
In today's digital landscape, cybersecurity in healthcare is not just an option; it is a necessity. CMMC compliance is a vital framework that ensures healthcare organizations adhere to stringent cybersecurity standards, crucial for protecting sensitive data and maintaining eligibility for Department of Defense contracts. Achieving compliance significantly enhances cybersecurity measures, builds trust with patients and partners, and ultimately safeguards against financial losses stemming from data breaches and operational disruptions. As the threats evolve, healthcare CFOs must recognize the unique challenges they face and take proactive steps to address them through robust Cyber Solutions.
The escalating prevalence of cyber threats in the healthcare sector has rendered cybersecurity an urgent priority for medical organizations, especially those collaborating with the Department of Defense (DoD). Grasping the nuances of CMMC compliance is essential, as it not only protects sensitive patient information but also bolsters the credibility of healthcare providers in a fiercely competitive environment. Alarmingly, statistics indicate that a substantial number of contractors are failing to meet these standards. This raises a critical question: how can healthcare CFOs ensure their organizations are equipped to navigate the complexities of compliance while simultaneously defending against the ever-evolving landscape of cyber risks?
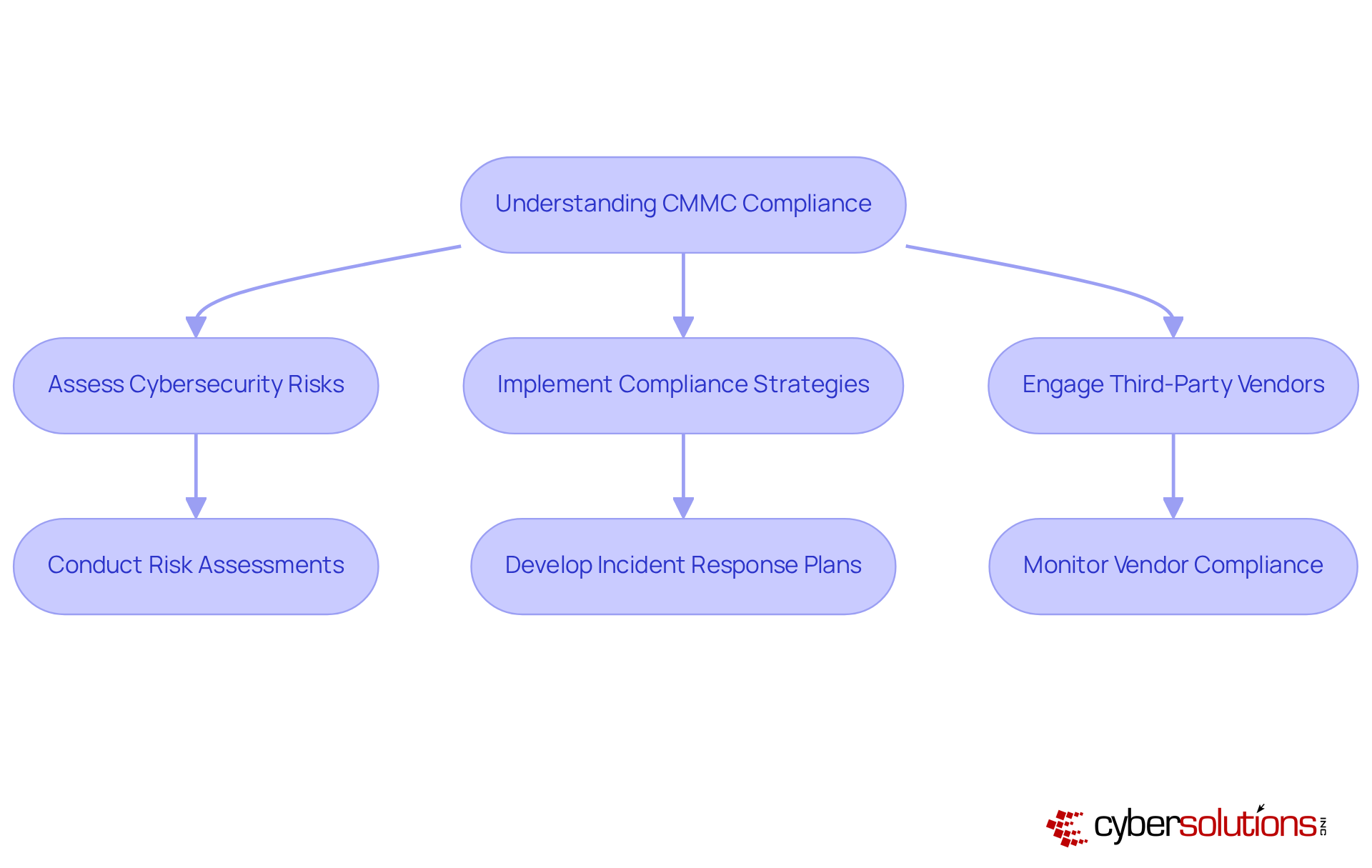
What is CMMC compliance? It is a critical framework established by the Department of Defense (DoD) to guarantee that contractors meet rigorous cybersecurity standards. For medical entities, achieving these standards is vital for protecting sensitive data, including Controlled Unclassified Information (CUI) and Federal Contract Information (FCI). This commitment not only enhances cybersecurity strategies but also bolsters the trust that patients and partners place in medical providers.
As cyber threats become increasingly sophisticated, knowing what is CMMC compliance emerges as a fundamental aspect of a medical facility's risk management strategy, especially for those engaged with DoD contracts. Alarmingly, nearly 80 percent of DoD contractors may be falling short of essential cybersecurity standards, raising the question of what is CMMC compliance in light of a staggering 94% rise in ransomware attacks on medical providers since 2021.
Furthermore, this standard offers an additional layer of security beyond HIPAA regulations, enabling healthcare entities to effectively safeguard patient information while navigating the complexities of regulatory frameworks. Case studies reveal that organizations prioritizing compliance not only mitigate risks but also enhance their overall cybersecurity posture, rendering them more resilient against potential breaches.
Industry experts emphasize the necessity for entities to act promptly to ; failure to do so could jeopardize their eligibility for crucial government contracts and result in significant financial repercussions.

The medical sector is increasingly vulnerable to cybercriminal threats, primarily due to the sensitive data it manages. With the rise of telehealth and digital health records, the risk of has escalated significantly. For medical organizations collaborating with the Department of Defense (DoD), adhering to stringent cybersecurity standards is imperative, as these organizations must comply with regulations like HIPAA. This regulatory framework not only bolsters the security posture of medical service providers but also addresses the challenges associated with protecting Controlled Unclassified Information (CUI).
By mid-2025, over 100 Level 2 certifications are expected to be granted, highlighting the urgency for compliance, especially as nearly half of defense contractors report only moderate readiness for these requirements. Understanding what is CMMC compliance is crucial for medical CFOs to recognize its critical role in safeguarding their organizations against cyber risks and ensuring adherence to regulatory guidelines. Moreover, as medical institutions increasingly depend on third-party vendors for services such as telehealth, it becomes essential to understand what is CMMC compliance to ensure that these vendors adhere to the necessary standards for maintaining a robust cybersecurity framework.
The necessity of rapid incident response strategies cannot be overstated; having a dedicated incident response team in place can significantly mitigate damage and enhance overall cybersecurity resilience. Cyber Solutions offers tailored IT services specifically designed for the healthcare sector, including Compliance as a Service (CaaS), which simplifies the regulatory process and provides expert guidance to ensure compliance with industry standards. Our offerings include vital tools such as endpoint protection and threat detection, further reinforcing the security measures required for adherence.
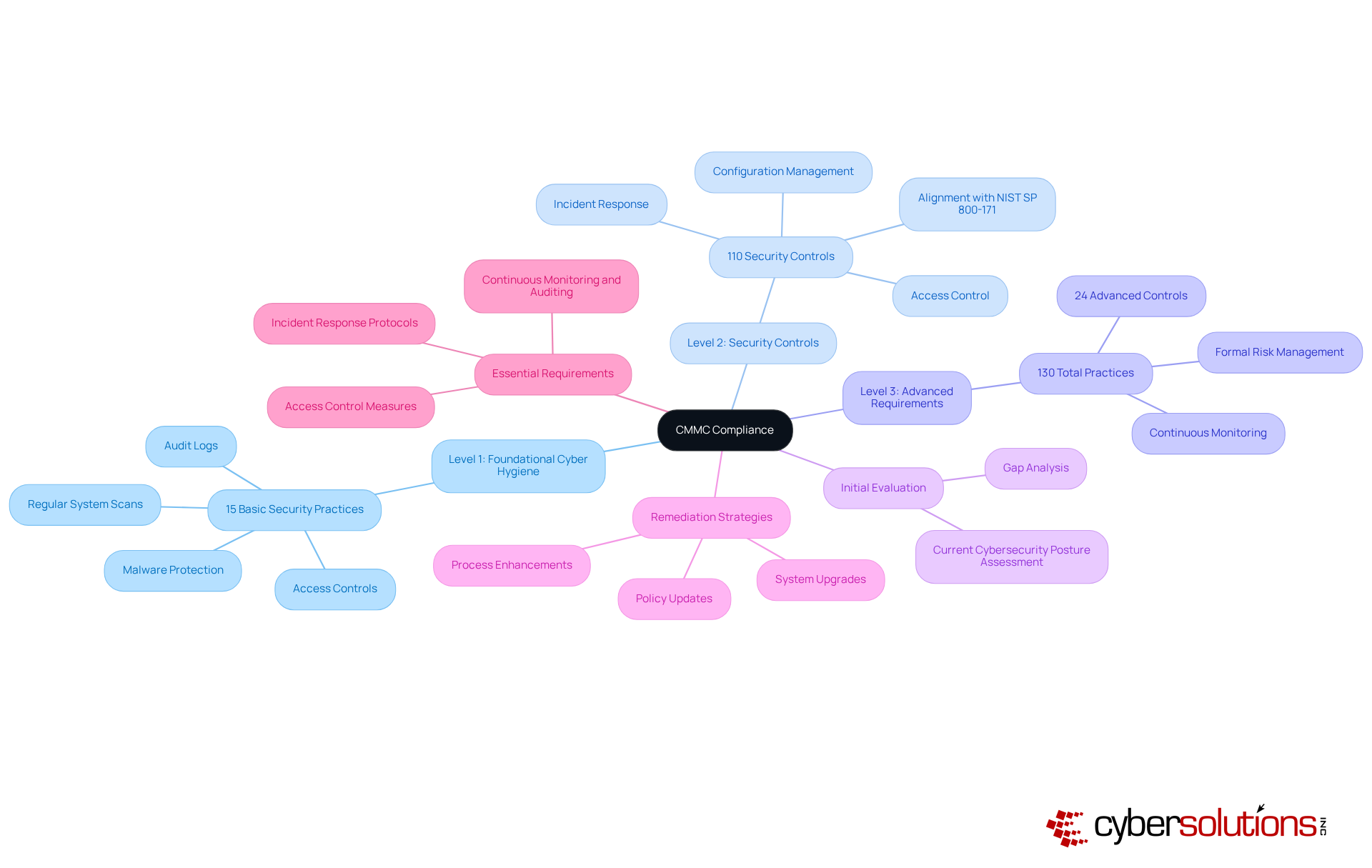
In today's digital landscape, the importance of cybersecurity in healthcare cannot be overstated. Understanding what is reveals that it is structured into three distinct levels, each escalating in its cybersecurity requirements.
To achieve adherence, healthcare organizations must first conduct a comprehensive initial evaluation and gap analysis of their current cybersecurity posture in relation to what is CMMC compliance. This critical process identifies necessary adherence actions and includes tailored remediation strategies such as:
Essential requirements encompass:
Moreover, creating a System Security Plan (SSP) is crucial, serving as a regulatory guide that outlines security policies and procedures. By understanding what is CMMC compliance, medical entities can formulate a comprehensive plan to attain adherence and strengthen their overall cybersecurity framework. How prepared is your organization to navigate these challenges and enhance its security posture?
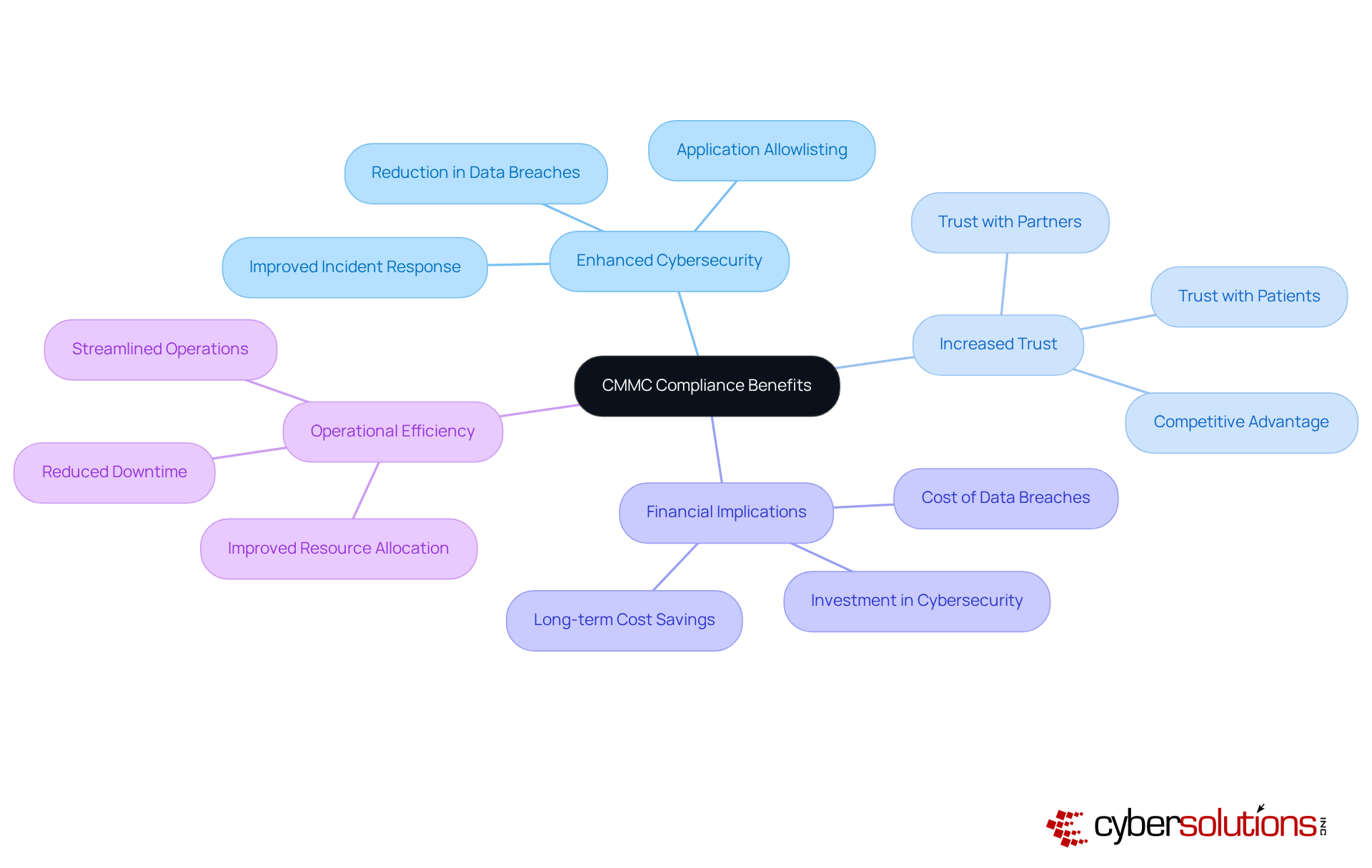
Understanding what is presents a vital opportunity for medical entities, delivering numerous benefits such as enhanced cybersecurity, increased trust with patients and partners, and eligibility for Department of Defense contracts. By implementing the mandated security measures, organizations can drastically diminish the risk of data breaches, which recent reports indicate average $10.93 million per incident in the healthcare sector. This financial burden underscores the importance of proactive adherence; organizations that delay their readiness face not only potential monetary losses but also disruptions in operations.
A fundamental element of this proactive strategy is application allowlisting, recognized as a gold standard in cybersecurity. By preventing unauthorized or malicious applications from executing and consistently monitoring application activity, allowlisting reduces the attack surface and mitigates vulnerabilities, thereby enhancing compliance with standards such as HIPAA, PCI-DSS, and GDPR. This essential measure not only protects sensitive data but also aids organizations in fulfilling rigorous regulatory requirements, ensuring adherence to data protection protocols.
Furthermore, compliance with cybersecurity standards streamlines operations by establishing uniform practices, which can lead to better resource allocation and return on investment (ROI). Medical entities that have successfully implemented CMMC measures report improved operational efficiency and reduced downtime, culminating in significant long-term cost savings.
For CFOs in the medical sector, grasping these implications is crucial for making informed budgeting decisions regarding cybersecurity investments. The financial repercussions of data breaches are projected to rise in 2025, emphasizing the necessity for organizations to view adherence as a strategic investment rather than merely a regulatory obligation. Additionally, embracing a flat-rate pricing model for managed IT and cybersecurity services can simplify budgeting and enhance operational efficiency, offering peace of mind in a comprehensive package. Ultimately, understanding what is CMMC compliance not only fortifies cybersecurity but also cultivates trust with patients and partners, positioning healthcare organizations advantageously in an increasingly competitive landscape.
Understanding CMMC compliance is not merely a regulatory requirement; it is a strategic necessity for healthcare organizations, especially for CFOs who must navigate the intricate landscape of cybersecurity regulations. This framework is pivotal in safeguarding sensitive patient data and elevating the overall trustworthiness of medical entities in an environment increasingly besieged by cybercriminals. By prioritizing compliance, healthcare organizations can significantly mitigate the financial and operational repercussions of data breaches while ensuring eligibility for vital government contracts.
Key points throughout this article underscore the critical role of CMMC compliance within the healthcare sector:
Organizations that commit to CMMC compliance not only enhance their cybersecurity posture but also streamline operations, optimize resource allocation, and cultivate trust with patients and partners. The financial ramifications of non-compliance present a compelling incentive for proactive measures.
Given the escalating cyber threats confronting healthcare organizations, embracing CMMC compliance transcends mere regulatory obligation; it emerges as a strategic imperative. As the healthcare landscape continues to evolve with digital advancements, the necessity for robust cybersecurity becomes increasingly critical. It is essential for healthcare CFOs and decision-makers to grasp the significance of CMMC compliance as a vital investment in their organization’s future, ensuring resilience against cyber threats and positioning themselves advantageously in a competitive market.
What is CMMC compliance?
CMMC compliance is a framework established by the Department of Defense (DoD) to ensure that contractors meet rigorous cybersecurity standards, which is particularly important for medical entities to protect sensitive data such as Controlled Unclassified Information (CUI) and Federal Contract Information (FCI).
Why is CMMC compliance important for healthcare organizations?
Achieving CMMC compliance is vital for healthcare organizations to enhance their cybersecurity strategies, protect sensitive patient information, and build trust with patients and partners. It also provides an additional layer of security beyond HIPAA regulations.
How does CMMC compliance relate to cybersecurity threats?
As cyber threats become more sophisticated, understanding CMMC compliance is essential for medical facilities' risk management strategies, especially for those involved with DoD contracts. The rise in ransomware attacks on medical providers highlights the urgency of compliance.
What are the consequences of not achieving CMMC compliance for healthcare organizations?
Failure to achieve CMMC compliance could jeopardize a healthcare organization's eligibility for government contracts and may lead to significant financial repercussions.
How does CMMC compliance enhance an organization's cybersecurity posture?
Organizations that prioritize CMMC compliance not only mitigate risks but also improve their overall cybersecurity posture, making them more resilient against potential breaches.
What percentage of DoD contractors may not meet cybersecurity standards?
Nearly 80 percent of DoD contractors may be falling short of essential cybersecurity standards, indicating a widespread issue in compliance.
How has the landscape of ransomware attacks changed since 2021?
There has been a staggering 94% rise in ransomware attacks on medical providers since 2021, underscoring the critical need for robust cybersecurity measures like CMMC compliance.