
In today's digital landscape, robust cybersecurity measures are paramount for healthcare organizations. Effective firewall services strategies are crucial for maximizing compliance by safeguarding sensitive information and ensuring adherence to regulatory standards such as HIPAA and GDPR. By implementing robust firewall measures—like access control policies and regular audits—organizations not only protect against data breaches but also demonstrate their commitment to regulatory compliance. This proactive approach mitigates potential financial and reputational risks, reinforcing the importance of cybersecurity in healthcare.
How prepared is your organization to face these challenges?
In an era where data breaches can cost healthcare organizations millions, the importance of robust firewall services is paramount. These digital sentinels are essential not only for safeguarding sensitive information but also for ensuring compliance with stringent regulations such as HIPAA and GDPR. As the landscape of cyber threats continues to evolve, healthcare organizations must ask: how can they effectively leverage firewall services to enhance their compliance and security posture? By exploring the types, best practices, and strategic management of firewall services, we uncover critical insights that can protect both data and reputation in an increasingly complex digital environment.
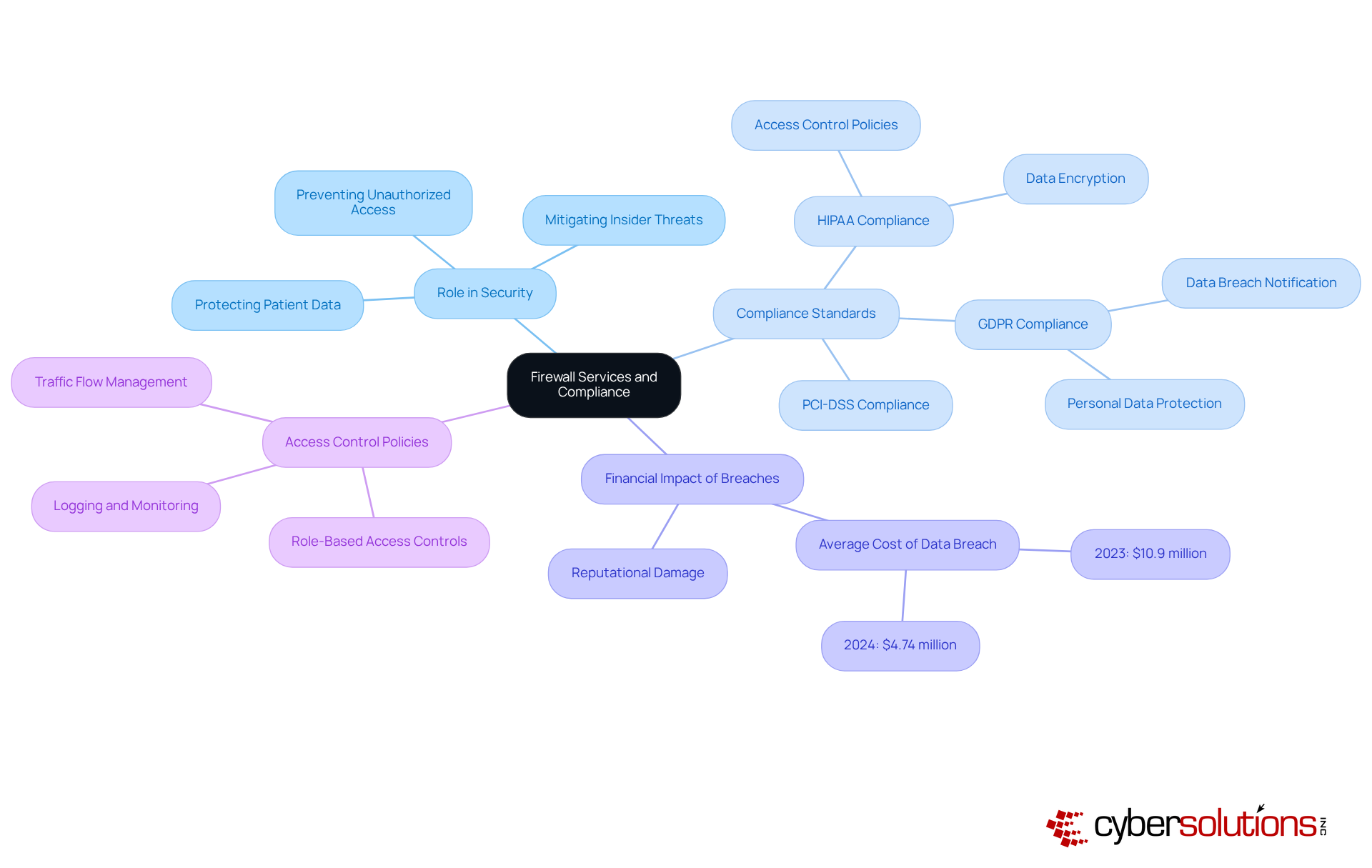
In today's digital landscape, cybersecurity stands as a paramount concern for healthcare organizations. Firewall services act as an essential barrier between trusted internal networks and untrusted external environments, effectively monitoring and managing both incoming and outgoing traffic in accordance with established protection protocols. Their role in is indispensable; security systems are integral in helping entities meet regulatory standards such as GDPR, HIPAA, and PCI-DSS by safeguarding sensitive information from unauthorized access.
Consider this: in 2023, the average cost of a data breach in healthcare soared to $10.9 million. This staggering figure underscores the financial ramifications of insufficient security measures. By implementing robust security protocols, organizations can demonstrate a commitment to data protection, significantly reducing the likelihood of breaches and regulatory violations. A healthcare provider that effectively utilizes these measures not only protects patient data but also ensures compliance with HIPAA regulations, thus averting potential fines and reputational harm.
Moreover, firewall services facilitate the implementation of access control policies that are essential for adhering to HIPAA and GDPR. This proactive approach ultimately enhances the overall security posture of the organization, ensuring that patient information remains secure while fostering trust with stakeholders. As healthcare continues to evolve, the integration of comprehensive cybersecurity strategies will be crucial for navigating the complexities of regulatory compliance and protecting sensitive data.
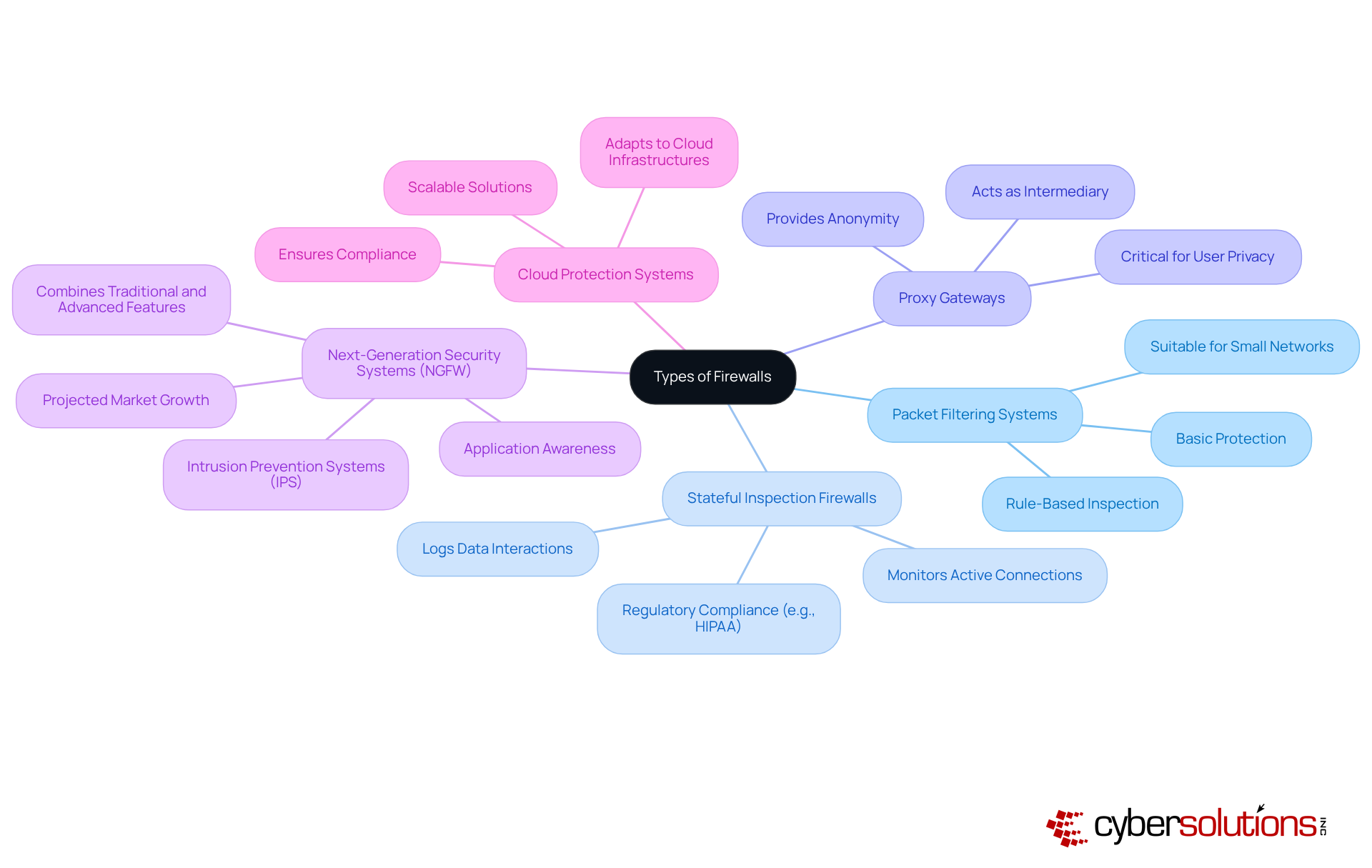
In today's digital landscape, cybersecurity is paramount, especially in healthcare. The role of firewall services is crucial in safeguarding sensitive information from increasingly sophisticated threats. Understanding the various is essential for organizations to protect their networks effectively.
Choosing the appropriate type of firewall services is essential for compliance. For instance, healthcare entities may require stateful inspection systems to meet HIPAA standards, while financial institutions could benefit from next-generation security solutions to guard against advanced cyber threats. IT protection experts emphasize that the selection of a network barrier should align with the specific regulatory demands and safety needs of the organization.
To maximize the effectiveness of their cybersecurity posture, organizations must embrace .
By adhering to these best practices, organizations can substantially improve their security posture with the implementation of firewall services while ensuring alignment with relevant regulations, ultimately safeguarding sensitive data and maintaining trust in their digital operations.

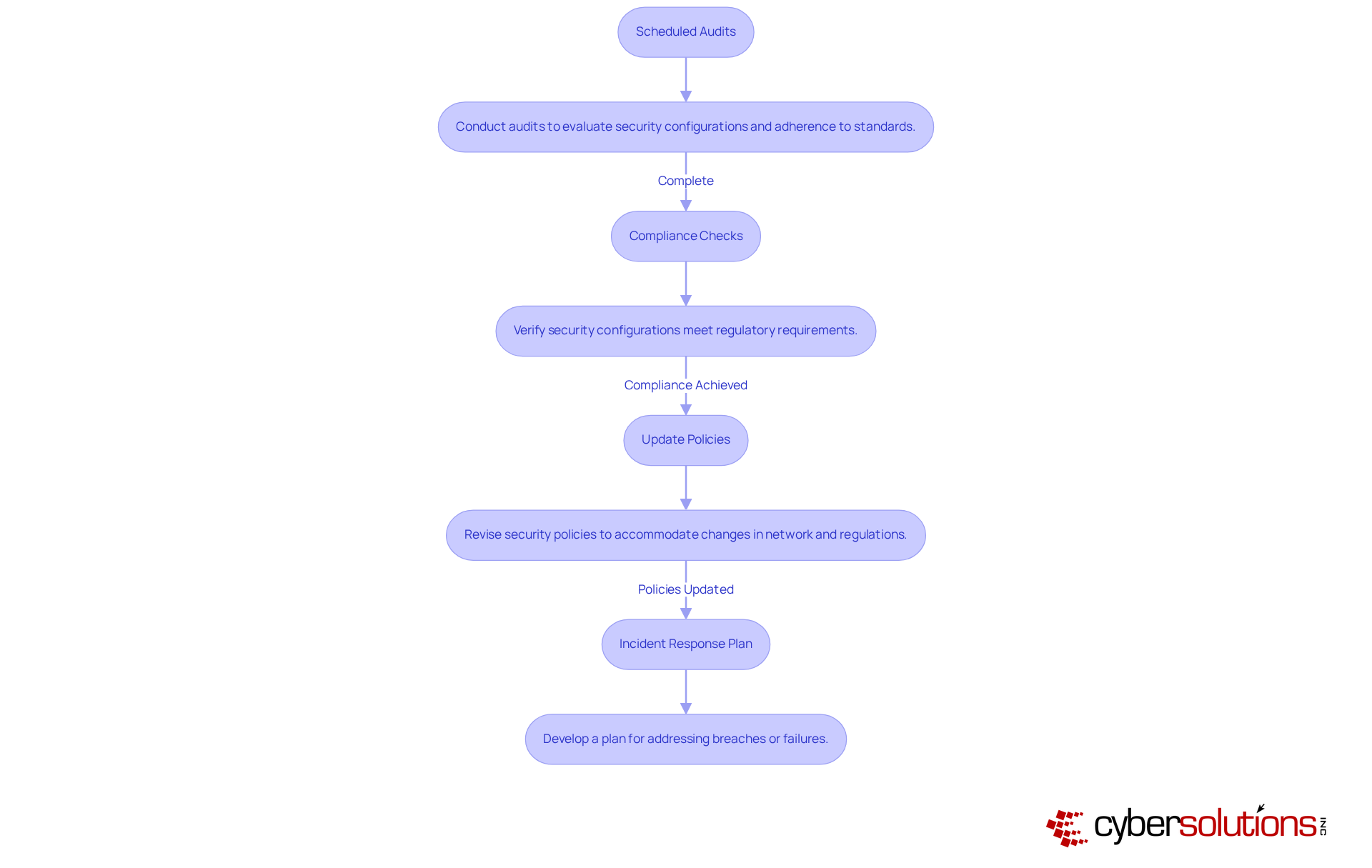
Regular reviews and updates are vital for effective security management and compliance. Organizations must embrace strategic approaches to fortify their defenses against evolving threats:
By implementing these strategies, organizations can sustain a robust security posture and ensure ongoing compliance with relevant regulations, ultimately enhancing their resilience against evolving cyber threats.
In the realm of healthcare, the importance of robust cybersecurity cannot be overstated. Firewall services play a critical role in safeguarding sensitive information and ensuring compliance with essential regulations such as HIPAA, GDPR, and PCI-DSS. By acting as a protective barrier against unauthorized access, these services not only mitigate the risk of data breaches but also shield organizations from the financial repercussions associated with regulatory penalties.
As we explored throughout this article, various types of firewall services—from basic packet filtering systems to advanced next-generation firewalls—each cater to specific needs and applications. This underscores the necessity of selecting the right solution that aligns with an organization’s regulatory requirements and security demands. Best practices for firewall configuration, including the implementation of a default deny policy and conducting regular audits, further bolster security measures and ensure compliance.
Ultimately, organizations must prioritize the integration of comprehensive cybersecurity strategies. A proactive approach to compliance management is essential; it not only protects sensitive data but also cultivates trust with stakeholders and sustains an organization’s reputation in an increasingly digital landscape. Taking decisive action now to optimize firewall services will pave the way for a more secure future, safeguarding both the organization and the individuals it serves.
What are firewall services and their primary function?
Firewall services act as a barrier between trusted internal networks and untrusted external environments, monitoring and managing both incoming and outgoing traffic according to established protection protocols.
Why are firewall services important for healthcare organizations?
They are crucial for ensuring compliance with regulatory standards such as GDPR, HIPAA, and PCI-DSS by safeguarding sensitive information from unauthorized access.
What is the financial impact of data breaches in healthcare?
In 2023, the average cost of a data breach in healthcare reached $10.9 million, highlighting the financial consequences of inadequate security measures.
How do robust security protocols benefit healthcare organizations?
Implementing strong security protocols demonstrates a commitment to data protection, reduces the likelihood of breaches and regulatory violations, and helps avoid potential fines and reputational damage.
How do firewall services support compliance with HIPAA and GDPR?
Firewall services facilitate the implementation of access control policies that are essential for adhering to HIPAA and GDPR regulations, enhancing the overall security posture of the organization.
What is the overall significance of integrating cybersecurity strategies in healthcare?
Comprehensive cybersecurity strategies are crucial for navigating regulatory compliance complexities and protecting sensitive data as the healthcare landscape continues to evolve.