
To optimize business IT support for healthcare CFOs, it is crucial to recognize the unique challenges they face. This article outlines four key steps:
Each step underscores the necessity of aligning IT strategies with operational goals, ensuring compliance with regulations such as HIPAA, and enhancing overall efficiency to improve patient care. By following these steps, healthcare CFOs can address the pressing demands of their roles and ensure robust IT support that meets both regulatory requirements and operational objectives.
In an industry where precision and compliance are paramount, the significance of cybersecurity in healthcare cannot be overstated. Healthcare CFOs face the daunting task of optimizing IT support to enhance operational efficiency while safeguarding sensitive patient information. This guide outlines essential steps to:
Providing CFOs with a roadmap to align technology with organizational goals. As the digital landscape evolves, healthcare leaders must consider how their IT strategies can not only comply with regulations but also adapt to the rapid pace of technological change.
How can they ensure that these strategies effectively address the unique challenges presented by cybersecurity threats?
Recognizing distinct IT requirements is crucial for healthcare organizations to ensure optimal operational efficiency and compliance. The following key steps will guide your assessment:
A comprehensive requirements evaluation not only aligns IT support with operational objectives but also enhances the quality of patient care. As Simon Lorenz, co-founder of Klara, emphasizes, effective communication and understanding of organizational requirements are essential for successful IT implementation in the medical field. Furthermore, nearly 50% of all medication errors occur when a medication is prescribed or ordered, underscoring the critical need for robust IT systems that can help mitigate such risks. By following these steps, CFOs in the medical sector can ensure their IT strategies are resilient, compliant, and tailored to their unique operational challenges.

In today's digital landscape, the significance of robust cybersecurity in healthcare cannot be overstated. Evaluating IT support providers is critical, and organizations must consider the following essential criteria:
By thoroughly assessing potential providers of business IT support against these criteria, healthcare organizations can ensure they collaborate with firms that grasp the complexities of healthcare IT and can provide customized solutions to enhance operational efficiency and compliance.

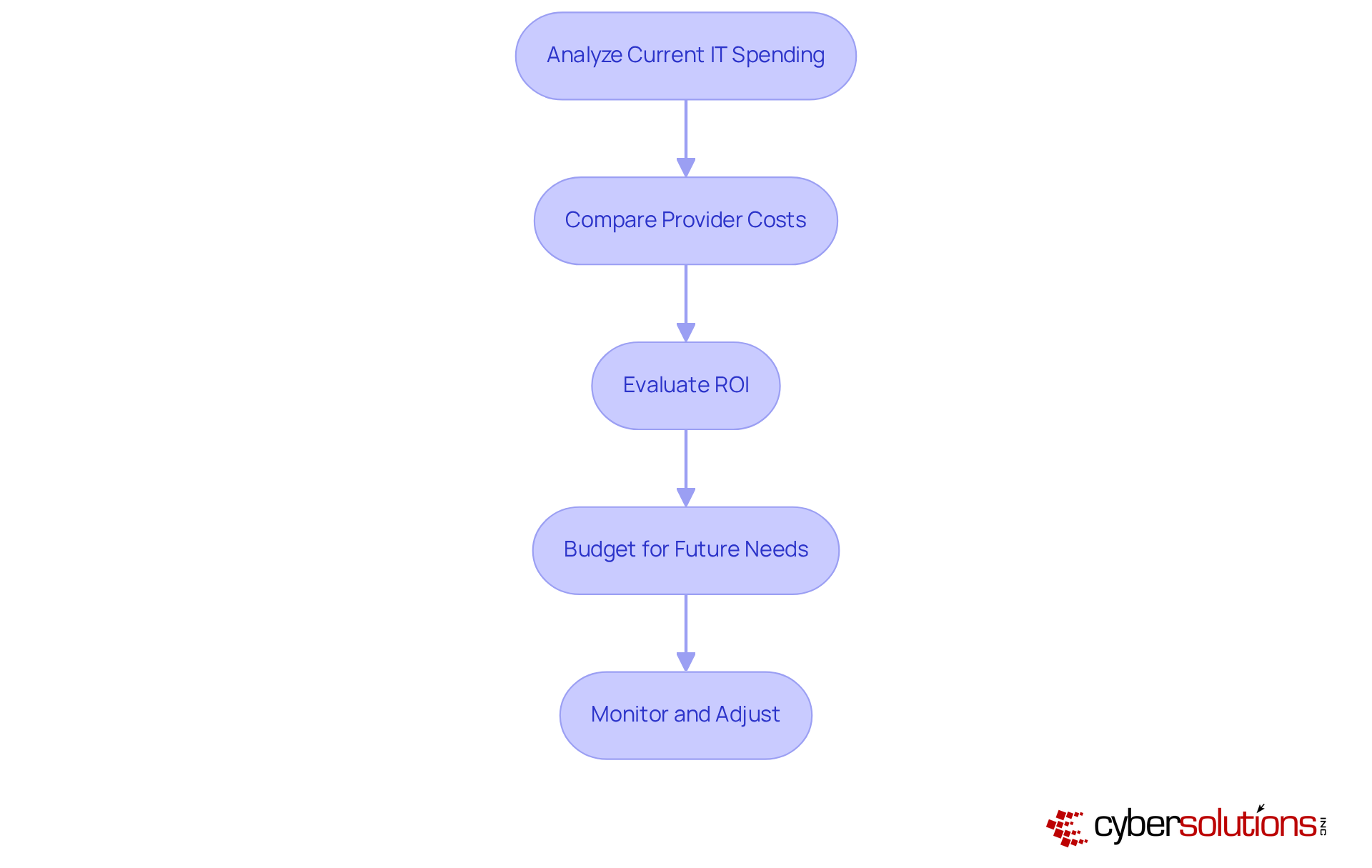
To ensure budget alignment and assess cost-effectiveness in healthcare IT spending, it is essential to follow these structured steps:
By conducting a thorough cost assessment, healthcare organizations can make informed decisions that enhance both operational efficiency and financial health.
To establish effective communication and support protocols, it is imperative to implement the following steps:
By establishing robust communication and support protocols, you can significantly enhance the efficiency of your IT support and ensure that staff can effectively address their technology needs.

Optimizing IT support for healthcare CFOs is not just beneficial; it is essential for enhancing operational efficiency, ensuring compliance, and ultimately improving patient care. Understanding and addressing the unique IT needs of healthcare organizations allows for the creation of a robust framework that meets regulatory standards while supporting the dynamic environment of healthcare.
Key strategies encompass:
Moreover, establishing clear communication and support protocols significantly enhances the effectiveness of IT support, empowering healthcare staff to address technology challenges swiftly and efficiently.
In conclusion, integrating strategic IT support transcends mere technical necessity; it is a critical component of healthcare management that directly influences patient safety and organizational success. By prioritizing these steps, CFOs can guide their organizations toward a future where technology not only enhances operational capabilities but also improves patient outcomes. Implementing these best practices will safeguard sensitive information and foster a culture of continuous improvement in healthcare IT.
Why is it important for healthcare organizations to identify their unique IT support needs?
Identifying unique IT support needs is crucial for healthcare organizations to ensure optimal operational efficiency and compliance with regulatory standards.
What is the first step in assessing IT support needs in healthcare?
The first step is to conduct a needs assessment by engaging with various departments—clinical, administrative, and IT—to gather insights on their specific IT challenges and requirements.
How do compliance requirements impact IT support in healthcare?
Compliance requirements, particularly standards like HIPAA, mandate specific IT practices that are essential for maintaining compliance and safeguarding patient information.
What is application allowlisting, and how does it enhance compliance efforts?
Application allowlisting ensures that only approved applications operate on IT systems, reducing the risk of unauthorized access and data breaches. It includes features like continuous monitoring of application activity and centralized management of allowlists to strengthen security.
What should be analyzed when evaluating current IT infrastructure?
Existing IT systems should be reviewed to identify gaps in support, security, and functionality, helping to pinpoint areas that require immediate attention and improvement.
How should healthcare organizations prioritize their IT requirements?
Organizations should rank identified requirements based on their urgency and potential impact on patient care and operational efficiency, allowing for strategic resource allocation and effective decision-making.
What role does cybersecurity play in healthcare IT support?
Comprehensive cybersecurity solutions, including proactive risk management and audit assistance, are essential for safeguarding patient health information (PHI) and ensuring adherence to HIPAA standards.
What is the overall benefit of conducting a thorough IT support needs assessment in healthcare?
A comprehensive evaluation aligns IT support with operational objectives and enhances the quality of patient care, helping to mitigate risks such as medication errors.