
In today’s digital landscape, cybersecurity threats loom large, posing significant risks to the financial integrity of organizations. This reality makes it imperative for CFOs to adopt robust protective measures. Managed cybersecurity services present a strategic advantage, equipping financial leaders with the essential tools and expertise to safeguard sensitive data while ensuring compliance with industry regulations. As the frequency of cyberattacks escalates and threats evolve, CFOs are faced with the pressing question: how can they effectively navigate this complex terrain and select the right services to enhance their defenses? This article delves into seven essential managed cybersecurity services that every CFO should consider to strengthen their organization’s security posture and mitigate risks.
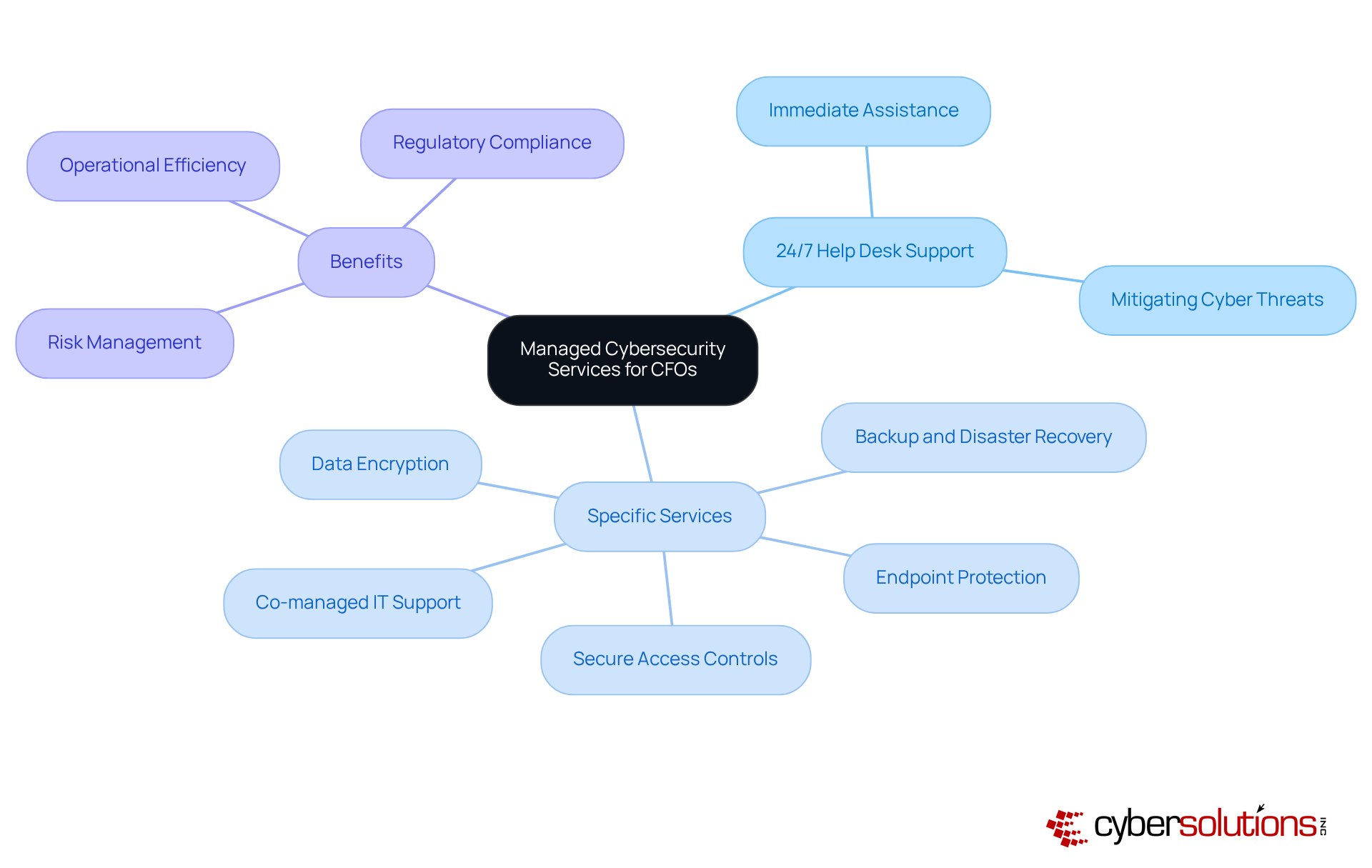
In today's digital landscape, the importance of cybersecurity cannot be overstated, particularly for CFOs in sectors such as healthcare, finance, manufacturing, and government. Cyber Solutions Inc. provides a strong array of services that are specifically tailored to meet the unique needs of these leaders. Central to these offerings is help desk support, which ensures immediate assistance in addressing IT issues and mitigating potential threats. This continuous support is crucial, especially considering that 80% of organizations faced payment fraud last year, underscoring the urgent need for vigilant cybersecurity measures.
Beyond help desk support, Cyber Solutions provides a comprehensive array of services, including:
Together, these services enhance operational efficiency, allowing financial leaders to concentrate on strategic initiatives without the distraction of IT complexities. The integration of cybersecurity measures not only protects sensitive information but also ensures compliance—an increasing concern for over 35% of financial executives who identify regulatory adherence as a top priority.
The successful implementation of cybersecurity protocols in healthcare facilities has proven effective in preventing incidents. By leveraging these comprehensive services, financial leaders can foster a secure environment that bolsters their organization's financial health and operational resilience. To maximize the benefits of these services, it is essential for financial leaders to continually assess risks and ensure alignment with evolving threats.
In today's rapidly evolving digital landscape, the importance of cybersecurity cannot be overstated. Cyber Solutions offers sophisticated risk awareness and incident response strategies that empower organizations to proactively manage threats. Their platform leverages advanced technologies to detect and respond to threats in real-time, ensuring that CFOs can mitigate risks and maintain compliance. A critical component of this strategy is endpoint protection, which acts as a proactive measure to prevent unauthorized software from executing, thereby significantly reducing the risk of malware and ransomware attacks. This method not only mitigates vulnerabilities but also assists organizations in meeting stringent compliance requirements such as data protection regulations.
With the global cybersecurity market projected to surge from $22.4 billion in 2023 to $60.6 billion by 2028, the necessity for adopting such technologies is evident. Moreover, 93% of leaders in the field anticipate encountering daily AI attacks by 2025, underscoring the urgent need for enhanced security measures. By integrating advanced threat intelligence and incident response strategies, financial leaders can enhance their organization's resilience against cyberattacks, ultimately safeguarding their bottom line.
The time to act is now. Are you prepared to face the challenges of an increasingly hostile cyber environment? Embracing managed cybersecurity services is not just a choice; it is a necessity for the sustainability and integrity of your organization.
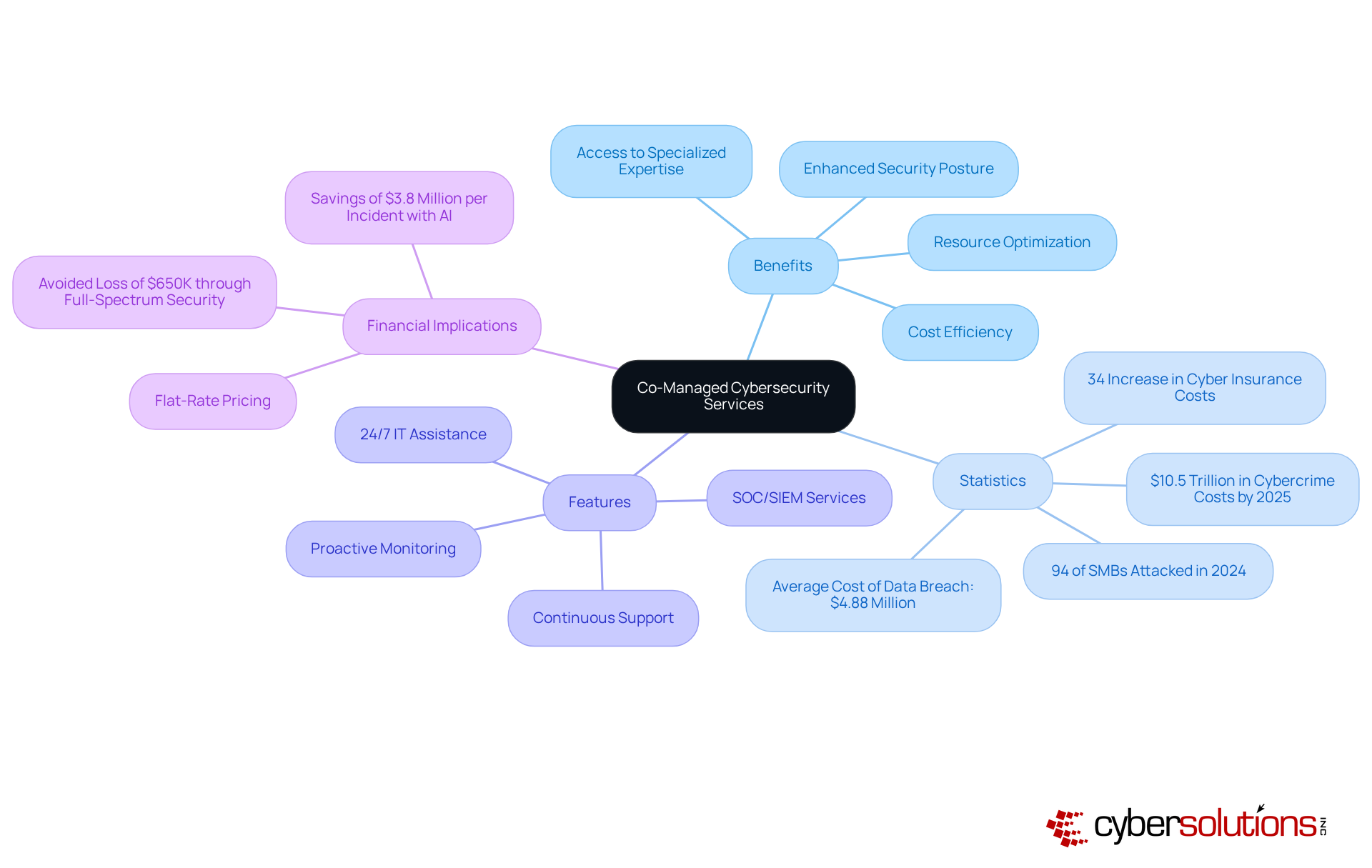
In today's digital landscape, cybersecurity is not just an option; it is a necessity for organizations, especially those with existing internal teams. Cyber Solutions excels in delivering services that significantly bolster these teams. This collaborative model empowers financial leaders to tap into specialized external expertise while retaining oversight of their cybersecurity strategies. By partnering with Cyber Solutions, CFOs can efficiently manage risks without shouldering the entire burden.
This strategic approach enhances an entity's resilience against evolving threats and optimizes resource allocation, allowing internal teams to concentrate on core business functions. With that clarity simplifies budgeting, Cyber Solutions ensures organizations can plan their expenses without the fear of unexpected IT costs. Furthermore, the extensive features offered—such as threat detection, SOC/SIEM, proactive monitoring, and continuous support—guarantee that organizations remain audit-ready and compliant with stringent regulations.
As cybercrime expenses are projected to reach $10.5 trillion globally by 2025, forging a partnership is increasingly essential for organizations aiming to safeguard their digital assets. The urgency for robust cybersecurity measures is underscored by the alarming statistic that 94% of SMBs reported being attacked in 2024, a significant rise from 73% in 2023. Additionally, the challenges are highlighted by a 34% increase in cyber insurance costs for small and midsize companies in 2024. This collaboration not only addresses pressing protection needs but also enables organizations to leverage technology alongside expertise. Notably, entities employing AI-driven risk detection and zero-trust frameworks can save an average of $3.8 million per incident, reinforcing the value of investing in comprehensive cybersecurity solutions.
In today's healthcare landscape, cybersecurity is not just important; it is essential for safeguarding patient information. Managed Detection and Response services, such as MDR, play a pivotal role in cybersecurity by providing ongoing oversight, risk identification, and threat mitigation. These services empower financial executives to confront potential dangers before they escalate into significant monetary losses. For instance, organizations that implement MDR have reported a remarkable 62% reduction in security incidents and a 50% decrease in the time taken to identify and respond to threats.
This proactive strategy not only fortifies security measures but also ensures adherence to regulations, such as HIPAA, which are crucial for maintaining compliance and avoiding costly penalties. Furthermore, investing in tailored IT services enhances ROI, enabling CFOs to transition their cybersecurity approach to a more strategic framework, which allows for a shift from reactive to proactive strategies, thereby protecting their organization’s assets and operational integrity.
The swift mobilization of resources, as demonstrated in our case studies, underscores the importance of having specialized expertise available within 24 hours to effectively manage risks. This layered approach not only mitigates immediate threats but also strengthens overall security measures, ensuring that healthcare organizations can safeguard patient data and operations against future vulnerabilities.
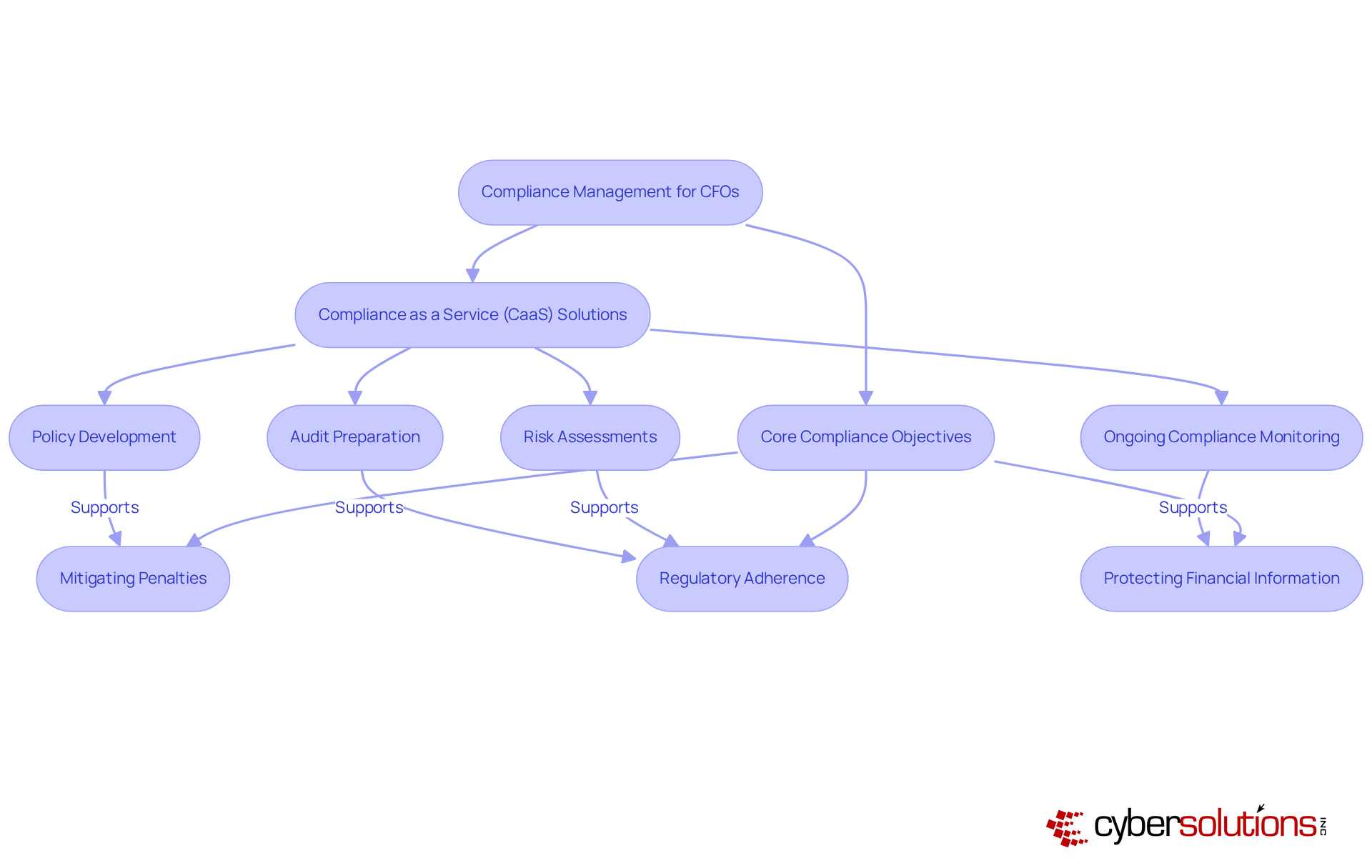
Effective compliance management is paramount for CFOs striving to ensure regulatory adherence and mitigate potential penalties. By establishing robust compliance frameworks, businesses can enhance their reputation and foster trust with stakeholders. Prioritizing compliance within the broader business strategy is essential; it not only protects against breaches but also aligns with critical regulations such as GDPR.
Cyber Solutions' services offer comprehensive solutions, including:
These services streamline adherence processes and significantly reduce the risk of non-compliance, which averages $14.82 million annually, as reported in the True Cost of Financial Crime Compliance Study. Moreover, organizations investing in compliance training (64%) and faster issue detection (53%), ultimately boosting overall operational efficiency.
As leaders, financial executives must remain proactive in adapting their compliance strategies. Leveraging technology and expert guidance is vital to avoiding substantial financial repercussions. Are you ready to take the necessary steps to safeguard your organization’s compliance and secure its future?
Frequent evaluations of safety measures are not just important; they are essential for fortifying the security posture of a company. In a landscape where threats are ever-evolving, cybersecurity firms provide assessments that serve a dual purpose: they identify vulnerabilities and offer actionable insights for effective remediation. This aligns with tailored strategies that address compliance gaps, ensuring that organizations are not only resilient but also compliant with industry standards through regular reviews and audits. By prioritizing regular assessments, CFOs can significantly enhance their organizations' defenses against potential breaches with proactive measures.
Research indicates that organizations that engage in regular assessments and conduct security audits experience a remarkable improvement in their security posture. This statistic underscores the pivotal role these assessments play in improving defense posture. Moreover, organizations that utilize threat intelligence can achieve better risk management, empowering them to rectify weaknesses before they can be exploited, ultimately safeguarding sensitive data and maintaining operational integrity.
A comprehensive strategy for achieving security excellence, which includes conducting mock audits and preparing detailed documentation. This approach reinforces the importance of vigilance in today's cyber climate. As cyber risks escalate, the imperative for regular assessments becomes increasingly clear. Are you ready to take the necessary steps to protect your organization and ensure its success?

In the realm of cybersecurity, analytics serve as a critical tool for financial leaders, providing essential insights that drive informed decision-making. By leveraging data analytics, organizations can continuously monitor threats, assess vulnerabilities, and respond swiftly to incidents. This not only fortifies the organization's defense but also enables CFOs to allocate resources with greater effectiveness.
For example, predictive analytics can pinpoint risks, facilitating prioritized responses. Moreover, analytics play a vital role in identifying anomalies in user behavior, which may signal potential insider threats. Consequently, CFOs are able to make strategic decisions that align with their organization's financial objectives, all while minimizing risks.
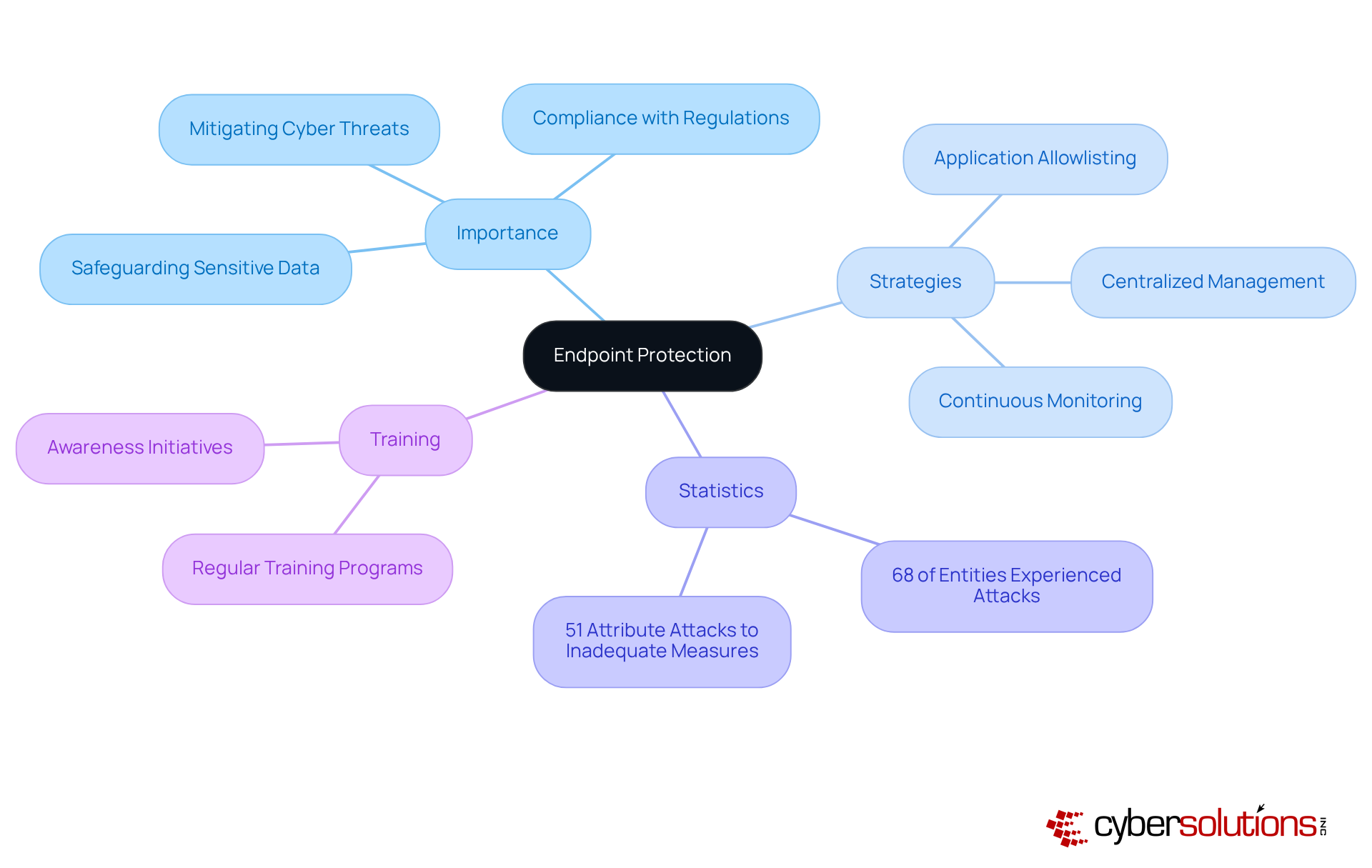
Endpoint protection stands as a crucial pillar of any cybersecurity strategy, especially for CFOs responsible for safeguarding sensitive financial data. In an era where cyber threats are rampant, implementing comprehensive solutions is not merely advisable; it is essential. These solutions effectively prevent unauthorized access to critical information, significantly mitigating the risk of data breaches and cyberattacks.
A cornerstone of this strategy is endpoint security, which proactively blocks malware and unauthorized software from executing. By adopting this approach, organizations can drastically reduce their attack surface and minimize vulnerabilities, all while ensuring data integrity. Features such as centralized management and continuous monitoring enhance the effectiveness of endpoint protection, empowering organizations to maintain strict control over software usage.
Expert insights reveal that cybersecurity measures are indispensable in today’s landscape, where 68% of entities have experienced one or more cyber incidents and/or their IT infrastructure. This statistic underscores the urgent need for robust security solutions. Furthermore, 51% of IT experts attribute the success of endpoint attacks to inadequate protective measures, illuminating the challenges organizations face in this domain.
Successfully implementing these solutions can significantly bolster an organization's resilience against potential financial losses and reputational damage, ultimately fostering a secure environment for financial operations. Additionally, consistent training and awareness initiatives for staff are paramount in reducing risks associated with cyber threats, ensuring that all personnel are equipped to identify and respond to potential threats.
A multi-layered approach, including firewalls and antivirus software, is essential for combating sophisticated endpoint attacks. This reinforces the necessity for comprehensive safeguarding measures that not only protect but also empower organizations in their cybersecurity endeavors.
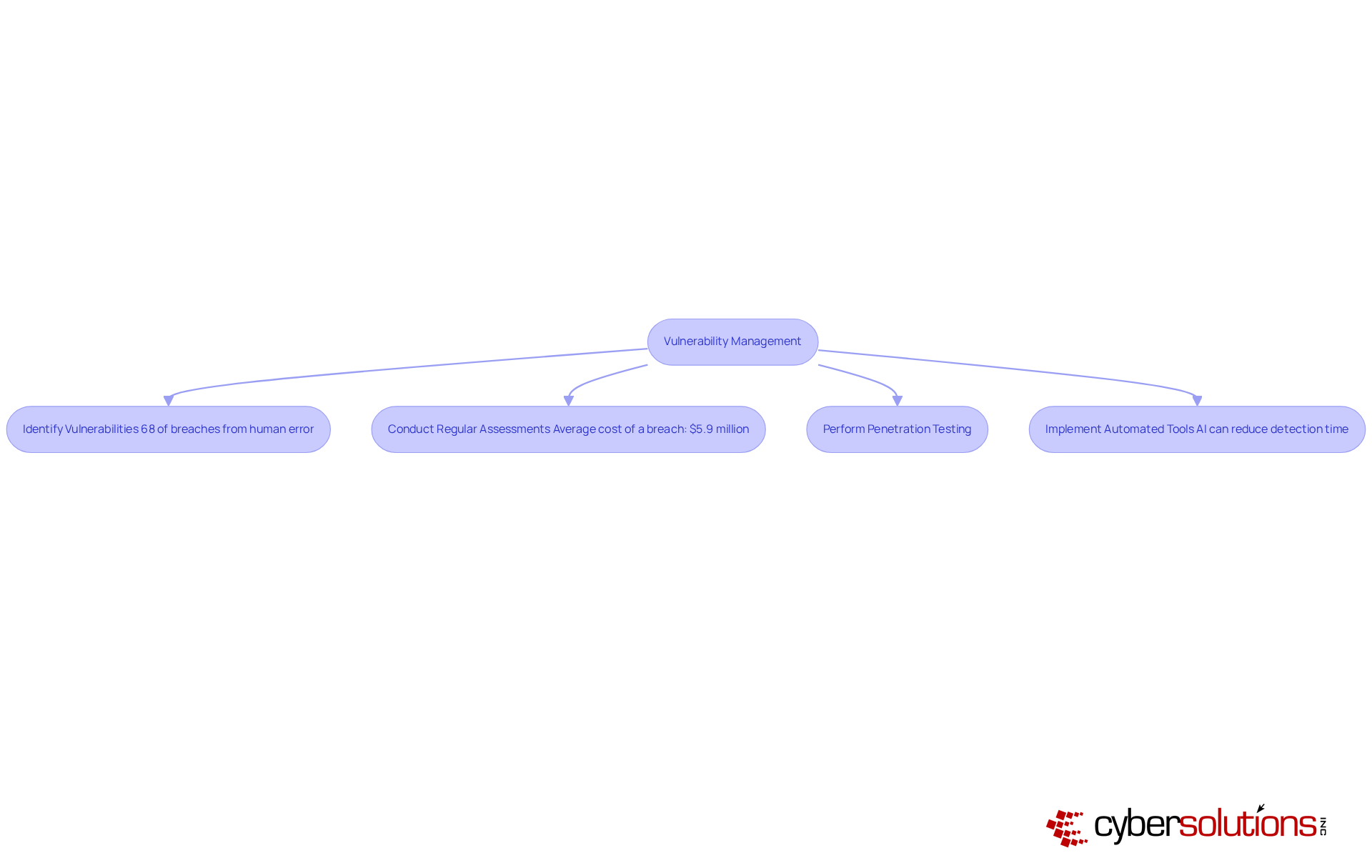
Vulnerability management stands as a cornerstone for identifying and addressing security weaknesses within a company's IT infrastructure. For CFOs, prioritizing this process is not merely advisable; it is essential for safeguarding their enterprises against potential cyber threats. A robust program empowers organizations to proactively confront weaknesses, ensuring that their systems remain resilient and effective.
In the realm of financial institutions, where sensitive data is paramount, the impact of data breaches is particularly significant. Consider this: recent statistics underscore the necessity for continuous monitoring and training to mitigate risks. Furthermore, the evolving threat landscape highlights the importance of proactive measures.
Effective practices include:
These practices serve to identify critical weaknesses before they can be exploited. In 2023, nearly 400,000 publicly exposed databases came to light, with organizations taking an average of 170 days to rectify these vulnerabilities. This delay can precipitate substantial data breaches, accentuating the urgency of timely remediation. By integrating automated tools, organizations can bolster their vulnerability detection and response capabilities, ultimately fortifying their cybersecurity posture.
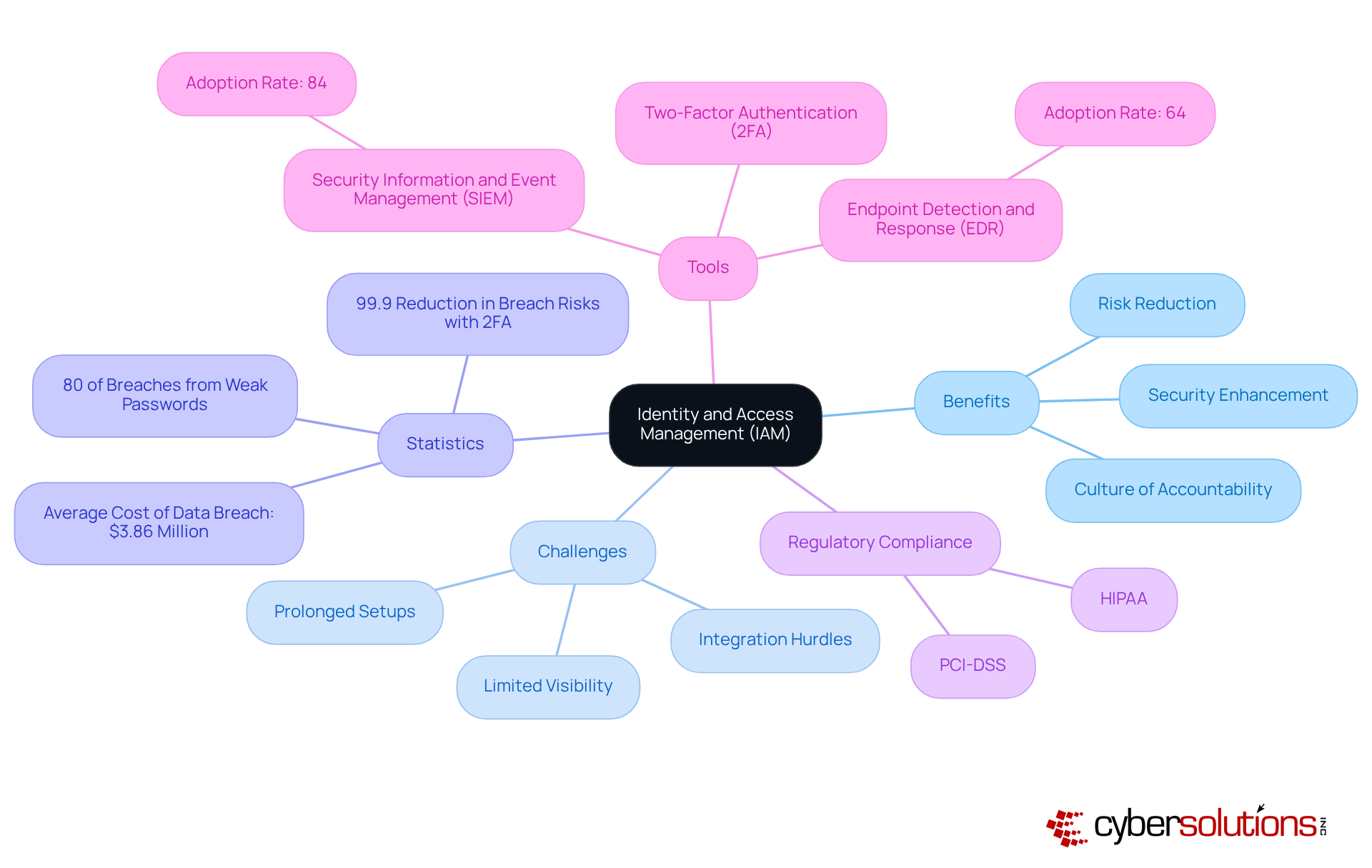
In today's digital landscape, identity and access management is particularly important in safeguarding sensitive financial data within healthcare. Compliance with stringent regulatory requirements such as HIPAA and PCI-DSS is essential. By implementing robust IAM strategies, organizations can significantly mitigate the risk of data breaches, with studies revealing that 80% of breaches originate from weak or stolen passwords. This proactive approach not only enhances security but also cultivates a culture of accountability within the organization.
Real-world evidence highlights the efficacy of IAM in preventing unauthorized access. For instance, organizations that have embraced two-factor authentication experienced an astounding 99.9% reduction in data breach risks. Furthermore, the integration of advanced tools like Security Information and Event Management (SIEM) and Endpoint Detection and Response (EDR) has become standard practice, with adoption rates of 84% and 64% respectively, underscoring a commitment to security.
Considering that the average cost of a data breach amounts to $3.86 million, implementing IAM solutions is a strategic imperative. By managing user access effectively, healthcare entities can secure sensitive financial data, diminish risks, and maintain trust with stakeholders. Additionally, pairing IAM with comprehensive compliance solutions—featuring regular audits—enhances the protective posture of healthcare organizations. Ongoing training is vital to ensure that all personnel are informed of security protocols and can actively contribute to the safeguarding of sensitive data. However, organizations frequently encounter challenges in deploying IAM solutions, such as prolonged setups and integration hurdles, which must be addressed to fully capitalize on the advantages of IAM.
In a landscape where cybersecurity threats continue to grow in complexity and frequency, the role of managed cybersecurity services is increasingly vital for CFOs. These services not only protect sensitive financial data but also empower financial leaders to focus on strategic initiatives rather than IT challenges. By leveraging solutions like 24/7 help desk support, endpoint protection, and compliance management, CFOs can create a robust cybersecurity framework that safeguards their organizations against potential risks.
The article highlights several key services that are essential for financial executives, including:
Each of these services plays a critical role in enhancing an organization's security posture, ensuring compliance with industry regulations, and ultimately protecting the bottom line. As cyber threats evolve, the integration of real-time analytics and identity access management further strengthens defenses, enabling informed decision-making and controlled access to sensitive information.
Ultimately, the imperative for CFOs is clear: embracing comprehensive managed cybersecurity services is not just a strategic advantage; it is a necessity for sustaining business integrity and resilience in an increasingly hostile cyber environment. By prioritizing these services, organizations can not only mitigate risks but also foster a culture of security that aligns with their long-term financial goals. Taking proactive steps towards enhancing cybersecurity measures today will pave the way for a secure and prosperous future.
What managed cybersecurity services does Cyber Solutions Inc. offer for CFOs?
Cyber Solutions Inc. offers a range of managed cybersecurity services including 24/7 help desk support, endpoint protection, data encryption, secure access controls, backup and disaster recovery, and co-managed IT support.
Why is 24/7 help desk support important for organizations?
24/7 help desk support provides immediate assistance in addressing IT issues and mitigating potential cyber threats, which is crucial for minimizing downtime and improving response times during incidents.
What sectors benefit from Cyber Solutions Inc.'s services?
CFOs in sectors such as healthcare, finance, manufacturing, and government benefit from Cyber Solutions Inc.'s managed cybersecurity services.
How does Cyber Solutions help organizations comply with industry regulations?
Cyber Solutions ensures compliance with industry regulations by providing services that protect sensitive information and by utilizing strategies such as application allowlisting, which helps meet compliance requirements like HIPAA and PCI-DSS.
What is the significance of application allowlisting in cybersecurity?
Application allowlisting is a proactive measure that prevents unauthorized software from executing, significantly reducing the risk of malware and ransomware attacks, and assisting organizations in meeting compliance requirements.
What are the projected trends in the AI cybersecurity market?
The global AI cybersecurity market is projected to grow from $22.4 billion in 2023 to $60.6 billion by 2028, indicating a rising necessity for adopting advanced cybersecurity technologies.
How does Cyber Solutions' co-managed cybersecurity services model work?
The co-managed cybersecurity services model allows organizations with existing internal teams to leverage external expertise while maintaining oversight of their cybersecurity strategies, optimizing resource allocation and enhancing resilience against threats.
What are the financial implications of cybercrime for organizations?
Cybercrime expenses are projected to reach $10.5 trillion globally by 2025, and small and midsize companies have seen a 34% increase in cyber insurance costs in 2024, highlighting the urgent need for robust cybersecurity measures.
How can organizations save costs by implementing Cyber Solutions' services?
Organizations employing AI-driven risk detection and zero-trust frameworks can save an average of $3.8 million per incident, reinforcing the value of investing in comprehensive cybersecurity solutions.
Why is it critical for financial leaders to continually assess their cybersecurity strategies?
It is essential for financial leaders to continually assess their cybersecurity strategies to ensure alignment with evolving risks and to maximize the benefits of managed cybersecurity services.