
In an era where digital threats are more pronounced than ever, organizations are compelled to seek robust solutions to protect their IT infrastructure. Fully managed IT support stands out as a strategic partner, providing a comprehensive framework that not only boosts operational efficiency but also strengthens cybersecurity defenses. Yet, with an abundance of options at their disposal, how can leaders accurately assess the true value of fully managed IT services amidst this overwhelming landscape? This article explores the key benefits of fully managed IT support, equipping decision-makers with essential insights to effectively navigate today’s intricate digital environment.
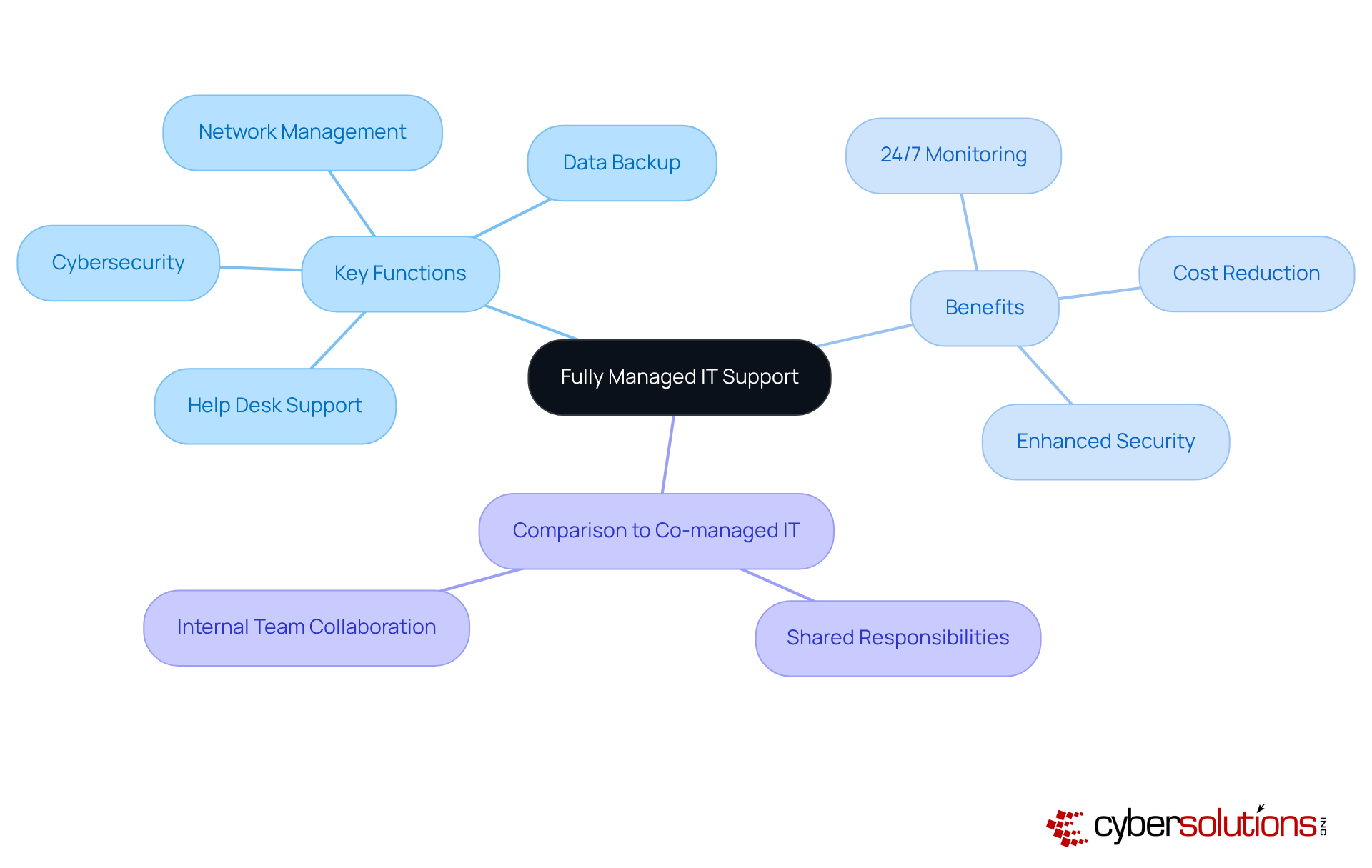
represents a comprehensive framework in which an external provider assumes full responsibility for an organization's IT infrastructure and operations. This model encompasses a broad spectrum of functions, including:
A critical component of this approach is monitoring and alert systems, which proactively detect anomalies and potential vulnerabilities. This ensures that suspicious activities are addressed before they escalate into serious threats. The primary objective is to facilitate seamless integration and oversight of all IT functions, allowing organizations to concentrate on their core activities without the burden of daily IT management.
In contrast, hybrid models involve collaboration between the internal IT team and an external provider, distributing responsibilities between the two. Notably, nearly 90% of small and medium-sized enterprises (SMBs) currently utilize or consider employing IT services, highlighting the growing reliance on these solutions. Organizations across various sectors, such as healthcare and finance, have successfully implemented fully supervised IT assistance to enhance operational efficiency, underscoring its significance in today's complex digital landscape.
Furthermore, organizations leveraging fully managed IT support can reduce total IT costs by 20-30%, making it not only a strategic choice but also a financially prudent one. By incorporating cybersecurity measures, organizations are protected against ransomware, phishing, and other malware attacks, maximizing ROI through tailored IT and cybersecurity services, including:
In today's rapidly evolving digital landscape, the importance of managed IT support cannot be overstated. Organizations are grappling with significant challenges related to cybersecurity, data management, and the pursuit of operational efficiency. The complexity of modern IT environments, coupled with the swift pace of technological advancements, complicates effective IT management. This is where fully managed IT support emerges as a vital solution, providing businesses access to expert guidance, cutting-edge technologies, and comprehensive security measures.
This service model not only bolsters cybersecurity through a layered approach—such as application allowlisting, which proactively prevents malware and unauthorized software from executing—but also ensures adherence to industry regulations like HIPAA, PCI-DSS, and GDPR. Quick response strategies, including round-the-clock on-site assistance, empower organizations to manage threats rapidly and recover more thoroughly. For instance, having an IT support team on-site within a day has proven crucial in minimizing damage and enhancing recovery efforts.
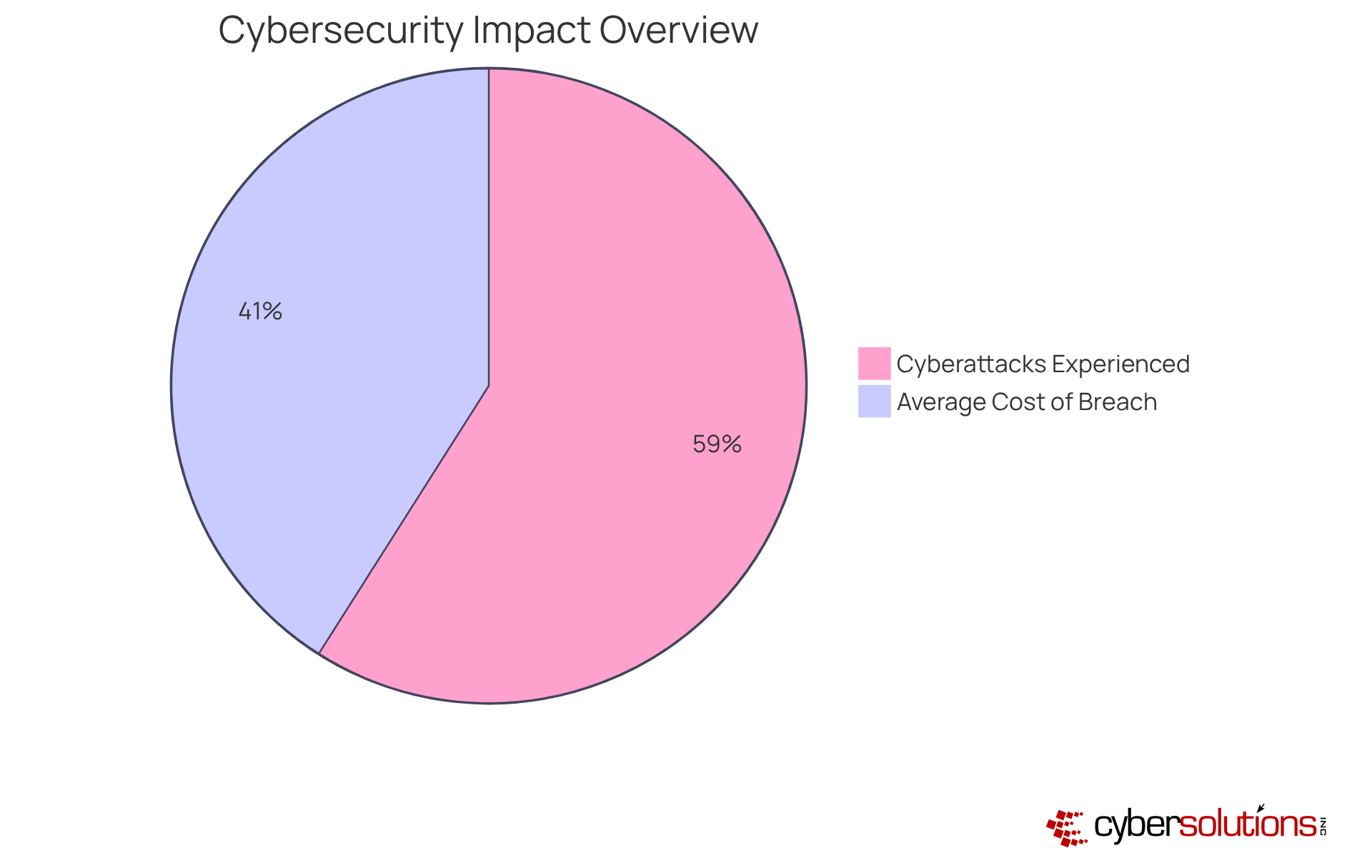
By incorporating these extensive resources, organized IT assistance becomes an essential element of a successful corporate strategy. Statistics reveal that:
By adopting a proactive strategy with managed IT support, organizations can significantly reduce these risks and improve their overall security framework.
Key components of fully managed IT support include:
These components work synergistically to create a holistic IT management solution, which includes fully managed IT support, that enhances operational efficiency and security, positioning organizations to thrive in a rapidly evolving digital landscape.

The advantages of fully managed IT support are substantial and transformative:
These compelling benefits position organizations aiming to enhance their IT capabilities while minimizing risks and costs to choose fully managed IT support as a strategic option.

Fully managed IT support stands as a strategic imperative for organizations aiming to streamline their IT operations and bolster security. By outsourcing IT management to specialized providers, businesses can concentrate on their core missions while reaping the benefits of comprehensive support that spans everything from network management to cybersecurity. This approach alleviates the burden of daily IT tasks, positioning companies to thrive in an increasingly complex digital landscape.
The multifaceted advantages of fully managed IT support are significant. Organizations can achieve substantial cost savings, with reductions in overhead expenses and predictable budgeting. Enhanced security measures are crucial in protecting against the rising tide of cyber threats, while continuous monitoring and expert guidance ensure operational resilience. Moreover, the scalability of managed IT services enables organizations to adapt swiftly to changing demands, fostering growth and innovation.
In light of these insights, embracing fully managed IT support emerges as a necessity for businesses striving to enhance their operational efficiency and security posture. As cyber threats continue to evolve and regulatory landscapes grow more complex, investing in a robust IT support framework is not merely a choice—it is essential. Organizations are encouraged to explore the transformative potential of fully managed IT services to safeguard their future and drive sustainable success.
What is fully managed IT support?
Fully managed IT support is a comprehensive framework where an external provider takes full responsibility for an organization's IT infrastructure and operations, including network management, cybersecurity, help desk support, and data backup.
What are the key functions included in fully managed IT support?
Key functions include network management, cybersecurity, help desk support, and data backup.
How does 24/7 network monitoring contribute to fully managed IT support?
24/7 network monitoring and alert systems proactively detect anomalies and potential vulnerabilities, allowing suspicious activities to be addressed before they escalate into serious threats.
What is the difference between fully managed IT support and co-managed IT solutions?
Fully managed IT support involves an external provider taking full responsibility for IT functions, while co-managed IT solutions involve collaboration between an internal IT team and an external provider, distributing responsibilities between the two.
What percentage of small and medium-sized enterprises (SMBs) use or consider using IT services?
Nearly 90% of small and medium-sized enterprises (SMBs) currently utilize or consider employing IT services.
In which sectors have organizations successfully implemented fully managed IT support?
Organizations in various sectors, such as healthcare and finance, have successfully implemented fully managed IT support to enhance operational efficiency and security.
How can organizations benefit financially from fully managed IT support?
Organizations leveraging Managed Service Providers (MSPs) can reduce total IT costs by 20-30%, making fully managed IT support a financially prudent choice.
What cybersecurity services are included in fully managed IT support?
Cybersecurity services include comprehensive firewall and network security solutions, as well as tailored IT and cybersecurity services such as SOC/SIEM, Office 365 Support, and Endpoint Protection.