Introduction
In an era where healthcare organizations are increasingly targeted by cyberattacks, the necessity for robust cybersecurity measures has never been more pressing. Security-as-a-Service (SECaaS) provides a strategic solution, enabling these entities to outsource their security needs while leveraging advanced technologies and expert guidance.
However, with a multitude of providers available, how can healthcare organizations ensure they select the right partner to safeguard sensitive data and maintain compliance?
This article explores the essential criteria for choosing SECaaS providers, equipping healthcare leaders with the insights necessary to navigate this critical decision-making process.
Understand Security-as-a-Service in Healthcare
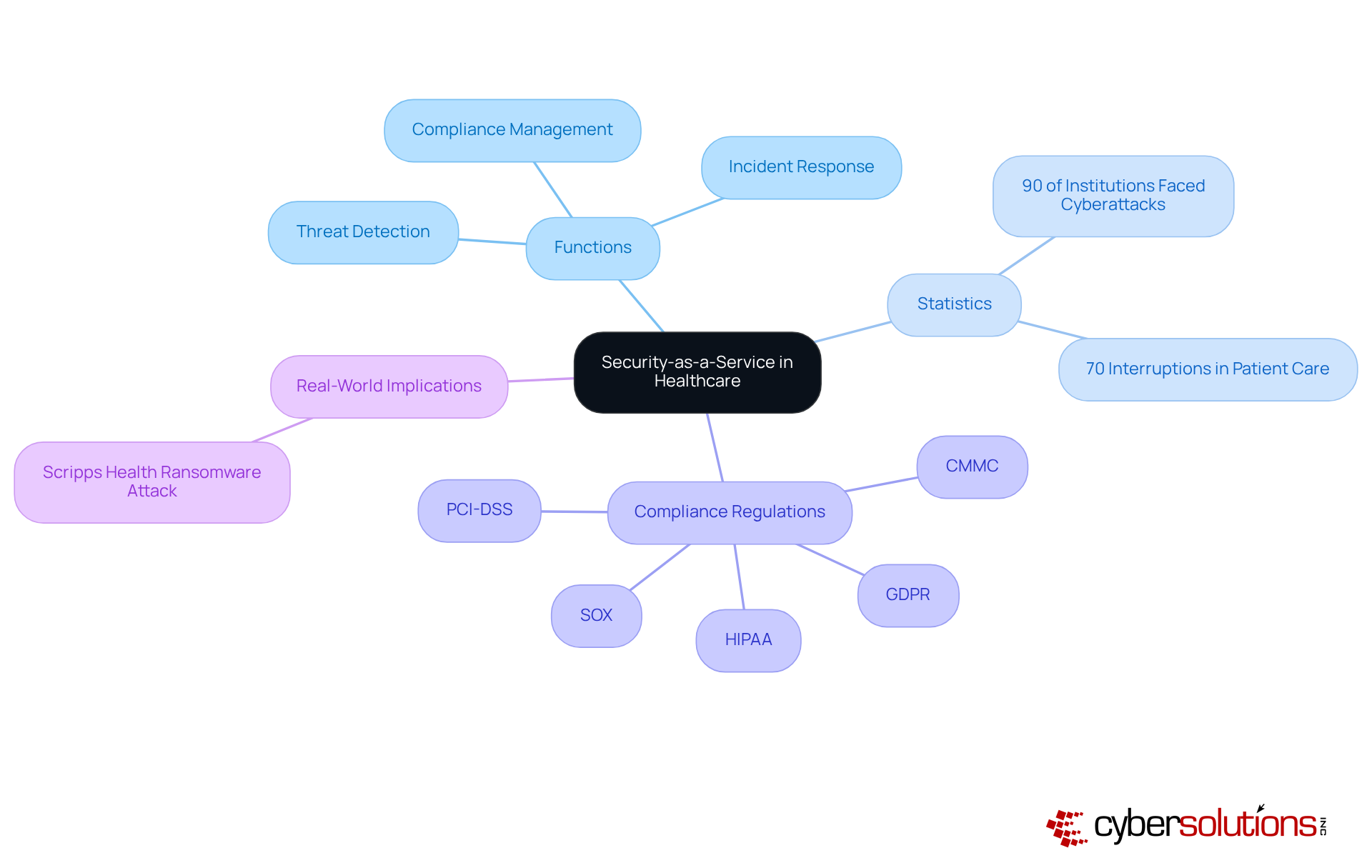
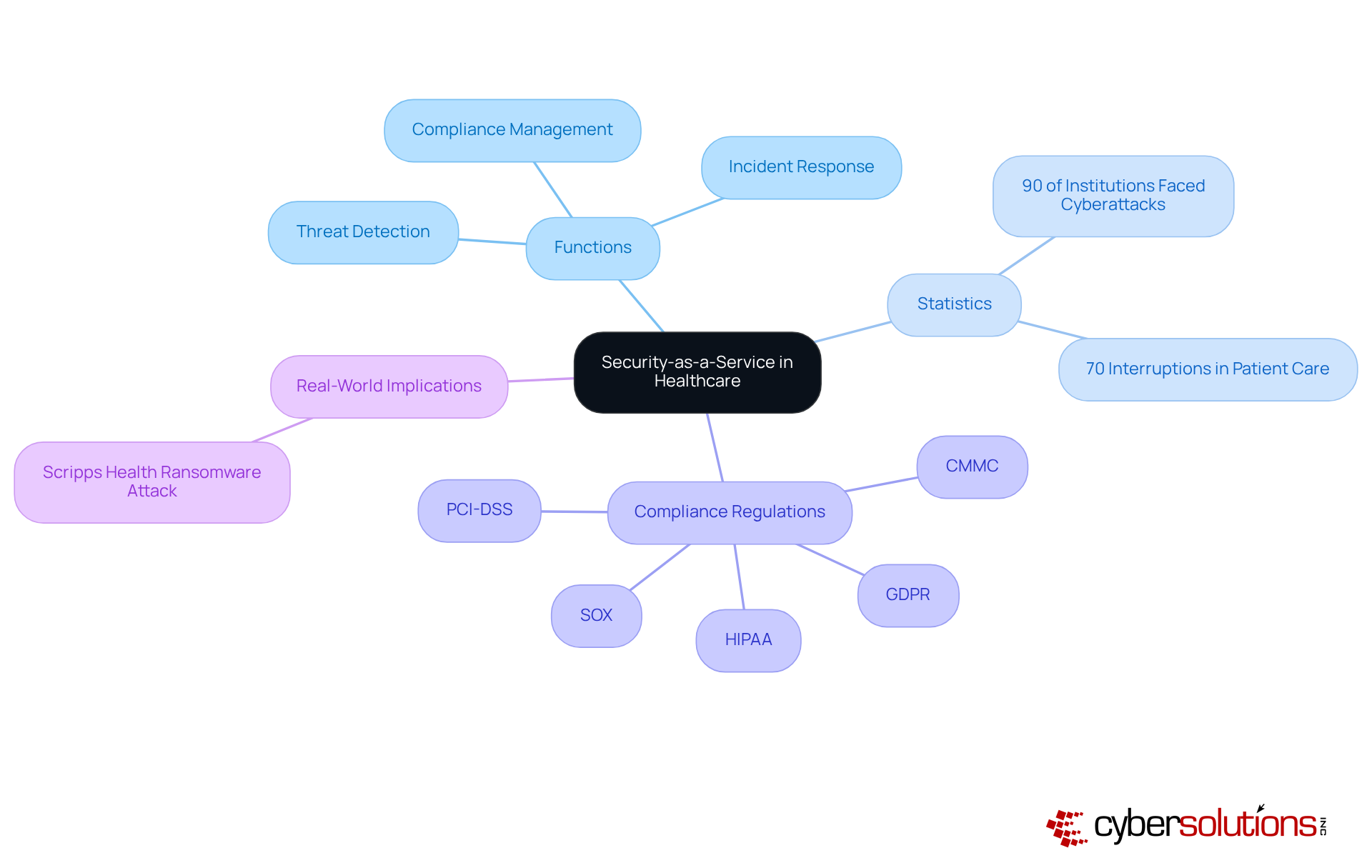
In today's digital age, cybersecurity is not just an option but a necessity for healthcare organizations. Security-as-a-Service (SECaaS) emerges as a vital cloud-based model, enabling healthcare entities to outsource their cybersecurity needs to experts. This comprehensive service encompasses critical protective functions, including:
These functions address the urgent need to safeguard sensitive patient data against escalating threats.
The reality is stark: over 90% of healthcare institutions reported experiencing a cyberattack last year, with these incidents interrupting patient care in 70% of cases. By adopting SECaaS, healthcare organizations can utilize advanced protective technologies and expert knowledge, alleviating the burden of maintaining an in-house security team. This strategic move not only fortifies their defenses but also allows them to concentrate on core operations while ensuring compliance with essential regulations such as:
Recent trends indicate a growing reliance on SECaaS, driven by the increasing complexity of cyber threats and the pressing need for robust protective frameworks. Experts advocate for this model, underscoring its potential to enhance resilience and streamline operations, particularly as healthcare entities grapple with challenges like tech sprawl, where some depend on up to 76 different security tools, highlighting the need for consolidation. The effectiveness of SECaaS is evident in real-world scenarios, such as the Scripps Health ransomware attack, which underscored the substantial risks, leading to a 30% increase in recovery time.
With SECaaS, healthcare entities can swiftly identify, contain, and mitigate threats, ensuring business continuity. As the healthcare landscape continues to evolve, organizations striving to improve security and maintain operational efficiency will find the adoption of SECaaS crucial.
Identify Key Criteria for Selecting SECaaS Providers
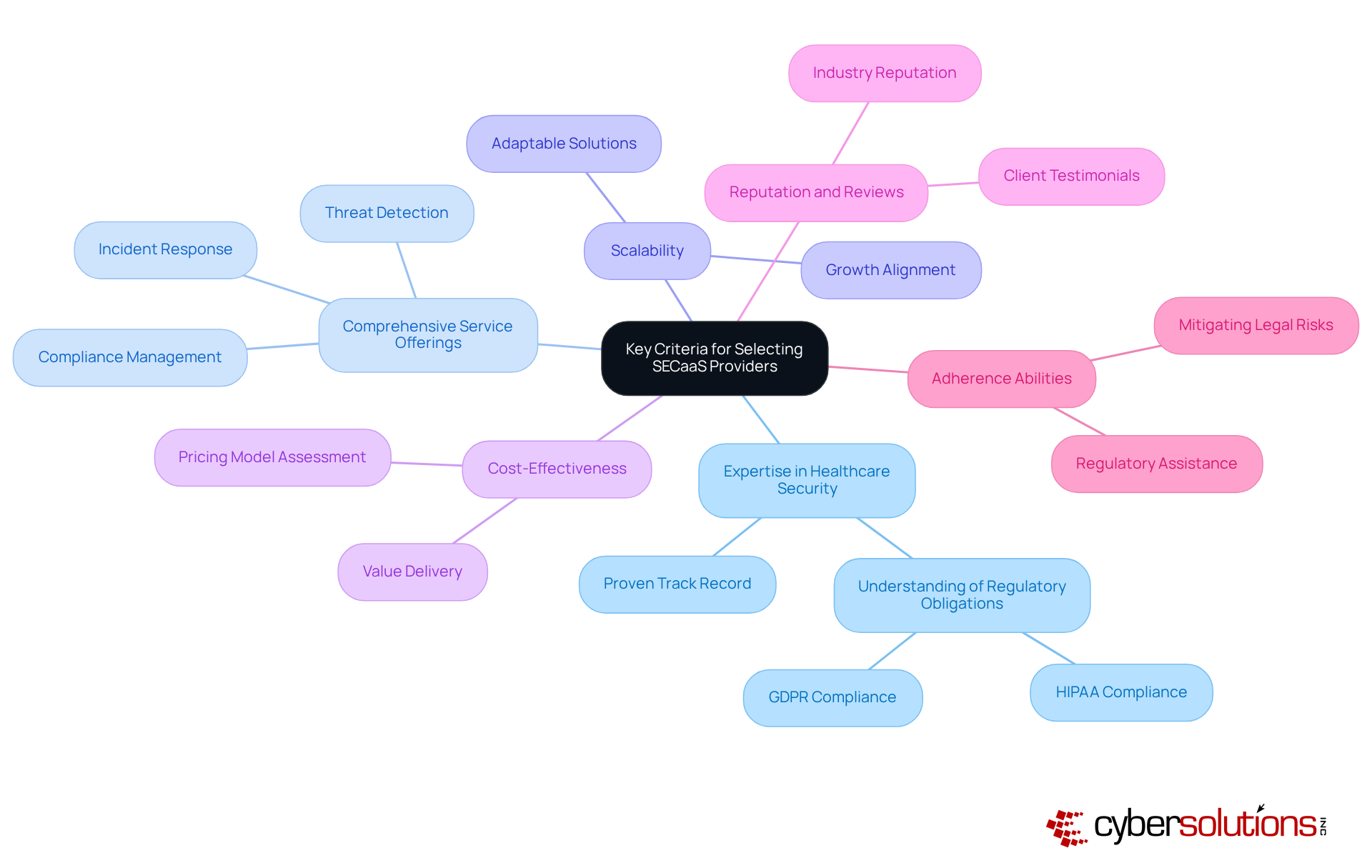
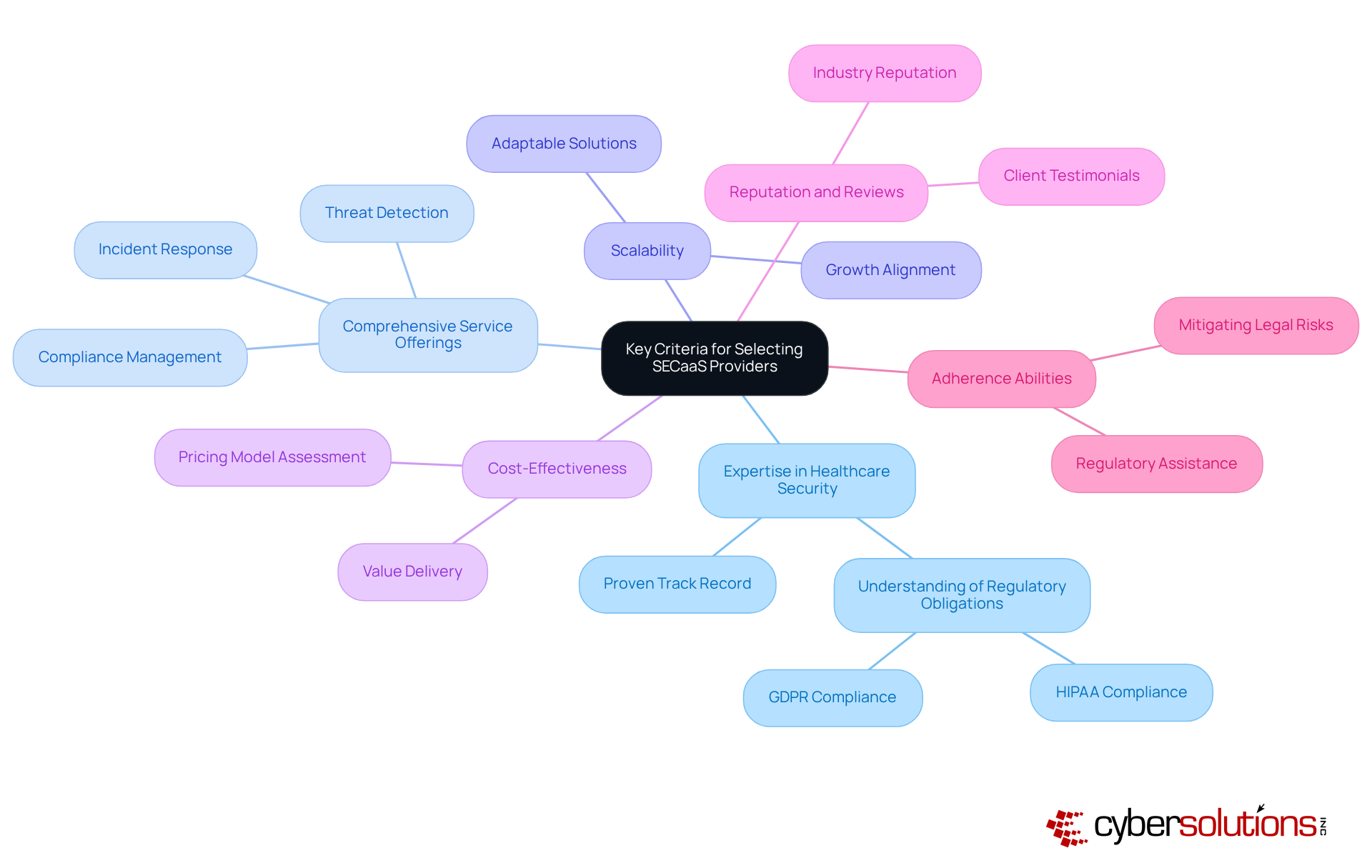
In today's digital landscape, selecting SECaaS providers is paramount for healthcare organizations seeking robust cybersecurity solutions. The unique challenges faced by these organizations demand careful evaluation of several key criteria.
- Expertise in Healthcare Security: It is essential to choose providers with a proven track record. They possess a deep understanding of the distinctive challenges and regulatory obligations, including compliance standards, that healthcare entities must navigate.
- Comprehensive Service Offerings: Opt for providers that deliver a full suite of services—ranging from threat detection to incident response and recovery—to comprehensively address all aspects of cybersecurity.
- Scalability: The provider should offer solutions that scale alongside the organization and adjust to evolving requirements.
- Cost-Effectiveness: Assess the pricing model of potential providers to ensure alignment with the organization's budget while delivering value through enhanced security measures. With cybercrime costs projected to exceed $23 trillion by 2027, wise financial planning is crucial.
- Reputation and Reviews: Investigate the provider's reputation within the industry and consider client testimonials to gauge their effectiveness and reliability. Notably, organizations such as Scripps Health and the University of Vermont Health Network have faced significant operational disruptions due to inadequate cybersecurity measures, underscoring the necessity of a dependable partner.
- Adherence to Compliance Standards: Ensure that the provider can assist with regulatory requirements, such as HIPAA and GDPR, to mitigate legal risks and safeguard sensitive patient information. With 31% of organizations reporting data breaches, compliance has never been more critical.
Evaluate and Compare SECaaS Providers Effectively
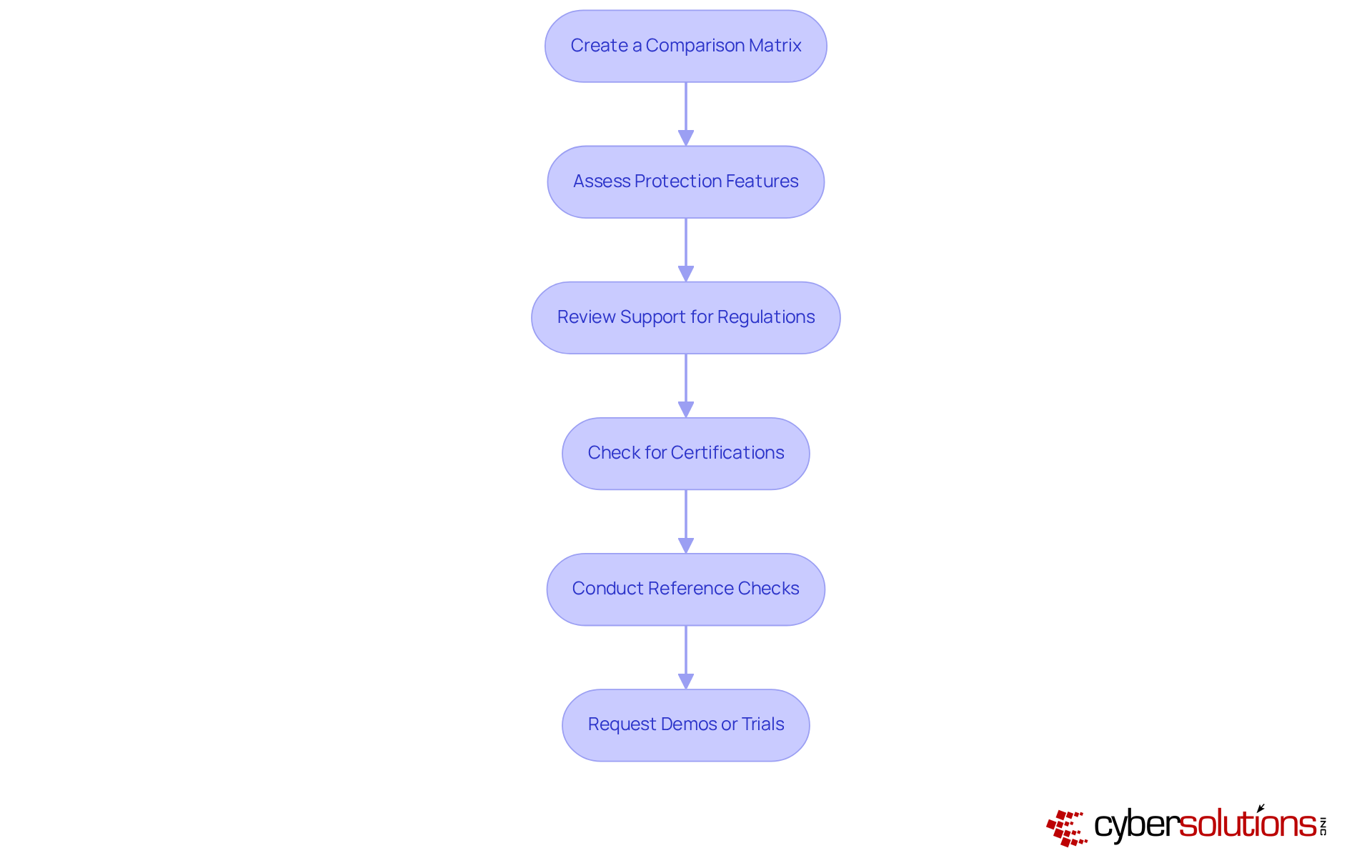
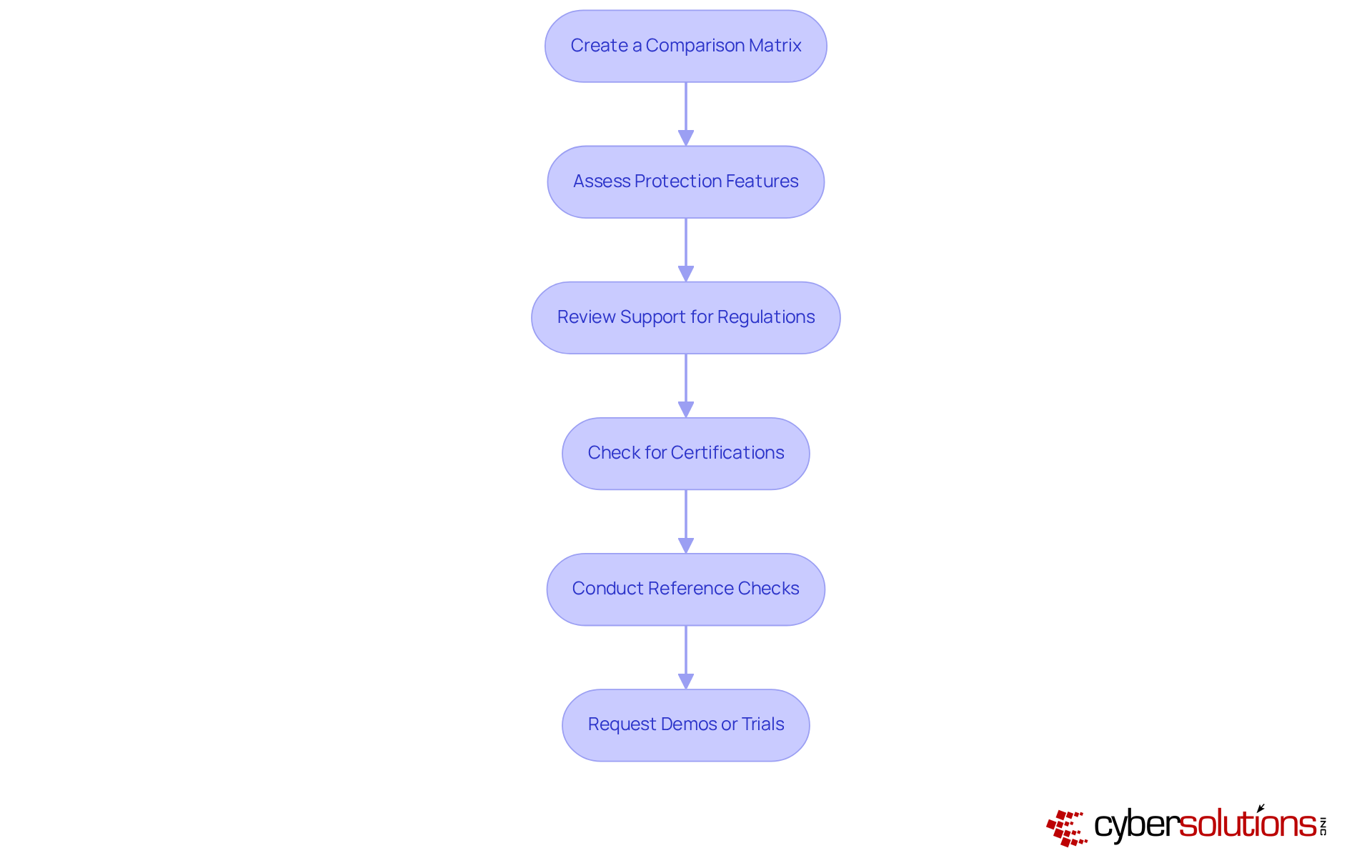
To effectively evaluate and compare SECaaS providers, healthcare organizations must undertake measures to safeguard their operations against increasing cyber threats.
- Create a Comparison Matrix: Develop a matrix that lists potential suppliers alongside their key features, pricing, and service offerings. This visual tool aids in making side-by-side comparisons, allowing for a clearer assessment of options.
- Assess Protection Features: Evaluate the protection features provided by each provider, focusing on critical aspects such as data encryption, incident response times, and threat detection. Given that healthcare organizations faced an average of 1,463 cyberattacks weekly in 2022, strong protective measures are essential. Additionally, consider the importance of application allowlisting, which proactively prevents unauthorized software from executing, thereby reducing vulnerabilities and enhancing overall security.
- Review Support for Regulations: Ensure that the providers can assist with compliance requirements to healthcare, including adherence to HIPAA, breach reporting timelines, regular audits, and reporting. The healthcare industry has ranked highest in data breach expenses for 12 consecutive years, making adherence support essential to reduce financial risks. Effective and thorough documentation, including risk assessments and remediation plans, are crucial for maintaining compliance.
- Check for Certifications: Look for industry certifications such as ISO 27001 or SOC 2 Type II, which indicate a commitment to best practices in safeguarding data. These certifications can offer assurance of the supplier's adherence to high security standards.
- Conduct Reference Checks: Reach out to current or past clients of the suppliers to gather insights about their experiences and the effectiveness of the services offered. Testimonials can illustrate how effectively the provider has acted in practical situations, especially in handling incidents and ensuring adherence to regulations.
- Request demos or trials: Whenever possible, request demonstrations or trial periods to assess the usability and effectiveness of the solutions offered by providers. This practical experience can assist in determining if the service fulfills the specific requirements of the establishment.
Ensure Continuous Support and Compliance Adaptability
In today's rapidly evolving landscape of cybersecurity, it is paramount for healthcare organizations to fortify their defenses and ensure compliance. To achieve continuous support and adaptability, organizations should implement the following strategic steps:
- Establish a service level agreement: A comprehensive SLA with a provider is essential. This agreement must delineate response times, support availability, and performance metrics, ensuring that organizations can depend on timely assistance and accountability.
- Regularly Review security policies: Periodic assessments of security measures and practices are vital for maintaining effectiveness and compliance with changing regulations. This proactive approach not only identifies gaps but also highlights areas for improvement, ensuring that security measures remain aligned with current best practices.
- Stay Informed on regulatory changes: Given the constant evolution of healthcare regulations, organizations must remain vigilant. By staying updated, they ensure that the provider can adjust their services accordingly, thereby upholding regulations and minimizing the risk of penalties.
- Implement training programs: Regular training sessions for staff on security protocols and regulatory requirements are crucial. This fosters a culture of safety within the organization, empowering employees to identify and respond effectively to potential risks.
- Utilize Reporting and Analytics: Leveraging data provided by analytics tools enables organizations to actively monitor their performance and security status. This data-driven approach facilitates proactive adjustments to protective strategies, enhancing overall resilience against cyber threats.
By adopting these strategies, organizations not only meet regulatory requirements but also establish a robust security posture that adapts to the dynamic landscape of cybersecurity.

Conclusion
In the evolving landscape of healthcare, the criticality of selecting the right security-as-a-service (SECaaS) provider is paramount. This strategic decision not only fortifies the security posture of healthcare organizations but also safeguards sensitive patient data against an ever-growing array of cyber threats. By outsourcing cybersecurity needs to specialized providers, healthcare entities can concentrate on their core missions while harnessing advanced technologies and expert knowledge.
The article underscores several essential factors to consider when choosing SECaaS providers, including:
- Their expertise in healthcare security
- Comprehensive service offerings
- Scalability
- Cost-effectiveness
- Compliance with regulatory requirements
Furthermore, effective evaluation methods—such as creating comparison matrices, assessing protection features, and conducting reference checks—are crucial for making informed decisions. Continuous support and adaptability in compliance are vital, as they enable organizations to stay aligned with evolving regulations and bolster overall resilience against cyber threats.
Ultimately, the proactive adoption of security-as-a-service solutions is indispensable for healthcare organizations striving to protect sensitive information and maintain operational efficiency. By prioritizing these considerations and nurturing a culture of security awareness, healthcare entities can not only mitigate risks but also position themselves as leaders in the battle against cybercrime. Embracing SECaaS transcends mere choice; it is a necessary step toward ensuring the safety and integrity of healthcare services in an increasingly digital world.
Frequently Asked Questions
What is Security-as-a-Service (SECaaS) in healthcare?
Security-as-a-Service (SECaaS) is a cloud-based model that allows healthcare organizations to outsource their cybersecurity needs to specialized providers, enabling them to focus on core operations while ensuring the protection of sensitive patient data.
What critical functions does SECaaS provide?
SECaaS encompasses several critical protective functions, including threat detection, incident response, and compliance management.
Why is SECaaS important for healthcare organizations?
SECaaS is important because over 90% of healthcare institutions reported experiencing cyberattacks, which can disrupt patient care. By utilizing SECaaS, organizations can enhance their security posture and ensure compliance with essential regulations.
What regulations must healthcare organizations comply with when using SECaaS?
Healthcare organizations must comply with regulations such as HIPAA, GDPR, PCI-DSS, CMMC, and SOX when utilizing SECaaS.
What trends are driving the adoption of SECaaS in healthcare?
The increasing complexity of cyber threats and the need for robust protective frameworks are driving the growing reliance on SECaaS providers in healthcare.
How does SECaaS help with operational efficiency?
SECaaS helps streamline operations by alleviating the burden of maintaining an in-house security team and allowing healthcare organizations to focus on their primary functions.
Can you provide an example of the effectiveness of SECaaS?
The Scripps Health ransomware attack is an example where the operational disruptions caused by a cyberattack highlighted the need for SECaaS, leading to a significant increase in recovery time.
What services do providers like Cyber Solutions offer to healthcare entities?
Providers like Cyber Solutions offer incident response services that help healthcare entities swiftly identify, contain, and mitigate threats to ensure business continuity.
List of Sources
- Understand Security-as-a-Service in Healthcare
- cybersecuritydive.com (https://cybersecuritydive.com/news/healthcare-cybersecurity-risks-report-fortified/753077)
- U.S. Digital Health Statistics from 2020 to 2025: Everything You Need to Know (https://columncontent.com/digital-health-statistics-2025)
- paloaltonetworks.com (https://paloaltonetworks.com/blog/2025/01/5-trends-shaping-healthcare-cybersecurity-in-2025)
- medcitynews.com (https://medcitynews.com/2025/07/healthcare-cybersecurity-3)
- isaca.org (https://isaca.org/resources/news-and-trends/industry-news/2025/healthcares-growing-threat-landscape)
- Identify Key Criteria for Selecting SECaaS Providers
- 25+ Best Cybersecurity Quotes (https://atera.com/blog/best-cybersecurity-quotes)
- isaca.org (https://isaca.org/resources/news-and-trends/industry-news/2025/healthcares-growing-threat-landscape)
- scribd.com (https://scribd.com/document/503996723/Cybersecurity-Breachesband-Issues-Surrounding-OnlineThreat-Protection)
- Evaluate and Compare SECaaS Providers Effectively
- Navigating Healthcare’s Digital Shift: Strategies to Enhance Cybersecurity and Protect Patient Data (https://kaufmanrossin.com/news/navigating-healthcares-digital-shift-strategies-to-enhance-cybersecurity-and-protect-patient-data)
- statista.com (https://statista.com/statistics/595164/worldwide-security-as-a-service-market-size)
- healthtechmagazine.net (https://healthtechmagazine.net/article/2025/07/prioritizing-cybersecurity-healthcare-measure-patient-safety)
- 3 Ways Healthcare Organizations Can Prepare for New Cybersecurity Requirements (https://honeywell.com/us/en/news/2025/02/3-ways-healthcare-organizations-can-prepare-for-new-cybersecurity-requirements)
- Ensure Continuous Support and Compliance Adaptability
- 38 Must-Know Healthcare Cybersecurity Stats (https://varonis.com/blog/healthcare-cybersecurity-statistics)
- Healthcare Data Breach Statistics (https://hipaajournal.com/healthcare-data-breach-statistics)
- hipaajournal.com (https://hipaajournal.com/healthcare-cybersecurity)
- Healthcare Compliance Trends & Statistics (https://ispartnersllc.com/blog/healthcare-compliance-trends)
- secureframe.com (https://secureframe.com/blog/compliance-statistics)