
Understanding compliance in business transcends mere rule-following; it embodies a strategic framework that can significantly define an organization's success. As companies navigate an increasingly complex regulatory landscape, the importance of compliance becomes paramount, influencing everything from operational efficiency to public trust.
But how can businesses transform compliance from a legal obligation into a competitive advantage that fosters growth and resilience? This article explores the multifaceted role of compliance in business, examining its evolution, key components, and the tangible benefits it offers in today’s dynamic environment.
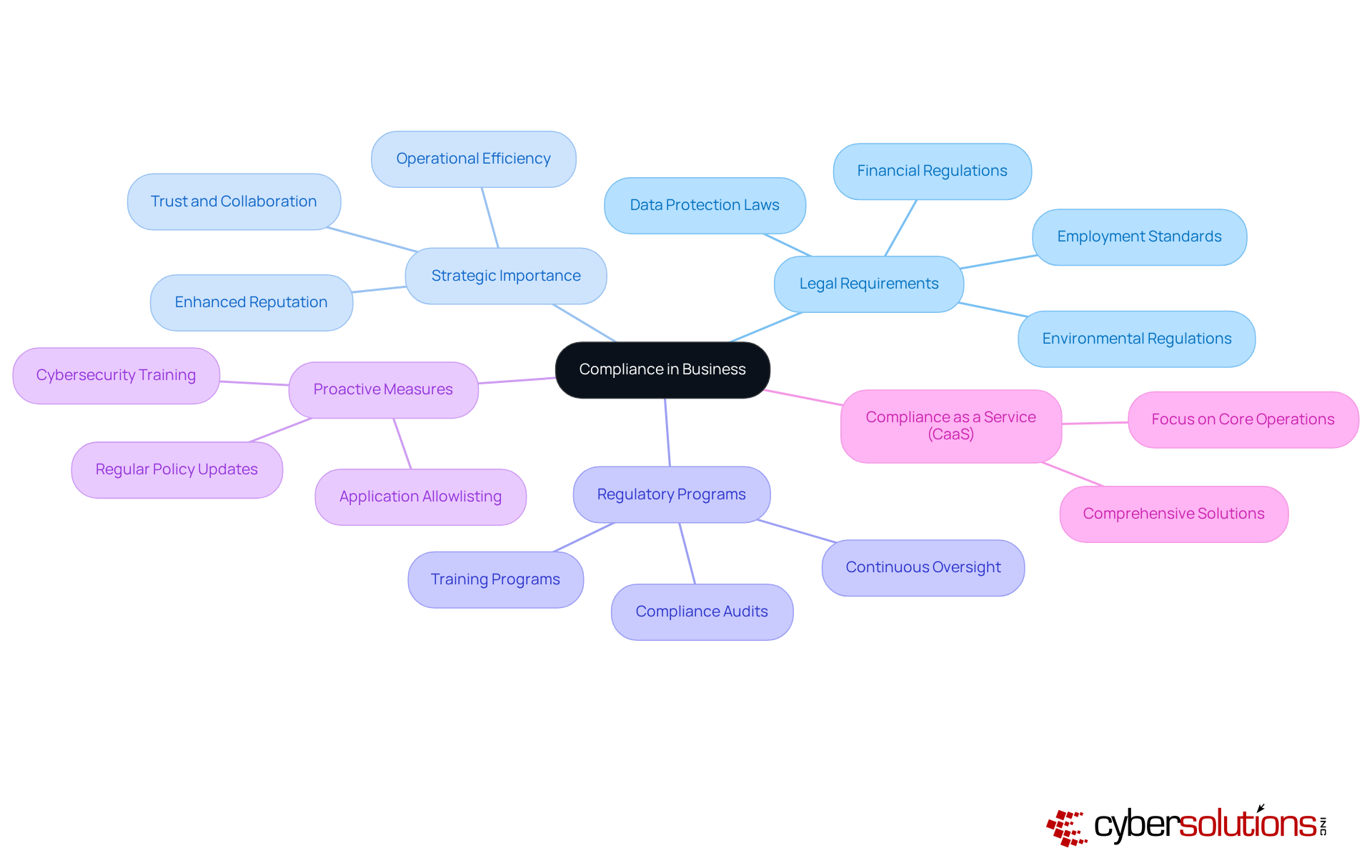
Compliance meaning in business is crucial, representing the adherence to laws, rules, guidelines, and specifications that govern operations. This encompasses a wide range of areas, including legal requirements, data protection laws, employment standards, and environmental regulations. Organizations must align their practices with these legal requirements to avoid penalties and maintain a good reputation.
Beyond being a legal obligation, compliance serves as a strategic imperative that can significantly enhance risk management and operational efficiency. For instance, companies that prioritize compliance can cultivate a culture of trust and collaboration, essential for successful partnerships.
Statistics reveal that companies with robust regulatory programs encounter fewer legal issues and enjoy a more favorable public image. Moreover, continuous oversight is vital for adapting to evolving regulations and sustaining compliance over time.
Cybersecurity plays a pivotal role in this process by proactively preventing unauthorized software from executing, thereby reducing the attack surface and minimizing vulnerabilities. This proactive approach not only aids in meeting regulatory requirements like HIPAA, PCI DSS, and GDPR but also bolsters overall cybersecurity posture.
Compliance as a Service (CaaS) offers organizations comprehensive solutions to fulfill regulatory requirements, ensuring they remain compliant while focusing on their core operations.
Ultimately, businesses act as responsible and ethical entities in their respective markets, which contributes to long-term success.
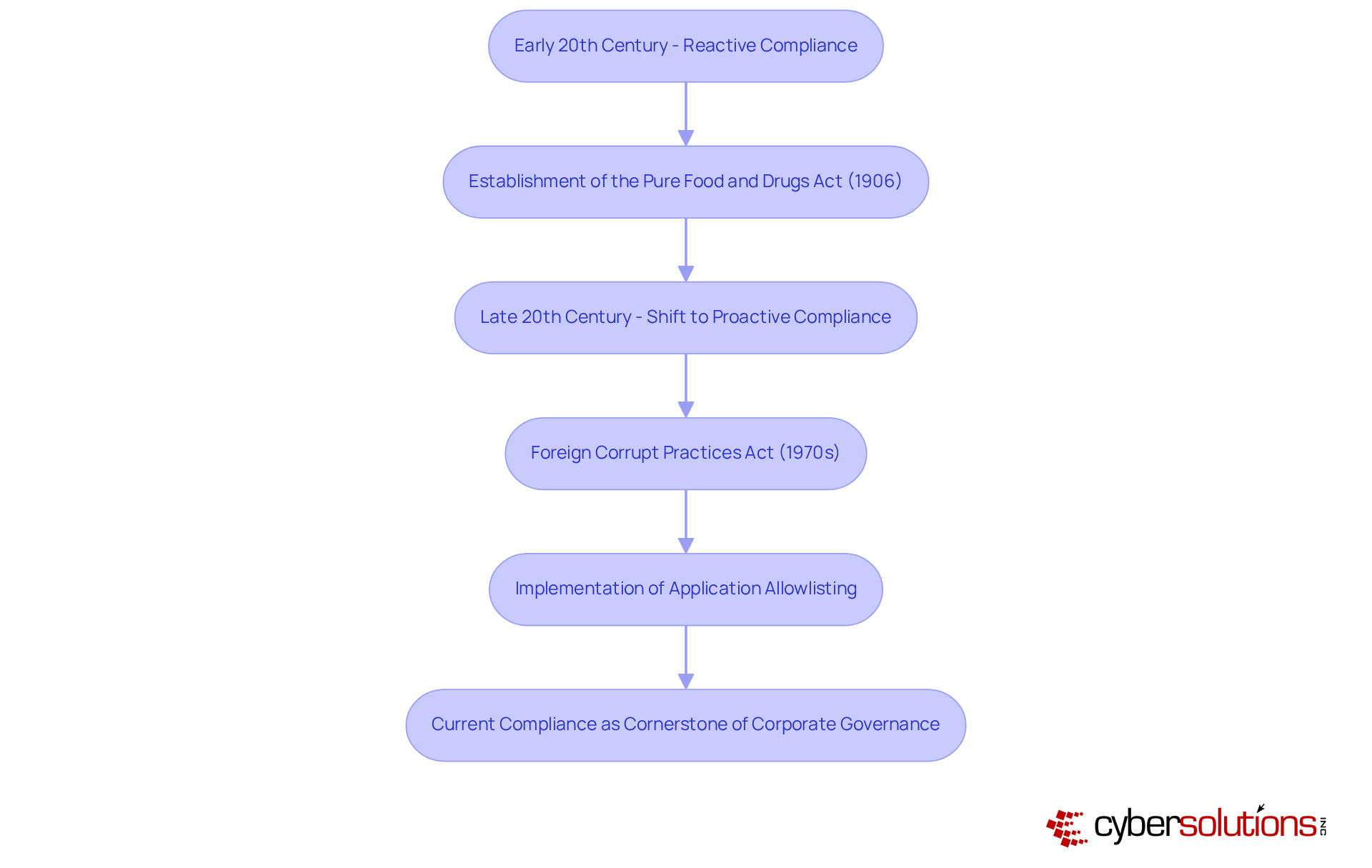
The roots of adherence can be traced back to the early 20th century, when businesses faced increasing scrutiny from regulatory bodies. Initially, adherence was largely reactive, focused on evading penalties rather than fostering a culture of accountability. This approach was exemplified by the establishment of the Pure Food and Drugs Act of 1906, which sought to protect consumers and ensure public safety.
As industries expanded and regulations became more intricate, the adherence landscape began to transform. By the late 20th century, particularly following the introduction of the Foreign Corrupt Practices Act in the 1970s, adherence evolved into a proactive strategy. Organizations started to prioritize compliance, recognizing that a robust compliance program could enhance their reputation and operational resilience.
The implementation of application allowlisting serves as a prime example of this shift in contemporary regulations. By preventing unauthorized or harmful applications from executing, entities can significantly reduce their attack surface while meeting stringent regulatory requirements such as data protection laws.
The 1991 federal sentencing guidelines further solidified this shift, establishing essential components for compliance programs and encouraging organizations to adopt a proactive approach. Today, adherence to regulations stands as a critical factor, influencing decision-making processes and shaping organizational culture.
Experts emphasize that the effectiveness of a regulatory program hinges on its alignment with a company's unique culture, highlighting the need for continuous adjustments to address evolving regulatory demands. As adherence continues to progress, organizations must harness advanced technologies, such as application allowlisting, to navigate the complexities of modern regulatory environments.
Business adherence encompasses several critical elements: regulatory adherence, operational adherence, and ethical adherence. Regulatory frameworks established by governmental entities, such as the guidelines for data protection and the regulations for healthcare. Conversely, operational adherence pertains to the internal policies and procedures that ensure efficient and ethical practices, aligning with organizational goals and industry standards. Ethical guidelines urge businesses to uphold ethical standards in their operations.
To effectively implement these components, organizations must adopt and allocate appropriate resources. For instance, a robust operational regulatory approach might involve:
Current trends reveal a growing concern, with 32% of organizations reporting compromised service account credentials—underscoring the necessity for stringent regulatory measures. As companies navigate the complexities of adherence, integrating ethical considerations into their understanding of compliance and governance becomes increasingly vital. This comprehensive approach not only protects against legal repercussions but also cultivates trust and transparency with stakeholders, ultimately contributing to organizational success.

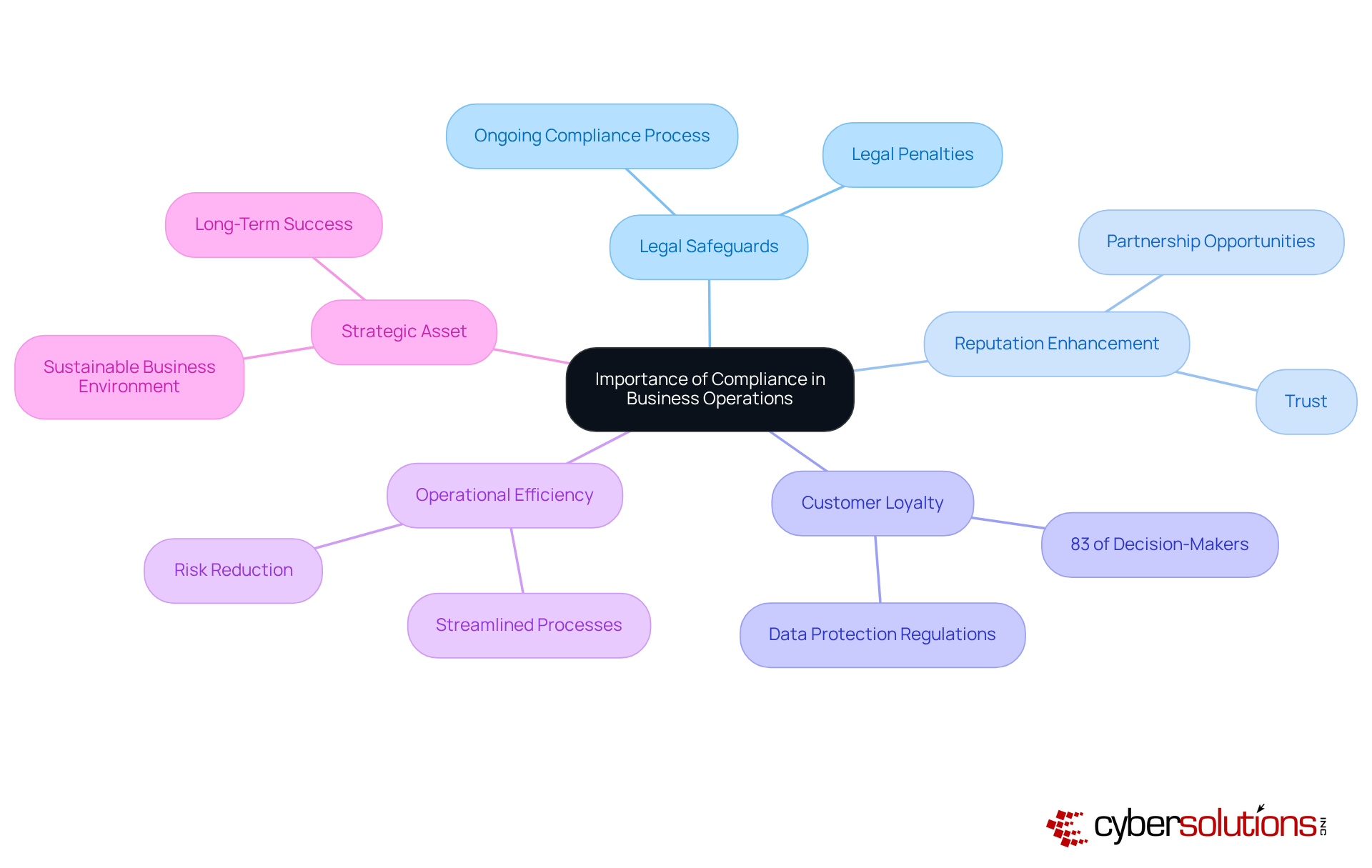
The concept of compliance plays a pivotal role in modern business operations, underscoring its significance for organizations today. It safeguards against substantial risks, which can severely impact financial stability. Moreover, compliance fosters trust among customers, investors, and stakeholders alike.
For instance, companies prioritizing compliance often experience increased customer loyalty; studies reveal that 83% of decision-makers incorporate regulations into their strategic planning. Furthermore, robust regulatory programs streamline processes, leading to improved efficiency.
Ultimately, the importance of compliance transcends mere legal obligations; it is a framework that cultivates a sustainable and ethical business environment, positioning organizations for long-term success.
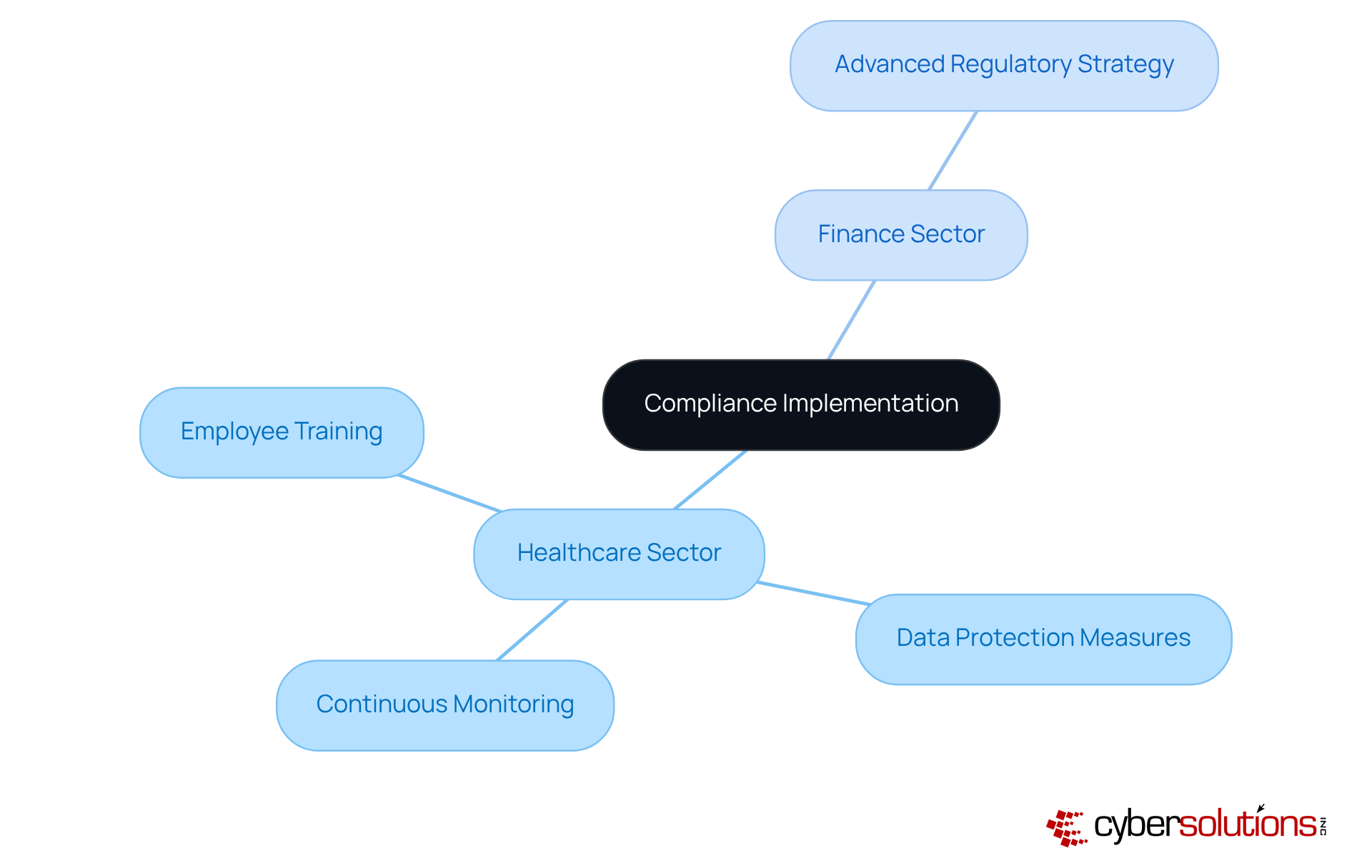
In the healthcare sector, adherence to regulations is paramount. Consider a notable instance where a healthcare provider established a compliance program that included:
This proactive stance not only allowed the organization to evade penalties but also significantly bolstered its reputation. Similarly, in the finance sector, a bank adopted an innovative approach by leveraging technology to enhance compliance. This initiative resulted in a marked reduction in the risk of non-compliance with financial regulations.
These instances highlight the necessity for tailored strategies that align with the unique requirements of each industry, ultimately fostering a culture of compliance and trust, reflecting the compliance meaning in business.
Understanding the significance of compliance in business is essential for organizations aiming to thrive in a complex regulatory environment. Compliance is not merely a legal requirement; it is a strategic asset that can enhance operational efficiency, foster trust, and ultimately contribute to long-term success. By integrating compliance into the core of business practices, companies can transform potential challenges into opportunities for growth and resilience.
Throughout the article, key points have been highlighted, including:
Real-world examples illustrate how tailored compliance strategies in sectors like healthcare and finance not only mitigate risks but also enhance reputation and stakeholder trust.
Reflecting on the broader implications, it becomes clear that prioritizing compliance is vital for sustainable business practices. As organizations navigate the complexities of modern regulations, embracing compliance as a fundamental aspect of their operations will not only safeguard against legal repercussions but also cultivate a culture of accountability and transparency. Businesses are encouraged to view compliance not just as a necessity but as a powerful driver of competitive advantage in today's dynamic landscape.
What does compliance mean in business?
Compliance in business refers to the adherence to laws, rules, guidelines, and specifications that govern operations, including financial regulations, data protection laws, employment standards, and environmental regulations.
Why is compliance important for organizations?
Compliance is crucial for organizations to avoid penalties, maintain operational integrity, enhance their reputation, and improve operational efficiency. Companies that prioritize compliance can foster a culture of trust and collaboration, essential for successful partnerships.
How does compliance impact a company's public image?
Organizations with robust regulatory programs tend to encounter fewer legal issues and enjoy a more favorable public image, which contributes to their overall reputation in the market.
What role does application allowlisting play in compliance?
Application allowlisting helps prevent unauthorized software from executing, reducing vulnerabilities and aiding in meeting regulatory requirements like HIPAA, PCI-DSS, and GDPR, while also enhancing overall cybersecurity.
What is Compliance as a Service (CaaS)?
Compliance as a Service (CaaS) provides organizations with comprehensive solutions to meet regulatory requirements, allowing them to focus on their core operations while ensuring compliance.
How has the approach to compliance evolved over time?
Initially, compliance was reactive, focused on evading penalties. Over time, especially after the introduction of the Foreign Corrupt Practices Act in the 1970s, it evolved into a proactive strategy emphasizing risk management and ethical practices.
What historical legislation influenced the evolution of compliance?
The Pure Food and Drugs Act of 1906 and the Foreign Corrupt Practices Act of the 1970s were significant in shaping the compliance landscape, encouraging organizations to adopt proactive compliance strategies.
Why is continuous oversight important for compliance?
Continuous oversight is essential for adapting to evolving regulations and sustaining compliance over time, ensuring that organizations remain aligned with current legal requirements.
How does compliance contribute to long-term success for companies?
Effective compliance mitigates risks and positions companies as responsible and ethical entities, which can lead to enhanced reputation, operational resilience, and long-term success in their respective markets.