
Understanding the nuances of cybersecurity has become increasingly critical, particularly for organizations involved with the Department of Defense (DoD). The stakes are higher than ever with the Cybersecurity Maturity Model Certification (CMMC) at the forefront of this initiative—a framework designed to bolster the security of sensitive information within the Defense Industrial Base. As compliance becomes mandatory for all DoD contracts involving Controlled Unclassified Information (CUI) by November 2025, organizations must not only navigate the complexities of this certification but also enhance their overall cybersecurity posture. How can they achieve this dual objective effectively?
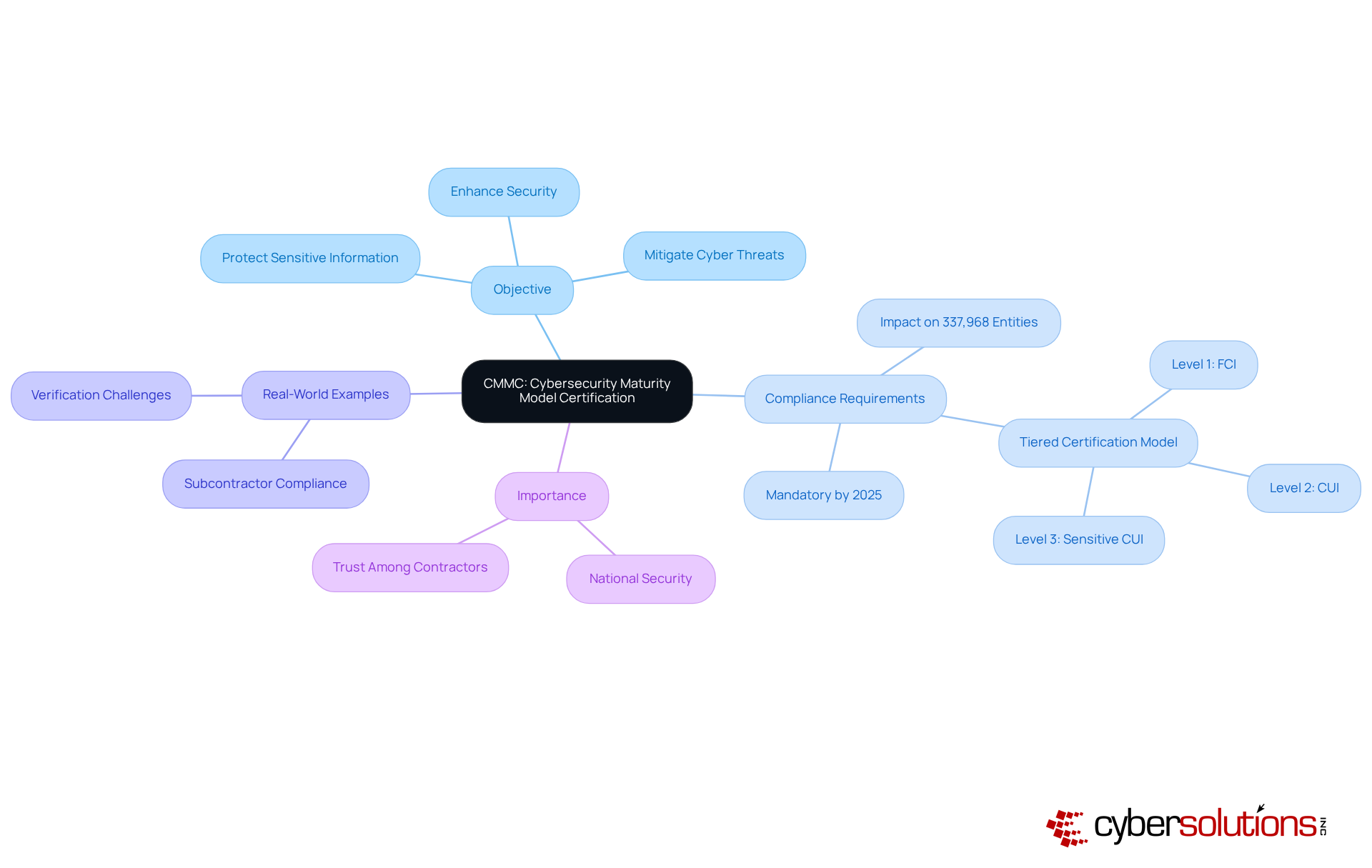
The CMMC, often asked about in the question 'what does CMMC stand for', is a critical framework established by the U.S. Department of Defense (DoD) aimed at strengthening the cybersecurity posture within the Defense Industrial Base (DIB). Its primary objective is to ensure that sensitive information, particularly Controlled Unclassified Information (CUI) and Federal Contract Information (FCI) is adequately protected. By implementing a standardized certification process, this initiative seeks to mitigate risks associated with vulnerabilities in the defense supply chain.
The significance of CMMC is underscored by the fact that, starting in 2025, certification will be required for all DoD contracts involving CUI or FCI. This requirement will impact approximately 337,968 entities across various sectors, underscoring the essential need for robust protective measures. As organizations prepare for compliance, they must implement a strategy that encompasses self-assessments and third-party evaluations, ensuring that their cybersecurity practices align with established standards.
Real-world examples illustrate the critical nature of this compliance framework in protecting sensitive data. For instance, defense contractors are now required to extend CUI or FCI obligations to all subcontractors, highlighting the necessity for thorough adherence across the supply chain. This collaborative approach not only enhances security but also fosters trust among contractors and their partners.
In conclusion, understanding what CMMC stands for is essential as the framework evolves in security compliance, especially with the evolving landscape in 2025 and beyond. Organizations must proactively assess their cybersecurity posture and engage with qualified assessors to meet the stringent requirements set forth by the DoD, ultimately ensuring the protection of national security and sensitive data.
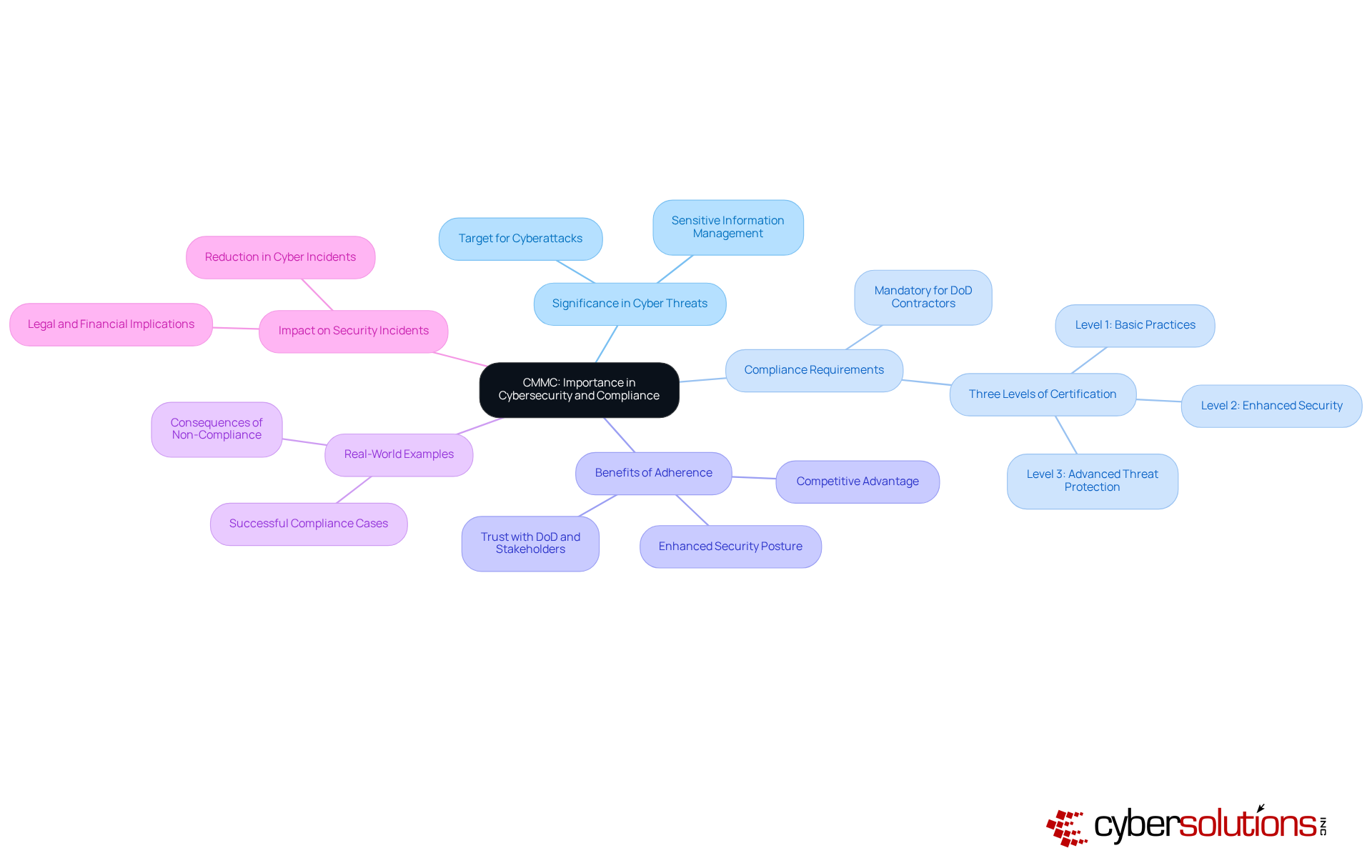
In today’s landscape of escalating cyber threats, understanding what does CMMC stand for is of paramount significance. Organizations engaged with the Department of Defense (DoD) are prime targets for cyberattacks due to the sensitive nature of the information they manage. This framework serves as an essential structure, compelling these entities to implement measures that significantly reduce the risk of data breaches.
Understanding what does CMMC stand for is essential, as compliance with the framework is not merely recommended; it is a requirement for contractors seeking to bid on DoD contracts, underscoring its crucial role within the defense sector. By adhering to established security guidelines, entities not only bolster their cybersecurity posture but also demonstrate a commitment to compliance, thereby cultivating trust with the DoD and other stakeholders.
Real-world examples illustrate how organizations have effectively enhanced their security through adherence to specific standards, showcasing the model’s efficacy in minimizing vulnerabilities. Furthermore, expert insights stress that following best practices is increasingly viewed as essential for maintaining competitiveness in the defense contracting arena, especially as digital security risks continue to evolve in 2025.
The impact of compliance with the CMMC framework extends beyond mere eligibility for contracts; it significantly influences the frequency and severity of cyber incidents, making it a critical factor for any organization operating in this domain.
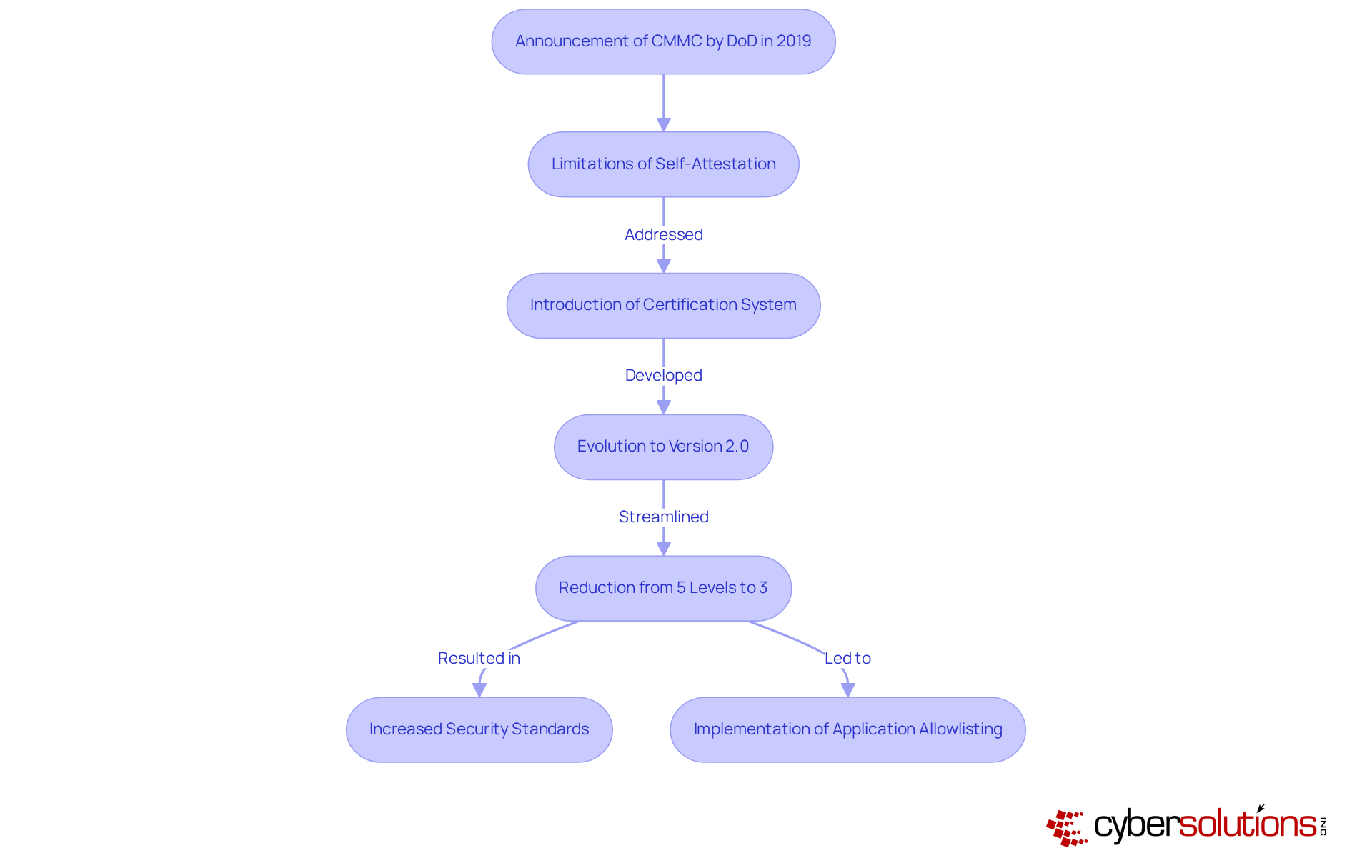
The emergence of the CMMC, which raises the question of what does CMMC stand for, underscores a critical response to the vulnerabilities within the defense supply chain. Announced by the Department of Defense (DoD) in 2019, this certification, which addresses what does CMMC stand for, was designed to rectify the limitations of the self-attestation model that allowed contractors to certify their own compliance without independent verification. This pivotal change was prompted by a series of breaches that exposed sensitive information, emphasizing the urgent need for a more rigorous and standardized approach to digital security.
The CMMC framework, and what does CMMC stand for, integrates established standards, such as NIST guidelines, into a comprehensive certification system that evaluates an organization's maturity in implementing security practices. Notably, the framework has evolved, with version 2.0 being the latest iteration, prompting the question of what does CMMC stand for in the context of ongoing regulatory demands and the ever-changing landscape of cyber threats. This updated framework has streamlined the certification process, reducing the levels from five to three, thereby facilitating compliance for contractors while also clarifying what does CMMC stand for in the context of maintaining security.
To understand what does CMMC stand for, organizations must implement security measures to protect Controlled Unclassified Information (CUI) in accordance with NIST 800-171 to achieve Level 2 adherence. Furthermore, to understand what does CMMC stand for, one must know that attaining CMMC Level 3 requires advanced security protocols to safeguard the most sensitive information, ensuring eligibility for federal contracts. As the DoD prepares to enforce these requirements, organizations must adapt to this new compliance environment, anticipated to be fully integrated into contracts by the end of 2025.
In this evolving context, the role of cybersecurity becomes increasingly vital. This proactive measure prevents unauthorized software from executing, thereby bolstering digital security and assisting organizations in meeting strict compliance standards. Key features of cybersecurity include:
All contributing to a secure environment.
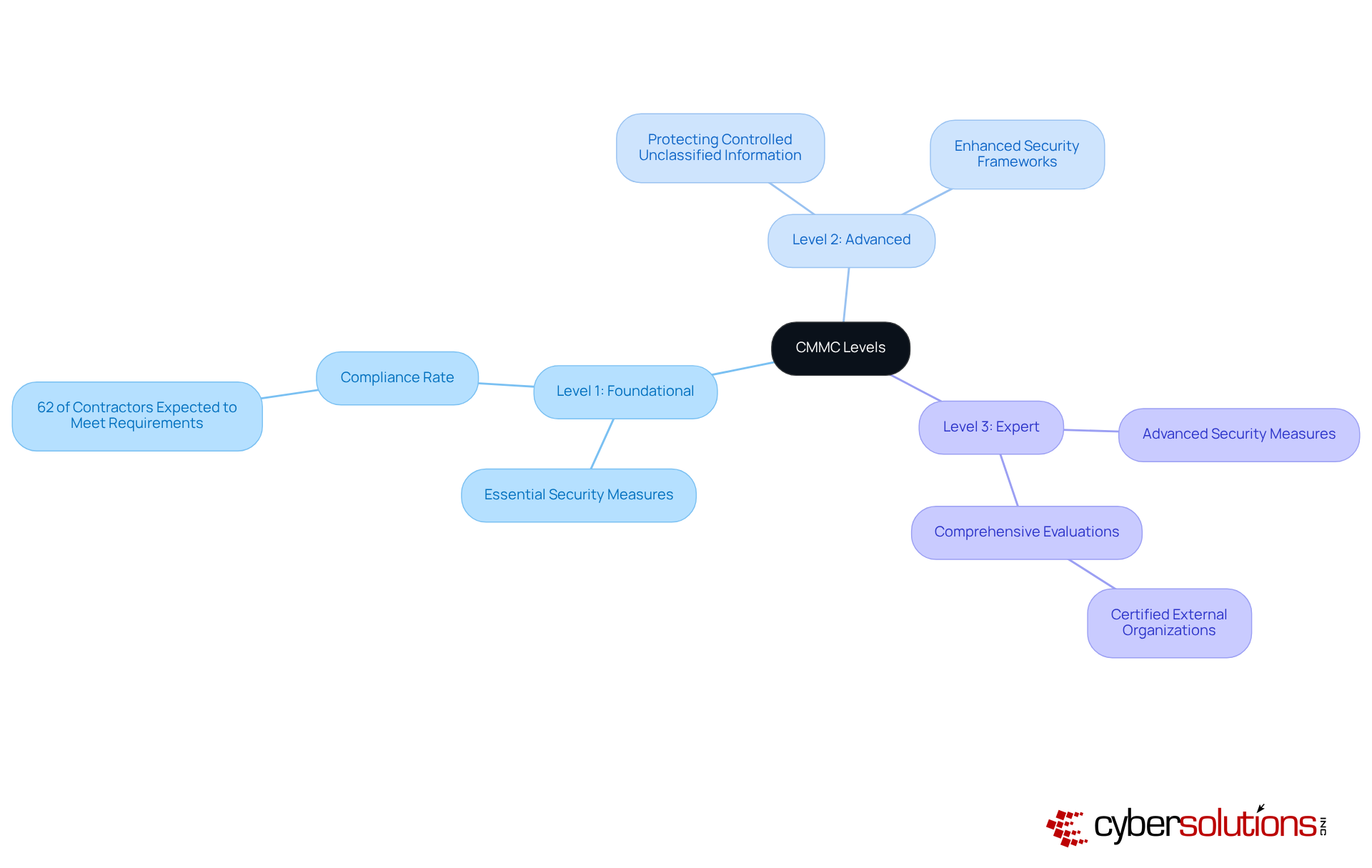
The CMMC, which raises the question of compliance, is organized into three distinct levels, each representing a different degree of security maturity and associated requirements.
Practical examples illustrate the journey of entities achieving certification. For instance, organizations that have attained Level 2 certification report enhanced security frameworks and improved operational efficiencies, showcasing the benefits of compliance. As the CMMC program advances, it is imperative for organizations to understand and prepare for the forthcoming changes, particularly with the evolving regulatory landscape.
The Cybersecurity Maturity Model Certification (CMMC) is a crucial framework aimed at bolstering cybersecurity within the Defense Industrial Base (DIB). By enforcing compliance with rigorous security standards, the CMMC seeks to safeguard sensitive information and reduce risks linked to cyber threats, thereby ensuring the integrity of the defense supply chain.
It is imperative to recognize that CMMC compliance is not merely optional; it is essential for organizations seeking to secure Department of Defense contracts. The tiered certification levels, from foundational to expert, illustrate the diverse degrees of security maturity required. Real-world examples reinforce the significance of these measures, demonstrating that adherence to CMMC not only enhances security protocols but also cultivates trust within the defense sector.
As the cybersecurity landscape continues to evolve, organizations must prioritize compliance with CMMC standards. The approaching deadline of November 10, 2025, serves as a critical reminder for entities to evaluate their cybersecurity practices and collaborate with qualified assessors. By taking these steps, they not only protect sensitive data but also contribute to the overarching goal of national security in an increasingly digital world.
What does CMMC stand for?
CMMC stands for Cybersecurity Maturity Model Certification.
What is the purpose of CMMC?
The purpose of CMMC is to strengthen the cybersecurity posture of organizations within the Defense Industrial Base (DIB) by ensuring that contractors and subcontractors effectively protect sensitive information, particularly Controlled Unclassified Information (CUI) and Federal Contract Information (FCI).
When will compliance with CMMC become mandatory?
Compliance with CMMC will become mandatory for all DoD contracts involving CUI or FCI starting November 10, 2025.
How many entities will be impacted by CMMC compliance?
Approximately 337,968 entities across various sectors will be impacted by CMMC compliance.
What does the CMMC certification process involve?
The CMMC certification process involves a tiered model that includes self-assessments and third-party evaluations to ensure that organizations' cybersecurity practices align with established standards.
How does CMMC affect subcontractors?
Defense contractors are required to extend CUI or FCI obligations to all subcontractors, emphasizing the need for adherence to cybersecurity standards across the entire supply chain.
Why is CMMC important for national security?
CMMC is important for national security as it plays a crucial role in safeguarding sensitive information and mitigating risks associated with cyber threats within the defense supply chain.