
In a time when data breaches and operational disruptions can devastate organizations in an instant, the significance of effective disaster recovery and backup strategies has reached an unprecedented level. This article explores ten essential strategies that not only protect sensitive information but also bolster organizational resilience against unexpected crises. As businesses confront evolving threats and increasing regulatory demands, the pressing question emerges: how can they ensure their disaster recovery plans are both robust and compliant? By examining these strategies, readers will gain valuable insights into navigating the complexities of disaster management in today’s digital landscape.
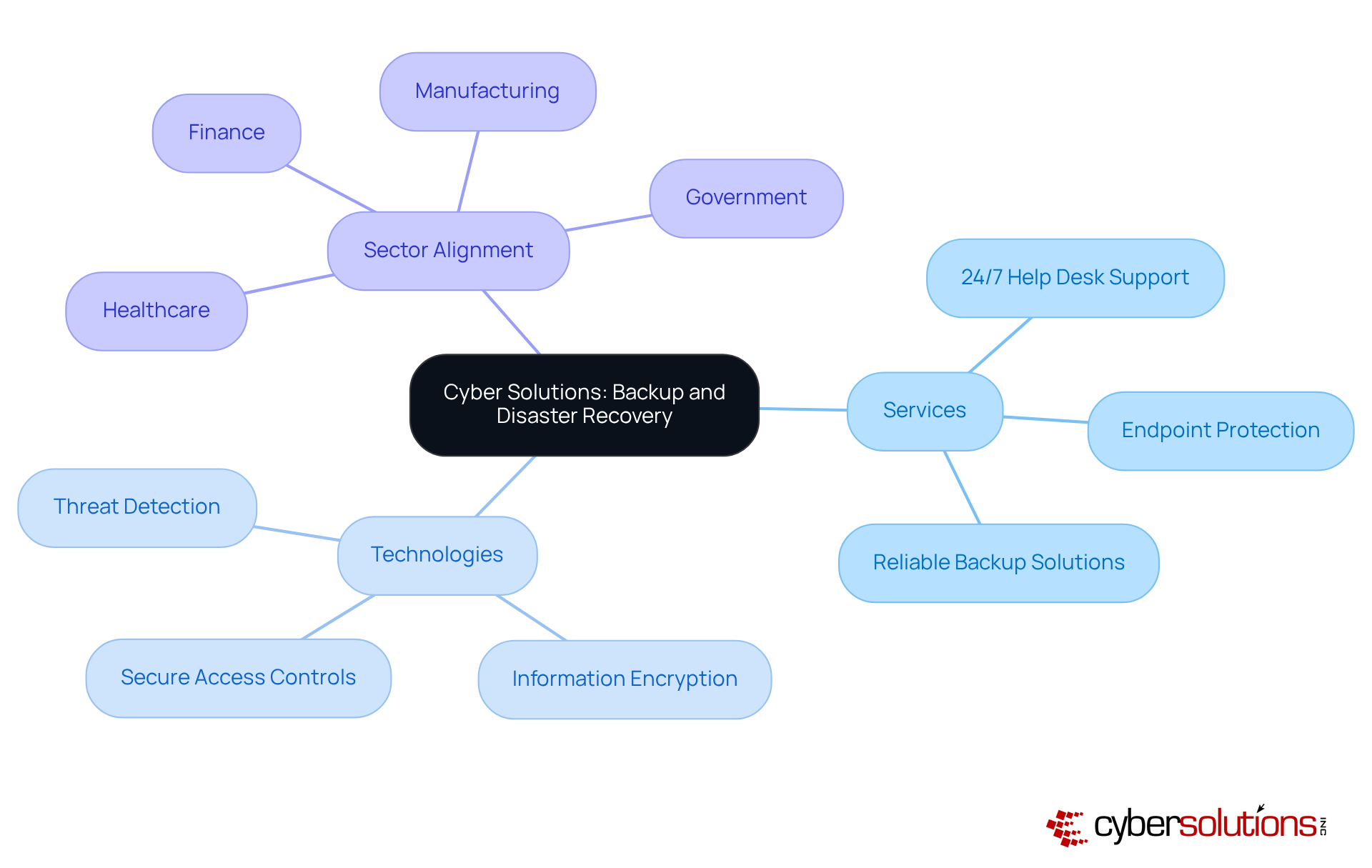
In today's digital landscape, the significance of cybersecurity cannot be overstated, particularly in the healthcare sector where sensitive information is at stake. Cyber Solutions Inc. provides a robust suite of services for disaster recovery, designed to protect against information loss and operational disruptions. This is crucial for healthcare organizations, which face unique challenges such as regulatory compliance and the protection of patient data.
Their comprehensive services encompass:
By implementing advanced technologies like threat detection, information encryption, and secure access controls, along with backup capabilities, organizations can recover swiftly from incidents, thereby minimizing downtime and mitigating financial repercussions.
What sets Cyber Solutions apart is their tailored approach, which aligns each service with the distinct security needs of various sectors, including finance, manufacturing, and government. This strategic alignment enhances overall resilience against potential threats, making it imperative for healthcare CFOs to consider such solutions. With Cyber Solutions, organizations can operate with confidence, ensuring their operations remain uninterrupted and secure.
In today's digital landscape, the importance of disaster recovery cannot be overstated, particularly for organizations relying on data integrity. IBM's advanced solutions for backup and recovery leverage artificial intelligence and cloud technologies to deliver exceptional performance. Key services such as IBM Cloud Backup and IBM Resiliency Orchestration automate restoration processes, ensuring that information is consistently backed up across various environments. This automation significantly reduces downtime and simplifies restoration efforts, making these solutions especially advantageous for entities that demand rapid recovery.
Integrating IBM's solutions into IT strategies enables businesses to realize operational efficiency while enhancing data security. As industry experts highlight, the integration of AI in disaster recovery procedures is revolutionizing how organizations manage their data. By 2025, forecasts suggest that these advancements will greatly enhance recuperation times and mitigate operational risks. Moreover, with 93 percent of cyber attacks targeting backup repositories, the impact of robust security measures on disaster recovery is profound, allowing enterprises to maintain continuity and compliance while effectively safeguarding essential information.
In conclusion, as organizations face increasing cyber threats, the adoption of IBM's innovative solutions becomes a strategic imperative. By prioritizing disaster recovery planning, businesses can not only protect their data but also position themselves for success in an ever-evolving threat landscape.

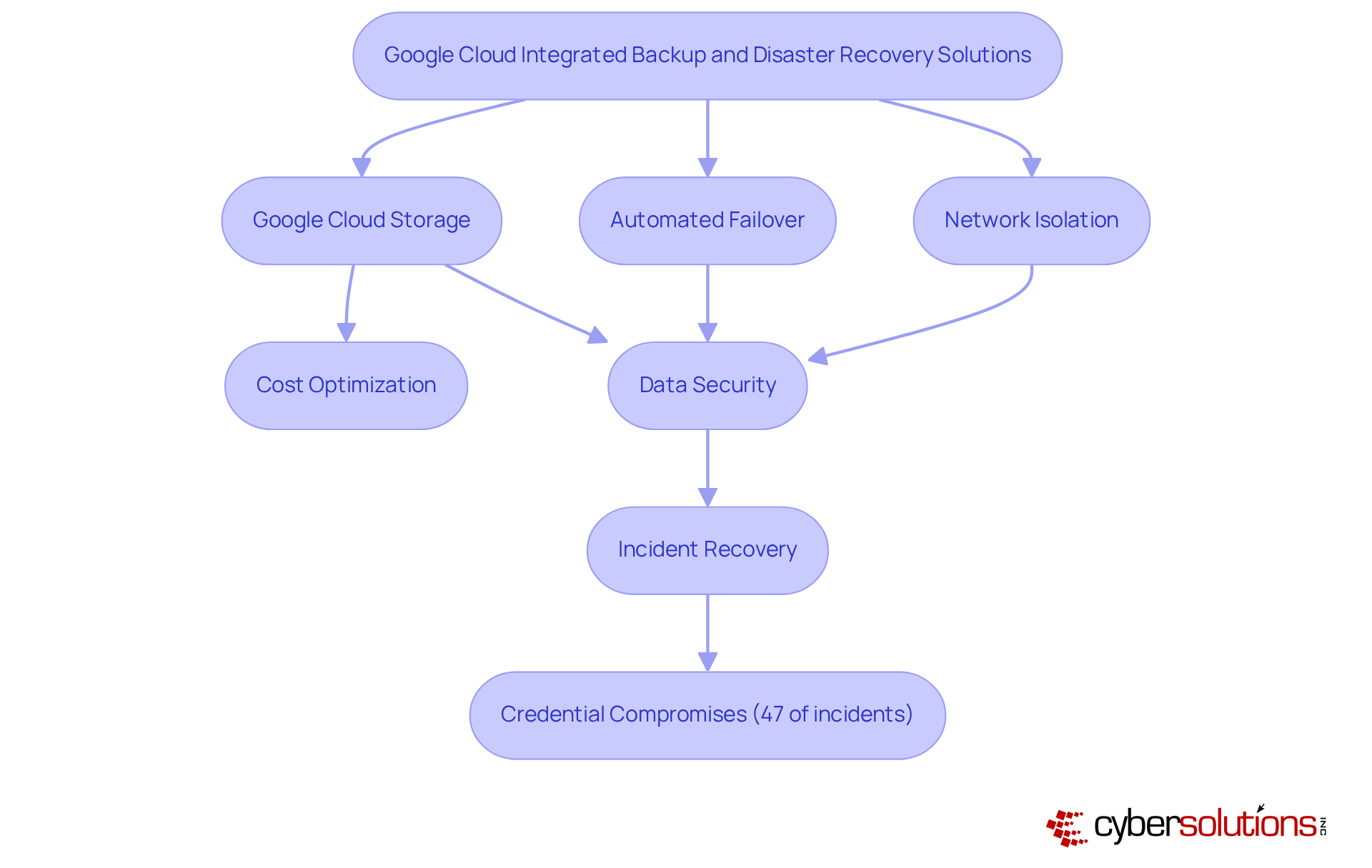
Google Cloud provides robust integrated solutions for backup and disaster recovery, which are essential for safeguarding information across diverse platforms. With tools such as data encryption and automated backups, organizations can leverage cloud resources, significantly reducing downtime during disruptions. As we look ahead to 2025, the anticipated increase in cyber threats underscores a growing reliance on cloud technology for information protection.
The advantages of Google Cloud Storage extend beyond mere information retention; it enables companies to streamline their operations while ensuring data security and recoverability. Experts in cloud technology emphasize the critical need for comprehensive disaster recovery plans, which include the use of automated failover systems to enhance recovery speed. A recommended practice is to isolate production and backup infrastructures through separate VPC networks, further bolstering information protection.
Real-world applications of Google Cloud Storage demonstrate its efficacy in backup scenarios. Organizations have effectively employed these solutions to recover from incidents involving data breaches, which represented 47% of cloud security incidents in the latter half of 2025. By adopting Google Cloud's integrated solutions, businesses not only secure their data but also strengthen their overall operational resilience.
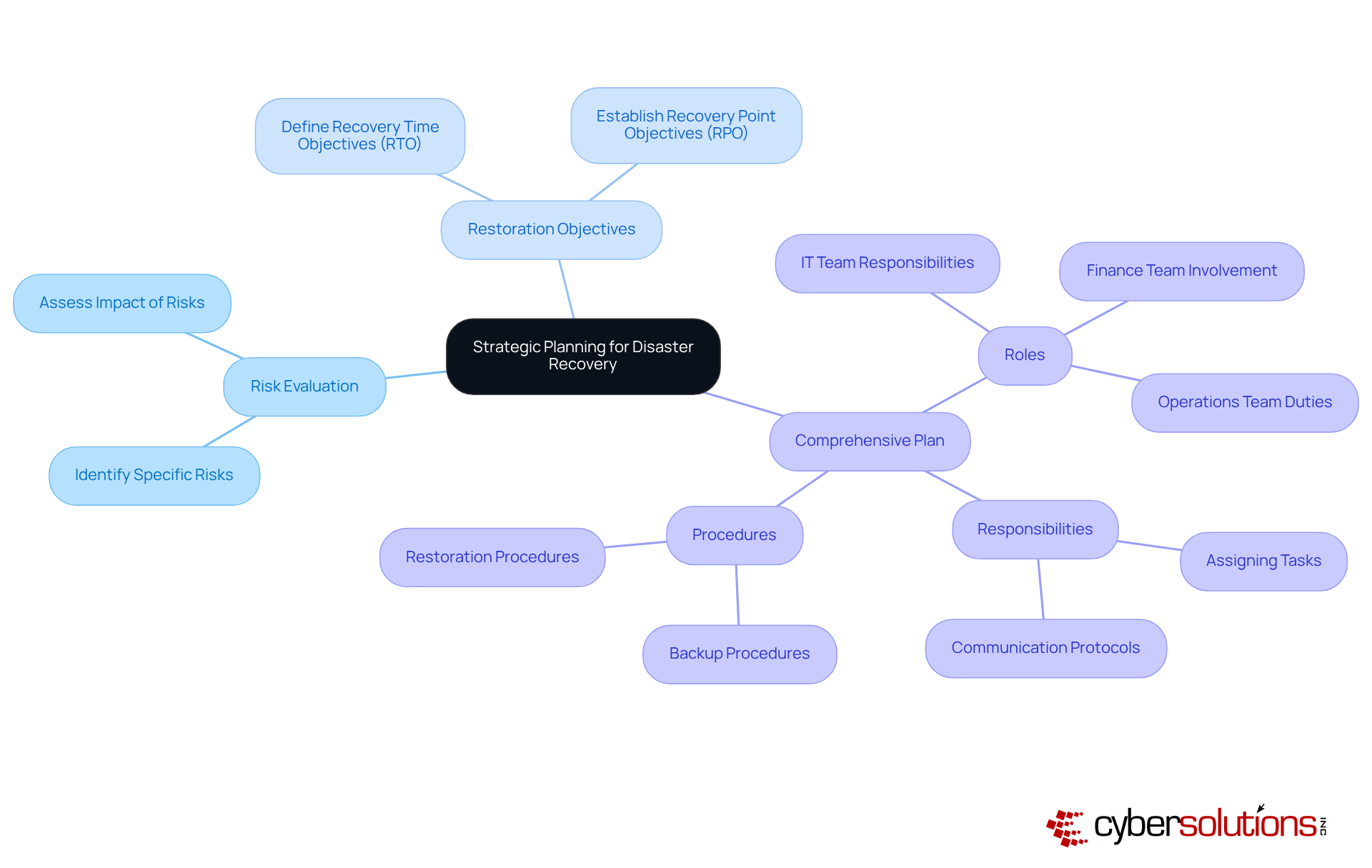
Effective management begins with strategic planning. Organizations must evaluate their risks, define restoration objectives, and create a plan that details roles, responsibilities, and procedures. This planning process should involve key stakeholders from IT, finance, and operations to ensure alignment. By establishing a clear strategy for disaster recovery, entities can enhance their preparedness for disruptions and ensure a swift recovery when incidents occur.
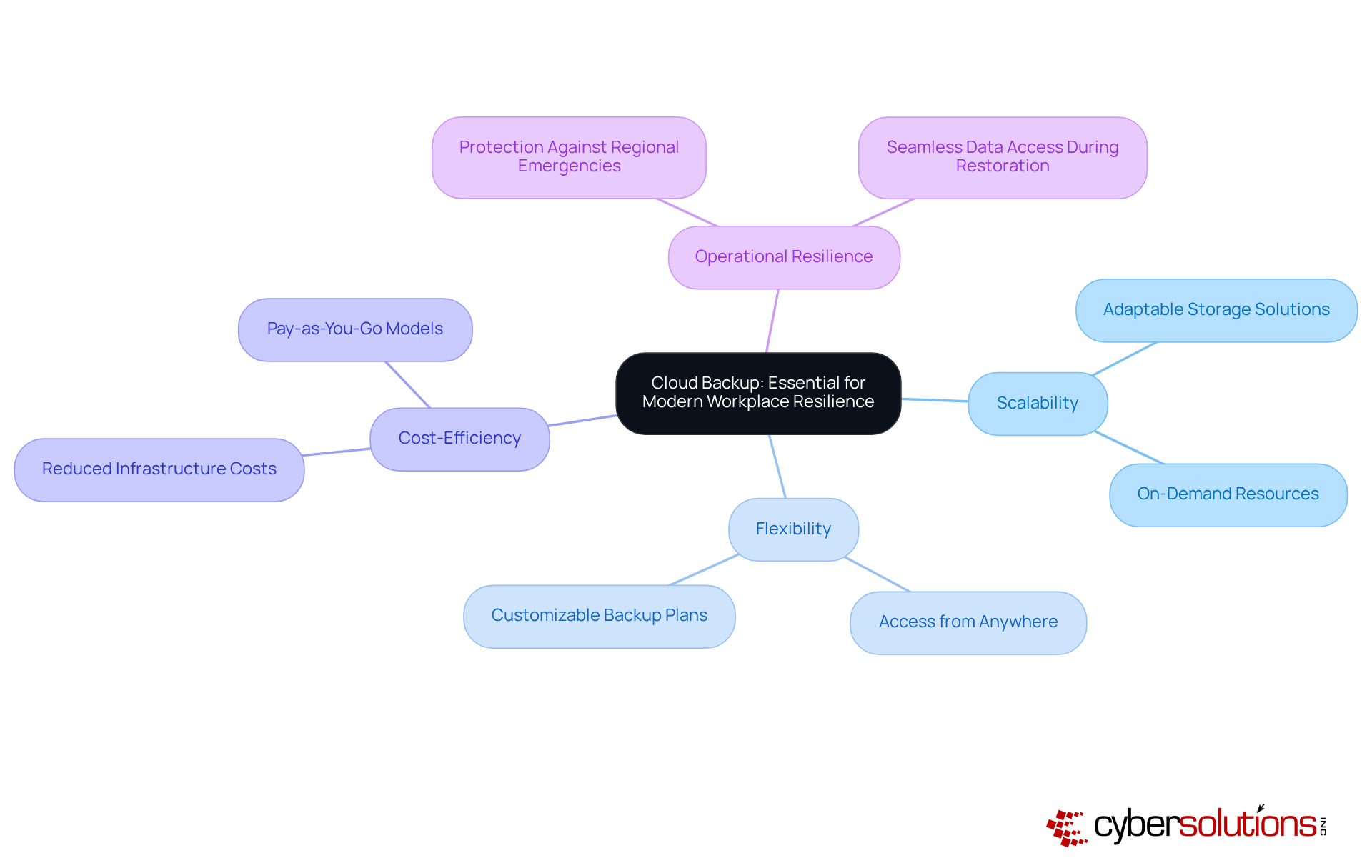
In today's digital landscape, are essential for ensuring information resilience, rather than being merely an option. Organizations must recognize that offer unparalleled scalability, flexibility, and cost-efficiency, which enable them to implement effective for their information offsite. This approach not only protects against regional emergencies but also by ensuring seamless access to data during restoration efforts.
By leveraging cloud backup solutions, companies can enhance their and ensure and backup of critical information, making it accessible no matter the circumstances. Investing in is not just prudent; it is a strategic imperative for any organization aiming to thrive in an increasingly unpredictable environment.
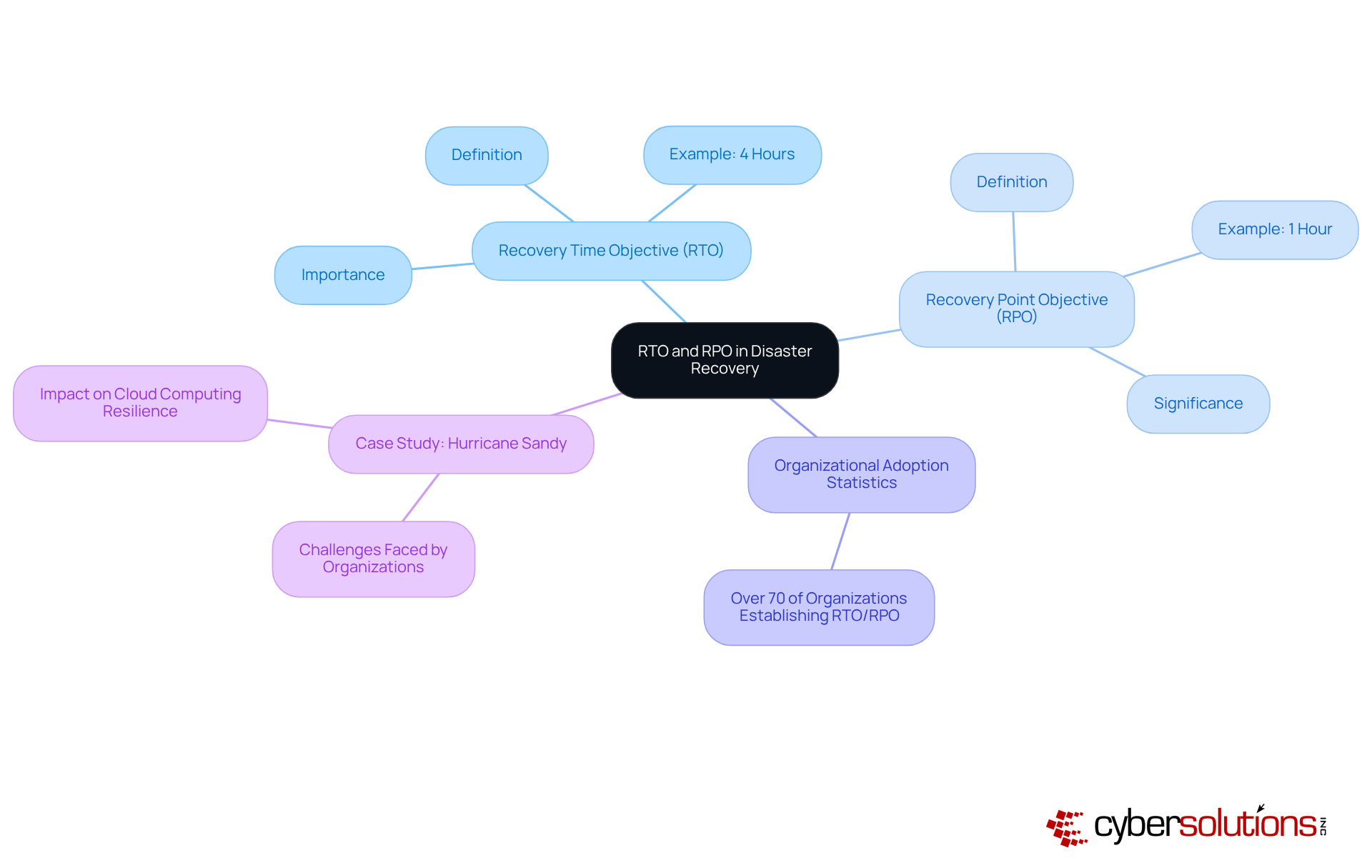
and RTO and RPO are critical metrics in disaster recovery that significantly impact a company's resilience. RTO defines the maximum allowable downtime following an incident, while RPO indicates the maximum permissible information loss measured in time. For example, a company with an RTO of four hours must restore operations within that timeframe to avoid substantial disruptions. Similarly, an RPO of one hour signifies that the organization can only tolerate minimal data loss.
In 2025, statistics indicate that over 70% of organizations have begun to establish their RTO and RPO metrics, recognizing their essential role in disaster recovery planning. By setting clear RTO and RPO objectives, businesses can prioritize restoration efforts and allocate resources more efficiently, ensuring a swift return to normal operations. Industry experts stress that understanding these metrics is crucial for aligning with business goals, ultimately enhancing resilience and minimizing risks during unforeseen events.
Consider the case of Hurricane Sandy, where numerous entities faced significant challenges due to unclear RTO and RPO metrics, resulting in prolonged downtimes and financial losses. As highlighted by industry expert Gelbstein, 'The security of information involves the protection of their confidentiality, integrity, and availability,' underscoring the necessity of robust metrics. Furthermore, concerns regarding organizational ability to uphold these standards have prompted organizations to reassess their disaster recovery strategies, ensuring they are equipped to tackle both natural and artificial emergencies.
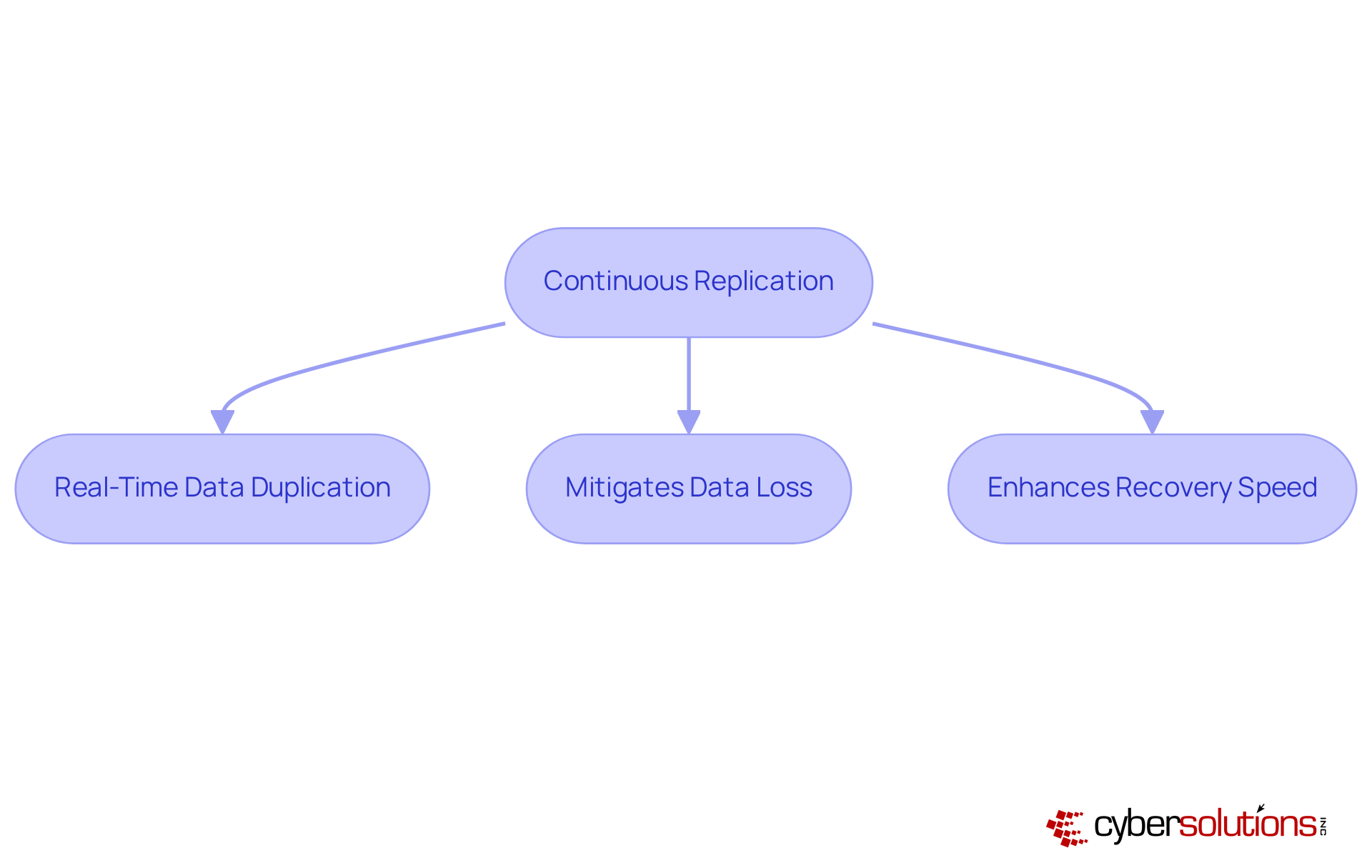
Continuous replication stands as a formidable protection strategy, ensuring real-time duplication of information to a secondary location. This method not only guarantees that data remains consistently current but also significantly mitigates the risk of data loss, which is essential for effective disaster recovery. By adopting this approach, organizations can markedly decrease recovery time and enhance their overall disaster recovery and backup success. This strategy is especially advantageous for businesses that demand reliability and cannot afford prolonged downtime.
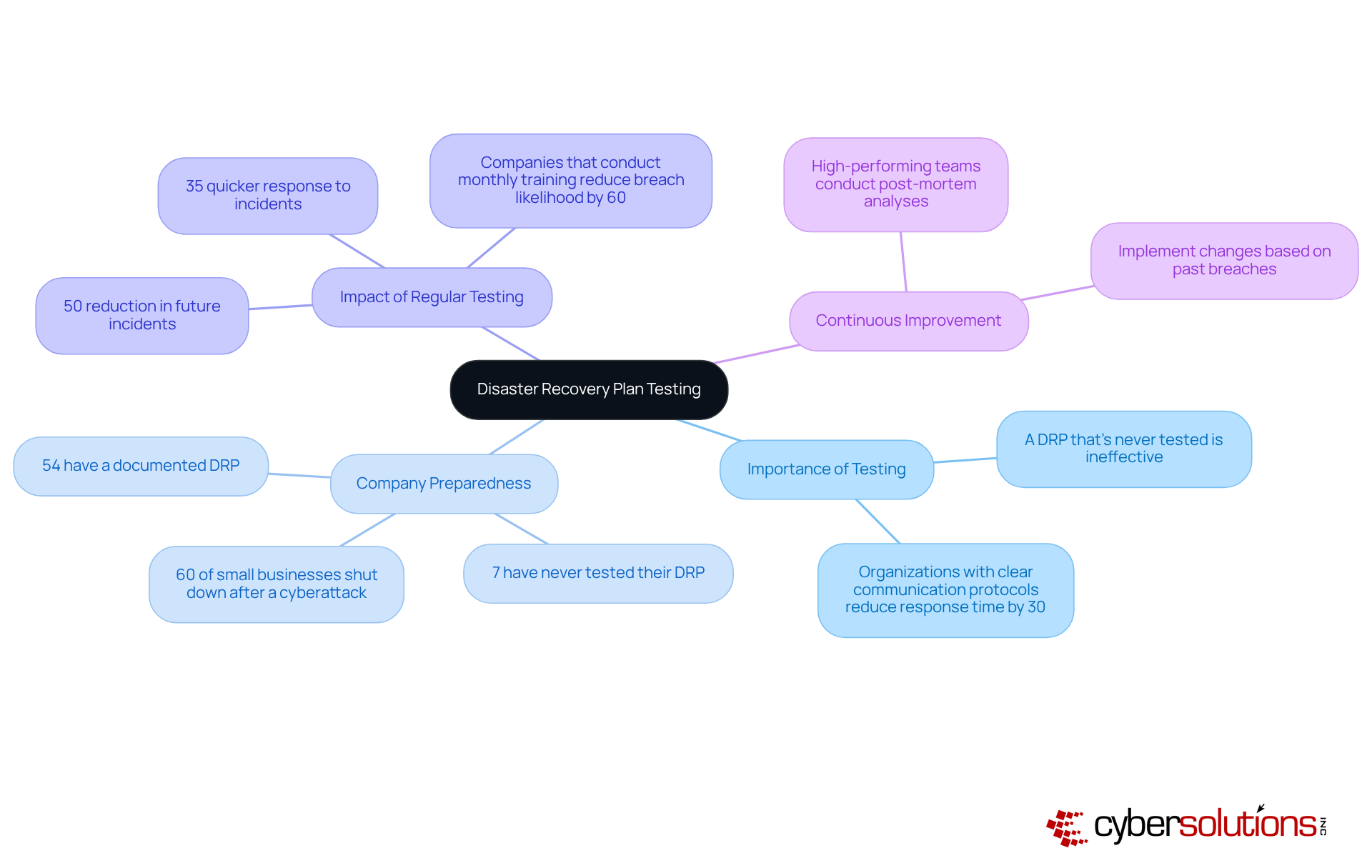
Routine evaluation of emergency response strategies is not just important; it is essential for confirming their efficacy and ensuring organizational durability. Frequent simulations and drills, involving all relevant stakeholders, clarify roles and responsibilities during emergencies. Notably, entities conducting exercises at least quarterly can react 35% quicker to incidents, significantly enhancing restoration results.
Experts assert that a disaster recovery plan (DRP) that is never tested is fundamentally ineffective. Alarmingly, only 54% of companies currently have a documented plan, and a staggering 7% admit they have never tested their plan. This lack of readiness in disaster recovery and backup can lead to severe consequences; FEMA indicates that 25% of businesses facing a major crisis never resume operations.
Moreover, entities that implement regular testing can reduce future incident rates by as much as 50%. This underscores the importance of preparedness through regular testing and post-incident reviews. As IBM succinctly states, "A DRP that’s never tested is basically a piece of paper." By fostering a culture of readiness and integrating testing into daily operations, businesses can better respond efficiently to emergencies, ultimately safeguarding their operations and reputation. To ensure your entity is prepared, prioritize testing and actively engage all participants in the process.
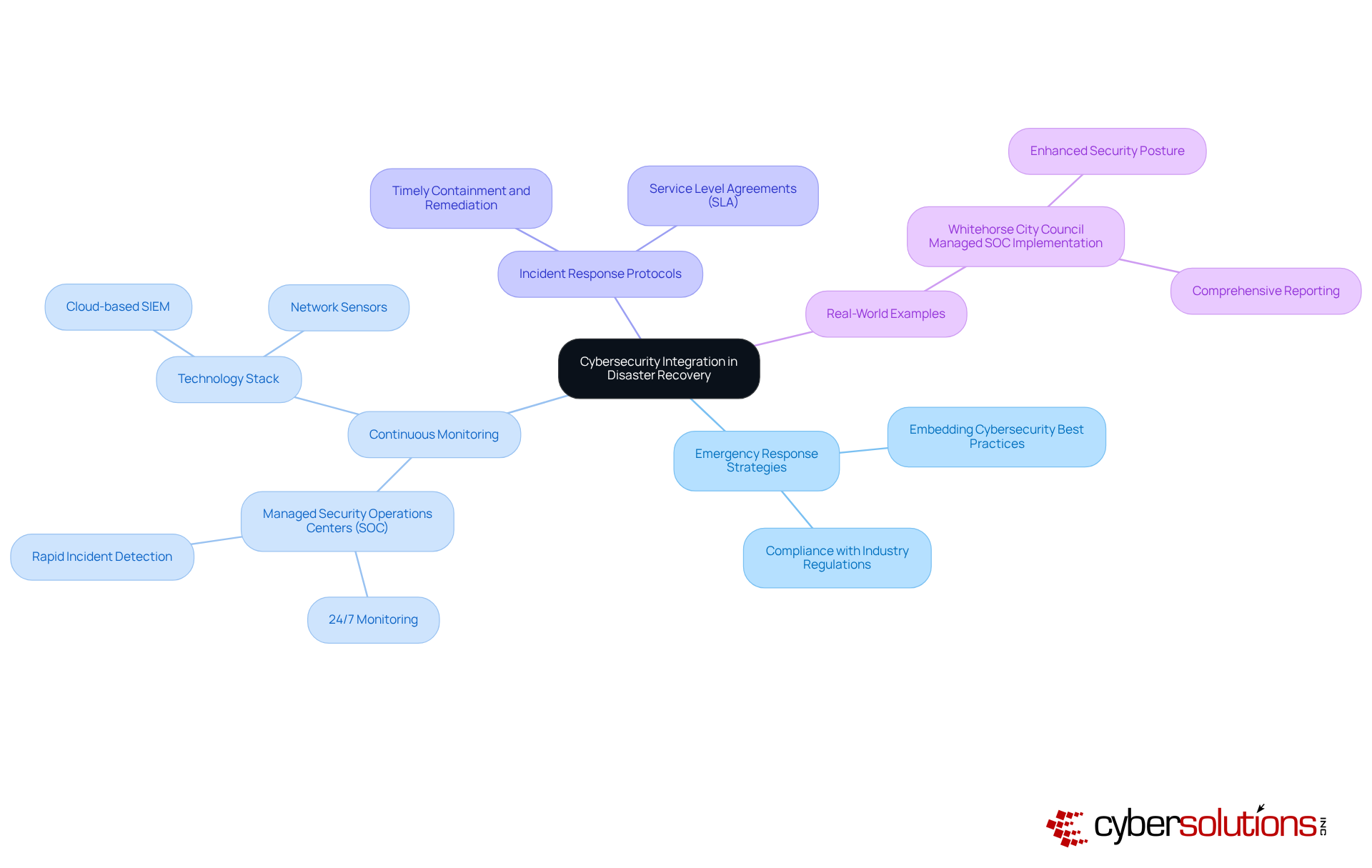
Incorporating cybersecurity into emergency response strategies is not just advisable; it is imperative for organizations aiming to safeguard against evolving threats. With cyberattacks, including malware and information breaches, becoming increasingly prevalent, it is essential for organizations to explicitly address these challenges. By embedding cybersecurity measures into restoration strategies, businesses not only enhance their resilience but also ensure compliance with industry regulations. This comprehensive approach safeguards sensitive data and strengthens the overall security posture of the organization.
Current trends indicate a shift towards proactive measures within emergency management frameworks. Organizations are recognizing the critical need for continuous monitoring and rapid response to mitigate the impact of cyber threats effectively. For example, the implementation of security information and event management has demonstrated effectiveness in providing 24/7 monitoring and prompt detection of security incidents, significantly reducing security risks.
The impact of ransomware on disaster recovery and backup planning is profound. As attacks rise, entities must prioritize strategies that incorporate cybersecurity along with incident response protocols. Real-world examples, such as the successful deployment of a Managed SOC for Whitehorse City Council, illustrate how tailored cybersecurity solutions can enhance response strategies. This implementation not only improved incident response times but also delivered comprehensive reporting and actionable insights, ultimately strengthening the security posture and providing greater peace of mind for stakeholders.
By 2025, integrating cybersecurity into emergency response strategies will transcend being a best practice; it will become essential for entities striving to navigate the complexities of contemporary threats efficiently. By adopting a holistic approach that merges IT resilience with cybersecurity, businesses can better prepare for and recover from potential disasters.
Adherence factors play a pivotal role in compliance, particularly for organizations operating within regulated sectors such as healthcare and finance. Understanding regulations, including HIPAA, GDPR, and PCI DSS, is imperative, as these frameworks dictate the necessary protocols for data protection during recovery efforts.
For instance, to protect patient information, organizations must implement strict access controls.
By integrating crisis management strategies with these regulations, organizations not only mitigate the risk of penalties but also enhance their overall security posture. This proactive compliance approach cultivates trust among clients and stakeholders, showcasing a commitment to data security.
Notably, compliance is essential in maintaining business continuity and safeguarding critical information assets.

In the realm of disaster recovery and backup, the necessity for robust strategies cannot be overlooked. Organizations must prioritize comprehensive planning and the integration of advanced technologies to safeguard their critical data and ensure operational continuity. By recognizing the unique challenges posed by cybersecurity threats and regulatory requirements, businesses can effectively navigate the complexities of disaster recovery, positioning themselves for success in an increasingly unpredictable environment.
The article outlines essential strategies for effective disaster recovery, including:
Moreover, it emphasizes the need for regular testing of disaster recovery plans and the integration of cybersecurity measures to enhance resilience against potential threats. Each of these elements contributes to a holistic approach that not only protects sensitive information but also fosters organizational confidence in the face of disruptions.
Ultimately, organizations are urged to adopt a proactive stance towards disaster recovery and backup. By investing in tailored solutions and prioritizing strategic planning, businesses can ensure they are well-equipped to respond swiftly to incidents, thereby minimizing downtime and safeguarding their reputation. Embracing these essential strategies will empower organizations to thrive amidst challenges, reinforcing the significance of disaster recovery as a critical component of operational success.
What is the significance of cybersecurity in the healthcare sector?
Cybersecurity is crucial in the healthcare sector due to the need to protect sensitive information, ensure regulatory compliance, and safeguard patient data.
What services does Cyber Solutions Inc. provide for disaster recovery and backup?
Cyber Solutions Inc. offers 24/7 help desk support, endpoint protection, and reliable backup solutions that ensure data integrity and availability.
How does Cyber Solutions enhance disaster recovery and backup capabilities?
Cyber Solutions uses advanced technologies such as threat detection, information encryption, and secure access controls to enhance disaster recovery and backup capabilities.
What unique approach does Cyber Solutions take in its services?
Cyber Solutions tailors its services to align with the specific security and compliance requirements of various sectors, including finance, manufacturing, and government.
What are the key features of IBM's backup and disaster recovery solutions?
IBM's solutions leverage artificial intelligence and cloud technologies, offering services like IBM Cloud Backup and IBM Resiliency Orchestration that automate restoration processes.
How does the integration of AI impact disaster recovery and backup?
The integration of AI in disaster recovery and backup processes is expected to significantly enhance recuperation times and mitigate operational risks by 2025.
What is the importance of IBM Cloud Backup?
IBM Cloud Backup is crucial for maintaining operational efficiency and continuity, especially since 93 percent of attacks target backup repositories.
What solutions does Google Cloud offer for disaster recovery and backup?
Google Cloud provides integrated solutions like Google Cloud Storage for disaster recovery and backup, and Google Cloud Disaster Recovery with automated failover and recovery capabilities.
How does Google Cloud Storage optimize costs for organizations?
Google Cloud Storage allows companies to manage resources efficiently, which helps optimize costs while ensuring data security and recoverability.
What is a recommended practice for enhancing information protection in disaster recovery?
It is recommended to isolate production and backup infrastructures through separate VPC networks to bolster information protection.
What real-world applications demonstrate the effectiveness of Google Cloud Storage?
Organizations have successfully used Google Cloud Storage to recover from incidents, including credential compromises, which accounted for 47% of cloud security incidents in the latter half of 2025.