
In an era where digital threats evolve at an alarming pace, comprehending the intricacies of password spray attacks is imperative for organizations committed to safeguarding sensitive information. These sophisticated assaults exploit prevalent password vulnerabilities, often bypassing traditional security measures with unsettling ease.
As the cybersecurity landscape becomes increasingly intricate, how can businesses effectively shield themselves from these subtle yet damaging intrusions? This article explores essential best practices that not only clarify the mechanics of password spray attacks but also equip organizations with the strategies necessary to strengthen their defenses.
Credential spray attacks represent a sophisticated form of brute-force assault, where perpetrators seek illicit access to multiple accounts by leveraging a limited selection of commonly used credentials. This method diverges markedly from traditional brute-force techniques, which focus on a single account with numerous credential attempts. By distributing attempts across various accounts, credential spraying diminishes the likelihood of triggering account lockout systems, rendering it a particularly insidious threat in the current landscape.
As we progress into 2025, the prevalence of credential spray attacks has surged, with significant incidents reported across diverse sectors. For instance, the UNK_SneakyStrike campaign has targeted over 80,000 accounts, utilizing advanced tools like TeamFiltration to conduct extensive user enumeration and credential spraying efforts. This campaign exemplifies the threat landscape, as attackers can operate undetected for prolonged periods, often executing unauthorized access attempts in concentrated bursts followed by periods of inactivity.
Cybersecurity professionals underscore the critical need for organizations to recognize the implications of spray attacks. Industry leaders have observed that many organizations harbor a false sense of security, believing they are insulated from overt threats while remaining susceptible to these subtle tactics. The ramifications can be severe, resulting in unauthorized access to sensitive data and substantial remediation costs. Alarmingly, only 4% of defense contractors are fully equipped to meet minimum cybersecurity standards, highlighting systemic vulnerabilities that credential spraying exploits.
Key characteristics of credential spray attacks include:
As organizations navigate the complexities of modern cybersecurity, understanding the dynamics of credential spray incidents is essential. Implementing robust safeguards, such as employee training and stringent access protocols, can significantly mitigate the risks associated with these intrusions, thereby protecting sensitive information and ensuring organizational integrity.

In today's digital landscape, security is paramount, particularly within the cybersecurity realm. Password spray attacks stand out as a distinct threat, differing from brute-force and traditional attacks due to their unique approach and implementation. While brute-force attacks leverage stolen username and credential pairs to infiltrate accounts, password spray attacks employ a more sophisticated method. This method focuses on numerous accounts using a limited selection of commonly used passphrases—think 'password123' or 'qwerty.' Such a targeted approach not only reduces detectability but also complicates defensive measures for organizations.
As we look ahead to 2025, the effectiveness of password spray attacks is underscored by its ability to exploit weak credential practices, achieving a success rate of approximately 1%. This lower success rate is a direct consequence of its focused nature, particularly against high-value accounts in critical industries like healthcare, finance, and government. Understanding these distinctions is vital for organizations aiming to craft tailored defenses. Implementing detection strategies can significantly bolster security. By distributing resources efficiently, organizations can ensure robust protection against these evolving cyber threats.
In conclusion, grasping the nuances of password spray attacks versus other attack methods is essential for cybersecurity preparedness. Are your defenses prepared to counter such sophisticated threats?

To effectively detect password spray attacks, organizations must implement comprehensive detection strategies. This involves meticulously tracking login attempts across multiple accounts and systems to prevent unauthorized access.
Leveraging analytics is crucial for identifying spikes in failed login attempts or unusual login locations, especially for detecting potential breaches. Establishing instant alerts and monitoring systems empowers IT teams to respond swiftly to potential threats like password spray attacks.
Continuous monitoring ensures that suspicious activities, including repeated failed logins, are detected and stopped before they escalate into significant threats, significantly bolstering detection capabilities. Regular log reviews, combined with machine learning algorithms to detect anomalies, enable organizations to identify potential attacks, including those executing password spray techniques.
Companies that have successfully implemented these strategies report improved security posture and reduced incident response times, which underscores the effectiveness of a proactive approach to cybersecurity in defending against password spray attacks. Moreover, offering prompt training for personnel on identifying dubious emails and upholding appropriate security protocols is crucial in strengthening defenses against such threats.

To effectively mitigate the threat of password spray attacks, organizations must implement a range of precautionary measures. Policies that mandate complex and unique passwords are essential; research shows that 88% of passwords used in successful attacks are 12 characters or fewer.
Furthermore, implementing multi-factor authentication significantly enhances protection, making it exceedingly difficult for attackers to conduct password spray attacks and gain unauthorized access, as over 99.9% of compromised accounts lack MFA. This statistic reflects the growing trend of organizations adopting robust protective measures.
Regularly renewing and conducting security assessments can help identify and address vulnerabilities. Additionally, fostering a culture of security through staff training on the importance of strong passwords and the risks associated with weak passwords is crucial.
It is vital to acknowledge that password hygiene is essential, underscoring the need for institutions to enforce stricter policies. Organizations must also recognize common pitfalls, such as employees writing down passwords, which can severely compromise security.
This holistic approach not only strengthens defenses but also aligns with the proactive nature of cybersecurity, as encapsulated by the principle that 'protection begins with design, not detection.'

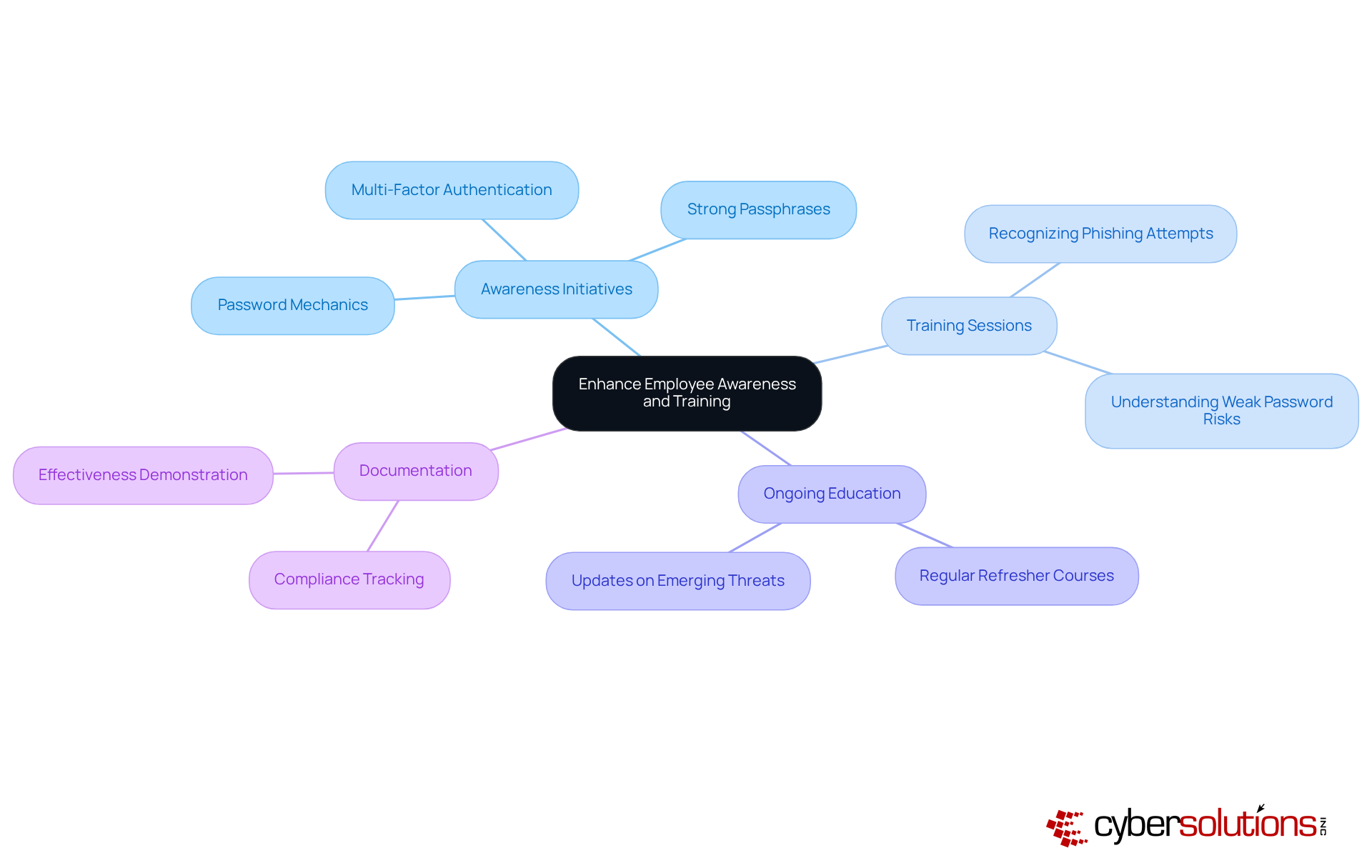
Increasing employee awareness through regular training is essential for preventing password spray attacks. Organizations must establish comprehensive awareness initiatives that educate employees on the mechanics of password security, the significance of strong passwords, and the necessity of multi-factor authentication (MFA).
Training sessions should include practical exercises, such as:
As evidenced by recent studies, timely training on identifying and maintaining proper password hygiene can significantly bolster an organization's overall protection stance. Furthermore, cultivating an environment where employees feel empowered to report unusual activities can enhance safety.
Regular refresher courses and workshops are vital to keeping employees vigilant and informed. Organizations with strong training programs have demonstrated a reduction in security-related risks, highlighting the critical role of ongoing education in sustaining robust cybersecurity defenses. Additionally, documenting training sessions is crucial for compliance and showcasing the effectiveness of these initiatives.
In today's cybersecurity landscape, understanding and effectively combating password spray attacks is paramount. These attacks exploit common password vulnerabilities and utilize sophisticated tactics that can evade traditional security measures. Organizations must recognize the unique characteristics of password spraying, distinguishing it from other attack methods such as credential stuffing and brute-force attacks, to develop tailored defenses that specifically address this threat.
Key strategies include:
Additionally, fostering a culture of cybersecurity awareness through regular employee training is crucial for mitigating risks associated with password spray attacks. By equipping personnel with the knowledge to recognize and respond to potential threats, organizations can significantly strengthen their defenses.
Ultimately, proactive measures and a commitment to continuous improvement in cybersecurity practices are vital for safeguarding sensitive information. As cyber threats evolve, organizations must remain vigilant and adaptive, ensuring that their security frameworks are not only reactive but also designed to prevent attacks before they occur. Embracing these best practices will not only protect against password spray attacks but also enhance overall cybersecurity resilience.
What are credential spray attacks?
Credential spray attacks are a sophisticated form of brute-force assault where attackers seek access to multiple accounts by using a limited selection of commonly used credentials, rather than targeting a single account with numerous attempts.
How do credential spray attacks differ from traditional brute-force attacks?
Unlike traditional brute-force attacks that focus on one account with many attempts, credential spray attacks distribute attempts across various accounts, reducing the likelihood of triggering account lockout systems.
Why have credential spray attacks become more prevalent?
The prevalence of credential spray attacks has surged, particularly as organizations remain unaware of their vulnerabilities and may harbor a false sense of security, making them susceptible to these subtle tactics.
Can you provide an example of a recent credential spray attack?
The UNK_SneakyStrike campaign targeted over 80,000 Microsoft Entra ID accounts, utilizing advanced tools for extensive user enumeration and credential spraying, exemplifying the covert nature of such attacks.
What are the key characteristics of password spray attacks?
Key characteristics include exploitation of common password choices, low-volume efforts across various accounts, and the ability to bypass standard security measures, often evading detection by conventional protection systems.
What are the potential consequences of credential spray attacks for organizations?
The ramifications can include unauthorized access to sensitive information and substantial remediation costs, highlighting the need for organizations to recognize and address these threats.
How can organizations protect against credential spray attacks?
Implementing robust safeguards such as multi-factor authentication and stringent access protocols can significantly mitigate the risks associated with these intrusions.
How do password spray attacks compare to credential stuffing?
Password spray attacks focus on numerous accounts using a limited selection of commonly used passwords, while credential stuffing leverages stolen username and credential pairs to infiltrate specific accounts.
What is the success rate of credential spraying attacks?
The success rate of credential spraying is approximately 1%, which is a result of its focused nature, particularly against high-value accounts in critical industries like healthcare and finance.
Why is it important for organizations to understand password spray attacks?
Understanding the dynamics of password spray attacks is essential for developing effective cybersecurity strategies and ensuring robust protection against evolving cyber threats.