Introduction
In a world where digital threats loom larger than ever, the quest for reliable cybersecurity firms becomes a critical endeavor for businesses of all sizes. The importance of selecting the right partner cannot be overstated; it not only safeguards sensitive information but also enhances operational resilience.
However, with countless options available, what key factors should businesses consider to ensure they make an informed decision? This guide delves into a systematic approach to assess cybersecurity needs, research local firms, and evaluate their expertise.
Ultimately, it empowers organizations to fortify their defenses against an ever-evolving landscape of cyber threats.
Assess Your Business's Cybersecurity Needs
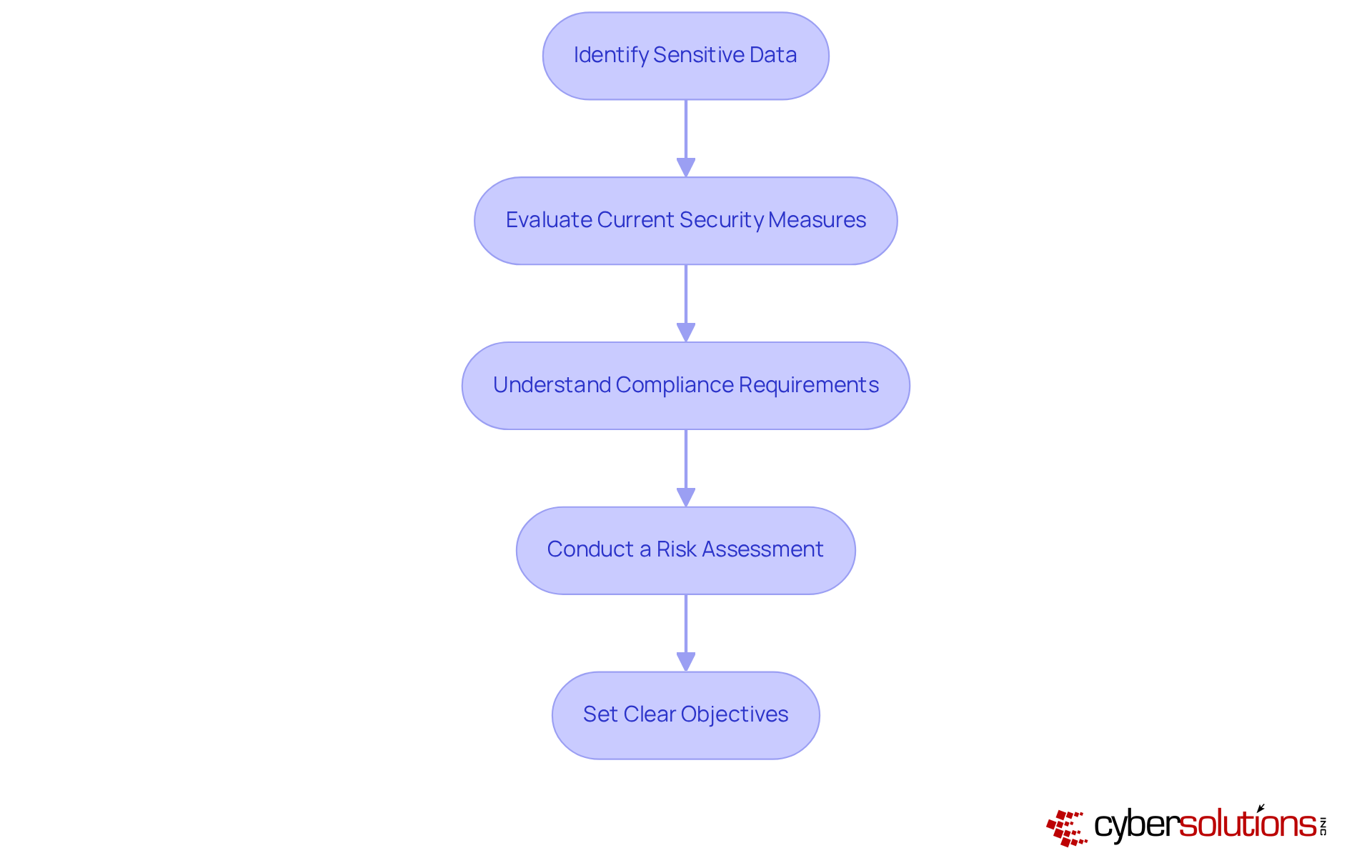
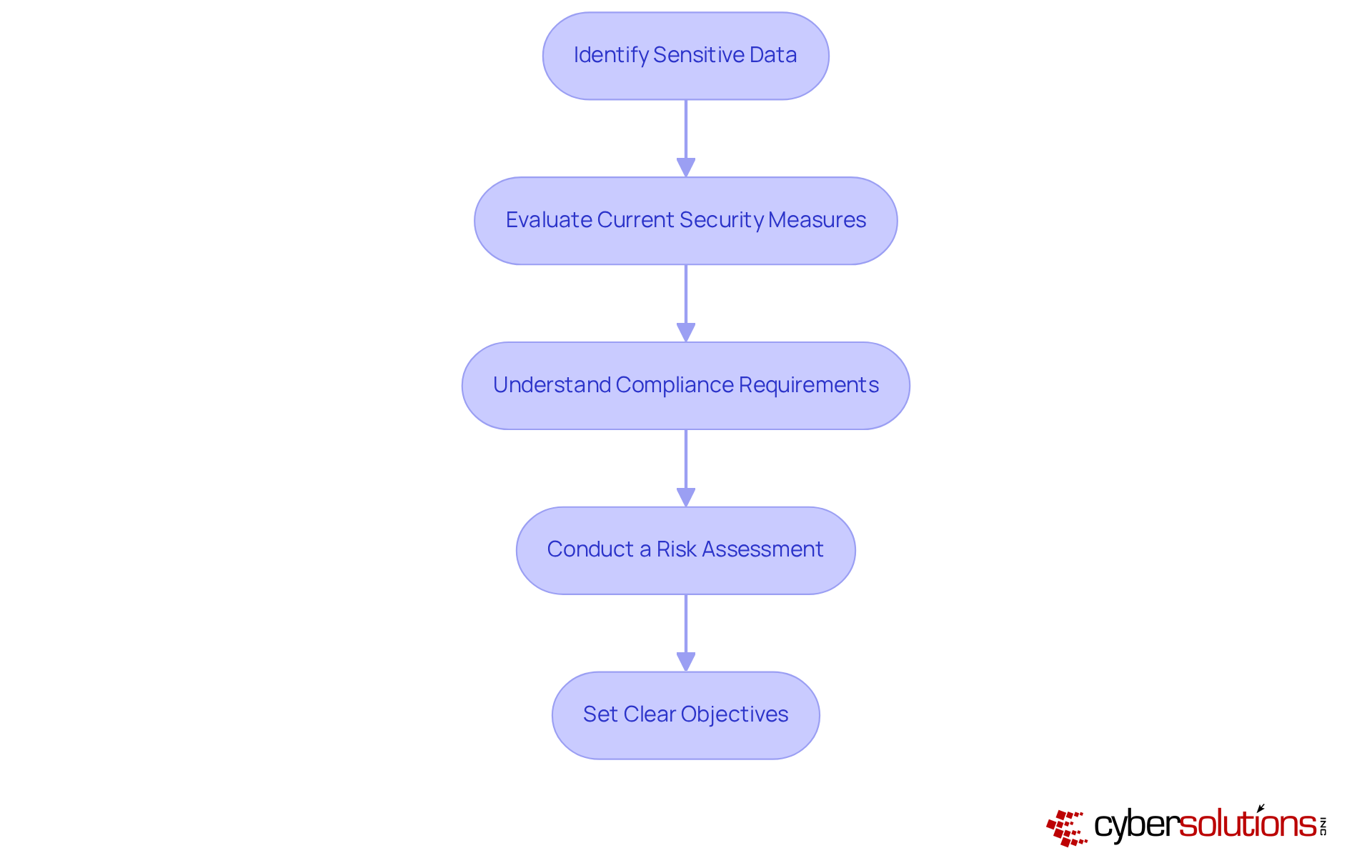
Begin by conducting a thorough evaluation of your business's online security requirements. In today's digital landscape, understanding cybersecurity is paramount for protecting sensitive data. Consider the following steps:
- Identify Critical Data: Determine what data is critical to your operations, such as customer information, financial records, and proprietary data. According to recent surveys, 86% of small and medium-sized enterprises have performed a security needs evaluation, emphasizing the significance of identifying sensitive information.
- Review Security Protocols: Review existing security protocols and identify any gaps or weaknesses. Many businesses find that regular assessments can reveal vulnerabilities before they are exploited, allowing for proactive measures.
- Understand Regulations: Familiarize yourself with industry-specific regulations (e.g., HIPAA for healthcare, PCI-DSS for payment processing) that dictate certain security standards. Compliance is crucial, as non-adherence can lead to significant financial penalties and reputational damage.
- Analyze Threats: Analyze potential threats and vulnerabilities that could impact your business, including cyberattacks, data breaches, and insider threats. Experts stress that frequent risk evaluations enhance action plans, allowing businesses to understand the measures to implement in the case of a breach.
- Set Clear Objectives: Define what you want to achieve with your cybersecurity strategy, such as reducing risk, ensuring compliance, or improving response times. Establishing clear goals will guide your efforts and help measure success.
By completing this assessment, you will gain a clearer understanding of your security environment, which will guide your search for cybersecurity firms.
Research Local Cybersecurity Firms
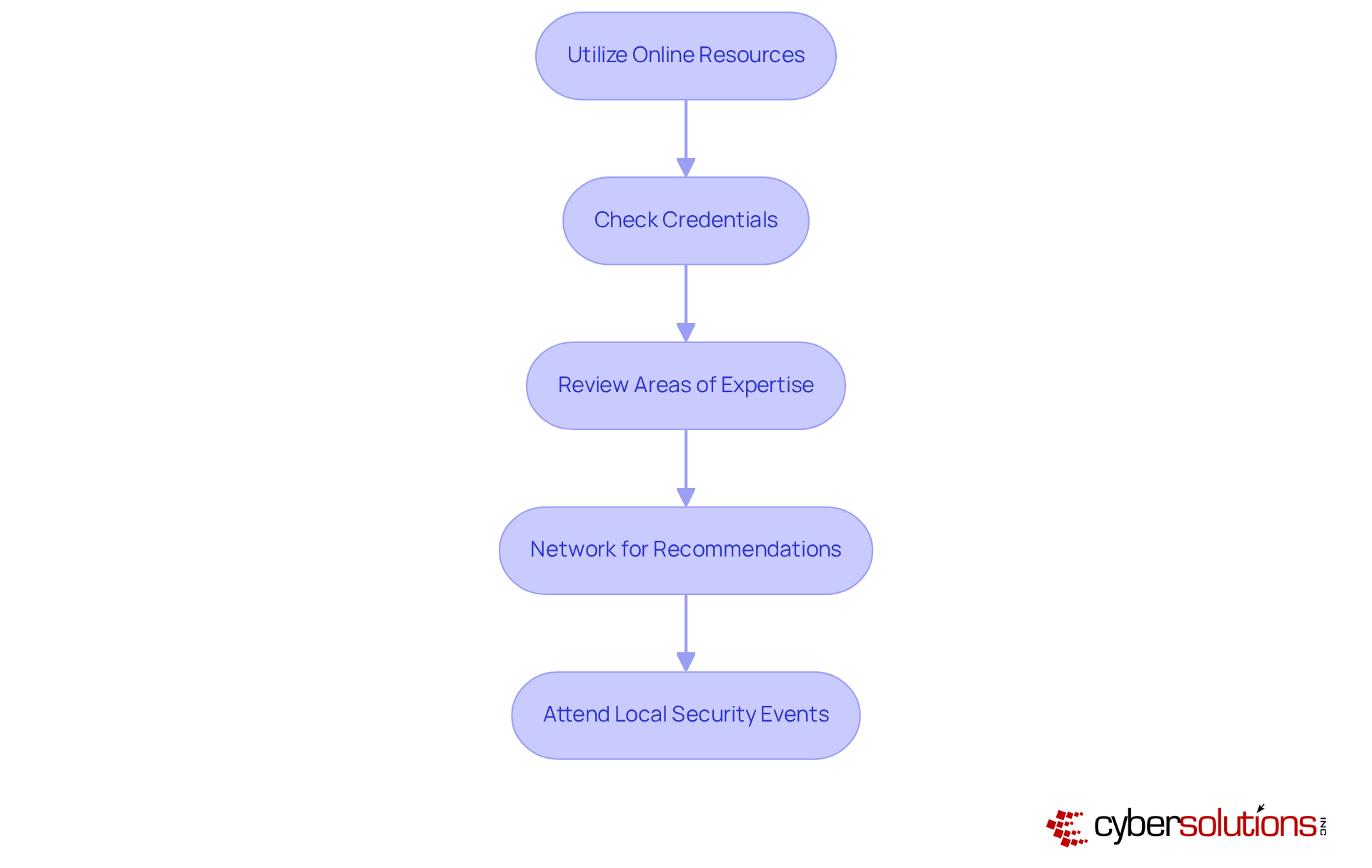
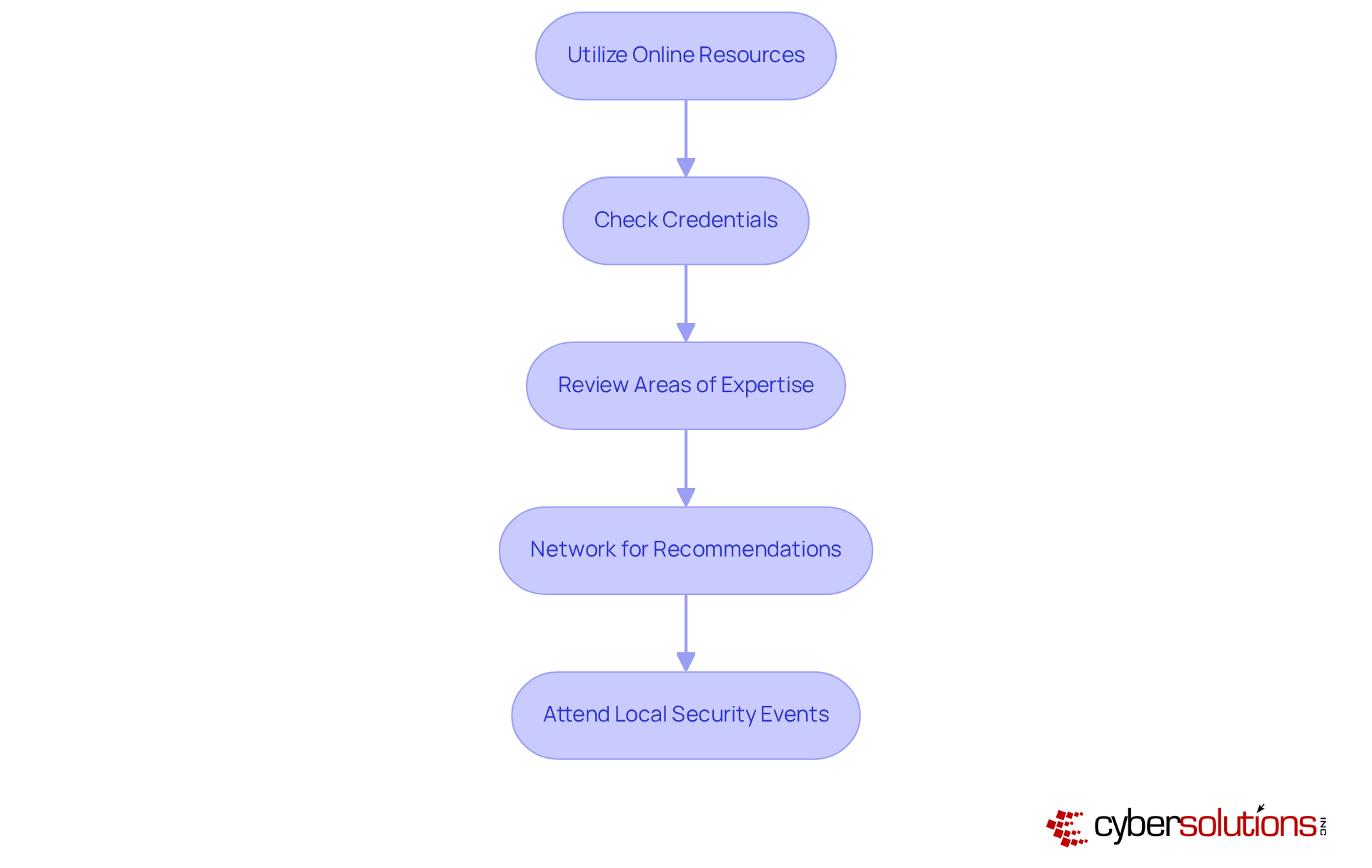
In today's digital landscape, the importance of cybersecurity cannot be overstated, particularly in the healthcare sector, where data protection is critical. To effectively research local cybersecurity firms, follow these steps:
- Utilize online resources by leveraging search engines and platforms such as LinkedIn, Yelp, and industry-specific directories to compile a comprehensive list of firms near me. This approach allows you to access a wide range of options tailored to your needs.
- Check Credentials: Look for certifications that signify an organization's expertise and adherence to industry standards. Firms with these credentials demonstrate a commitment to maintaining high security practices, which is crucial in today’s threat landscape.
- Review Their Areas of Expertise: Ensure the companies you consider possess relevant experience in your field and understand the unique security challenges you face. For instance, companies specializing in healthcare security will be more adept at managing sensitive data than those focusing on other industries. Additionally, inquire about their application allowlisting practices and continuous monitoring capabilities, as these proactive approaches can significantly mitigate the risk of malware and unauthorized software execution.
- Network for Recommendations: Connect with colleagues in your field to gather suggestions on reliable firms. Personal referrals can provide valuable insights into the effectiveness and reliability of potential partners. A notable case study involving a healthcare provider that successfully restored 4,500 endpoints after a ransomware attack illustrates the importance of effective and continuous security training.
- Attend Events: Engage in local security conferences or workshops to connect with potential companies and gain insights into their services directly. These events often highlight the latest trends and technologies, enabling you to evaluate companies' capabilities in real-time.
By following this research approach, you will develop a shortlist of firms near me that are well-equipped to address your cybersecurity needs, ensuring you collaborate with suppliers capable of efficiently protecting your organization from emerging threats.
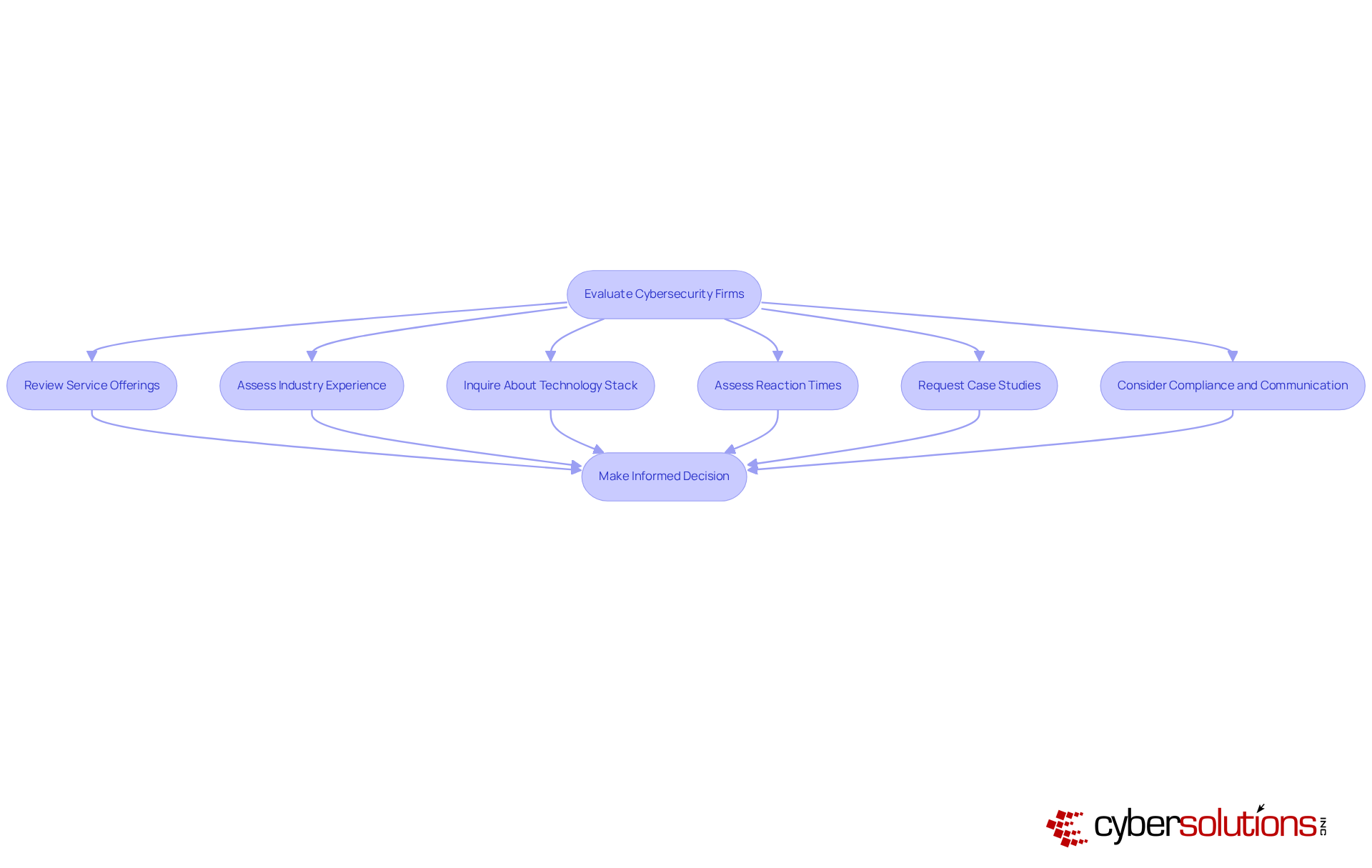
Evaluate Services and Expertise of Each Firm
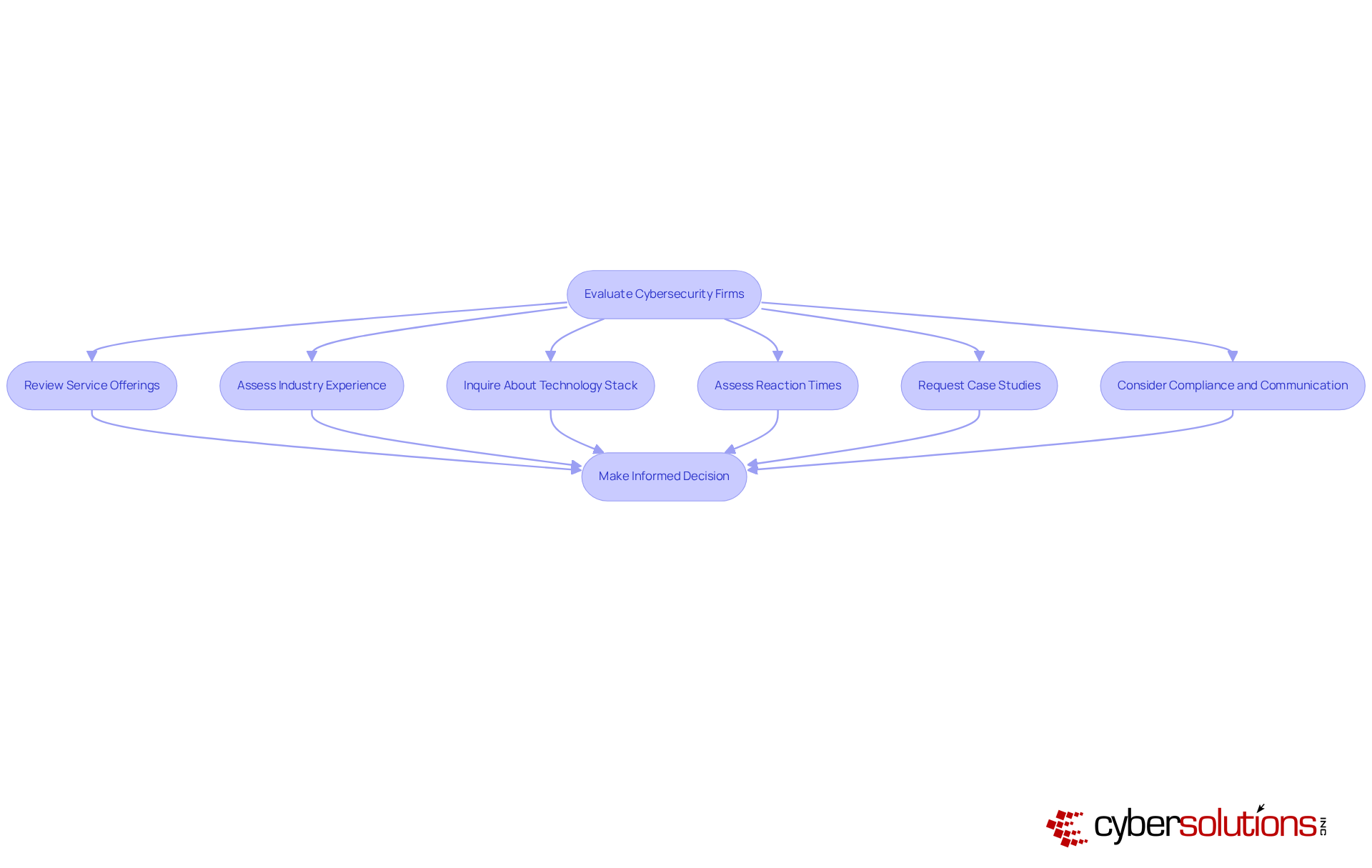
In today's digital landscape, the importance of robust cybersecurity cannot be overstated, especially in the business environment, where sensitive data is at constant risk. As you compile a shortlist of cybersecurity firms, it is crucial to comprehensively evaluate their services and expertise.
- Review Service Offerings: Look for a comprehensive range of services, including threat detection, incident response, and compliance oversight. Efficient crisis response reduces harm through an organized procedure, making it crucial to select firms that excel in these areas. Cyber Solutions, for instance, offers tailored IT services that address the unique security and compliance needs of industries such as healthcare, finance, manufacturing, and government.
- Assess Industry Experience: Check if the firm has worked with businesses similar to yours and understand their approach to cybersecurity in your sector. Industry experience can decrease future occurrence rates by 50%, which highlights the importance of consulting firms that possess industry-specific experience. Cyber Solutions has demonstrated success in rapidly mobilizing to address ransomware attacks, showcasing their expertise in healthcare continuity.
- Inquire About Technology Stack: Ask about the tools and technologies they use to protect clients, ensuring they are current with the latest advancements in digital security. Companies leveraging AI-driven security automation can save an average of $2.22 million per breach, which underscores the importance of modern technology in effective cybersecurity, particularly for small businesses. Cyber Solutions employs advanced tools like machine learning algorithms and secure access controls to defend against evolving cyber threats.
- Assess Reaction Times: Comprehend their emergency handling procedures and how swiftly they can respond to possible dangers. The typical duration to identify a breach is 204 days, with an extra 54 days required to manage it; therefore, it is essential for companies to engage firms that have swift action capabilities. Cyber Solutions' rapid response team, significantly minimizing the potential effects of a cyber event.
- Request Case Studies: Ask for examples of past successes or challenges they have faced with other clients to gauge their problem-solving capabilities. High-performing security teams carry out thorough post-mortem evaluations following each event, which can offer insights into their effectiveness and adaptability. Cyber Solutions has successfully restored 4,500 endpoints following a ransomware attack, showcasing their dedication to thorough crisis management and cybersecurity education.
- Consider Compliance and Communication: Ensure that the organization has a clear communication strategy during a cyber event and is compliant with relevant regulations. Only 30% of organizations regularly test their incident response plans, which highlights the importance of having a strong plan in place when assessing cybersecurity firms. Cyber Solutions emphasizes streamlined communication to improve audit readiness and security.
This evaluation will assist you in identifying which company has the expertise to safeguard your business effectively.
Review Client Testimonials and Case Studies
In today's digital landscape, the importance of robust cybersecurity in healthcare cannot be overstated. To effectively assess the performance of potential firms, consider the following steps:
- Read Reviews: Explore reviews on the company's website, social media, and third-party review platforms to gauge client satisfaction and service quality. Positive testimonials can suggest a company's reliability.
- Request Case Studies: Ask the firm for case studies that showcase their success in tackling cybersecurity challenges for other clients. For example, a recent case study emphasizes their swift action to mitigate a breach in a healthcare environment, where they restored 4,500 endpoints and improved security measures. This example illustrates their effectiveness in crisis management and the structured response plan they implemented, which included immediate action and specialized expertise.
- Evaluate Client Retention: Inquire about their retention rates, which serve as a key indicator of the company's reliability and effectiveness. For instance, the average retention rate for cybersecurity service providers is around 77%, reflecting their ability to maintain long-term client relationships.
- Seek References: Request references from current or past clients to obtain firsthand accounts of their experiences with the organization. This direct feedback can uncover valuable insights into the organization's operational strengths and weaknesses.
- Analyze Feedback: Look for common themes in feedback, such as responsiveness, expertise, and overall satisfaction. Recognizing these patterns can assist you in determining the company's strengths and areas for enhancement.
This thorough review process will allow you to assess the company's reputation and reliability, ensuring you choose a partner that matches your needs among the firms near me.

Compare Pricing and Support Options
Selecting a cybersecurity firm near me is a critical decision that demands careful consideration of pricing and support options. Begin by requesting detailed quotes. Always ask for clarification on services. This helps avoid unexpected costs and ensures you understand what you are paying for.
Next, evaluate support options. Various companies provide differing levels of support. Seek alternatives like:
- Event handling times
- Personalized account management
While many companies offer basic support, advanced services such as incident response may involve extra expenses, so clarify these details beforehand.
Consider contract terms. Review the terms of service carefully, paying attention to:
- Contract length
- Cancellation policies
- Any additional fees
Assess value by comparing the services provided against the pricing to determine which company offers the best value for your specific needs. For instance, while certain companies may charge between $100 and $149 per hour, others might provide more extensive packages that warrant higher prices.
Finally, do not hesitate to negotiate terms. Many firms are open to discussions that can help tailor their offerings to better fit your budget and requirements.
By meticulously comparing pricing and support options from near me, you can make a well-informed decision that balances cost with quality of service, ultimately enhancing your organization's cybersecurity posture.

Conclusion
Selecting the right cybersecurity firm is paramount for any organization intent on safeguarding sensitive data and ensuring compliance in today's digital landscape. By assessing their specific cybersecurity needs and conducting thorough research on local firms, organizations can effectively align with the right experts to protect their operations.
This article presents a comprehensive strategy for choosing a cybersecurity firm, beginning with:
- An evaluation of business requirements
- Meticulous research of local firms
- Assessing their services and expertise
- Reviewing client testimonials
- Comparing pricing and support options
Each step is meticulously designed to empower businesses with the insights necessary for making informed choices, thereby enhancing security and minimizing vulnerability to cyber threats.
In summary, the importance of selecting a reputable cybersecurity firm cannot be overstated. Organizations must prioritize their cybersecurity requirements and take proactive steps to thoroughly evaluate potential partners. By adhering to the outlined approach, businesses can identify a firm that not only meets their specific needs but also strengthens their security posture against evolving cyber threats. Taking decisive action now paves the way for a more secure future, ensuring that sensitive information remains protected and compliance is upheld.
Frequently Asked Questions
How can I assess my business's cybersecurity needs?
Begin by conducting a thorough evaluation that includes identifying sensitive data, evaluating current security measures, understanding compliance requirements, conducting a risk assessment, and setting clear objectives for your security strategy.
What types of sensitive data should I identify?
Sensitive data includes customer information, financial records, and proprietary data critical to your operations.
Why is it important to evaluate current security measures?
Regular assessments can reveal vulnerabilities before they are exploited, allowing businesses to take proactive measures to enhance their security.
What compliance requirements should I be aware of?
Familiarize yourself with industry-specific regulations such as HIPAA for healthcare and PCI-DSS for payment processing, as non-compliance can lead to financial penalties and reputational damage.
What is a risk assessment and why is it necessary?
A risk assessment analyzes potential threats and vulnerabilities that could impact your business, such as cyberattacks and data breaches, helping to enhance action plans and preparedness in case of a breach.
How do I research local cybersecurity firms?
Utilize online resources, check credentials, review their areas of expertise, network for recommendations, and attend local security events to compile a comprehensive list of cybersecurity firms.
What credentials should I look for in cybersecurity firms?
Look for certifications such as CISSP, CISM, or CompTIA Security+ that demonstrate an organization’s expertise and adherence to industry standards.
Why is it important to review a firm's areas of expertise?
Ensuring that firms have relevant experience in your field is crucial, as they will better understand the unique security challenges you face, such as managing HIPAA compliance in healthcare.
How can personal referrals help in selecting a cybersecurity firm?
Personal referrals from colleagues can provide valuable insights into the effectiveness and reliability of potential security service providers.
What benefits do local security events offer?
Local security conferences or workshops allow you to connect with potential companies and gain insights into their services, helping you evaluate their capabilities in real-time.
List of Sources
- Assess Your Business's Cybersecurity Needs
- Must-Know Small Business Cybersecurity Statistics for 2026 (https://bdemerson.com/article/small-business-cybersecurity-statistics)
- cisa.gov (https://cisa.gov/topics/cybersecurity-best-practices)
- Why Every Business Needs a Cybersecurity Risk Assessment in 2025 (https://trustconsultingservices.com/why-every-business-needs-a-cybersecurity-risk-assessment-in-2025)
- krcrtv.com (https://krcrtv.com/news/local/national-cybersecurity-month-highlights-safe-business-practices-amid-security-threats)
- Small business cybersecurity: Survey shows reason for worry (https://mastercard.com/us/en/news-and-trends/stories/2025/small-business-cybersecurity-study.html)
- Research Local Cybersecurity Firms
- cybersecuritydive.com (https://cybersecuritydive.com)
- wsj.com (https://wsj.com/tech/cybersecurity?gaa_at=eafs&gaa_n=ASWzDAgBUDSHZEed7_6ww43HTWbAMuHVgZ2esV0B59zaMAAZkbjwnAttI8X3&gaa_ts=68e700f0&gaa_sig=rejOKnZsMlxnbsOeaTggyQZ0aLaCKFt54M3NAixFQaMaj31ik6L_mrh_mrHCWgkSeKoymk5a1hcoJpnaaZj2Tg%3D%3D)
- The Hacker News | #1 Trusted Source for Cybersecurity News (https://thehackernews.com)
- Security Week Home (https://securityweek.com)
- mordorintelligence.com (https://mordorintelligence.com/industry-reports/cybersecurity-certifications-market)
- Evaluate Services and Expertise of Each Firm
- Incident Response: Importance of an Effective Incident Response Team in Cybersecurity | CyberMaxx (https://cybermaxx.com/incident-response-importance)
- cyble.com (https://cyble.com/knowledge-hub/strengthen-business-cyber-defenses)
- CISA Shares Lessons Learned from an Incident Response Engagement | CISA (https://cisa.gov/news-events/cybersecurity-advisories/aa25-266a)
- Incident Response Statistics to Know in 2025 (https://jumpcloud.com/blog/incident-response-statistics)
- Review Client Testimonials and Case Studies
- welivesecurity.com (https://welivesecurity.com/en/business-security/case-cybersecurity-successful-businesses-built-protection)
- thecyberwire.com (https://thecyberwire.com/pages/testimonials.html)
- cyberinfoblog.com (https://cyberinfoblog.com/blog-post-categories/case-studies)
- Customer Retention Rates by Industry: 2026 Report – First Page Sage (https://firstpagesage.com/seo-blog/customer-retention-rates-by-industry)
- explodingtopics.com (https://explodingtopics.com/blog/customer-retention-rates)
- Compare Pricing and Support Options
- tvgconsulting.com (https://tvgconsulting.com/how-much-does-cybersecurity-cost)
- cybersnowden.com (https://cybersnowden.com/what-is-the-average-cost-of-cyber-security-services-in-2025)
- infosecurity-magazine.com (https://infosecurity-magazine.com/news-features/channel-partners-critical)
- Cybersecurity Pricing Guide April 2026 (https://clutch.co/it-services/cybersecurity/pricing)
- Average Cost of Cybersecurity Services [Updated for 2025] (https://belltec.com/how-much-do-cybersecurity-services-cost)