
In an era where cyber threats loom larger than ever, businesses are confronted with the formidable task of safeguarding their sensitive data and ensuring operational integrity. SIEM cybersecurity stands out as an essential ally, providing a robust framework for real-time threat detection and incident response. As organizations grapple with the complexities of digital security, one pivotal question arises: how can the strategic implementation of SIEM not only bolster defenses but also enhance overall business resilience amidst the ever-evolving landscape of cyber challenges?
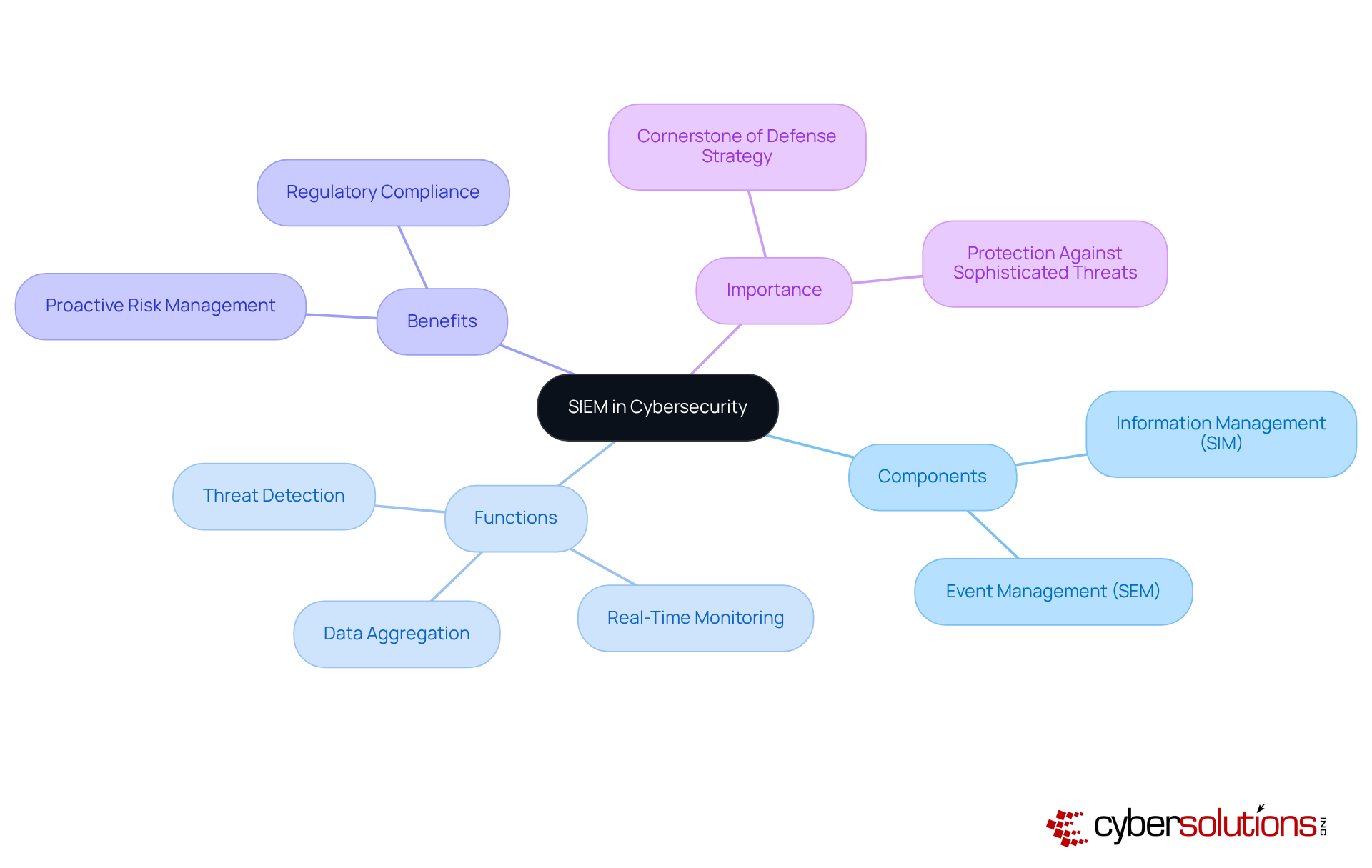
In today's digital landscape, the significance of robust cybersecurity cannot be overstated, particularly for organizations facing an array of threats. SIEM stands out as a comprehensive solution that compiles and analyzes data related to potential threats from various sources within an organization. By integrating information management (SIM) and event management (SEM), SIEM provides a unified perspective on an organization's security posture.
This system aggregates log data from servers, network devices, and applications, enabling teams to identify, investigate, and respond to incidents in real-time. Continuous monitoring ensures that suspicious activities are detected and addressed before escalating into significant risks, thereby protecting organizations from ransomware, phishing, and other malware attacks. Furthermore, the incorporation of advanced analytics enhances SIEM's capabilities, allowing for the detection of patterns and anomalies indicative of security incidents.
As cyber threats become increasingly sophisticated, SIEM serves as the cornerstone of an organization's defense strategy. It empowers teams to make informed decisions while ensuring data integrity. In this evolving cybersecurity landscape, adopting SIEM solutions is not merely a choice but a necessity for organizations aiming to safeguard their operations and data.
In today's rapidly evolving digital landscape, the deployment of SIEM solutions is crucial for enhancing business security. SIEM cybersecurity provides organizations with tools, empowering organizations to swiftly identify and respond to security incidents. This capability was exemplified by Cyber Solutions during a recent incident, where 4,500 endpoints were restored, minimizing potential harm and significantly reducing downtime—an essential factor for maintaining operational continuity. A structured action plan is vital in this process, ensuring that all measures are coordinated and effective.
Moreover, SIEM cybersecurity systems play a pivotal role in incident management by automating the gathering and reporting of safety-related data. This automation helps organizations meet regulatory obligations, including HIPAA, PCI-DSS, and GDPR. Additionally, the integration of application allowlisting further fortifies compliance by proactively preventing unauthorized software from executing, thereby mitigating vulnerabilities.
The centralized logging and analysis capabilities of SIEM cybersecurity systems enhance incident response, allowing teams to examine and resolve threats more efficiently. By leveraging threat intelligence and advanced analytics, SIEM cybersecurity systems significantly enhance an organization's overall defensive posture, making it more resilient against the ever-evolving landscape of cyber threats. In conclusion, the strategic implementation of SIEM cybersecurity not only protects sensitive data but also cultivates a robust and agile business framework, essential for navigating today's challenges.
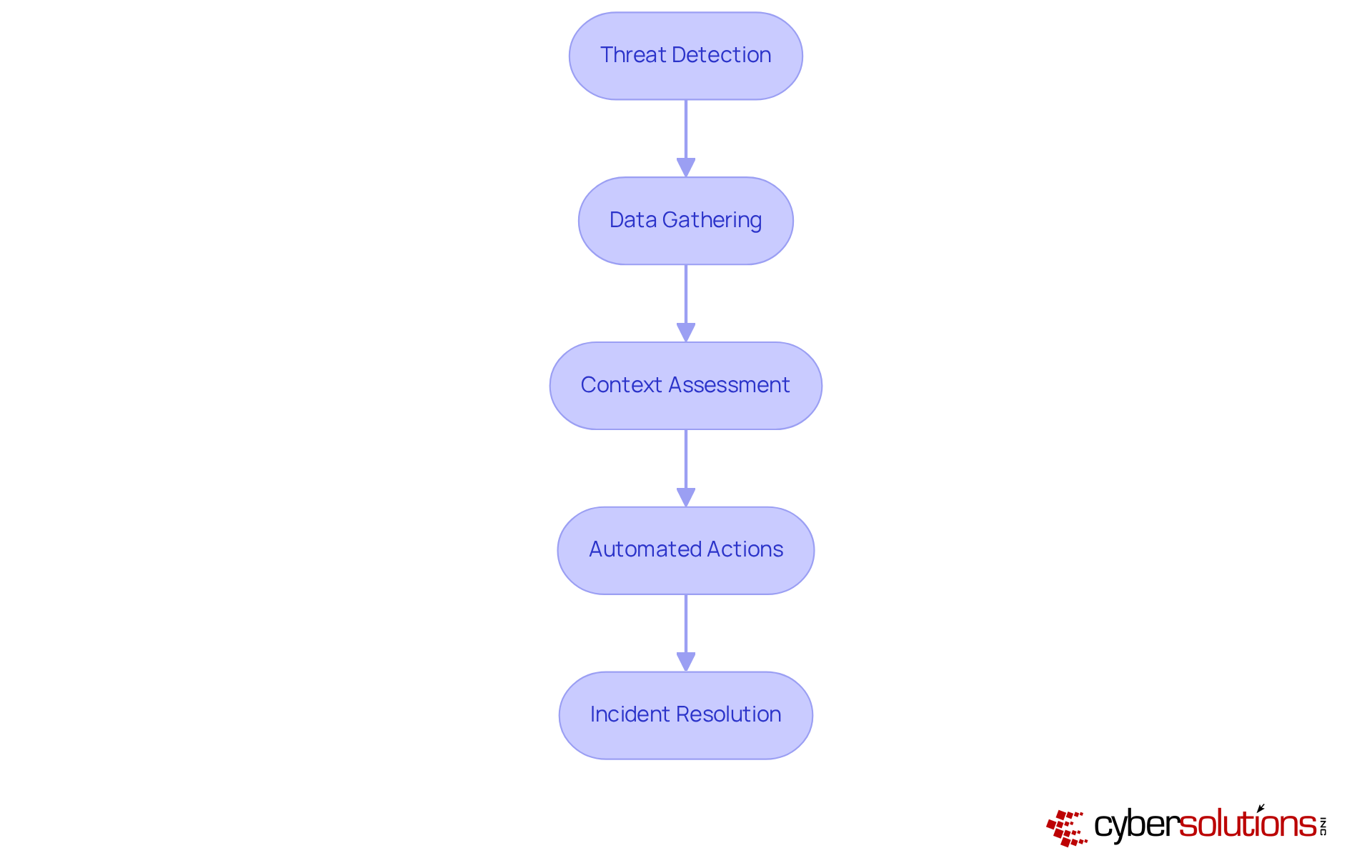
is indispensable in cybersecurity, providing security teams with essential tools to identify and assess security incidents in real-time. When a threat is detected, SIEM systems gather relevant data from diverse sources, enabling analysts to understand the context and magnitude of the incident. This centralized approach facilitates faster decision-making and more coordinated actions.
Moreover, SIEM often features automated actions that can initiate predefined measures to mitigate risks before they escalate. By streamlining the incident response process, SIEM not only reduces the time to resolve incidents but also minimizes the potential impact on business operations.
The integration of threat intelligence further amplifies this capability, equipping organizations to stay ahead of emerging threats and adapt their response strategies effectively.
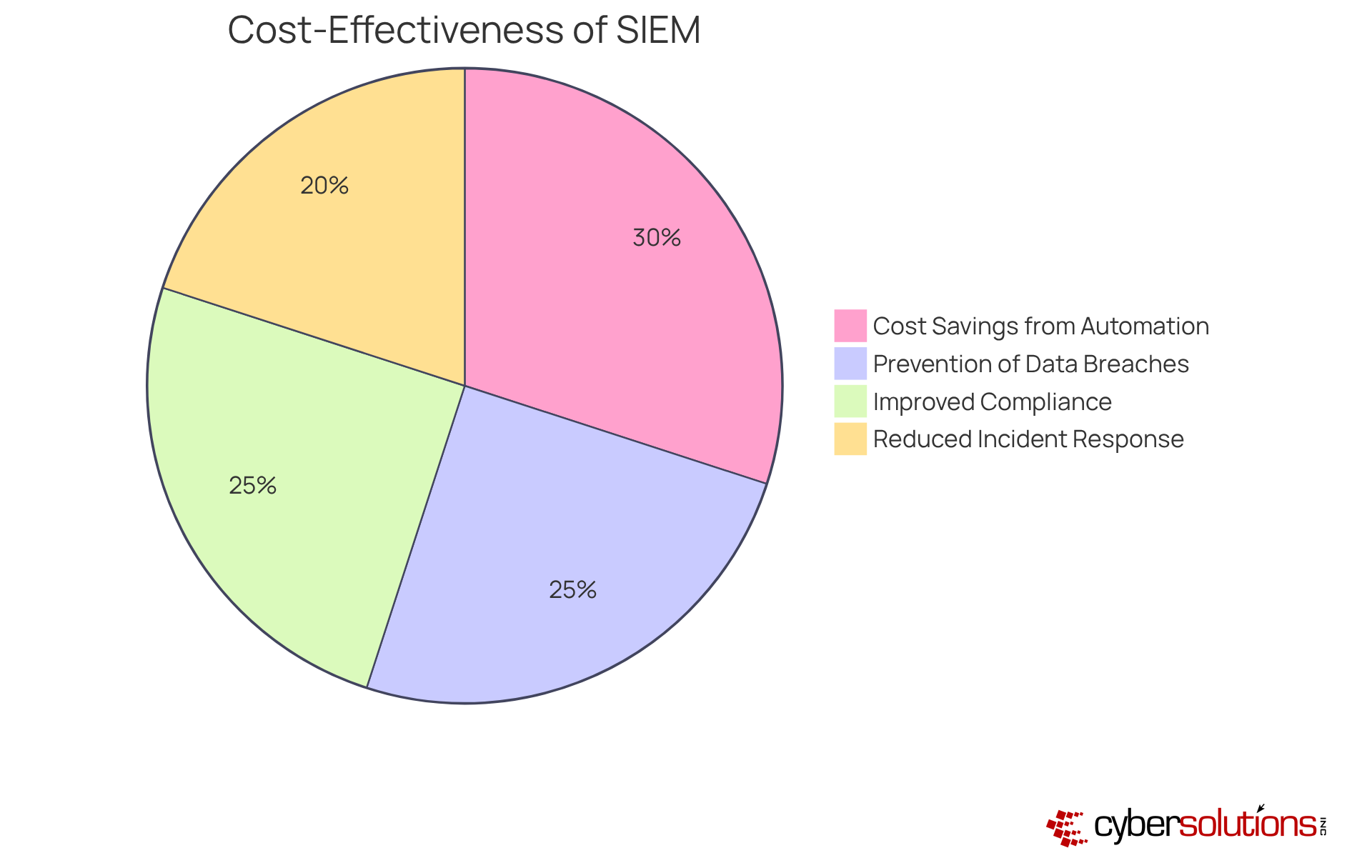
Investing in security information and event management solutions is not just a luxury; it is essential for organizations striving to enhance security while optimizing budgetary allocations.
With SIEM solutions, businesses can effectively eliminate unforeseen IT expenses and establish a robust security posture, paving the way for improved financial planning.
By automating a multitude of protective processes, this system significantly reduces the need for extensive manual oversight and examination, which can be resource-intensive. Such automation not only lowers operational costs but also empowers security teams to concentrate on more strategic initiatives rather than mundane tasks.
Moreover, the cost-effectiveness of SIEM cybersecurity systems, along with continuous network surveillance and instant notifications, can prevent costly data breaches and incidents that may result in severe financial repercussions and damage to reputation.
By showcasing a clear return on investment (ROI) through decreased incident response times and enhanced compliance management, SIEM solutions emerge as a critical element of a fiscally responsible cybersecurity strategy.
The importance of SIEM cybersecurity for business resilience cannot be overstated. As organizations navigate an increasingly complex digital landscape, integrating SIEM solutions emerges as a critical strategy for safeguarding operations and data. This comprehensive approach not only enhances threat detection and incident response but also fortifies compliance management, ensuring that organizations can effectively mitigate risks while adhering to regulatory standards.
Key insights from the discussion reveal that SIEM systems provide real-time monitoring, enabling the swift identification and resolution of security incidents. The automation of data gathering and reporting simplifies compliance efforts, while the centralized logging capabilities streamline incident management. Furthermore, the cost-effectiveness of SIEM solutions allows organizations to optimize their cybersecurity investments, reducing operational costs and preventing costly data breaches.
Ultimately, embracing SIEM cybersecurity solutions is essential for any organization aiming to thrive in today's threat-laden environment. By prioritizing the implementation of SIEM, businesses not only protect their sensitive information but also build a resilient framework capable of adapting to ongoing challenges. The strategic deployment of SIEM is not just a defensive measure; it is a proactive investment in the future stability and success of the organization.
What does SIEM stand for in cybersecurity?
SIEM stands for Security Information and Event Management.
How does SIEM contribute to cybersecurity?
SIEM compiles and analyzes data related to potential threats from various sources within an organization, providing a comprehensive solution for identifying, investigating, and mitigating threats in real-time.
What components make up SIEM?
SIEM integrates information management (SIM) and event management (SEM) to provide a unified perspective on an organization's security posture.
What types of data does SIEM aggregate?
SIEM aggregates log data from servers, network devices, and applications.
How does SIEM enhance threat detection?
SIEM employs continuous monitoring to detect suspicious activities, and advanced analytics and machine learning to identify patterns and anomalies indicative of security incidents.
Why is SIEM considered essential for organizations?
SIEM is essential because it helps organizations proactively manage risks, ensures compliance with industry regulations, and protects against sophisticated cyber threats such as ransomware and phishing attacks.
What is the primary benefit of using SIEM in cybersecurity?
The primary benefit of using SIEM is its ability to provide a comprehensive and real-time view of an organization’s security posture, allowing for quick response to potential threats.