
In the complex and ever-evolving landscape of healthcare, the necessity for specialized IT support is more critical than ever. Medical organizations are confronted with stringent regulations, escalating cyber threats, and the urgent need to safeguard sensitive patient data. The advantages of collaborating with an IT support company become increasingly evident.
This article explores seven compelling reasons why healthcare providers should consider engaging an IT support company, highlighting how such partnerships not only enhance operational efficiency but also strengthen cybersecurity measures. Yet, in a world where cyberattacks are on the rise, how can healthcare organizations ensure they are adequately protected while maintaining their focus on patient care?
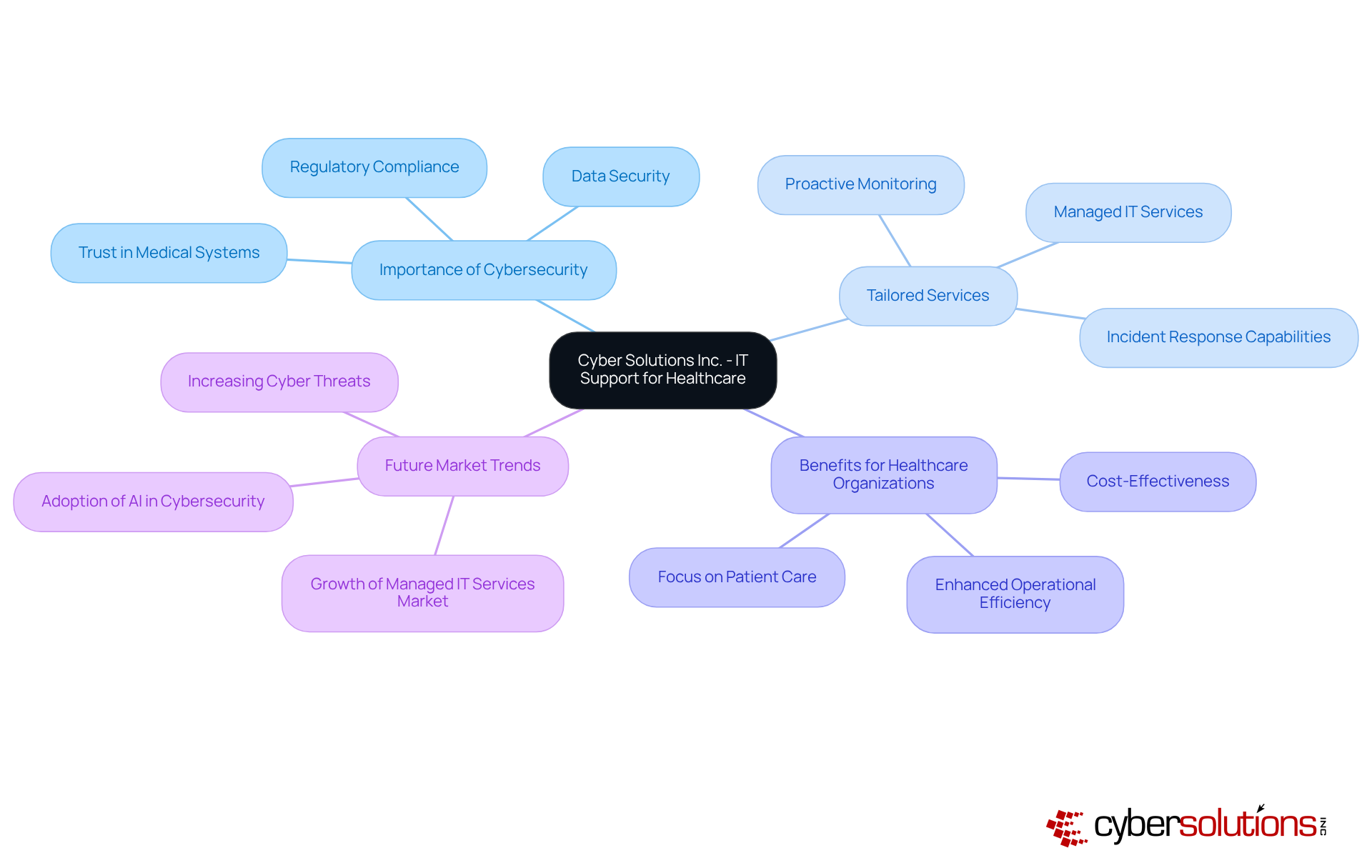
In today's healthcare landscape, the importance of robust IT support cannot be overstated. Cyber Solutions Inc. excels as an IT support company by delivering specifically crafted solutions for medical organizations, addressing the challenges—such as stringent regulations and the imperative of data security. The company offers a comprehensive suite of services designed to enhance operational efficiency and fortify cybersecurity. This includes proactive monitoring and threat detection, essential in a landscape where cyber threats are increasingly sophisticated.
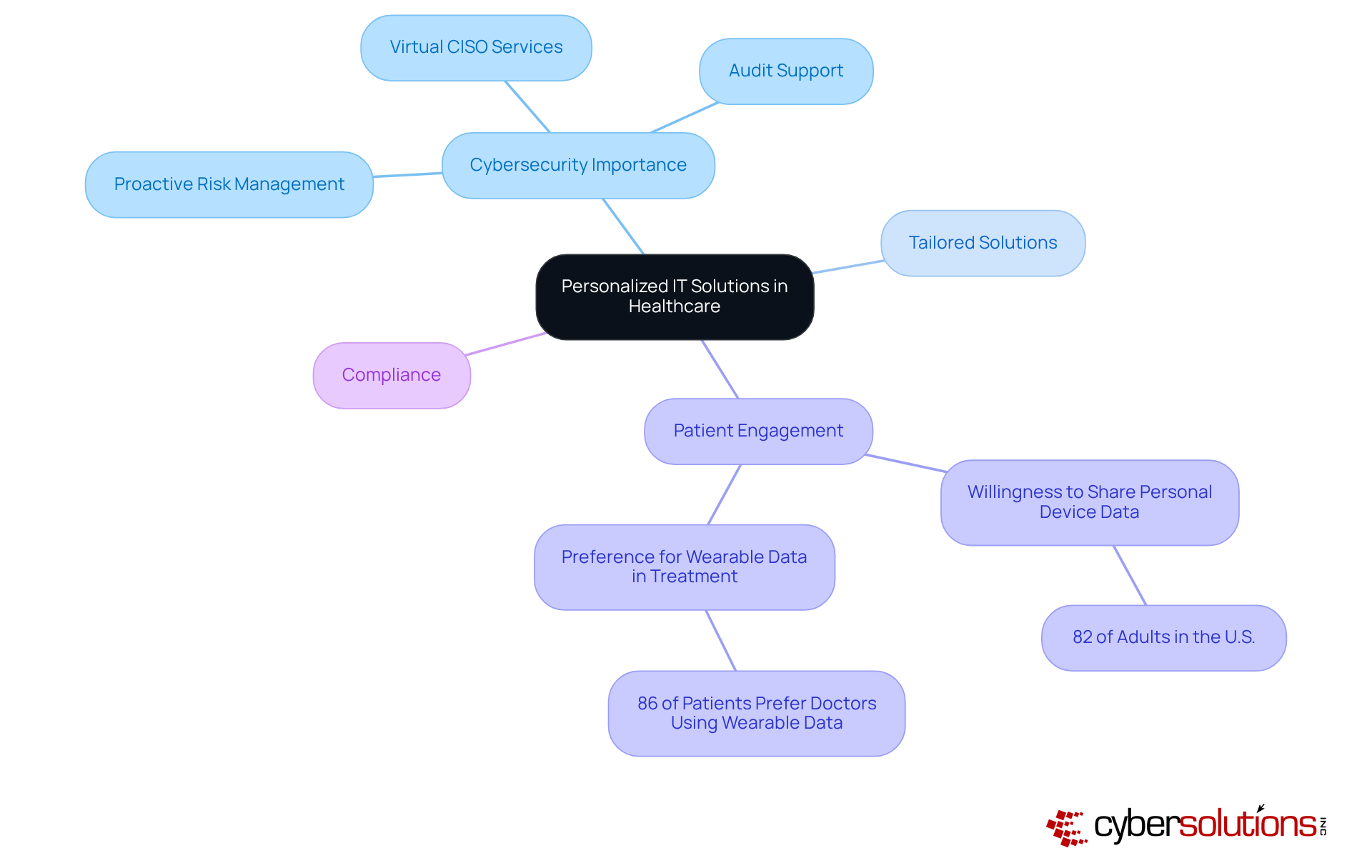
As noted by industry experts, effective IT measures are crucial for protecting patient data and maintaining trust in medical systems. Moreover, the incorporation of personalized IT solutions from an IT support company has demonstrated success in diverse medical environments, optimizing operations and allowing providers to focus on delivering quality patient care without the distractions of IT complexities. With the medical IT market expected to expand substantially, Cyber Solutions Inc. is poised to spearhead the implementation of strategies that not only fulfill compliance standards but also improve overall operational resilience.
In today's healthcare landscape, the importance of cybersecurity cannot be overstated. The help desk provides essential support, which is a vital service that enables healthcare organizations to maintain uninterrupted operations. This constant availability is crucial for swiftly addressing technical issues, significantly reducing downtime—an issue that can disrupt workflows and delay treatments, ultimately impacting patient care. Research indicates that system downtime in medical facilities can lead to financial losses, underscoring the necessity for immediate technical support.
With a dedicated help desk at their disposal, the support team empowers medical providers to tackle any IT issues that arise, ensuring that essential systems remain operational. This proactive approach not only enhances the reliability of medical services but also fosters trust between patients and providers, thereby strengthening the institution's credibility. Furthermore, as an IT support company, Cyber Solutions offers tailored IT solutions and services, including:
This comprehensive support shields against evolving cyber threats such as ransomware and phishing attacks, allowing medical facilities to focus on delivering quality care. As noted by industry specialists, the availability of help desk support is no longer optional; it is essential for modern medical systems to remain efficient, secure, and reliable.
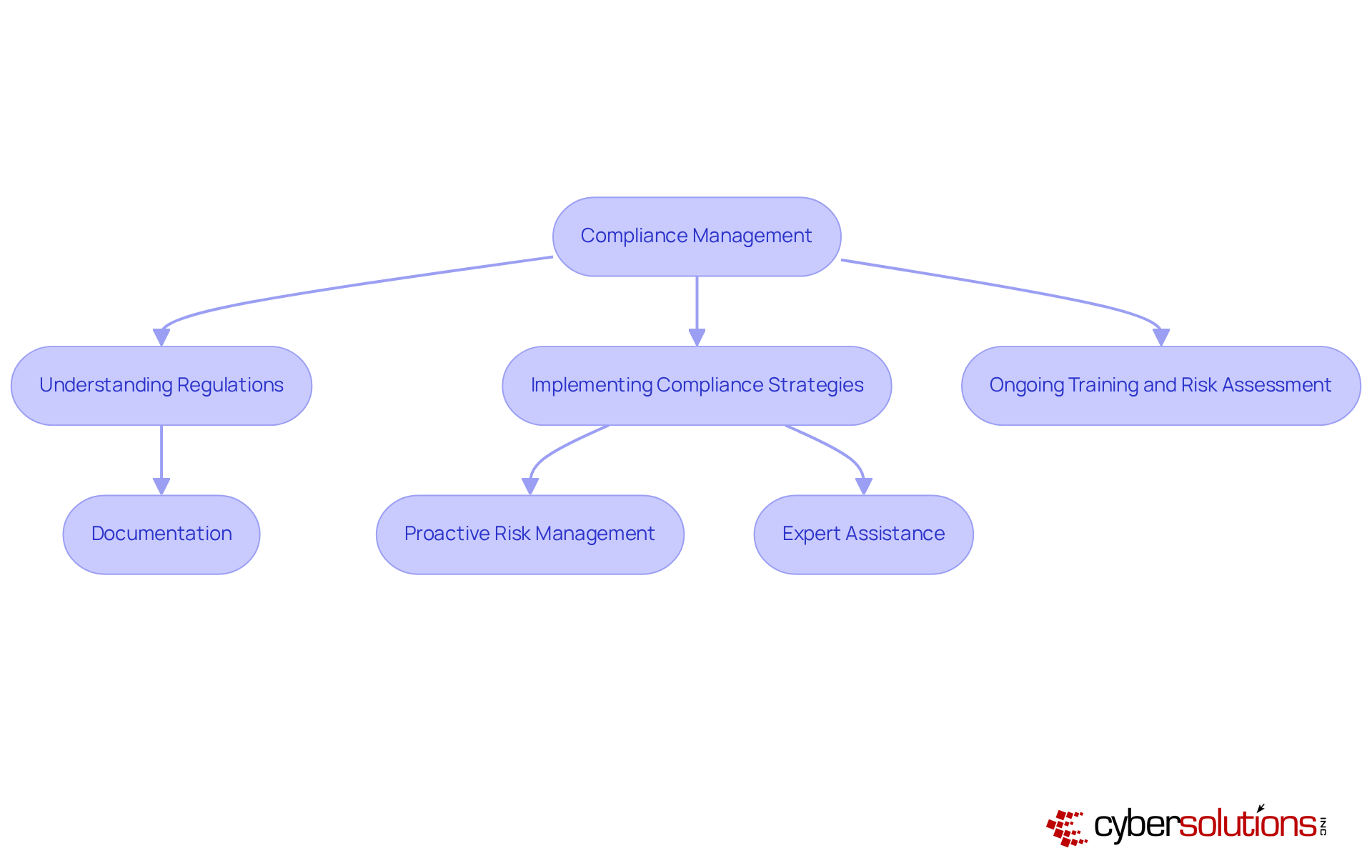
Compliance management is crucial for healthcare organizations, particularly as they navigate the complex landscape of regulations such as HIPAA and HITECH. The IT support company offers robust solutions designed to assist healthcare providers in meeting these stringent requirements. By ensuring that IT systems and processes align with regulatory standards, the support company significantly mitigates the risk of non-compliance. For instance, in 2022, the Office for Civil Rights (OCR) imposed over $28 million in fines for HIPAA violations, highlighting a heightened enforcement environment.
Furthermore, non-compliance can result in severe repercussions, including financial penalties. In 2022, 55% of penalties imposed by OCR were on small medical practices, underscoring that even smaller entities are not exempt from the consequences of regulatory failures. The IT support company empowers healthcare providers to focus on patient care by alleviating the burdens of compliance management, thereby enhancing overall patient safety.
Recent updates in regulations stress the necessity for ongoing training and risk assessments, as regulatory experts emphasize the importance of a proactive compliance strategy. The organization integrates these strategies into its services, which include:
This comprehensive approach positions the organization as an indispensable partner in the medical sector, committed to cultivating a culture of compliance and security.
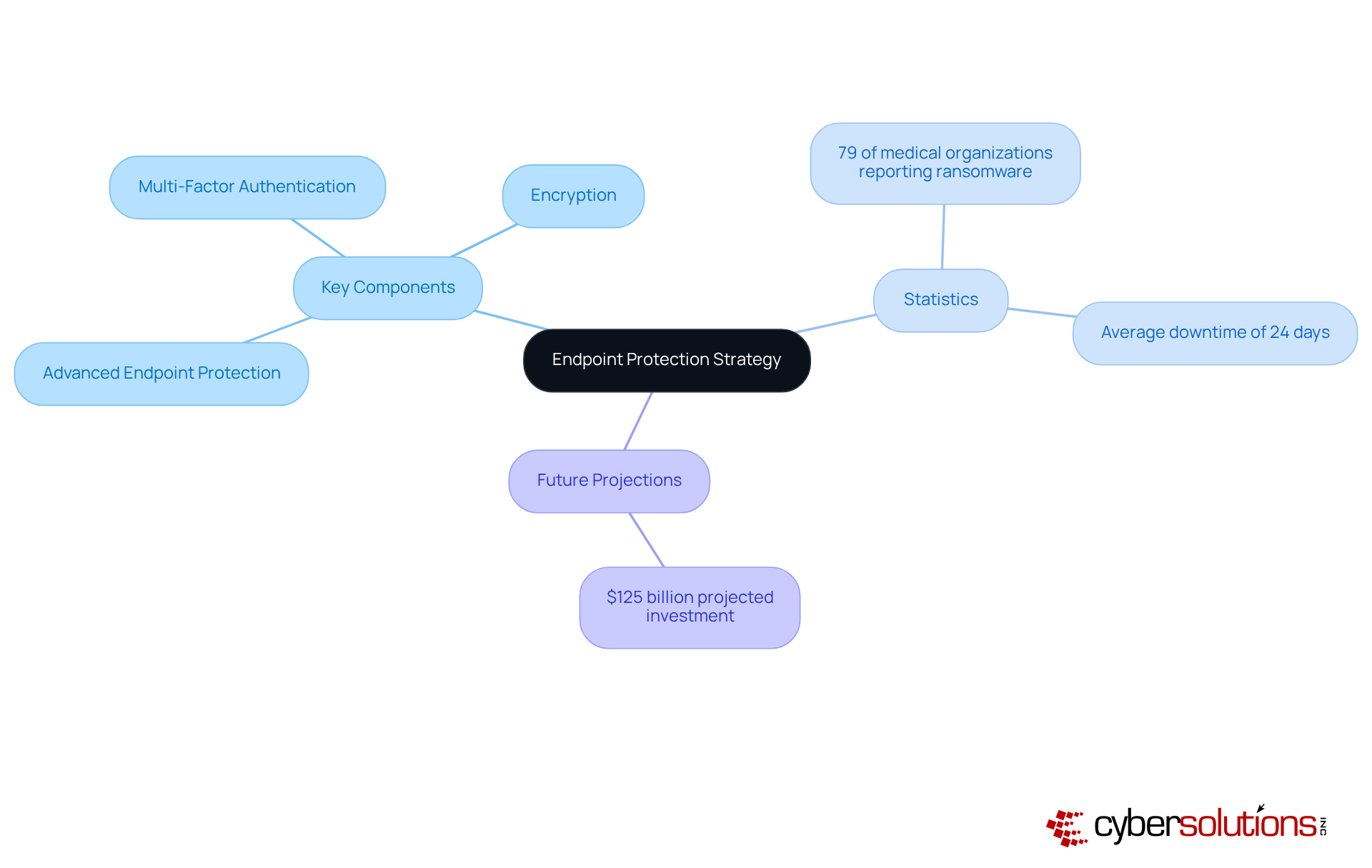
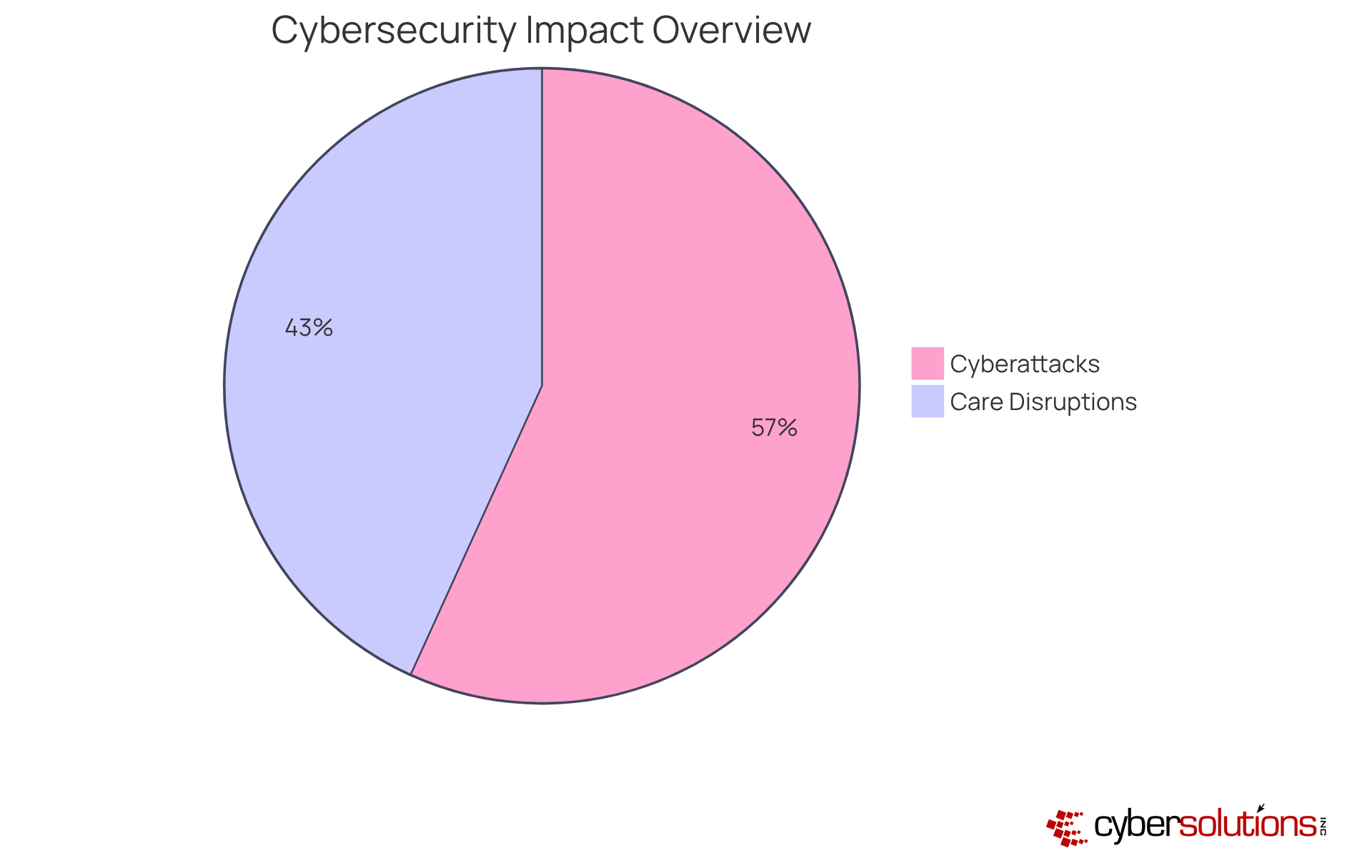
Cyber Solutions Inc. underscores the critical role of endpoint protection as a fundamental aspect of its cybersecurity strategy. As medical institutions face an alarming rise in cyberattacks, cybersecurity has become more essential than ever. The troubling increase in hacking-related incidents, which have been the leading cause of data breaches in U.S. medical facilities since 2014, accentuates this urgency.
Our comprehensive solutions incorporate advanced technologies, including:
to secure all devices connected to the network, ensuring that patient information remains confidential and protected from unauthorized access. This proactive strategy not only fortifies data security but also aids medical entities in adhering to stringent regulatory standards.
With 79% of medical organizations reporting cyber incidents in the past year, and an average downtime of 24 days following such incidents, the necessity for robust cybersecurity is undeniable. By leveraging best practices, including our security assessments and incident response strategies, Cyber Solutions empowers medical providers to navigate the complexities of modern cybersecurity.
Our swift response to security incidents guarantees rapid recovery, ultimately bolstering patient trust and operational integrity. As forecasted by Cybersecurity Ventures, the medical sector is projected to invest over $125 billion in cybersecurity products and services from 2020 to 2025, underscoring the vital need for effective cybersecurity measures.
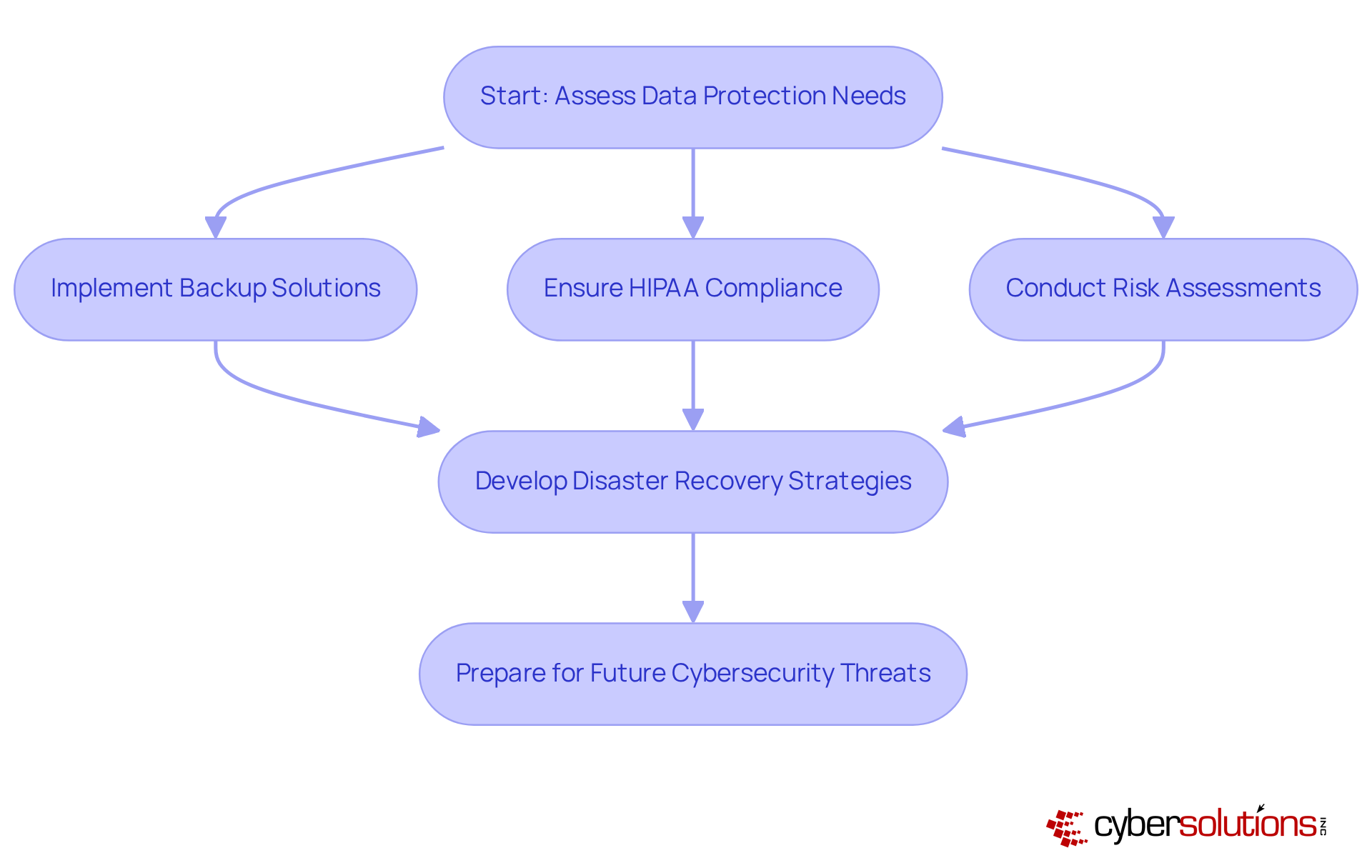
In today's healthcare landscape, safeguarding sensitive data is paramount. Backup solutions are essential for medical entities to protect against data loss and ensure continuity. Tech Inc. offers robust backup options that create secure replicas of critical data, enabling medical providers to recover swiftly from unforeseen events such as cyberattacks or natural disasters.
Our tailored services as an IT support company specifically cater to the unique security and compliance needs of the medical sector, ensuring that organizations can adhere to regulations and procedures. By implementing comprehensive backup strategies and conducting thorough assessments, Tech Inc. guarantees that medical facilities can maintain operations and continue delivering care, even amidst significant disruptions.
With the increasing frequency of cyber threats, it is vital for healthcare organizations to prioritize their disaster recovery plans. Are you prepared to face the challenges that lie ahead? Let Tech Inc., your trusted IT partner, be your partner in navigating these complexities, ensuring that your organization remains resilient and compliant in the face of adversity.
In today's digital landscape, the importance of cybersecurity cannot be overstated. An IT support company employs to proactively identify cyber threats. By continuously monitoring systems for unusual activities and potential vulnerabilities, the company can swiftly detect and respond to threats before they escalate into significant incidents. This proactive strategy not only enhances the security stance of medical providers but also mitigates the risk of data breaches. With the average cost of a medical breach reaching $10.93 million, the necessity for robust cybersecurity measures is evident.
Recent statistics reveal that:
Such alarming figures underscore the critical need for effective cybersecurity solutions. Experts emphasize that investing in cybersecurity is not merely a choice; it is a moral duty to patients and highlights the significance of creating a resilient medical ecosystem. As the landscape of cyber threats continues to evolve, it is imperative for healthcare entities to prioritize advanced detection methods to safeguard sensitive data and ensure operational continuity. By doing so, healthcare organizations can not only protect their assets but also uphold their commitment to patient care.
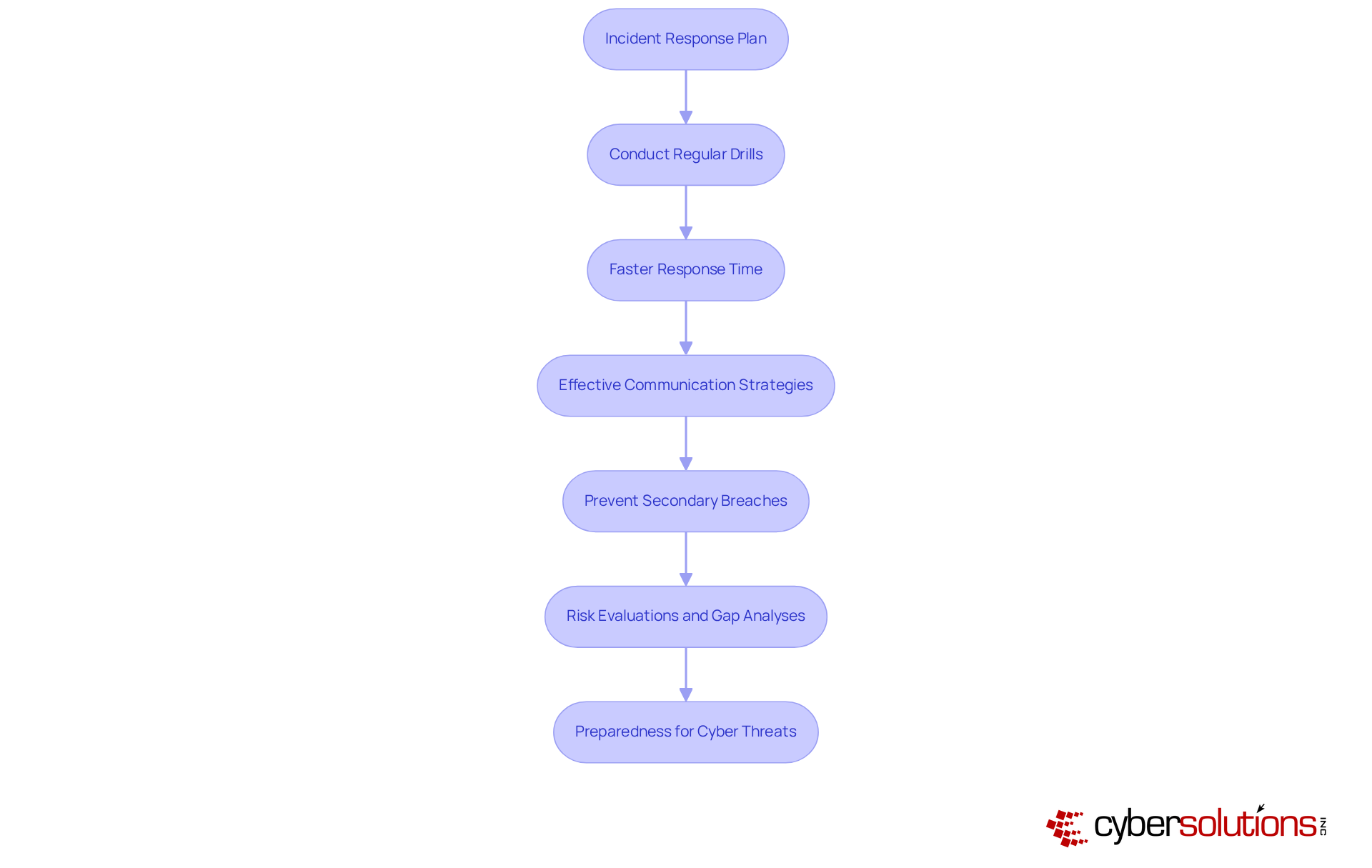
In today's digital landscape, the significance of cybersecurity in healthcare cannot be overstated. In the event of a security breach, the company implements a robust plan designed to facilitate rapid recovery and minimize disruptions for medical institutions. The dedicated team is trained to act swiftly, effectively containing breaches and restoring systems to normal operations with minimal downtime. This capability is crucial for preserving patient trust and ensuring that medical providers can continue offering essential care without major interruptions.
Organizations that conduct incident response planning can respond to incidents 35% faster, underscoring the importance of preparedness in mitigating the impact of cyber threats. Furthermore, during a breach, a well-prepared team can prevent 21% more secondary breaches caused by mismanaged responses. By employing these effective strategies, the company not only assists medical entities in navigating the complexities of compliance but also helps them meet standards such as HIPAA, PCI-DSS, CMMC, SOX, and GDPR.
Our thorough risk evaluations and gap analyses are instrumental in identifying vulnerabilities, ensuring that healthcare entities are well-prepared to address potential threats. As cybersecurity specialist Sean Blanton emphasizes, 'The best-performing companies are closing these gaps with AI, automation, and regular training.' This highlights the urgency for medical entities to establish a comprehensive incident response plan, positioning them to effectively combat the ever-evolving cybersecurity landscape.
In today's healthcare landscape, the importance of cybersecurity cannot be overstated. The company prioritizes regular assessments to uncover and mitigate potential security weaknesses within medical IT systems, relying on its expertise. By systematically assessing the security stance of their clients, the company guarantees that medical entities can effectively address the constantly changing environment of cyber threats. This proactive strategy not only fortifies IT security but also aligns with best practices, as emphasized by industry experts from the field.
Regular evaluations are vital for ensuring adherence to regulations such as HIPAA. These assessments assist entities in identifying areas of non-compliance and executing corrective measures before problems occur. Furthermore, they foster a culture of security awareness among employees, reducing the likelihood of human error and enhancing the overall defense against cyber attacks. In a sector where 92% of medical institutions reported facing at least one cyberattack in the past year, the significance of strong vulnerability management strategies is clear.
By investing in regular assessments and utilizing comprehensive services—including virtual CISO support and threat intelligence from an experienced provider—organizations can safeguard sensitive patient data, maintain trust, and reduce the financial and operational risks related to data breaches. Consider scheduling regular evaluations and engaging with our virtual CISO services to ensure compliance and protect sensitive patient data.
In today's healthcare landscape, cybersecurity is not just a necessity; it is a critical component of operational integrity. By leveraging the expertise of this IT support company, medical institutions can achieve significant cost savings that simplifies budgeting and eliminates unforeseen IT expenses. This all-encompassing pricing package encompasses everything from email licenses to advanced security measures, delivering peace of mind in a single solution.
This proactive approach by the IT support company minimizes downtime, allowing medical providers to function smoothly and efficiently. The company's effective response and remediation procedures ensure that essential medical operations continue with minimal interruption, ultimately enhancing ROI. Resources can be allocated more effectively, enabling a greater focus on patient care. Financial specialists emphasize the importance of investing in technology; organizations that prioritize these investments often witness substantial returns.
Consider this: the average cost of EHR downtime can soar to $7,900 per minute, highlighting the urgency of addressing these issues. By partnering with Digital Security, medical institutions can safeguard their operations through comprehensive IT support and a Zero Trust strategy, thereby improving their financial performance. To fully capitalize on these benefits, organizations should evaluate their current IT infrastructure and explore the advantages of a tailored IT support solution.

The importance of IT support cannot be overstated. Medical organizations face unique challenges that require tailored solutions from an IT support company. Cyber Solutions is dedicated to providing customized services that not only optimize performance but also ensure compliance. By thoroughly understanding each client's specific needs, we integrate personalized IT solutions, including:
This tailored approach enhances operational efficiency and aligns with the growing trend of incorporating technology into financial strategies, enabling service providers to achieve their goals effectively.
As the medical field evolves towards individualized care, the necessity for an IT support company that offers solutions to improve patient outcomes and optimize operations becomes increasingly evident. A recent survey revealed that 82% of adults in the U.S. are willing to share personal device data to take a more active role in their health. This underscores the demand for services that facilitate better patient engagement.
Successful implementations of tailored IT strategies have demonstrated substantial benefits. For instance, medical providers utilizing AI-driven analytics have reported enhanced patient care through data insights. Notably, 86% of patients indicate a preference for doctors who incorporate wearable data into their treatment strategies. This trend highlights the critical role that an IT support company plays in facilitating data-driven decision-making and enhancing patient care.
Moreover, the significance of cybersecurity cannot be overlooked. By preventing unauthorized software from executing, application allowlisting significantly decreases the attack surface and assists entities in meeting stringent compliance requirements, including HIPAA. Addressing the unique needs of medical organizations is vital for promoting innovation and enhancing patient care. By focusing on personalized IT solutions, Cyber Solutions Inc. positions itself as an IT support company that plays a vital role in navigating the complexities of modern healthcare, ultimately driving better outcomes for both providers and patients.
Choosing an IT support company tailored for healthcare is not merely a strategic decision; it is a crucial investment in the integrity and efficiency of medical organizations. The unique challenges faced by healthcare providers, from stringent regulatory compliance to the protection of sensitive patient data, underscore the necessity for specialized IT solutions. By partnering with an experienced IT support company like Cyber Solutions Inc., healthcare organizations can enhance operational resilience, improve cybersecurity measures, and ultimately focus more on delivering quality patient care.
Key insights from the article highlight the multifaceted benefits of IT support in healthcare:
As the healthcare sector continues to evolve, the importance of investing in comprehensive IT support cannot be overstated. Organizations are encouraged to evaluate their current IT strategies and consider the advantages of tailored support services. By prioritizing cybersecurity and operational efficiency, healthcare providers not only protect their assets but also enhance patient trust and care quality. Embracing these IT solutions is a vital step toward navigating the complexities of modern healthcare and ensuring a resilient future for both providers and patients.
What services does Cyber Solutions Inc. provide for healthcare organizations?
Cyber Solutions Inc. offers tailored IT support specifically for medical organizations, including proactive monitoring, expert incident response, endpoint protection, data encryption, and 24/7 network monitoring and alert services.
Why is cybersecurity important for healthcare organizations?
Cybersecurity is crucial for protecting sensitive patient data, maintaining trust in medical systems, and ensuring compliance with regulatory standards. Effective cybersecurity measures help safeguard against increasingly sophisticated cyber threats.
How does Cyber Solutions Inc. enhance operational efficiency for medical providers?
By providing managed IT services, Cyber Solutions Inc. optimizes operations, allowing healthcare providers to focus on delivering quality patient care without the distractions of IT complexities.
What is the significance of 24/7 help desk support in healthcare IT?
24/7 help desk support is vital for maintaining uninterrupted operations in medical organizations. It enables swift resolution of technical issues, significantly reducing downtime that can disrupt workflows and impact patient care.
What are the consequences of non-compliance with healthcare regulations?
Non-compliance with regulations such as HIPAA and GDPR can lead to substantial legal penalties, financial losses, and reputational damage. In 2022, significant fines were imposed for HIPAA violations, affecting even small medical practices.
How does Cyber Solutions Inc. assist with compliance management?
Cyber Solutions Inc. provides robust compliance management services that include extensive reporting and documentation tailored to HIPAA standards, proactive risk management, and expert assistance through fractional or virtual CISO services.
What recent updates in HIPAA compliance should healthcare organizations be aware of?
Recent updates emphasize the necessity for ongoing training and risk assessments, highlighting the importance of a proactive compliance approach to mitigate risks associated with regulatory failures.
How does Cyber Solutions Inc. contribute to patient safety?
By alleviating the burdens of compliance management and enhancing overall security, Cyber Solutions Inc. empowers medical organizations to focus on patient care, ultimately improving patient safety.