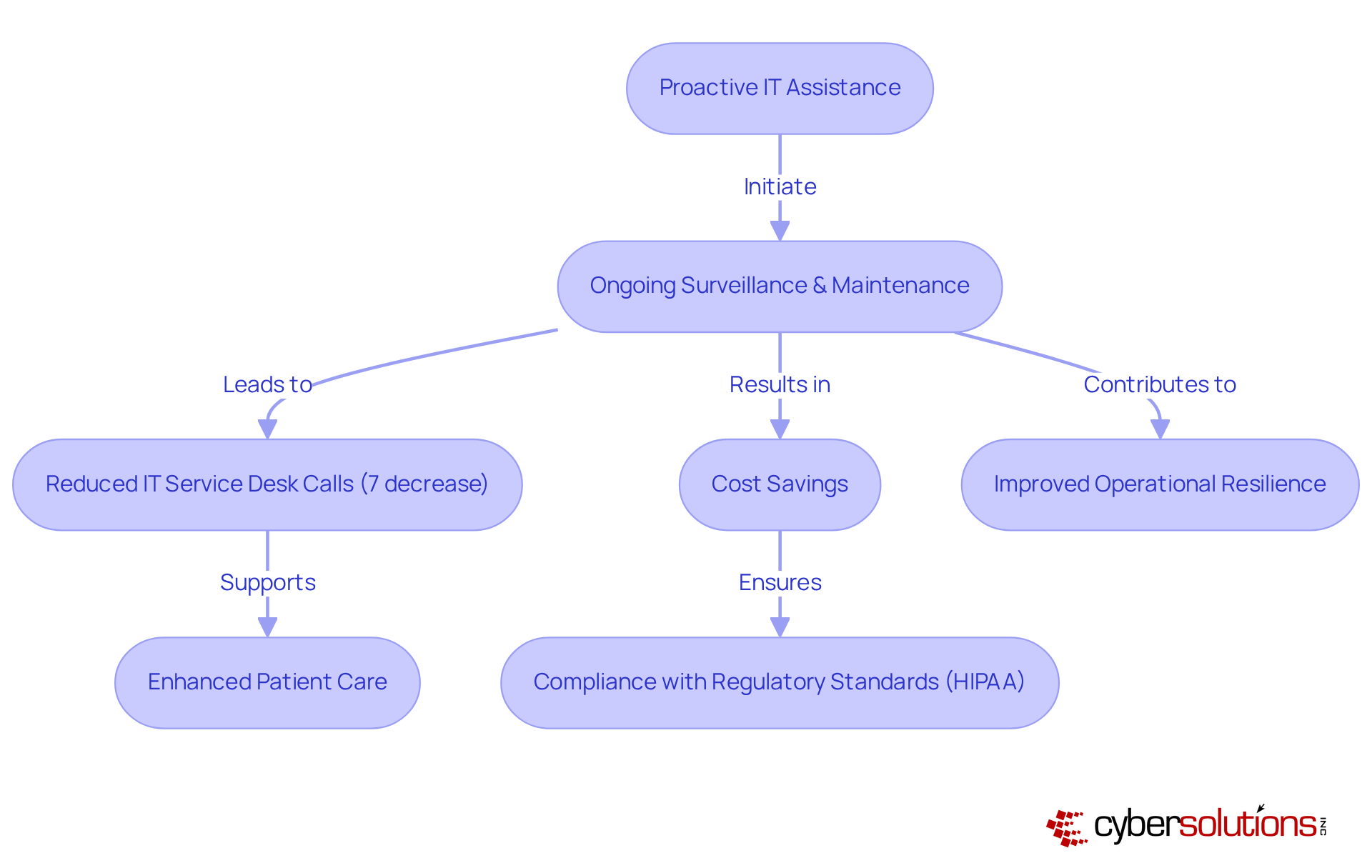
Proactive support is essential for the healthcare sector, encompassing ongoing surveillance and maintenance of systems that empower medical entities to identify and resolve potential issues before they escalate. This strategy is vital for patient safety and ensuring that critical systems remain operational. Notably, medical institutions experience an average 7% monthly decrease in IT service desk calls when implementing proactive measures, leading to significant cost savings and improved efficiency. Cyber Solutions employs skilled technicians and conducts regular system audits to detect vulnerabilities early, allowing healthcare providers to concentrate on patient care without the disruptions caused by IT failures.
By adopting proactive endpoint management, organizations can utilize real-time device data to make informed decisions regarding support and hardware refreshes, ultimately bolstering their operational capabilities. The Kelsey-Seybold Clinic exemplifies this transformation, having revamped its IT operations to enhance experiences for both staff and patients through proactive monitoring. Such strategies not only avert costly downtime but also foster a more reliable and efficient delivery system for health services. Regular assessments and comprehensive risk analyses are crucial for maintaining system integrity, further underscoring the importance of proactive support in today's medical landscape.
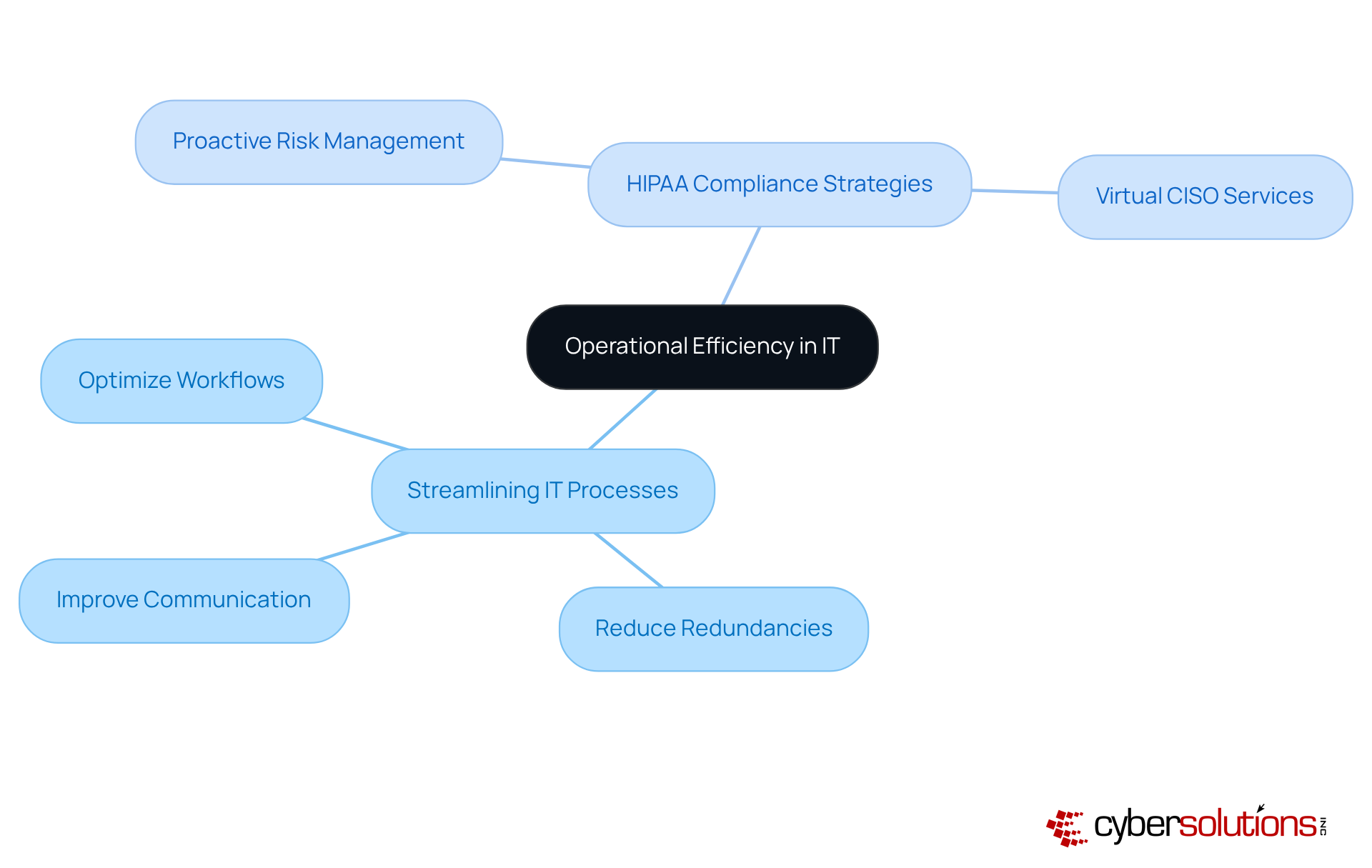
Incorporating robust cybersecurity measures—such as tailored remediation strategies, professional guidance, and fractional or virtual CISO services—ensures that organizations remain compliant and audit-ready, effectively safeguarding patient health information.
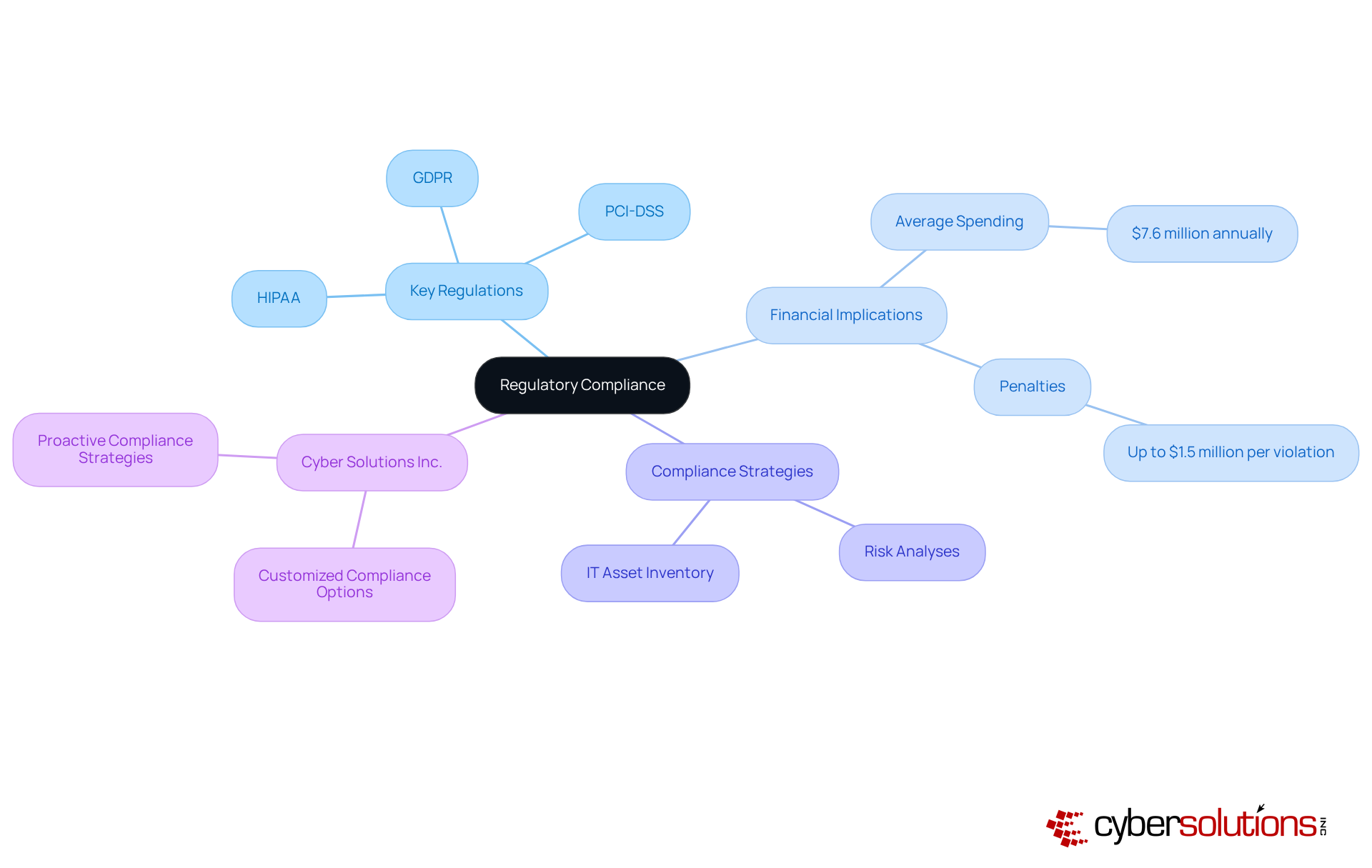
Navigating the intricate landscape of medical regulations presents significant challenges for many organizations. The importance of cybersecurity in healthcare cannot be overstated; it is crucial for medical providers to effectively meet stringent requirements such as data protection. With the average-sized community hospital spending nearly $7.6 million annually on compliance activities, the costs are substantial. Current penalties for HIPAA violations can reach up to $1.5 million per violation category per year, underscoring the critical need for robust compliance measures.
Organizations that successfully navigate these regulations often leverage expert guidance and technology solutions. For instance, medical organizations that implement and maintain an inventory of IT assets handling protected health information (PHI) can significantly reduce risks. As compliance experts note, regulatory compliance is not merely a back-office task; it has become a strategic priority.
Cyber Solutions Inc. stands out by providing customized options that not only assist clients in avoiding penalties but also enhance their reputation through a proven dedication to quality service. By incorporating technology solutions and ongoing oversight, the company enables medical providers to concentrate on delivering quality care while confidently managing the intricacies of regulatory obligations.
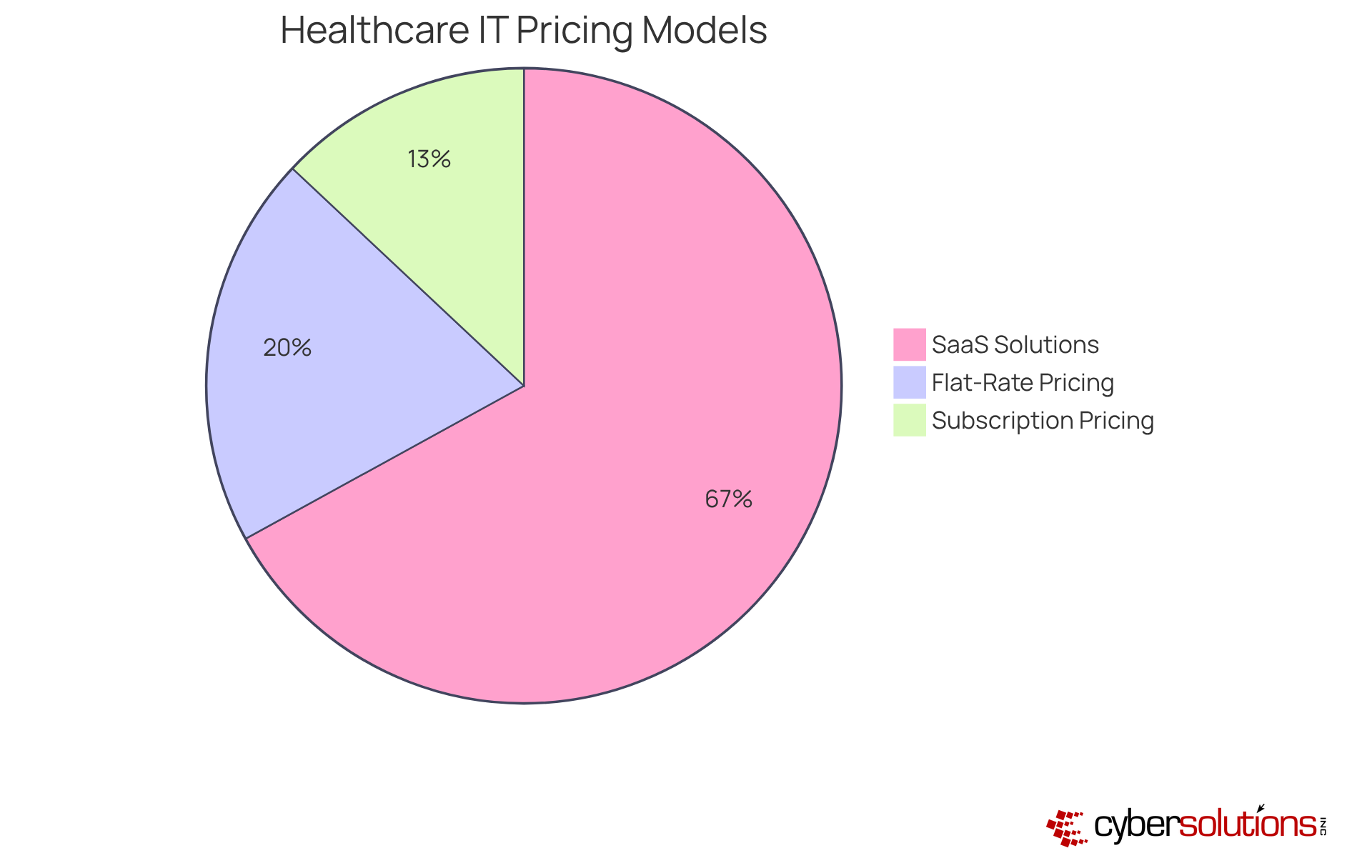
In today's healthcare landscape, effective IT support is crucial for medical entities striving to enhance care and operational efficiency. Cyber Solutions Inc. offers solutions that empower these organizations to operate with confidence. By implementing transparent flat-rate pricing structures, clients can sidestep unexpected costs, enabling better financial planning. This is essential for medical providers, who often operate within tight budgets and must ensure that every dollar spent directly contributes to improved patient outcomes.
For instance, SaaS solutions allow hospitals to access technology without the burden of large upfront costs. This approach effectively converts capital expenditures into manageable monthly expenses, fostering a more sustainable financial model. Furthermore, statistics reveal that 67% of medical institutions prioritize SaaS solutions in their purchasing decisions, recognizing the flexibility and scalability these models provide. By adopting predictable pricing strategies, medical providers can streamline their budgeting processes and invest in technologies that enhance both client outcomes and operational workflows.
In light of the unique challenges faced by CFOs in the healthcare sector, it is imperative to consider the benefits of cost-effective IT solutions. Cyber Solutions Inc. stands ready to assist medical entities in overcoming financial hurdles, ensuring that their IT investments yield maximum returns while safeguarding the quality of care.
In an era where cyber threats are increasingly sophisticated, the importance of cybersecurity cannot be overstated. Cyber Solutions Inc. stands at the forefront, offering tailored cybersecurity strategies designed specifically for medical facilities. Their comprehensive suite of services includes:
All meticulously crafted to protect sensitive patient data from breaches. Alarmingly, medical institutions are facing a staggering 32 percent increase in cyberattacks in 2025, with potential costs soaring into the hundreds of millions of dollars. By leveraging advanced technologies, to uphold security while ensuring operational integrity.
Effective threat detection is not just beneficial; it is essential. Organizations that adopt proactive measures. Cybersecurity experts emphasize that a robust strategy is vital for mitigating the impact of attacks, allowing medical organizations to recover swiftly and maintain continuity of care. With the right strategies in place, healthcare institutions can adeptly navigate the complexities of modern threats and regulations.
In today's healthcare landscape, cybersecurity is paramount. Cyber Solutions Inc. provides crucial tailored support specifically for healthcare providers, ensuring that prompt assistance is always within reach. This dedicated service is staffed by experienced professionals who are adept at swiftly resolving technical issues, significantly reducing downtime. In environments where immediate responses can directly influence patient outcomes, such support is not just beneficial but essential.
Moreover, our comprehensive services proactively detect anomalies and potential vulnerabilities. This proactive approach allows for instant alerts and real-time insights, enabling swift action to mitigate risks. Continuous-functioning healthcare call centers can manage peak demands more efficiently, with research indicating that organizations with a dedicated team providing 24/7 IT support experience enhanced efficiency and operational effectiveness. Leading organizations strive for an average response time, a metric vital for maintaining high service quality.
As noted by industry specialists, 'reliable support is the cornerstone of any IT help desk,' underscoring the importance of reliable support in fostering positive user experiences. Additionally, a staggering 96% of patient complaints in medical services are linked to customer service issues, further highlighting the critical role of effective support. By enabling medical providers to focus on delivering quality care without the distraction of technical problems, Cyber Solutions Inc., a local IT support company, establishes itself as an indispensable partner in the medical landscape. Equipped with advanced security measures, we safeguard against ransomware, phishing, and other malware attacks.
Our services also include customized access controls and restrictions, ensuring that only authorized users can access sensitive information, which is essential for maintaining security in medical settings. In a world where cybersecurity threats are ever-evolving, can you afford to compromise on IT support?
In today's rapidly evolving landscape of cybersecurity threats, choosing a partner like Cyber Solutions is crucial for organizations in the medical field. Such providers offer specialized expertise that aligns with the healthcare industry, ensuring compliance and security. A local IT support company has an in-depth understanding of regional regulations, market dynamics, and community-specific challenges, which enables it to deliver solutions that significantly enhance operational efficiency.
This localized approach streamlines processes and fosters a culture that adapts to the ever-changing environment of medical care. Medical organizations can particularly benefit from tailored services such as:
These services directly address specific needs, ensuring that healthcare providers remain compliant and secure.
Our CaaS solutions simplify the navigation of complex regulatory landscapes through comprehensive risk assessments, policy development, and ongoing compliance monitoring. Additionally, our services guarantee that in the event of a cyberattack, we can respond quickly, restoring systems and ensuring business continuity.
Statistics reveal that medical facilities utilizing local IT expertise experience improved operational outcomes, notably a reduction in downtime and enhanced patient satisfaction. By selecting a local partner, medical providers can ensure they receive the necessary support to effectively navigate their unique environments.

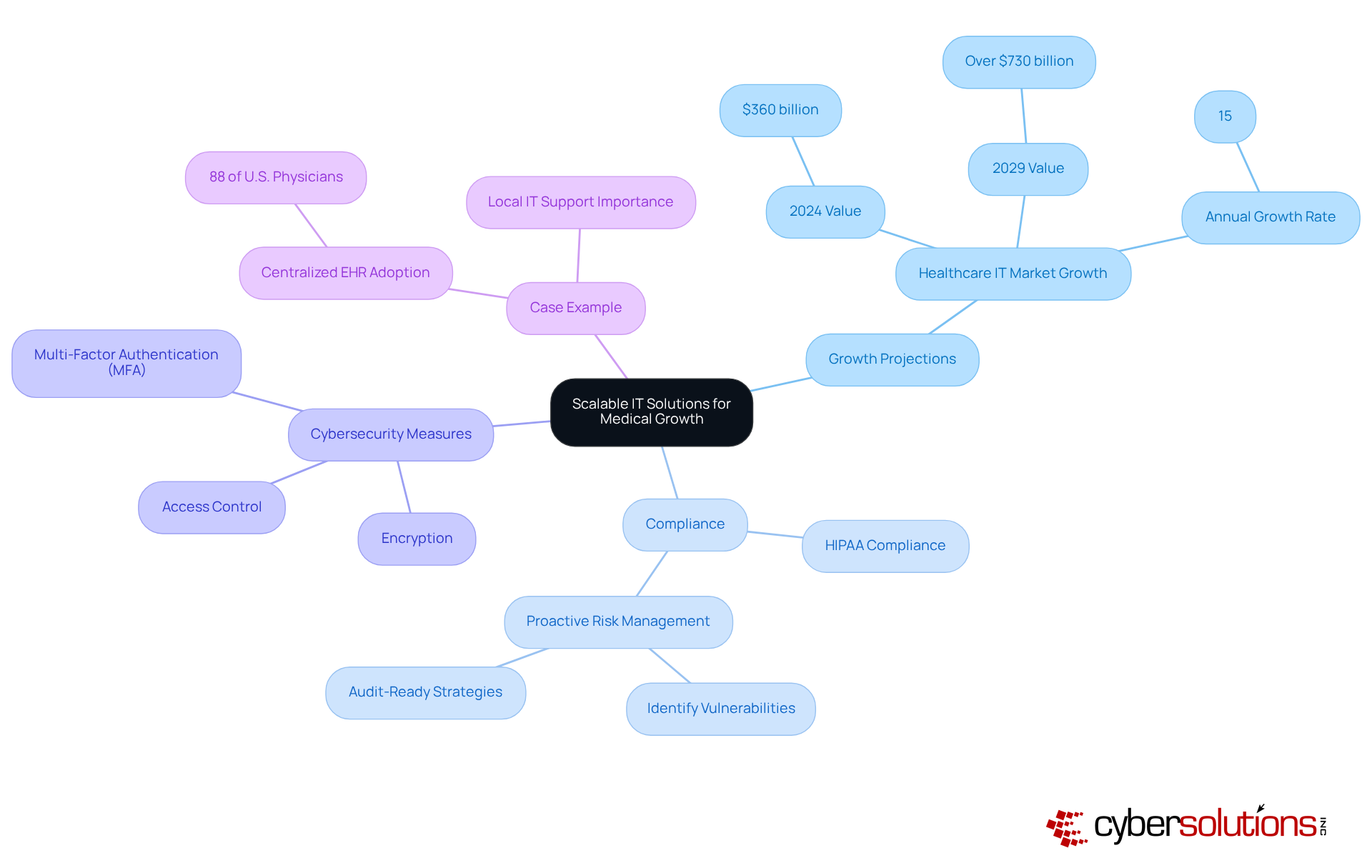
Cyber Solutions Inc. offers solutions that are meticulously crafted to evolve alongside healthcare organizations. As medical service providers expand their offerings, open new locations, or face increased patient volumes, they can work with a local IT support company to customize their IT support to meet these dynamic needs. This adaptability is not merely beneficial; it is essential, especially considering that the IT market for medical services is projected to grow from $360 billion in 2024 to over $730 billion by 2029, with an impressive annual growth rate of 15%. Such growth necessitates IT systems that can seamlessly integrate into existing workflows while enhancing operational efficiency.
In addition to scalability, Cyber Solutions ensures comprehensive security through robust cybersecurity measures. Our proactive risk management strategies are designed to identify and address vulnerabilities, thereby safeguarding patient health information (PHI) and ensuring that organizations remain audit-ready. We implement encryption, multi-factor authentication (MFA), and stringent access control measures to prevent unauthorized access. With expert guidance from our compliance team, we provide strategic oversight to effectively navigate the complexities of compliance.
As a case in point, with 88% of U.S. office-based physicians adopting centralized Electronic Health Records (EHR) systems, the demand for a reliable IT partner becomes increasingly critical. Cyber Solutions ensures that medical providers can maintain high-quality care and patient satisfaction during periods of expansion by collaborating with a dedicated IT team to minimize operational disruptions through effective planning and a Zero Trust strategy. An IT professional emphasizes, "Embracing scalable solutions is essential for maximizing resources without compromising quality or accessibility." By leveraging advanced technologies and fostering collaboration, Cyber Solutions Inc. positions itself as an indispensable partner in navigating the complexities of medical growth. To fully realize your entity's potential, consider implementing these strategies today.
In today's healthcare landscape, operational efficiency is not just beneficial; it is essential for organizations striving to improve patient care while ensuring compliance with HIPAA regulations. Healthcare technologies are ever-evolving, making it crucial for healthcare providers to adopt robust strategies.
Our comprehensive strategies for achieving and maintaining operational efficiency incorporate innovative solutions, including:
This approach safeguards protected health information (PHI) against unauthorized access and breaches. By enhancing operational efficiency and ensuring ongoing compliance, medical providers can focus on what truly matters: patient outcomes.
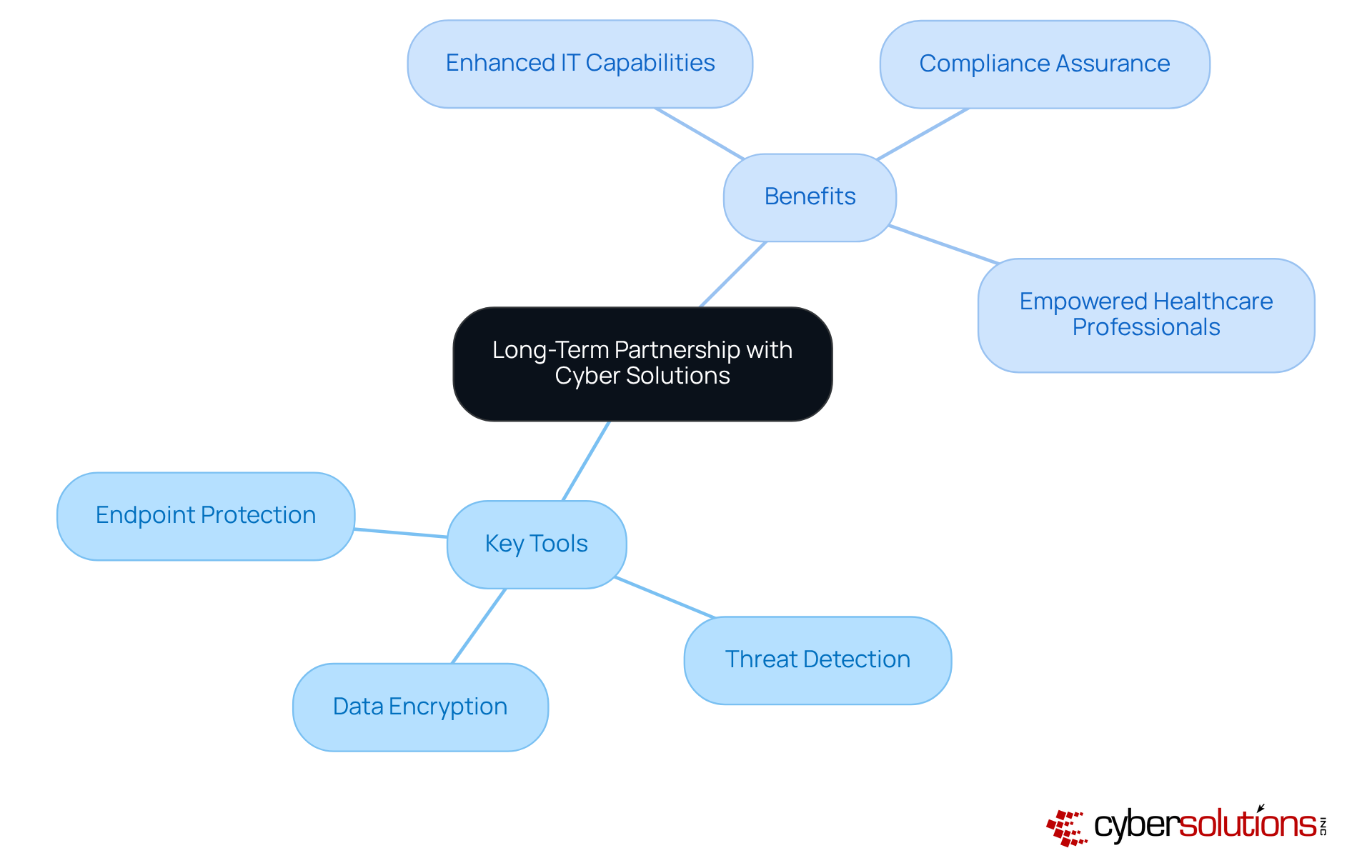
In today's rapidly evolving healthcare landscape, forming a partnership with Cyber Solutions Inc. is essential for medical organizations seeking consistent and reliable IT support that adapts to their changing needs. The unique security and compliance requirements of the medical sector demand specialized IT services. Cyber Solutions Inc. addresses these needs by providing crucial tools such as:
This sustainable relationship not only fosters trust and collaboration but also empowers both parties to work together towards shared objectives.
Cyber Solutions Inc. enables healthcare providers to enhance their operational capabilities. By implementing proactive measures like application allowlisting to prevent unauthorized software execution, organizations can ensure compliance with stringent regulations. This focus on security allows healthcare professionals to dedicate their efforts to delivering high-quality care to their patients.
As cybersecurity threats continue to escalate, it is imperative for healthcare organizations to prioritize their IT infrastructure. With Cyber Solutions, medical institutions can effectively safeguard their systems while maintaining the trust of their patients and stakeholders.
Selecting a local IT support company for healthcare transcends mere convenience; it represents a strategic choice that can profoundly elevate patient care and operational efficiency. Local providers, such as Cyber Solutions Inc., deliver tailored solutions that specifically tackle the unique challenges medical institutions encounter, including stringent compliance requirements and the imperative for robust cybersecurity measures. By harnessing local expertise, healthcare organizations can secure the specialized support essential for navigating the complexities of the healthcare landscape.
This article underscores several compelling arguments for opting for local IT support, notably:
Furthermore, the emphasis on cybersecurity measures highlights the urgent necessity for healthcare providers to protect sensitive patient data from escalating cyber threats. Through the implementation of advanced technologies and the provision of ongoing support, local IT partners empower medical facilities to concentrate on their primary mission: delivering exceptional patient care.
Given the evolving challenges in healthcare IT, the significance of establishing long-term partnerships with local IT support providers cannot be overstated. Such collaborations not only enhance operational capabilities but also foster trust and resilience amid potential disruptions. Healthcare organizations are strongly encouraged to prioritize local IT support as a crucial element of their strategy to enhance efficiency, compliance, and patient satisfaction. Embracing these tailored solutions is vital for navigating the intricacies of today's healthcare environment while safeguarding the future of patient care.
What services does Cyber Solutions Inc. provide for the healthcare sector?
Cyber Solutions Inc. offers tailored IT support including 24/7 help desk support, advanced endpoint protection, and Compliance as a Service (CaaS) to help healthcare organizations maintain operational efficiency and protect sensitive patient data.
Why is cybersecurity particularly important in healthcare?
Cybersecurity is crucial in healthcare because 92% of medical providers reported experiencing at least one cyberattack in the past year, highlighting the need for robust measures to safeguard sensitive patient information and comply with strict regulatory requirements.
What proactive strategies does Cyber Solutions Inc. implement to enhance cybersecurity?
The company employs advanced encryption, multi-factor authentication, and continuous monitoring to enhance security and compliance for healthcare providers.
How does Cyber Solutions Inc. assist organizations in maintaining HIPAA compliance?
Cyber Solutions Inc. provides HIPAA compliance services that include strong cybersecurity measures, proactive risk management to identify vulnerabilities, and customized reporting and audit assistance to prepare entities for audits.
What are the benefits of proactive IT support in healthcare?
Proactive IT support minimizes downtime, ensures critical systems remain operational, and leads to an average 7% monthly decrease in IT service desk calls, resulting in significant cost savings and improved efficiency for medical institutions.
How does proactive endpoint management contribute to healthcare operations?
Proactive endpoint management utilizes real-time device data to make informed decisions regarding support and hardware refreshes, ultimately enhancing operational resilience and improving digital experiences for both staff and patients.
What financial implications do medical organizations face regarding regulatory compliance?
The average-sized community hospital spends nearly $7.6 million annually on compliance activities, and current penalties for HIPAA violations can reach up to $1.5 million per violation category per year.
How does Cyber Solutions Inc. help organizations navigate regulatory compliance?
Cyber Solutions Inc. provides customized options that assist clients in avoiding penalties, enhancing their reputation through a commitment to data security and patient privacy, and incorporating proactive compliance strategies with ongoing oversight.