
In the rapidly evolving landscape of healthcare, the urgency of cybersecurity cannot be overstated. Small businesses grapple with significant challenges posed by cybersecurity threats and regulatory compliance, where the stakes are particularly high. Protecting sensitive patient information is paramount, making the choice of an IT support provider a critical decision for medical organizations.
With a myriad of options available, how can these businesses discern which IT support companies genuinely meet their unique needs and can safeguard their operations effectively?
This article delves into the key criteria for selecting an IT support provider and compares the top contenders in Calgary, equipping healthcare entities with the insights necessary to make informed choices in a complex environment.
In today's digital landscape, the importance of IT support cannot be overstated. Small enterprises, particularly in the medical sector, face unique challenges that necessitate the services of IT professionals to protect sensitive patient information and comply with stringent regulations. IT support not only addresses immediate technical issues but also plays a pivotal role in strategic planning, risk management, and operational efficiency.
A vital aspect of this support is cybersecurity, which proactively prevents malware and unauthorized software from executing. This approach significantly reduces the attack surface and minimizes vulnerabilities, making it essential for healthcare providers. The stakes are exceptionally high; data breaches can result in substantial financial penalties—averaging over $3 million per incident—and can severely erode patient trust. Consider the WannaCry ransomware incident in 2017, which disrupted numerous medical services globally, underscoring the dire consequences of inadequate cybersecurity measures.
Investing in reliable IT assistance from a qualified provider transcends mere technical necessity; it is a strategic investment that can profoundly influence a business's growth and sustainability. By ensuring compliance with regulations such as HIPAA and enhancing data security through measures like encryption—featuring centralized management and continuous monitoring—IT support empowers healthcare entities to concentrate on delivering quality patient care while mitigating risks associated with cyber threats.

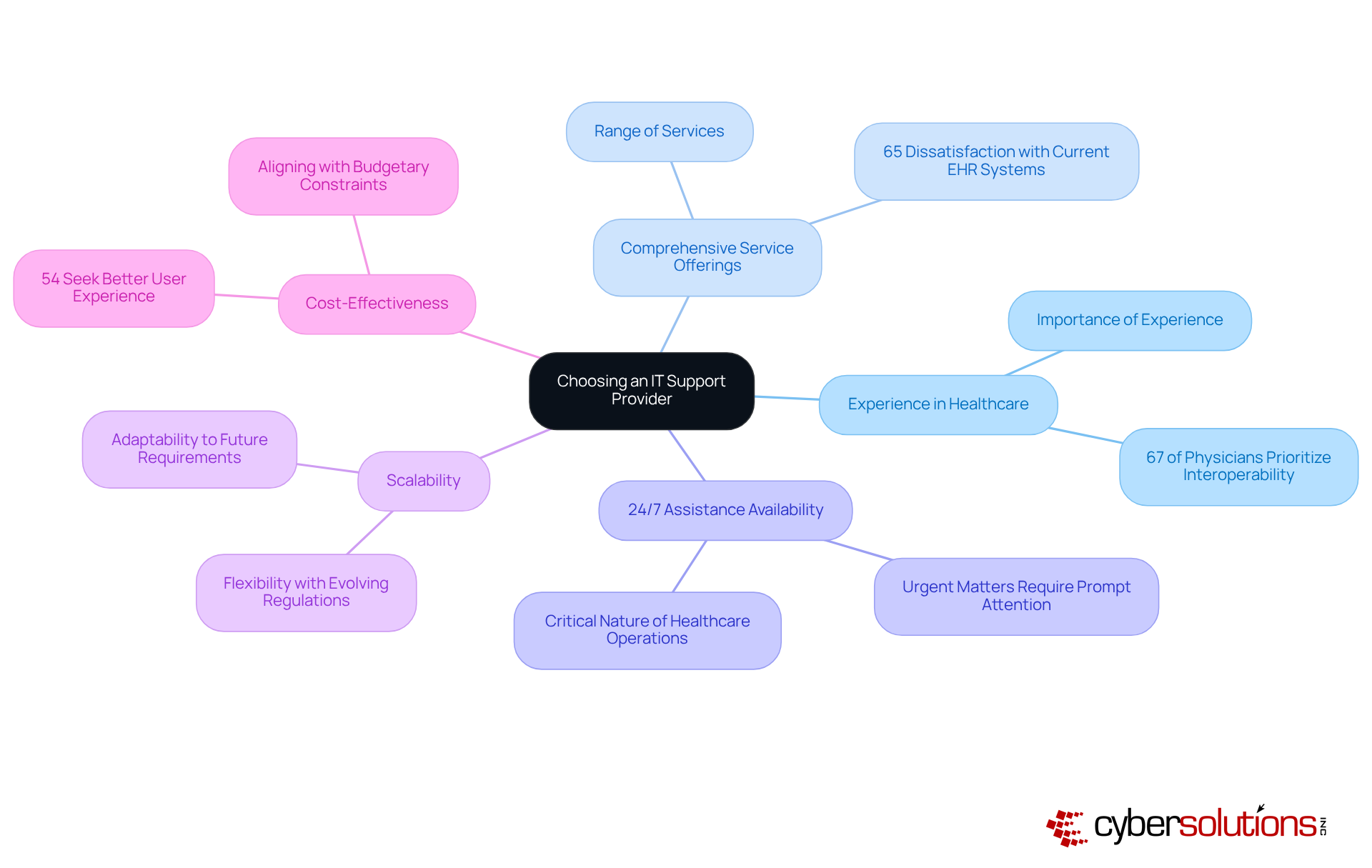
When selecting an IT support provider, healthcare organizations must prioritize several critical criteria:
By concentrating on these essential elements, medical institutions can make educated choices when evaluating IT support companies for small business needs, ultimately enhancing their operational efficiency and security stance.
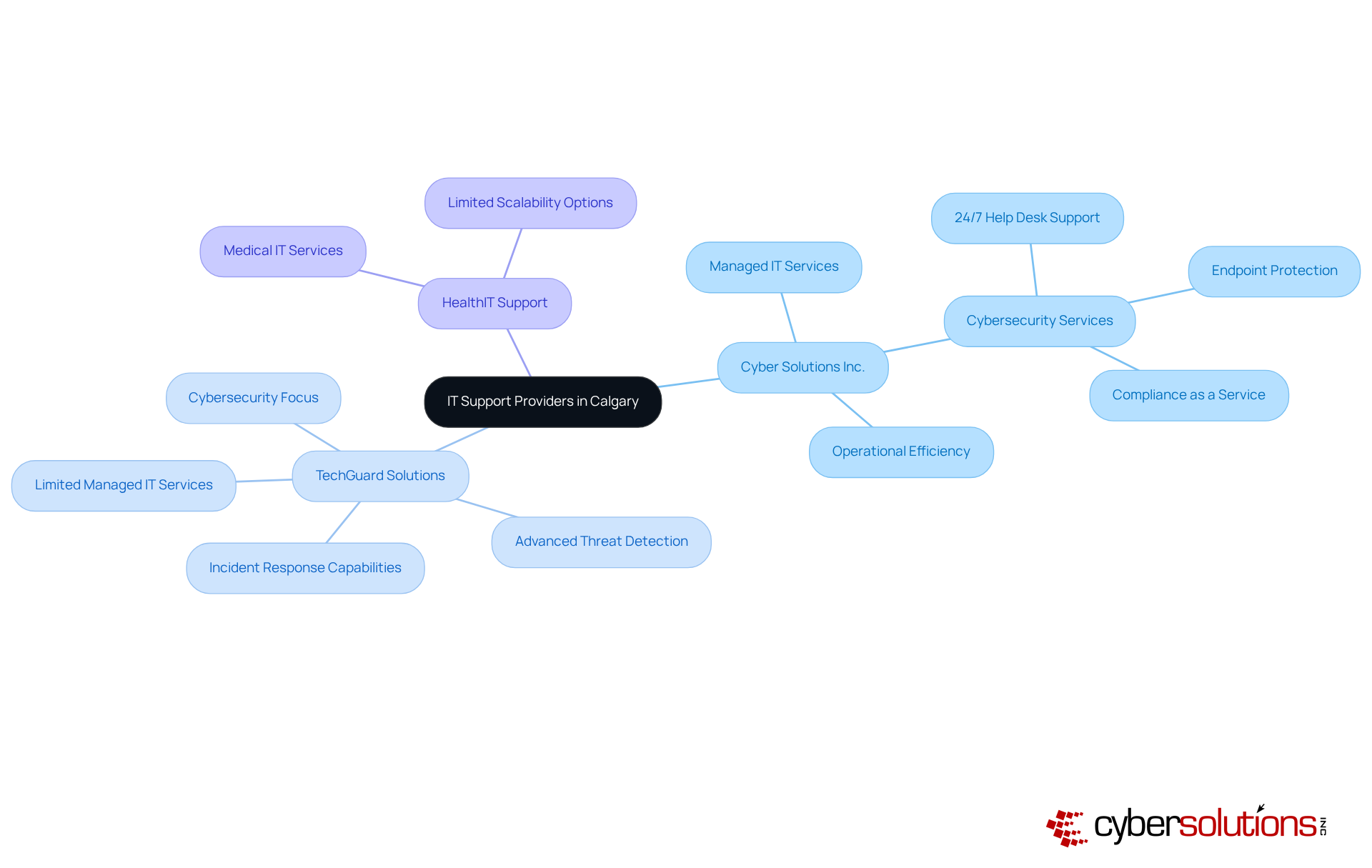
In today's digital landscape, the importance of IT support cannot be overstated. Calgary hosts several companies in the medical field, each offering distinct advantages.
Among these options, MedTech Solutions stands out due to its holistic approach. By combining proactive monitoring with tailored services, they effectively address both operational and compliance needs. This positions them as the ideal partner for businesses that are looking for seeking reliable assistance. In a sector where technology is critical, having a dependable partner like MedTech Solutions is not just beneficial—it's essential.
In today's digital landscape, IT support is not just important—it's essential. With the increasing frequency of cyber threats, a complex web of regulations and threats exists. Evaluating potential IT providers is crucial for ensuring compliance.
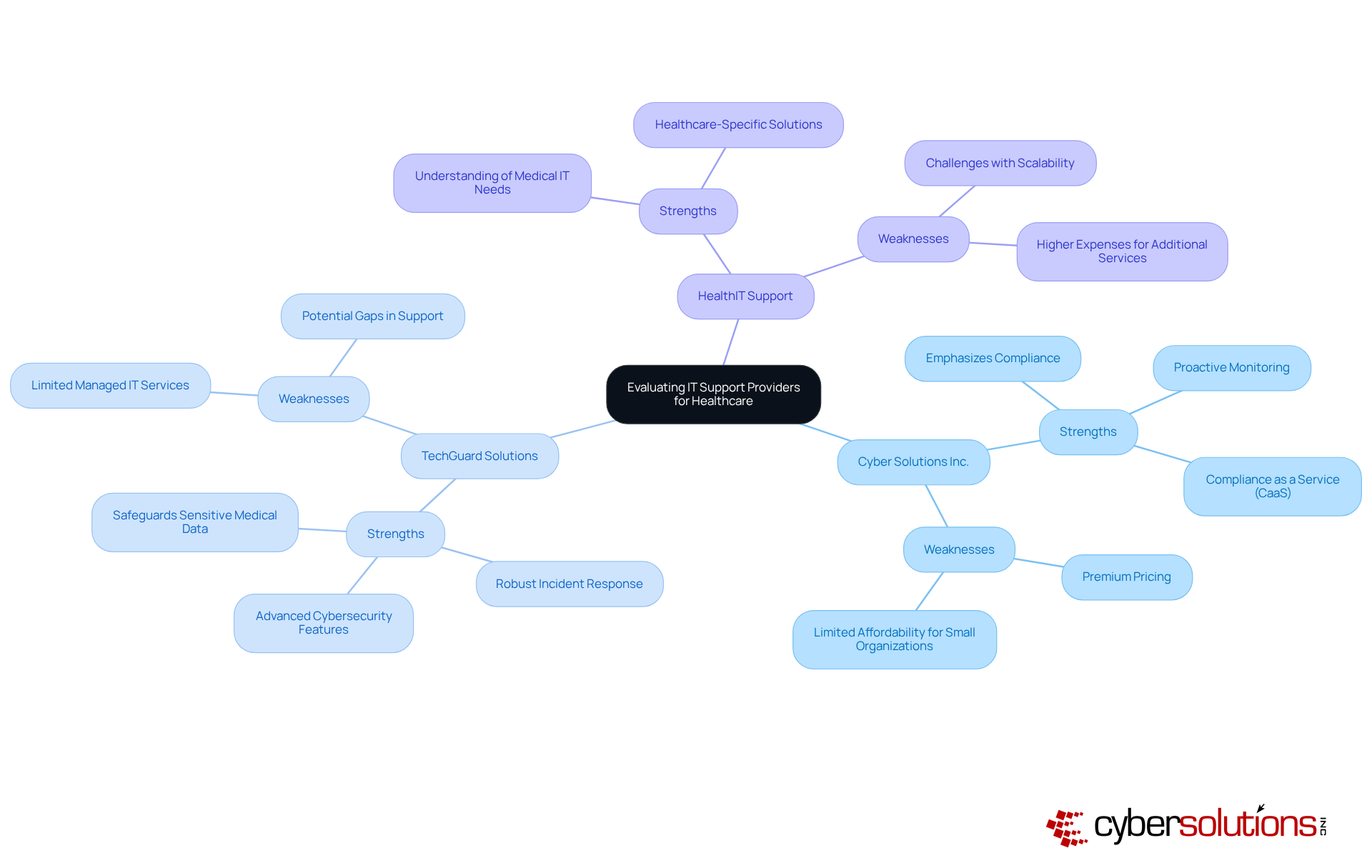
Cyber Solutions Inc. stands out with its comprehensive suite of services tailored specifically for the healthcare sector.
TechGuard Solutions is recognized for its advanced cybersecurity features and robust incident response capabilities.
HealthIT Support demonstrates a profound understanding of medical IT needs, making them a strong candidate for institutions seeking specialized expertise.
By carefully evaluating these strengths and weaknesses, healthcare organizations can better align their needs with IT support providers, ensuring they receive the necessary support to maintain compliance and enhance operational efficiency.
Selecting the right IT support company is critical for small businesses in the healthcare sector, where the implications of inadequate support can be dire. In today's landscape, cybersecurity threats are ever-evolving, making a strategic partnership with IT support providers essential. Not only does this enhance operational efficiency, but it also safeguards sensitive patient data against cyber threats. This proactive approach is vital for compliance with stringent regulations, ultimately allowing healthcare professionals to focus on delivering quality care.
Key criteria for choosing an IT support provider include:
A comparative analysis of top IT support companies in Calgary highlights the strengths and weaknesses of each provider. Cyber Solutions Inc. stands out for its holistic approach to managed IT and cybersecurity services. In contrast, other providers like TechGuard Solutions and HealthIT Support offer specialized services but may lack the comprehensive support required by many medical institutions.
Healthcare organizations are urged to carefully evaluate their options, considering the unique challenges they face. By prioritizing experienced and comprehensive IT support, small businesses can not only protect their operations but also enhance their overall service quality. This ensures they remain resilient in the face of future challenges, ultimately delivering the quality care that patients deserve.
Why is IT support important for small businesses, especially in the healthcare sector?
IT support is crucial for small businesses in healthcare to protect sensitive patient information, comply with regulations, and enhance operational efficiency. It addresses immediate technical issues and plays a key role in strategic planning and risk management.
What is application allowlisting and why is it significant?
Application allowlisting is a security measure that prevents malware and unauthorized software from executing. It significantly reduces the attack surface and minimizes vulnerabilities, making it essential for healthcare providers to protect against cyber threats.
What are the potential consequences of inadequate cybersecurity in healthcare?
Inadequate cybersecurity can lead to data breaches, resulting in substantial financial penalties averaging over $3 million per incident, and can severely erode patient trust. Historical incidents, like the WannaCry ransomware attack in 2017, highlight the serious repercussions of insufficient cybersecurity measures.
How does IT support contribute to compliance with regulations like HIPAA?
Effective IT support helps healthcare entities ensure compliance with regulations such as HIPAA by implementing necessary security measures, like application allowlisting, which features centralized management and continuous monitoring of data security.
What are the strategic benefits of investing in IT support for small medical businesses?
Investing in reliable IT support is a strategic imperative that can significantly influence a small medical business's success and sustainability by enhancing data security, ensuring regulatory compliance, and allowing healthcare providers to focus on delivering quality patient care while mitigating cyber risks.