
In an era where cyber threats are becoming increasingly sophisticated, the demand for robust security solutions is more pressing than ever. Organizations face the dual challenge of protecting sensitive data and ensuring compliance with ever-evolving regulations. This article explores the compelling reasons why partnering with a Security as a Service provider, such as Cyber Solutions Inc., is essential for modern businesses.
What are the key advantages of outsourcing security services?
How can tailored solutions enhance operational resilience while effectively mitigating risks?
As the cybersecurity landscape continues to shift, understanding these dynamics is crucial for any organization striving to safeguard its future.
In today's digital landscape, the importance of cybersecurity in healthcare cannot be overstated. Cyber Solutions Inc. distinguishes itself as a leader by offering personalized protection solutions tailored to the unique needs of various industries, particularly healthcare, finance, manufacturing, and government. This bespoke approach not only ensures compliance with stringent regulatory frameworks but also strengthens defenses against evolving threats. With healthcare entities experiencing a staggering increase in cyberattacks, aligned security measures with operational and financial strategies are imperative.
The impact of cybersecurity on business performance is profound. By focusing on specific vulnerabilities and compliance requirements, organizations can optimize their investment in security, avoiding the pitfalls of generic solutions that fail to address their distinct challenges. Industry leaders assert that personalized security services are critical for effectively mitigating risks and enhancing resilience. Cyber Solutions Inc. offers a comprehensive suite of services, including:
These services are specifically designed for the healthcare sector.
Furthermore, the necessity of rapid incident response is paramount. Cyber Solutions Inc. provides a 24-hour on-site response team, ensuring that threats are contained swiftly and effectively. This layered approach—encompassing endpoint isolation, malware removal, and user training—facilitates a quicker and more thorough recovery, minimizing operational disruption while reinforcing a Zero Trust framework for healthcare organizations.
As the market for cybersecurity services is projected to grow significantly, with a compound annual growth rate (CAGR) of 15.2% through 2029, the demand for customized solutions is increasingly critical. Additionally, the market is expected to reach $69.89 billion in 2029 at a CAGR of 16%, underscoring the necessity of tailored offerings in the evolving cybersecurity landscape.
Cyber Solutions Inc. exemplifies this trend by delivering services that not only protect sensitive data but also enhance overall operational efficiency and cost-effectiveness. Their commitment to understanding the specific needs of clients in regulated sectors positions them as a trusted partner in navigating the complexities of modern cybersecurity challenges.

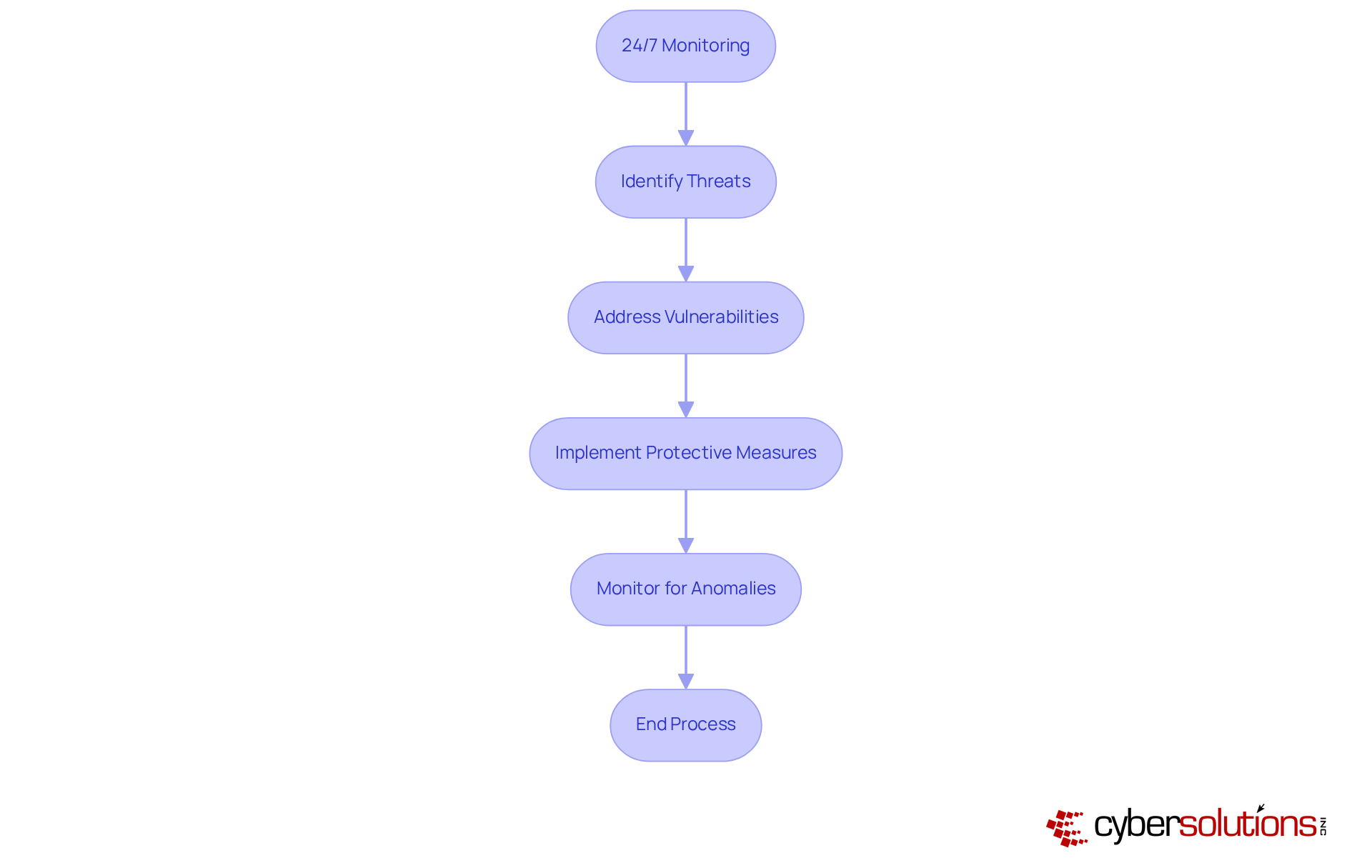
In today's digital landscape, monitoring stands as a cornerstone of effective cybersecurity. With the rise of sophisticated cyber threats, organizations must prioritize security. By leveraging advanced technologies and skilled personnel, potential risks are swiftly identified and addressed. This proactive strategy not only minimizes the risk of data breaches and operational disruptions but also empowers businesses to concentrate on their core activities with peace of mind.
Ongoing surveillance enhances security while providing invaluable insights into the evolving risk environment. Our comprehensive services, including SOC/SIEM and threat intelligence, are designed to detect anomalies and potential vulnerabilities. With instant alerts and real-time insights, organizations can take swift action to prevent downtime or breaches, safeguarding their operations and customer trust.
Implementing security measures allows organizations to effectively mitigate the impact of cyber threats. By shielding your enterprise from ransomware, phishing, and other malware assaults, you can leverage security protocols and customized access controls that scale with your operations. In this ever-changing cyber landscape, prioritizing cybersecurity is not just an option—it's a necessity for maintaining and fostering trust with your customers.
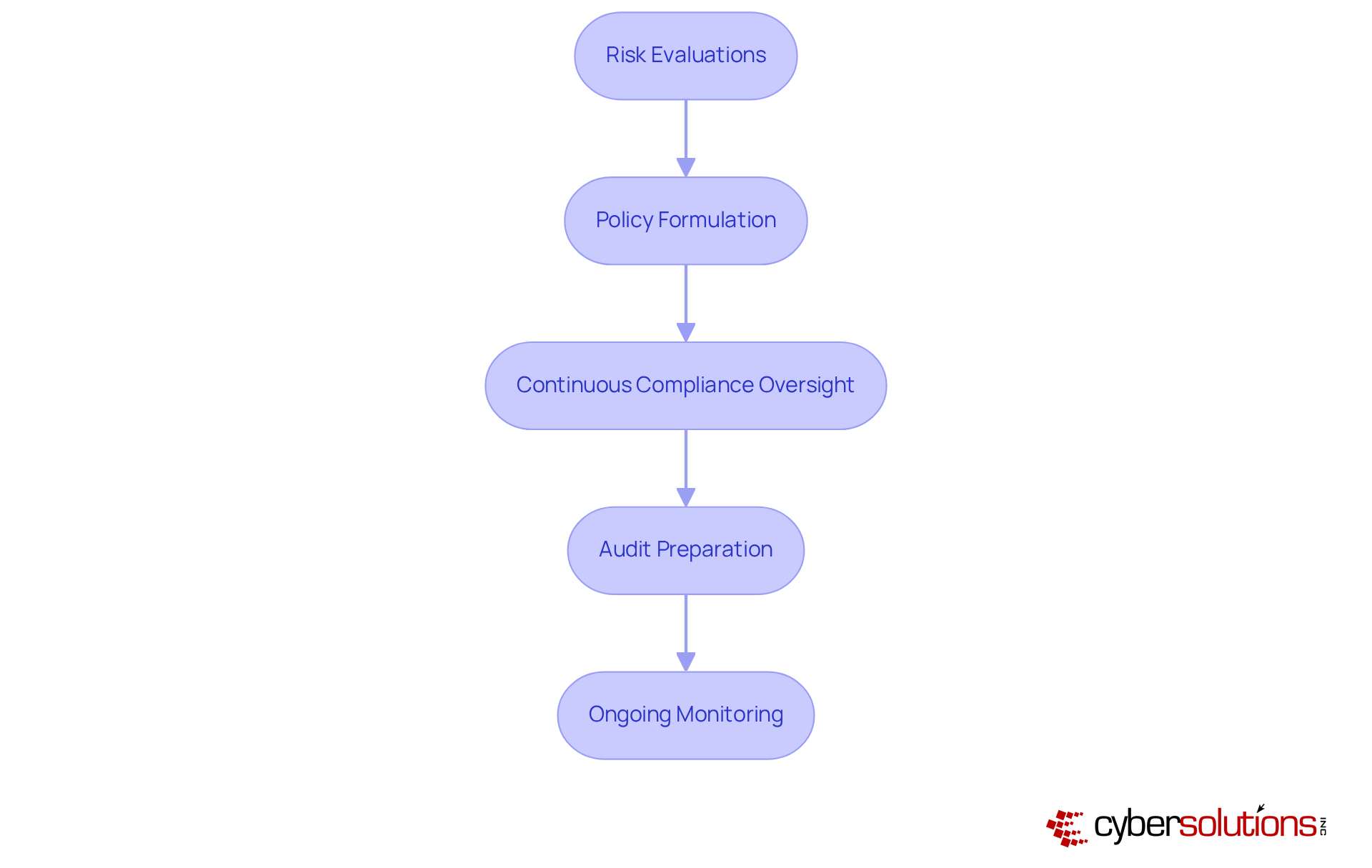
In today's business landscape, compliance management is not just a necessity but a critical component for businesses operating in industries such as healthcare, finance, and legal. Cyber Solutions Inc. stands out by offering comprehensive solutions that simplify the navigation of intricate regulations like HIPAA, PCI-DSS, and GDPR.
Our CaaS encompasses:
This ensures that organizations not only evade penalties but also enhance their operational integrity. This service, which includes audit preparation and ongoing monitoring, guarantees that businesses remain secure and compliant in an ever-evolving regulatory environment.
Furthermore, CaaS empowers small and medium-sized enterprises to access enterprise-level compliance expertise without the prohibitive costs associated with hiring in-house staff.
How prepared is your organization to tackle the challenges of compliance? With our solutions, you can confidently manage compliance and focus on what matters most—your business.
In today's rapidly evolving landscape, advanced risk detection technologies are not just beneficial; they are essential for identifying and mitigating hazards before they escalate into serious incidents. Cyber Solutions employs state-of-the-art tools and methodologies to continuously monitor networks for suspicious activities and potential vulnerabilities. By adopting proactive monitoring strategies, organizations can significantly lower their exposure to risks, fostering a more secure operational environment.
Cybersecurity experts emphasize the importance of advanced threat detection, with a striking 86% endorsing the implementation of proactive measures to enhance protection. In the healthcare sector, effective strategies include:
Notably, research indicates that companies utilizing advanced threat detection can save an average of $3.81 million per breach, underscoring the financial advantages of proactive risk management.
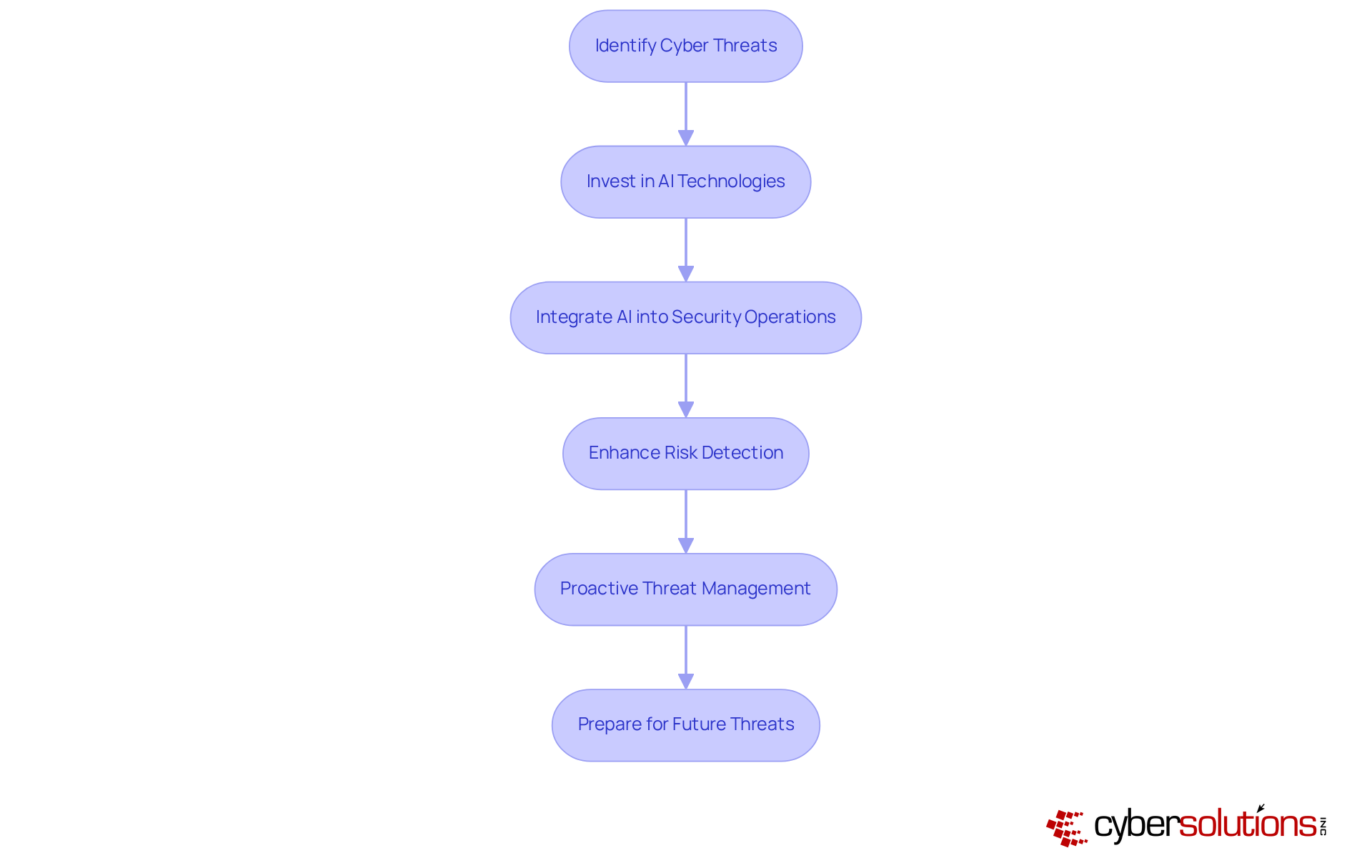
Our case studies reveal that entities adopting these strategies experience a significant enhancement in their security posture. As we approach 2025, the emphasis on cybersecurity will only intensify. Organizations are urged to leverage advanced technologies before they can be exploited. By continuously training AI models with new data, organizations can detect and respond swiftly to emerging threats. This forward-thinking approach not only improves security but also ensures compliance with regulatory standards, ultimately safeguarding the entity's reputation and financial stability.

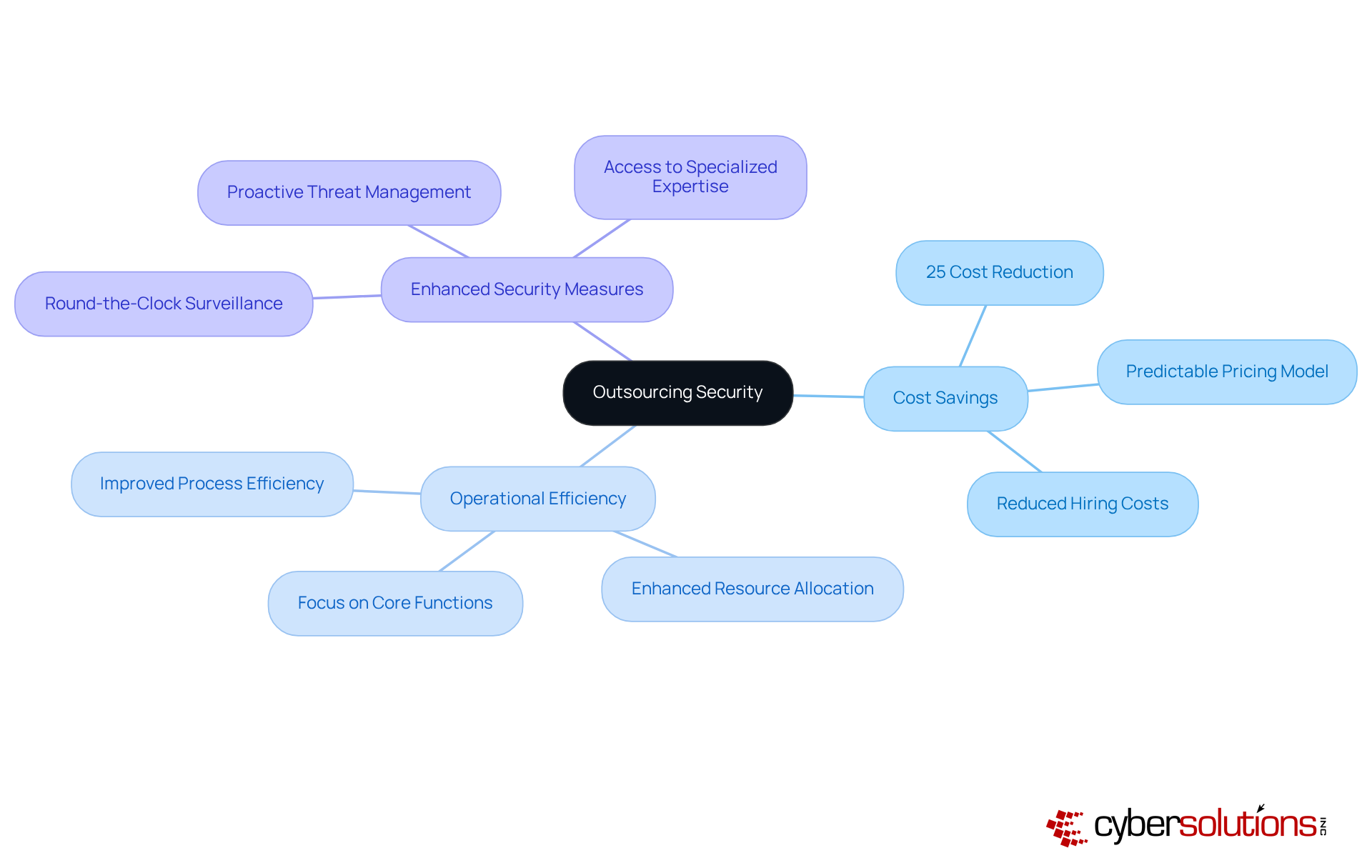
In today's digital landscape, choosing a provider such as Cyber Solutions Inc. is not just a luxury; it is essential for safeguarding companies against escalating threats. By eliminating the need for internal security teams and infrastructure, organizations can redistribute resources more efficiently, allowing for a more strategic allocation of funds.
The services offered by Cyber Solutions enable businesses to budget with confidence, all while receiving extensive support that includes threat monitoring. This strategic approach not only strengthens security measures but also significantly enhances overall operational efficiency. Companies that adopt such models often report improvements in their operational processes, with many experiencing a reduction in costs by an average of 25% compared to managing operations in-house.
This financial predictability empowers businesses to focus on their core functions, fostering innovation and expansion while ensuring security. With round-the-clock network surveillance and immediate notifications, Cyber Solutions guarantees protection, effectively shielding companies from ransomware, phishing, and other malware assaults.
Are you ready to enhance security and reduce costs?
In today's digital landscape, cybersecurity is not just an option; it is a necessity, especially in healthcare. Collaborating with a security as a service provider grants access to a team of experts, which is a vital resource for entities aiming to enhance their security posture. Our services are meticulously designed to rapidly identify, contain, and mitigate threats, ensuring business continuity and minimizing potential damage. These skilled experts employ advanced techniques, equipping organizations to tackle emerging safety challenges head-on.
Consider this: organizations that conduct incident response exercises at least twice a year can save an average of $1.49 million per breach. In stark contrast, companies lacking a dedicated incident response team face breach costs that are $2.66 million higher. This stark difference underscores the importance of having a dedicated team. Furthermore, with 68% of breaches involving human error, and companies with poor internal communication experiencing a 33% increase in breach containment time, it becomes clear that training is essential for effectively mitigating risks.
By leveraging the expertise of Cyber Solutions as a security as a service provider, organizations can significantly improve their overall protective stance, achieving peace of mind as they prepare to manage any cybersecurity risk that may arise. Additionally, our solutions simplify compliance, ensuring your organization meets critical standards like HIPAA, PCI-DSS, and GDPR. As CISA states, "Organizations that train employees quarterly reduce incidents by 60%," reinforcing the importance of ongoing training and expertise in safeguarding against threats.
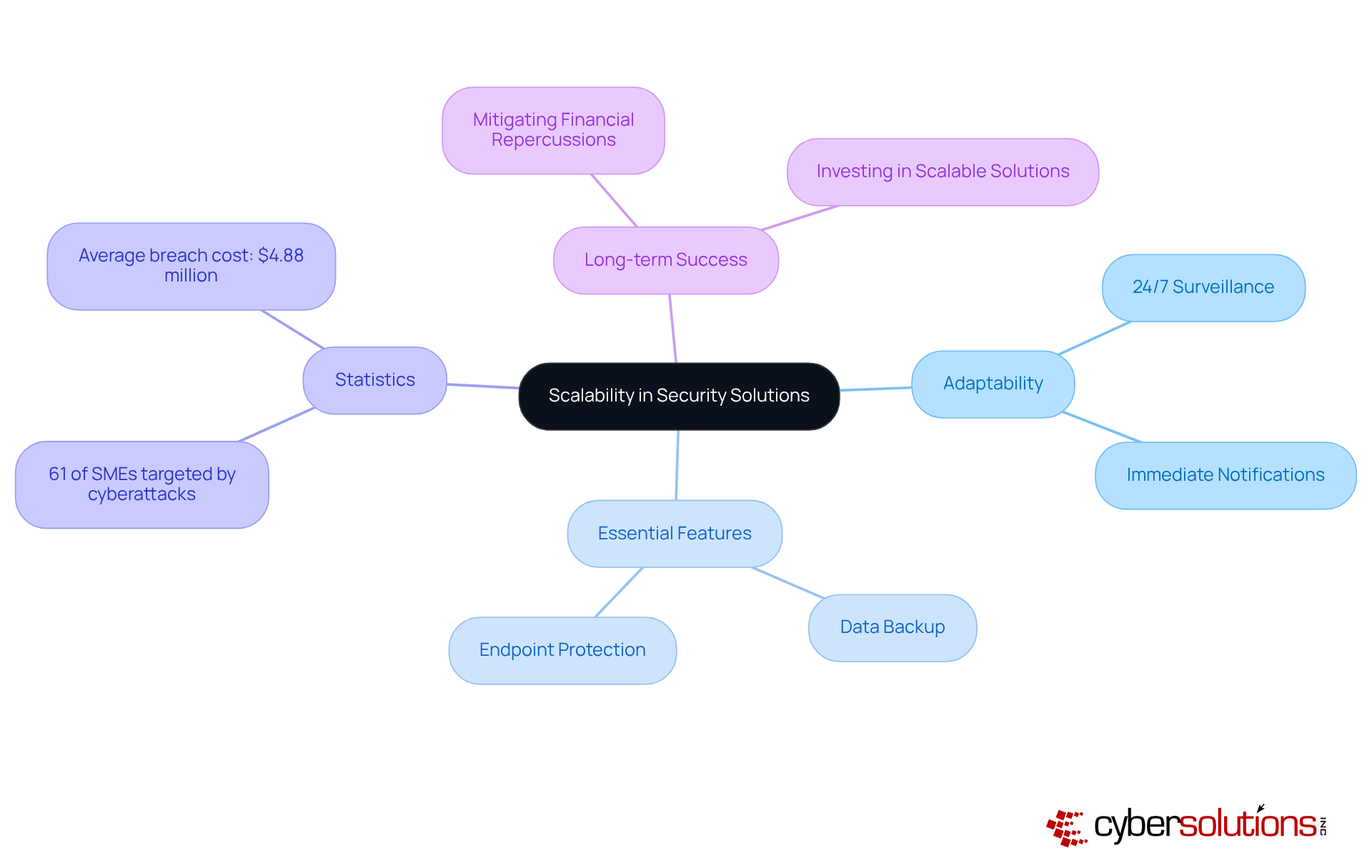
In today's rapidly evolving digital landscape, scalability is not just an option for companies aiming to expand; it is a necessity. Cyber Solutions Inc. recognizes this imperative, providing adaptable protection solutions as a service that evolve alongside shifting corporate requirements. With features such as round-the-clock network surveillance and immediate notifications, organizations can swiftly identify irregularities and potential vulnerabilities. This ensures that suspicious activities are detected and addressed before they escalate into serious threats, providing peace of mind as businesses expand their operations or integrate new technologies.
Moreover, essential features like cost-effective solutions and expert support are vital for maintaining robust security without incurring excessive costs. The urgency of this need is underscored by the alarming statistic that cyberattacks are on the rise. This highlights the critical importance of security services provided by a trusted provider, tailored to the unique challenges faced by organizations today. Industry leaders emphasize that proactive measures are essential, particularly when utilizing a comprehensive security strategy; as Michael Coates aptly notes, the objective is to manage risks wisely rather than eliminate them entirely.
This adaptability not only fosters long-term business success but also mitigates the impact of security breaches. By investing in scalable solutions, entities can adeptly navigate the complexities of growth while safeguarding their critical assets. Are you prepared to fortify your organization against the ever-present threat of cyberattacks? The time to act is now.
In today's rapidly evolving landscape of cyber risks, organizations must harness advanced technology to safeguard their operations. Cyber Solutions Inc. is at the forefront, prioritizing investment in cybersecurity innovations to provide clients with optimal protection. By leveraging technologies such as artificial intelligence (AI) and machine learning, the company significantly enhances its risk detection and response capabilities. For instance, AI can reduce risk detection times from days to mere seconds, showcasing a remarkable improvement in efficiency. Organizations employing AI have reported a 60% enhancement in identifying potential breaches compared to traditional methods.
As we approach 2025, integrating AI into cybersecurity is becoming increasingly essential. A staggering 93% of businesses expect to face daily attacks fueled by AI, highlighting the urgent need for proactive measures. Additionally, AI systems are capable of processing vast amounts of data in real time, utilizing predictive analytics to identify risks before they materialize. This capability is vital, especially considering that the global average cost of a data breach has soared to a record high of $4.88 million, underscoring the importance of effective security measures.
Technology leaders are acutely aware of AI's transformative potential in cybersecurity. As one specialist noted, 'AI can manage enormous volumes of data in real time, employing predictive analytics to recognize potential threats before they arise.' This sentiment resonates throughout the industry, with 70% of cybersecurity experts deeming AI essential in uncovering previously overlooked risks. By embracing these technologies, Cyber Solutions Inc. ensures that businesses are not only equipped to tackle current challenges but are also prepared to navigate the complexities of future cyber threats.
In today's digital landscape, the importance of cybersecurity cannot be overstated. Cyber Solutions Inc. recognizes that each industry encounters distinct cybersecurity challenges, particularly in the healthcare sector, where the average cost of a data breach is significant. By providing tailored security solutions, the company guarantees that healthcare entities receive focused safeguards designed to efficiently tackle their specific vulnerabilities.
This customized approach not only enhances protection but also ensures compliance with regulations and best practices, offering clients a robust framework that meets their unique needs. For instance, solutions such as:
are crucial for assisting healthcare organizations in navigating these complexities while adhering to regulations like HIPAA. Furthermore, application allowlisting is essential for preventing unauthorized software from executing, thereby minimizing vulnerabilities and risks.
As industry experts emphasize, cybersecurity is not merely a product; it is a continuous process. This underscores the necessity for organizations to adopt proactive measures. As the cybersecurity landscape evolves, the importance of customized solutions becomes increasingly clear. By implementing these tailored strategies, businesses can safeguard their digital assets while maintaining operational efficiency. Are you prepared to fortify your organization's defenses against evolving threats?

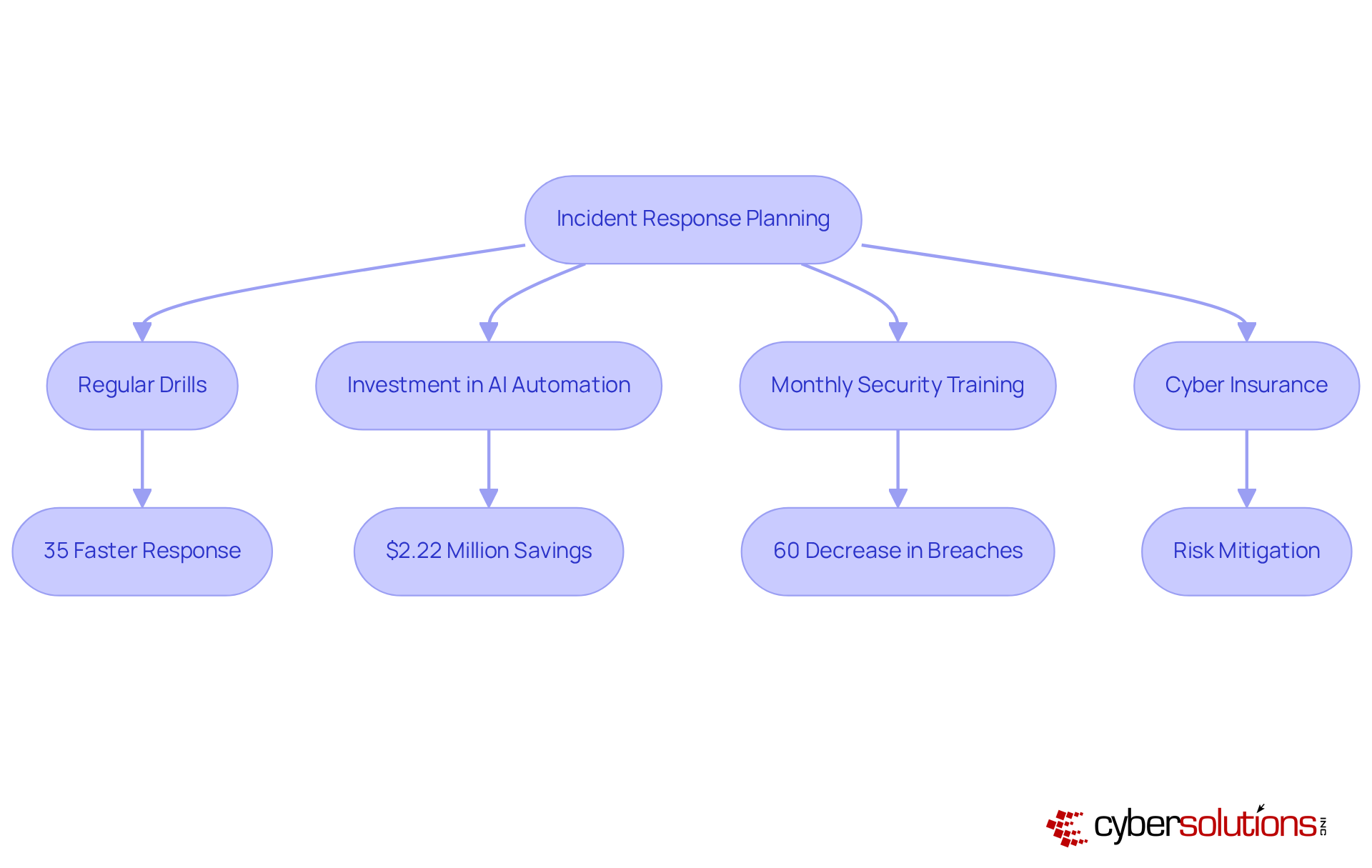
Effective incident response is crucial for a robust security posture. Cyber Solutions Inc. excels in its role as a security provider by developing comprehensive plans that outline precise steps to take in the event of a security breach. This proactive approach is vital; organizations that implement incident response plans can significantly reduce recovery times, which average 258 days for detection and containment. Notably, companies that manage to contain breaches in under 30 days can save over $1 million compared to those requiring more time.
Experts assert that timely and organized responses can mitigate damage and enhance recovery efforts. For instance, organizations that conduct regular drills can respond 35% faster to incidents, underscoring the value of preparedness. Furthermore, 88% of firms with incident response plans also have security measures in place, indicating a multi-layered approach to protection that further diminishes risks.
Real-world examples underscore the effectiveness of these strategies. Companies utilizing AI-driven automation for incident response protection have reported significant improvements, attributable to improved response times and containment capabilities. Additionally, organizations engaging in monthly security training can decrease the likelihood of breaches by 60%, emphasizing the significance of employee awareness in minimizing damage.
As we approach 2025, the evolving landscape of cyber risks makes comprehensive incident response planning even more critical for a business's resilience. By investing in these strategies, businesses not only safeguard sensitive data but also ensure operational continuity amid the increasing threat of cyber attacks.
In the rapidly evolving digital landscape, the importance of selecting a Security as a Service (SaaS) provider like Cyber Solutions Inc. is paramount. Tailored solutions that cater to the distinct needs of various industries, particularly healthcare, empower organizations to significantly strengthen their defenses against cyber threats while ensuring compliance with regulatory frameworks. This strategic partnership not only enhances security but also optimizes operational efficiency, enabling businesses to concentrate on their core activities with confidence.
The article underscores several key advantages of engaging a Security as a Service provider:
These are essential components that empower organizations to proactively mitigate risks. Additionally, the significance of compliance management, incident response planning, and access to cybersecurity expertise highlights the multifaceted benefits of outsourcing security services. As the cybersecurity landscape continues to evolve, the demand for scalable and cost-effective solutions becomes increasingly vital for businesses striving to safeguard their assets.
As organizations navigate the complexities of modern cybersecurity challenges, adopting a proactive and tailored approach is crucial. The insights provided by Cyber Solutions Inc. illustrate the necessity of investing in advanced security measures and expert knowledge to defend against emerging threats. By prioritizing cybersecurity and leveraging the advantages of Security as a Service, businesses can not only enhance their resilience but also secure their future in an increasingly digital world. The time to act is now—fortify defenses and embrace the benefits of tailored security solutions to thrive amidst evolving cyber risks.
What services does Cyber Solutions Inc. provide?
Cyber Solutions Inc. offers tailored security solutions including endpoint protection, hazard detection, data encryption, and secure access controls, specifically designed for industries such as healthcare, finance, manufacturing, and government.
Why is cybersecurity particularly important in the healthcare sector?
Cybersecurity is critical in healthcare due to a significant increase in hacking-related breaches, with a reported 256% rise. Robust protective measures are essential to ensure compliance with regulations and to safeguard sensitive patient data.
How does Cyber Solutions Inc. approach incident response?
Cyber Solutions Inc. provides a 24-hour on-site response team to swiftly contain threats. Their layered approach includes endpoint isolation, malware removal, and user training, which facilitates quicker recovery and minimizes operational disruption.
What is the projected growth of the security as a service market?
The security as a service market is projected to grow at a compound annual growth rate (CAGR) of 15.2% through 2029, while the Managed Security Services market is expected to reach $69.89 billion in 2029 at a CAGR of 16%.
What role does 24/7 monitoring play in cybersecurity?
24/7 monitoring is essential for continuous threat protection, allowing organizations to identify and address risks in real-time. This proactive strategy minimizes the risk of data breaches and operational disruptions.
What are the components of Cyber Solutions Inc.'s 24/7 monitoring services?
Their 24/7 monitoring services include SOC/SIEM and Data Backup Solutions, which detect anomalies and potential vulnerabilities while providing instant alerts and real-time insights.
What is Compliance as a Service (CaaS) offered by Cyber Solutions Inc.?
CaaS is a comprehensive solution that helps businesses navigate complex regulations such as HIPAA, PCI-DSS, and GDPR. It includes risk evaluations, policy formulation, and continuous compliance oversight.
How does Compliance as a Service benefit small and medium-sized enterprises?
CaaS enables small and medium-sized enterprises to access enterprise-level compliance expertise without the high costs associated with hiring in-house compliance staff, helping them remain secure and compliant.
How can organizations prepare for regulatory challenges with Cyber Solutions Inc.?
Organizations can leverage Cyber Solutions' CaaS to simplify compliance management, ensuring they are well-prepared to navigate regulatory challenges while focusing on their core business activities.