Introduction
Co-management in IT signifies a transformative strategy that empowers organizations to leverage the expertise of managed service providers while maintaining oversight of their internal operations. This strategic alliance not only boosts operational efficiency but also tackles pressing challenges, such as the cybersecurity threats stemming from human error.
As businesses contemplate the adoption of this model, they may ponder:
- What critical steps are necessary for effective co-management implementation?
- How can organizations ensure they fully capitalize on the advantages of this collaborative approach?
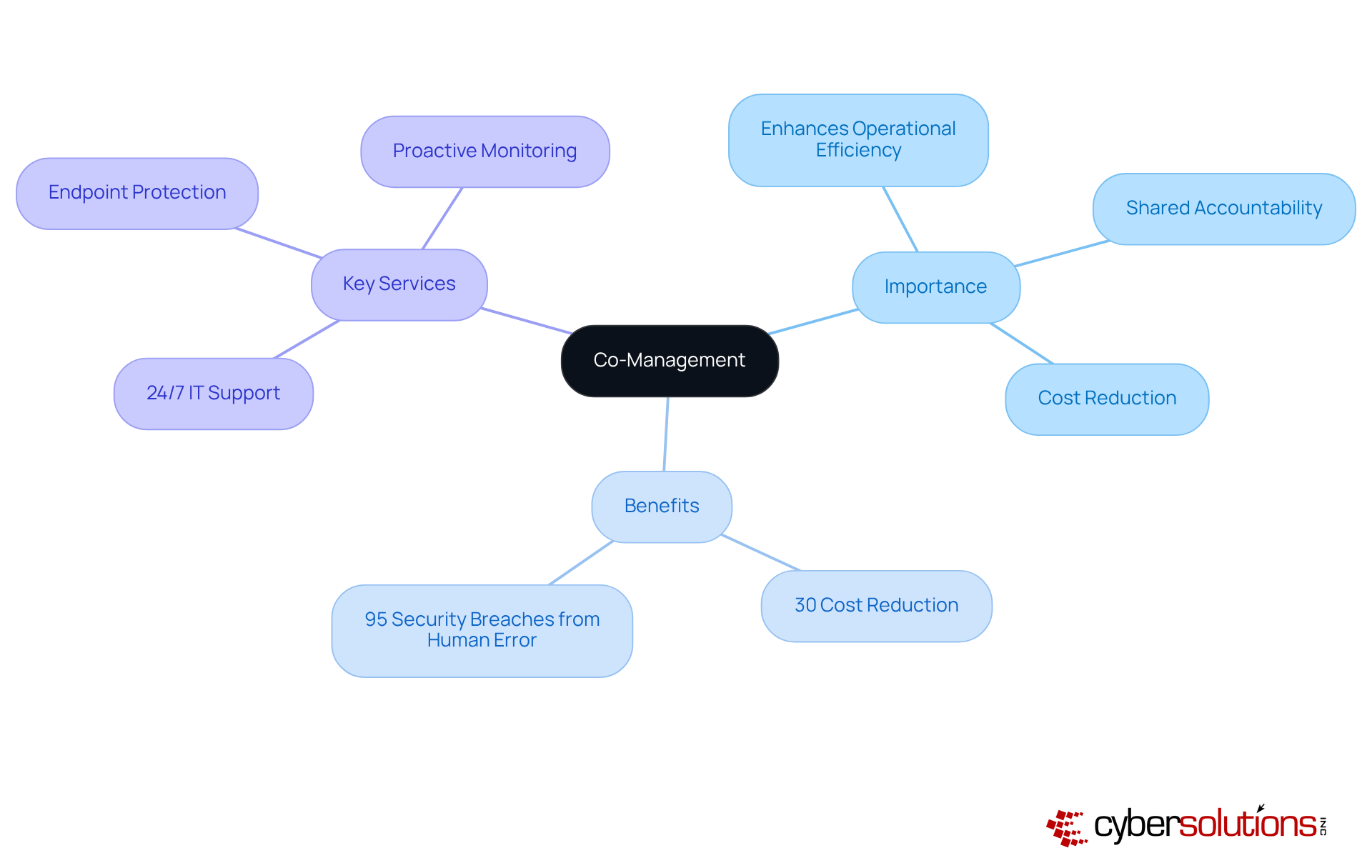
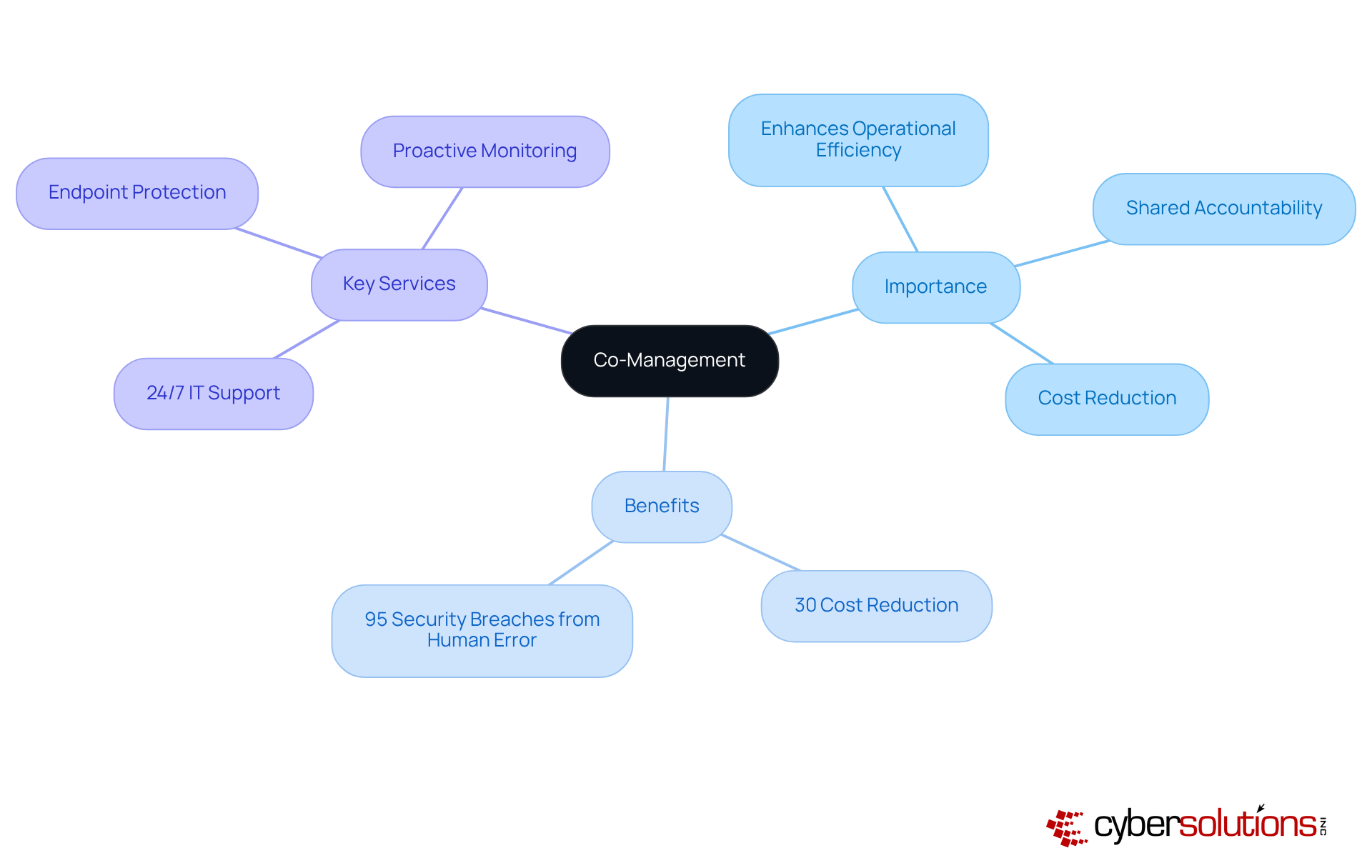
Define Co-Management and Its Importance
Co-management represents a strategy. This model enables businesses to leverage the specialized expertise of managed service providers (MSPs) while maintaining control over their internal IT operations. The importance of co-managing lies in its ability to enhance efficiency by combining the strengths of both parties.
For example, organizations can benefit from the MSP's advanced skills in cybersecurity, particularly critical as 95 percent of security breaches arise from human error. This partnership not only improves incident response times but also fosters a culture of collaboration, enabling teams to co-manage resource allocation and risk management more effectively.
Evidence shows that effective joint management partnerships can lead to a 30% reduction in costs while simultaneously improving service quality. By integrating collaborative management into their IT strategy, businesses can adeptly navigate the complexities of modern digital threats, ensuring a resilient and secure operational framework.
Key services provided by Cyber Solutions include:
All tailored to maximize ROI through bespoke IT and cybersecurity services.
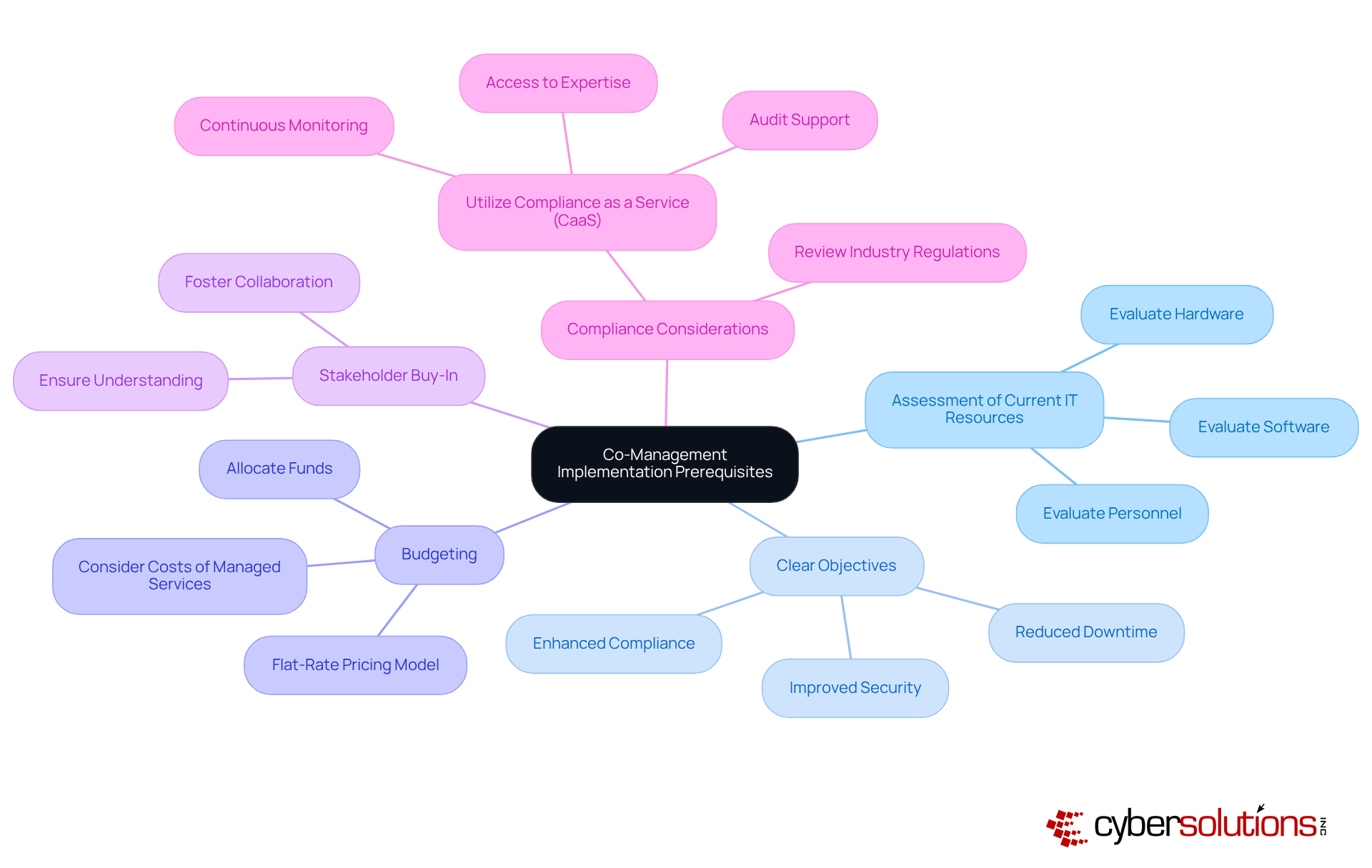
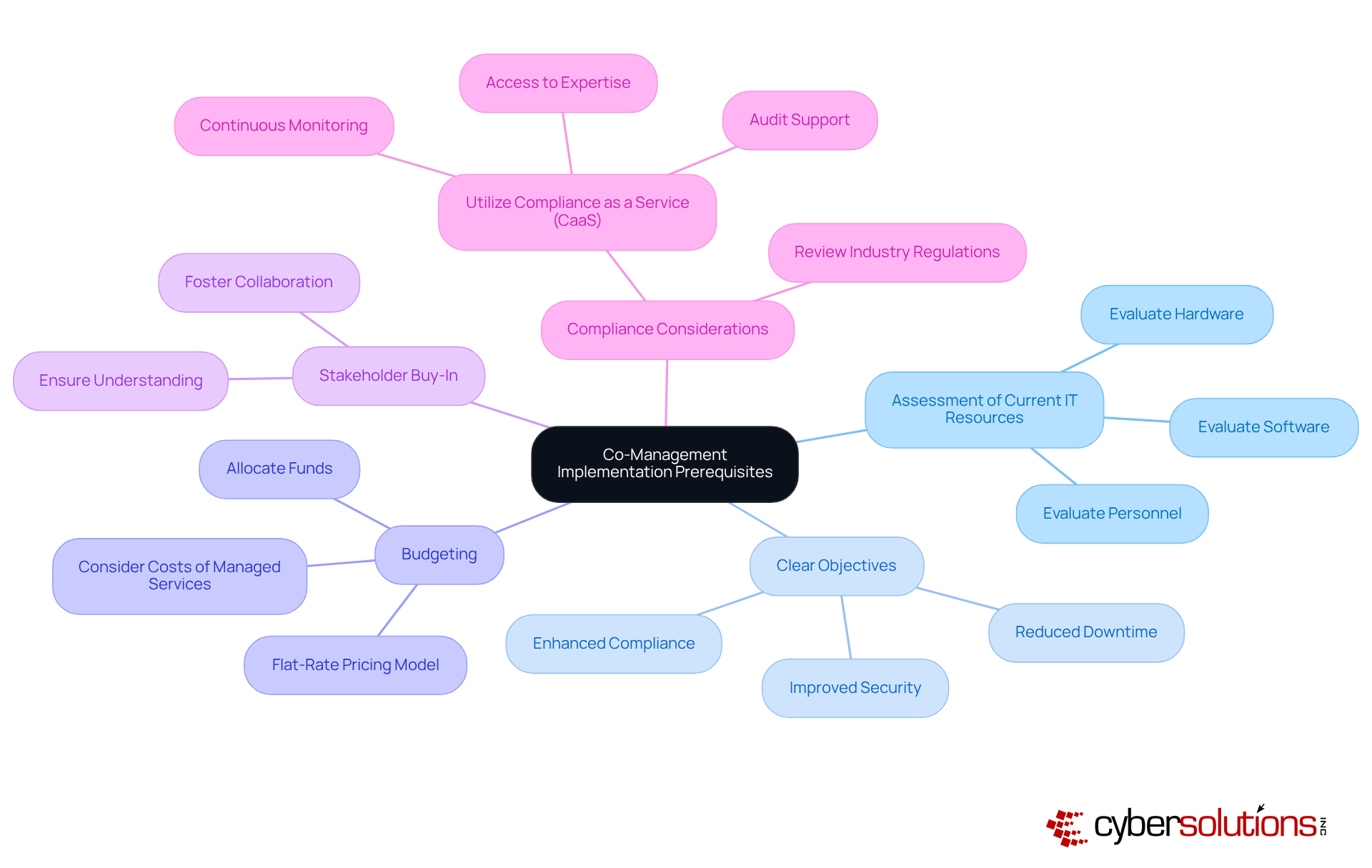
Identify Prerequisites for Co-Management Implementation
Before organizations co-manage their resources, they must thoroughly evaluate their existing infrastructure. The significance of this evaluation cannot be overstated. Key prerequisites include:
- Assessment of Current IT Resources: Conduct a comprehensive evaluation of existing hardware, software, and personnel to identify both strengths and weaknesses.
- Clear Objectives: Clearly define your goals to co-manage collaborative efforts, such as improved security, reduced downtime, or enhanced compliance.
- Budgeting: Budgeting involves allocating appropriate funds for both internal and external resources, carefully considering the costs associated with implementation and the potential return on investment. The flat-rate pricing model can simplify budgeting by providing predictable monthly costs.
- Stakeholder Engagement: It is crucial to ensure that all relevant stakeholders comprehend and endorse the initiative to co-manage, fostering a collaborative environment that is essential for success.
- Compliance Considerations: Review industry regulations that may impact your IT operations, ensuring that your strategy to co-manage aligns with compliance requirements. Utilizing Compliance as a Service (CaaS) can significantly facilitate this process, equipping businesses with the expertise needed to navigate complex regulatory landscapes. CaaS offers substantial benefits to small and medium-sized enterprises by providing access to enterprise-level compliance expertise without the prohibitive costs of hiring in-house staff. Industries such as healthcare, finance, and legal can particularly benefit from CaaS, as it ensures continuous monitoring and audit support.
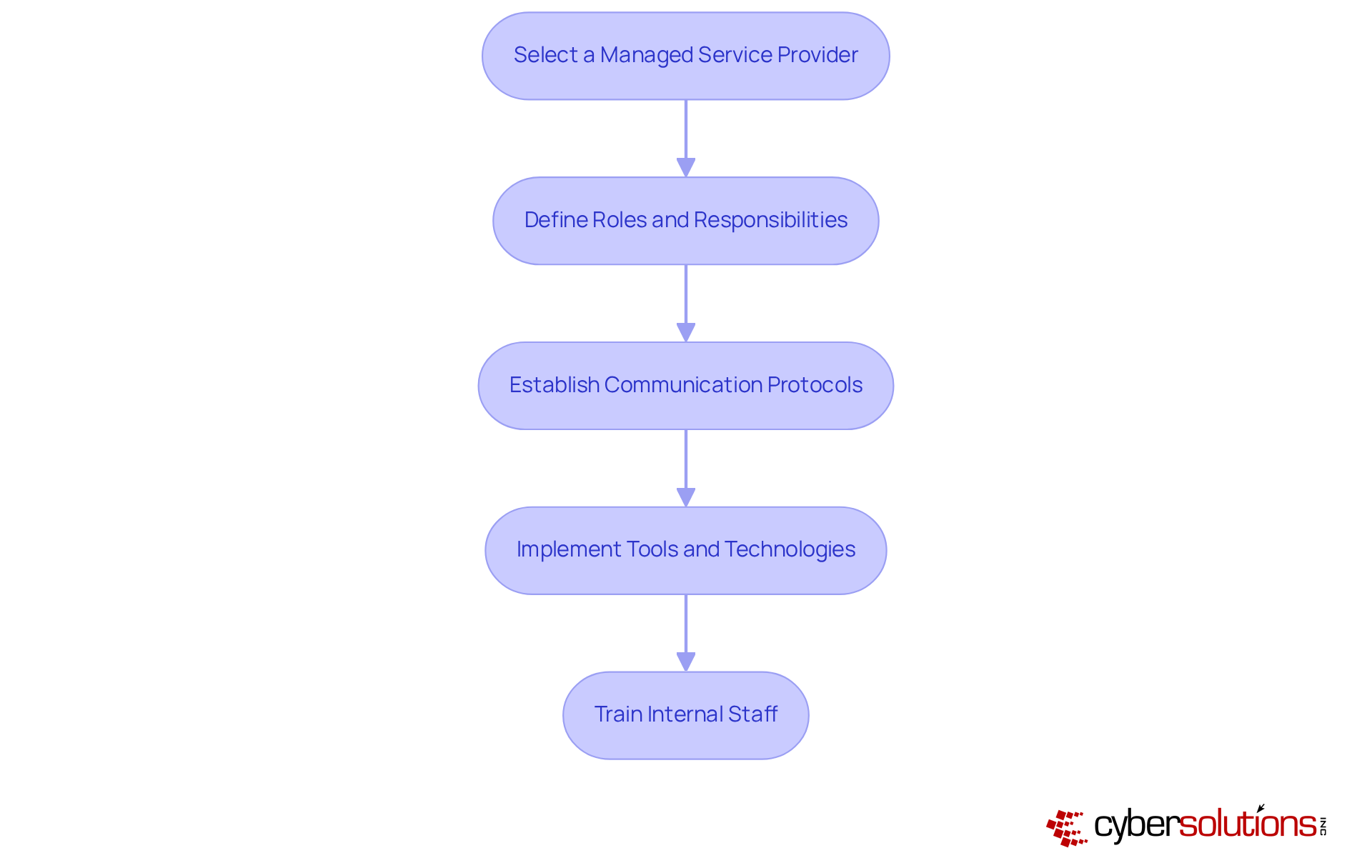
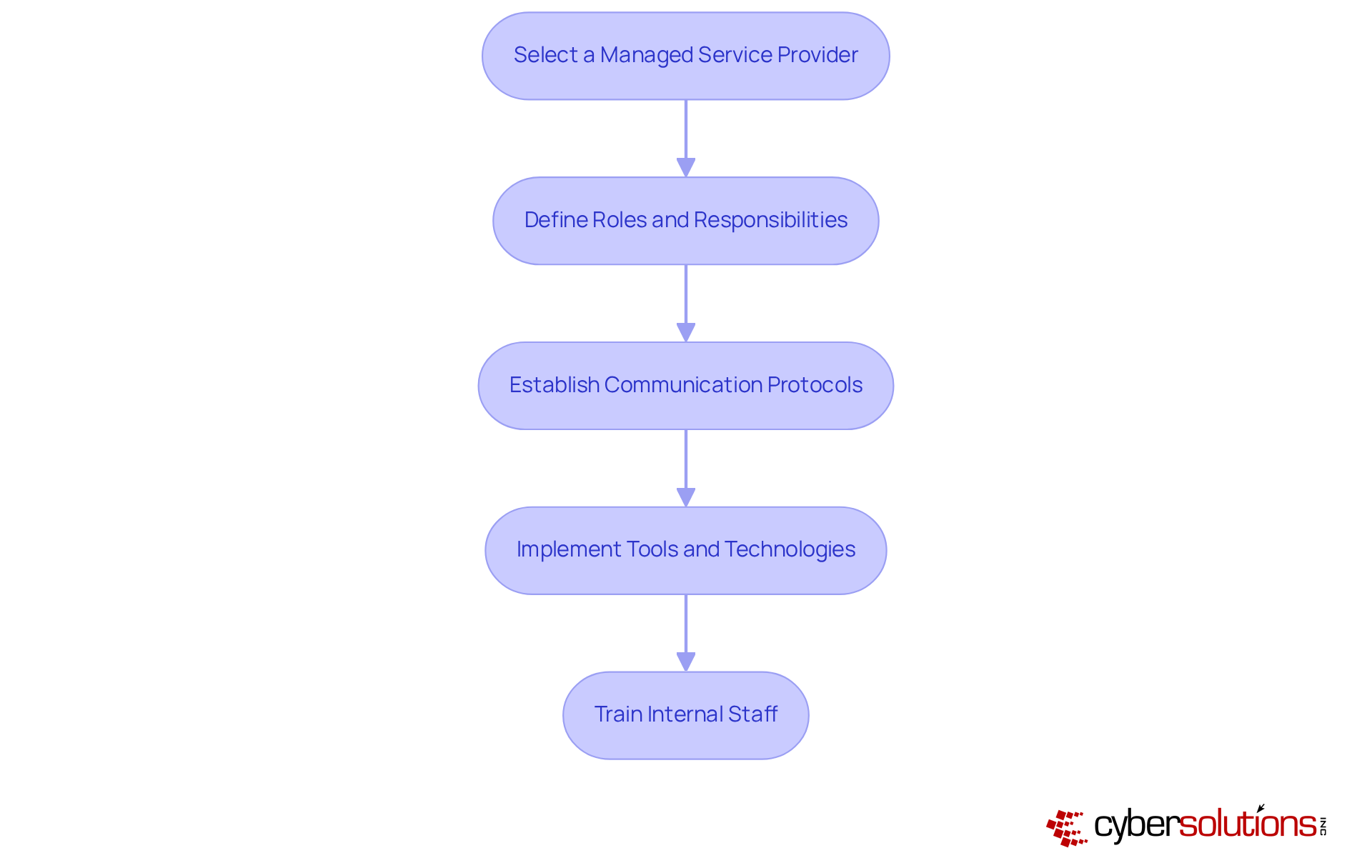
To configure co-management effectively, follow these steps:
- Select a managed service provider: Choosing the right MSP is crucial for operational success. Select an MSP that aligns with your entity's goals and possesses industry-specific experience. Research indicates that organizations using MSPs can increase productivity by 15-25% through improved efficiency and reduced downtime. At Cyber Solutions, our services offer a perfect blend of security, efficiency, and comprehensive support tailored for small to medium businesses.
- Define Roles and Responsibilities: Clearly outlining the duties of both your internal team and the MSP prevents overlaps and gaps in provision. This clarity is essential, as 44.9% of MSPs prioritize client satisfaction. As Robert Peterson, CEO of Infrascale, notes, it is vital to co-manage in order to align with clients' evolving needs. Compliance and risk assessments are integral to our service offerings, helping you stay audit-ready.
- Establish Communication Protocols: Setting up regular meetings and reporting structures fosters transparency and collaboration between teams. Effective communication is critical; organizations that adopt structured communication experience a significant decrease in disruptions to their operations. Our ongoing support at Cyber Solutions is designed to facilitate this communication, ensuring that your IT needs are met promptly.
- Implement tools and technologies by utilizing solutions that allow teams to co-manage functions, such as remote monitoring and management (RMM) software. The incorporation of advanced technologies enhances service delivery and operational efficiency, with tools to identify issues sooner and minimize downtime. Cyber Solutions provides support and proactive monitoring to ensure your business continuity and threat protection.
- Train Internal Staff: Providing training for your internal team on co-management practices is essential, focusing on shared objectives and teamwork. This investment in training is crucial; companies that prioritize employee development report higher retention rates. With Cyber Solutions, you can simplify your budget with flat-rate pricing that eliminates unexpected IT expenses, allowing you to focus on your core business operations.
Monitor and Evaluate Co-Management Success
To ensure the success of co-management, organizations must implement a robust monitoring and evaluation framework:
- Establish Key Performance Indicators (KPIs): Define KPIs that align with your objectives, such as customer satisfaction, system uptime, and cost efficiency. For instance, organizations that co-manage IT services have reported a reduction in operational costs by up to 50%, showcasing the effectiveness of collaborative efforts. This statistic aligns with findings from the industry report, emphasizing the importance of clear goals linked to measurable outcomes.
- Regular Performance Reviews: Conduct periodic reviews with the Managed Service Provider (MSP) to assess performance against established KPIs. This practice not only identifies areas for improvement but also fosters accountability and transparency in the partnership. As noted in the case study of a Croatian start-up, regular assessments help maintain alignment with strategic objectives.
- Solicit Feedback: Gather feedback from internal staff and the MSP to understand the effectiveness of collaboration and identify any challenges. Involving both parties in this dialogue can yield actionable insights that improve the shared management experience. The research highlights the value of employee involvement in refining processes.
- Adjust Strategies as Needed: Be prepared to adapt your collaborative management approach based on performance data. Ongoing enhancement is crucial; entities that adopt flexibility in their strategies frequently observe improved operational efficiency and responsiveness to evolving needs. This adaptability is essential, as demonstrated by successful implementations of co-management frameworks.
- Document Success Stories: Keep a record of achievements through collaborative management. These success stories serve as valuable resources for future initiatives and can help reinforce the benefits of co-management across the organization. For example, case studies illustrate the positive impact of effective co-management on operational outcomes.

Conclusion
Co-management in IT stands as a pivotal strategy that empowers organizations to enhance operational efficiency through collaboration with external managed service providers. This strategic alliance enables businesses to leverage specialized expertise while maintaining control over their internal IT operations. By effectively co-managing resources, organizations can adeptly navigate the complexities of modern digital threats, ultimately fostering a resilient and secure operational framework.
Key aspects of co-management have been thoroughly examined, highlighting the importance of:
- Defining clear objectives
- Assessing existing IT resources
- Selecting the right managed service provider
- Establishing effective communication protocols
Moreover, the necessity of monitoring and evaluating co-management success through key performance indicators and regular feedback has been underscored, illustrating how these practices can lead to significant cost reductions and improved cybersecurity measures.
The significance of co-management is profound; it not only streamlines IT operations but also cultivates a culture of shared accountability and continuous improvement. Organizations are urged to embrace this collaborative model, ensuring agility and responsiveness to the ever-evolving landscape of technology and cybersecurity. By proactively implementing co-management strategies, businesses can unlock their full potential and achieve greater operational efficiency in the digital age.
Frequently Asked Questions
What is co-management in IT?
Co-management is a strategic alliance where organizations and external IT providers share responsibilities in IT management, allowing businesses to utilize the specialized expertise of managed service providers (MSPs) while retaining control over their internal IT operations.
Why is co-management important?
Co-management is important because it enhances operational efficiency by combining the strengths of both organizations and MSPs. This collaboration improves incident response times, fosters shared accountability, and enables better resource allocation and risk management.
How does co-management improve cybersecurity?
Co-management improves cybersecurity by leveraging the advanced skills of MSPs, who provide comprehensive training programs and proactive monitoring services. This is crucial since 95 percent of security breaches result from human error.
What are the benefits of effective joint management partnerships?
Effective joint management partnerships can lead to a 30% reduction in costs while simultaneously strengthening cybersecurity measures, helping businesses navigate modern digital threats more effectively.
What key services does Cyber Solutions provide?
Cyber Solutions provides key services including 24/7 IT support, endpoint protection, and proactive monitoring, all tailored to maximize return on investment (ROI) through customized IT and cybersecurity services.
List of Sources
- Define Co-Management and Its Importance
- diligent.com (https://diligent.com/resources/blog/top-20-quotes-cyber-risk-virtual-summit)
- mark43.com (https://mark43.com/press/solutions-review-cybersecurity-awareness-month-quotes-from-industry-experts-in-2024)
- Configure Co-Management in Your Organization
- Key MSP Statistics and Trends to Know for 2025 (https://jumpcloud.com/blog/msp-statistics-trends)
- Managed Services Provider Statistics and Facts (2026) (https://scoop.market.us/managed-services-statistics)
- scribehow.com (https://scribehow.com/library/msp-statistics)
- MSP Statistics In The USA: 2025 / Infrascale (https://infrascale.com/msp-statistics-usa)
- Monitor and Evaluate Co-Management Success
- bridgera.com (https://bridgera.com/case_studies/iot-enablement-and-remote-monitoring-case-study)
- zabbix.com (https://zabbix.com/case_studies)
- denisonconsulting.com (https://denisonconsulting.com/case_studies/razum)