
In today's digital landscape, cybersecurity is not just an option but a necessity for healthcare organizations. With the increasing frequency and sophistication of cyber threats, healthcare CFOs face unique challenges that demand immediate attention.
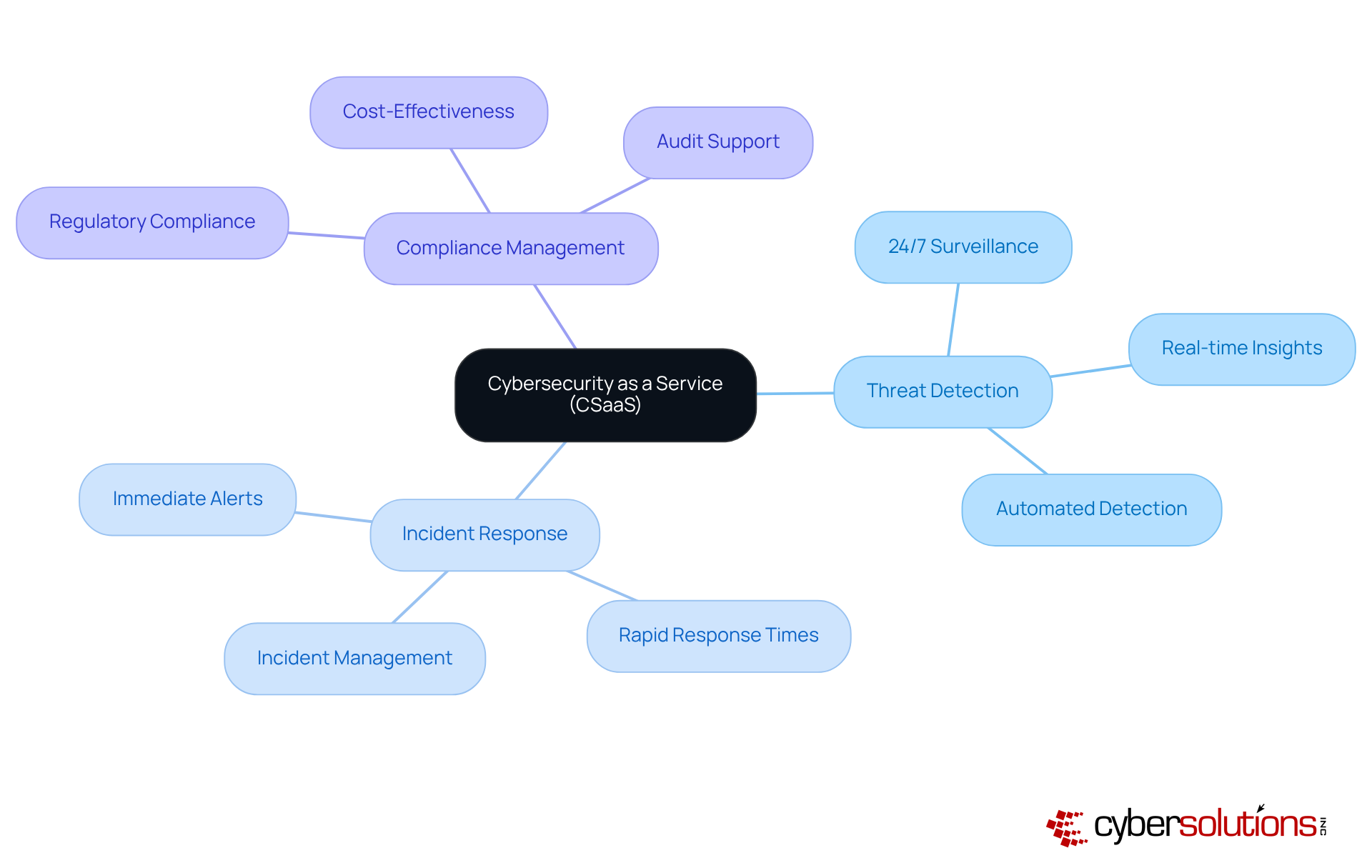
Cybersecurity as a Service (CSaaS) emerges as a vital solution, offering a subscription-based model that enhances security while simultaneously reducing costs and complexity. This innovative approach provides advanced threat detection, compliance management, and continuous monitoring, which are essential for safeguarding sensitive patient data.
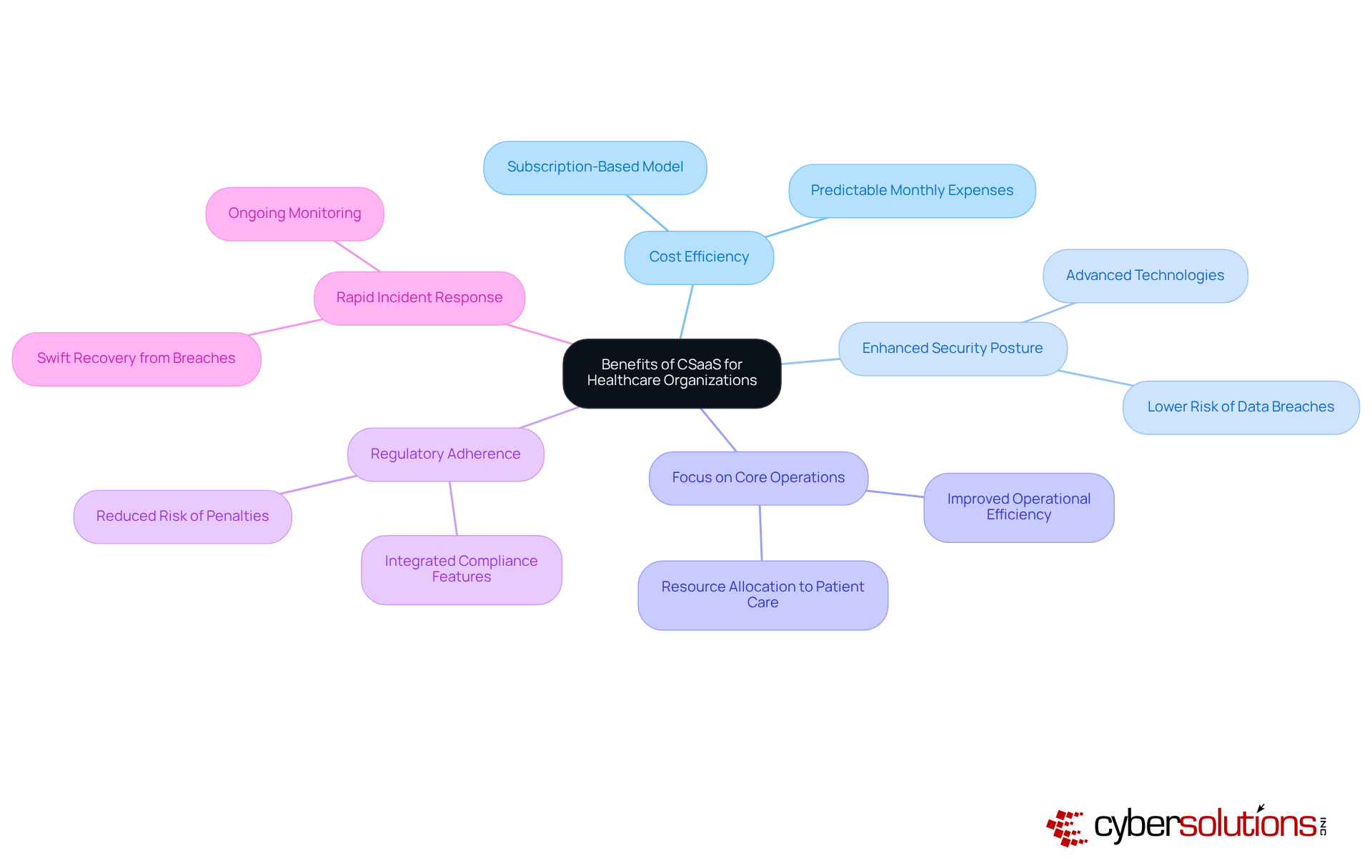
Healthcare organizations must efficiently allocate their resources to focus on patient care, yet the ever-evolving cybersecurity threats can divert attention from this core mission. CSaaS enables CFOs to maintain robust cybersecurity defenses without the burden of managing complex systems in-house. By leveraging this service, healthcare leaders can ensure compliance with regulations while enhancing their overall security posture.
As the healthcare sector continues to confront these pressing challenges, adopting CSaaS not only addresses immediate security concerns but also fosters long-term operational efficiency. The integration of advanced cybersecurity measures allows organizations to redirect their focus toward what truly matters: delivering quality patient care. In this way, CSaaS stands out as a strategic investment in the future of healthcare security.
In an era where healthcare organizations face an increasing barrage of sophisticated cyber threats, the significance of robust cybersecurity measures is paramount.
Cybersecurity as a Service (CSaaS) emerges as a transformative solution, offering healthcare CFOs a strategic advantage by delivering comprehensive, cloud-based security without the burden of substantial in-house investments.
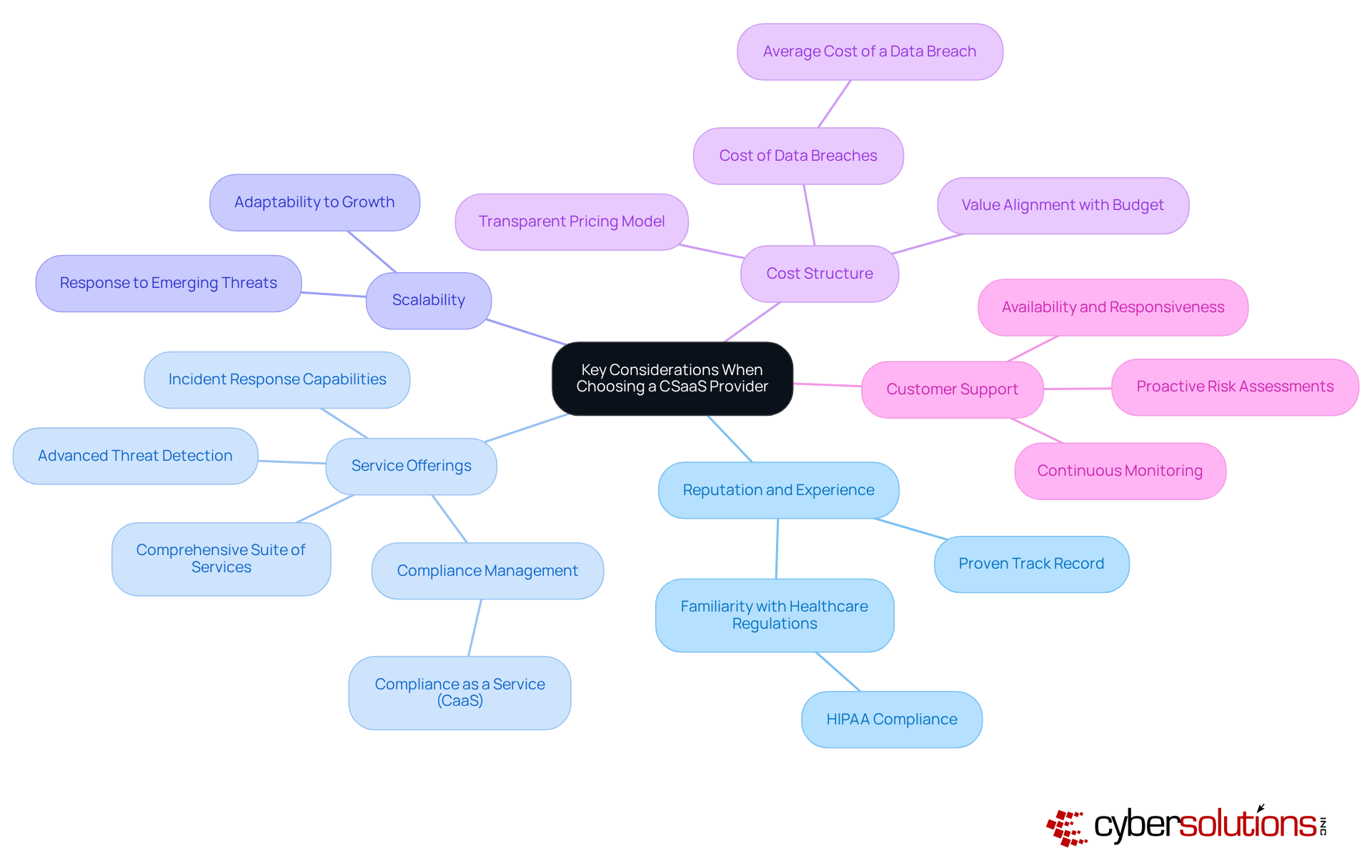
However, as the landscape of digital threats continues to evolve, how can CFOs ensure they are selecting the right CSaaS provider to protect sensitive patient data while optimizing their budgets?
This article explores the critical elements of CSaaS, contrasting it with traditional models and highlighting its unique benefits for healthcare organizations.
In today's digital landscape, cybersecurity is not just an option; it is a necessity, especially for healthcare organizations facing an ever-evolving array of threats. Cybersecurity as a service provides a cloud-based model that delivers comprehensive cybersecurity solutions, eliminating the need for extensive in-house infrastructure. This service encompasses a wide range of offerings, including:
All structured within a subscription-based framework. For healthcare entities, cybersecurity as a service facilitates the integration of advanced protection technologies and expert insights, ensuring adaptability and growth in their cybersecurity initiatives.
With 24/7 surveillance of networks to identify anomalies and potential vulnerabilities, cybersecurity as a service offers immediate alerts and . This capability enables prompt measures to prevent downtime or breaches, allowing CFOs to focus on strategic financial planning and resource allocation. By utilizing cybersecurity as a service to outsource these critical functions, organizations can safeguard themselves against evolving cyber threats while maintaining compliance with industry regulations. Notably, this service can also assist in reducing ongoing security expenses, making it a budget-friendly option.
According to the SANS Institute, 54% of participants reported that Managed Detection and Response (MDR) was successful in identifying and controlling cyber-attacks. This statistic underscores the efficacy of cloud security services in enhancing security posture. Real-world applications, such as Cyber Solutions' network monitoring services, further illustrate how this model provides continuous oversight and immediate notifications, demonstrating practical use in the healthcare sector.
The implementation of cloud security services not only strengthens security posture but also promotes more efficient resource utilization. Ultimately, this contributes to improved operational efficiency and cost-effectiveness, making it a strategic choice for healthcare organizations looking to navigate the complexities of cybersecurity.
In the rapidly evolving landscape of healthcare, the importance of cybersecurity cannot be overstated. As cyber threats become more sophisticated, healthcare organizations face unique challenges that demand a robust response. Comparing traditional cybersecurity models with cybersecurity as a service (CSaaS) reveals several key differences that can significantly impact a medical institution's security posture.
In summary, while conventional cybersecurity models have their merits, they cannot match the adaptability, economy, and comprehensive strategy that Cybersecurity as a Service provides, aligning effectively with the financial and operational objectives of medical facilities. As the industry progresses, the adoption of cloud security services is becoming increasingly essential for maintaining robust cybersecurity defenses.
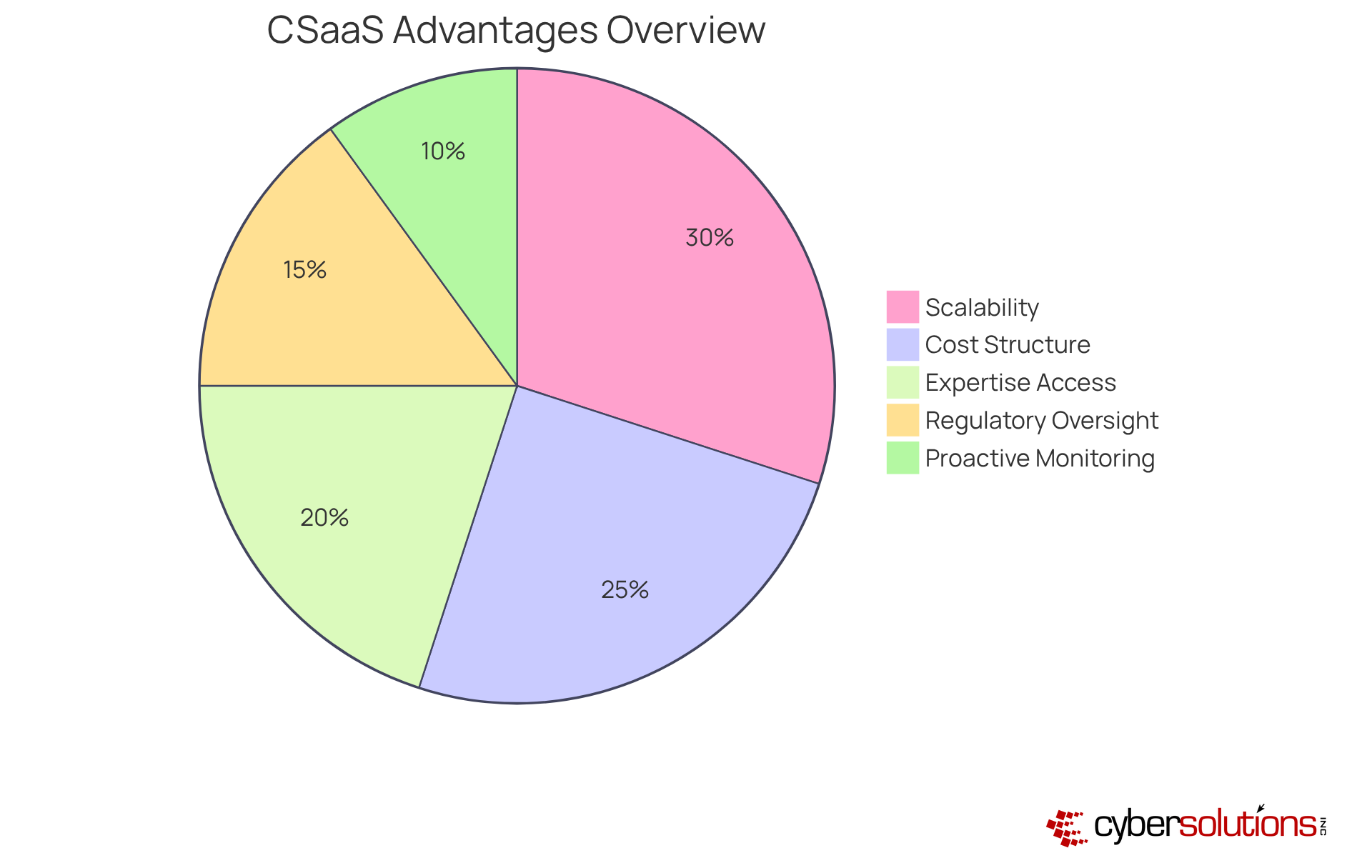
In today's healthcare landscape, adopting cybersecurity as a service is essential for organizations striving to enhance their financial and operational efficiency. For CFOs, the challenges of safeguarding sensitive data while managing budgets can be daunting. However, cybersecurity as a service presents a strategic solution that effectively addresses these concerns.
In summary, cloud security as a service not only strengthens security measures but also integrates effortlessly with the financial and operational goals of medical organizations. For CFOs looking to improve both security and efficiency, cybersecurity as a service emerges as a compelling and strategic option.
In today's healthcare landscape, the significance of robust cybersecurity cannot be overstated. As threats evolve, healthcare CFOs encounter unique challenges that require a strategic approach in choosing a cybersecurity as a service provider. Prioritizing the following key factors will empower CFOs to make informed decisions that enhance their organization's security posture.
By carefully weighing these factors, healthcare CFOs can select a provider of cybersecurity as a service that not only strengthens their cybersecurity posture but also aligns with their financial and operational objectives.
Cybersecurity as a Service (CSaaS) stands as a critical strategy for healthcare organizations, especially for CFOs who are navigating the complexities of data protection and regulatory compliance. This model enables healthcare entities to harness advanced cybersecurity solutions while sidestepping the burdensome costs and challenges associated with traditional in-house systems. Such a transition not only bolsters security but also aligns financial planning with operational efficiency, allowing healthcare providers to concentrate on delivering quality care while safeguarding sensitive information.
The discussion highlights key benefits of CSaaS, including:
By comparing it with traditional cybersecurity models, the adaptability and scalability of CSaaS emerge as significant advantages, making it a strategic choice for organizations confronting an increasingly sophisticated threat landscape. Moreover, the selection of a reputable provider with appropriate service offerings is paramount, as it directly influences the effectiveness of the cybersecurity strategy.
In an era where cyber threats continuously evolve, adopting cybersecurity as a service is not merely a prudent choice but an essential one for healthcare organizations. By prioritizing CSaaS, CFOs can ensure that their institutions are compliant, secure, and positioned to thrive within a challenging environment. The time to act is now; investing in CSaaS can cultivate a more resilient healthcare system that prioritizes patient safety and data integrity.
What is Cybersecurity as a Service (CSaaS)?
Cybersecurity as a Service (CSaaS) is a cloud-based model that provides comprehensive cybersecurity solutions, including threat detection, incident response, and compliance management, without the need for extensive in-house infrastructure.
Why is CSaaS important for healthcare organizations?
CSaaS is crucial for healthcare organizations as it helps them address the evolving array of cyber threats while ensuring compliance with industry regulations. It allows for the integration of advanced protection technologies and expert insights.
What are the key features of CSaaS?
Key features of CSaaS include 24/7 network surveillance, immediate alerts, real-time insights, and a subscription-based framework that helps organizations manage their cybersecurity needs effectively.
How does CSaaS help organizations focus on strategic planning?
By outsourcing critical cybersecurity functions to CSaaS providers, organizations can prevent downtime or breaches, allowing CFOs and management to concentrate on strategic financial planning and resource allocation.
What are the cost benefits of using CSaaS?
CSaaS can help reduce ongoing security expenses, making it a budget-friendly option for organizations while still providing robust cybersecurity measures.
How effective is Managed Detection and Response (MDR) in identifying cyber threats?
According to the SANS Institute, 54% of participants reported that Managed Detection and Response (MDR) was successful in identifying and controlling cyber-attacks, highlighting the effectiveness of cloud security services.
Can you provide an example of CSaaS in action?
An example of CSaaS in action is Cyber Solutions' network monitoring services, which offer continuous oversight and immediate notifications, demonstrating practical use in the healthcare sector.
What overall benefits does CSaaS provide for healthcare organizations?
CSaaS strengthens security posture, promotes efficient resource utilization, improves operational efficiency, and enhances cost-effectiveness, making it a strategic choice for healthcare organizations navigating cybersecurity complexities.