
In a world where businesses are increasingly reliant on technology, the demand for custom business software development is surging. Tailored solutions not only enhance operational efficiency but also address unique organizational challenges, providing significant advantages over off-the-shelf alternatives. However, the question remains: how can executives leverage these bespoke systems to streamline processes and secure a competitive edge in their industries? Exploring the multifaceted benefits of custom software development reveals a pathway to operational excellence and sustained growth.
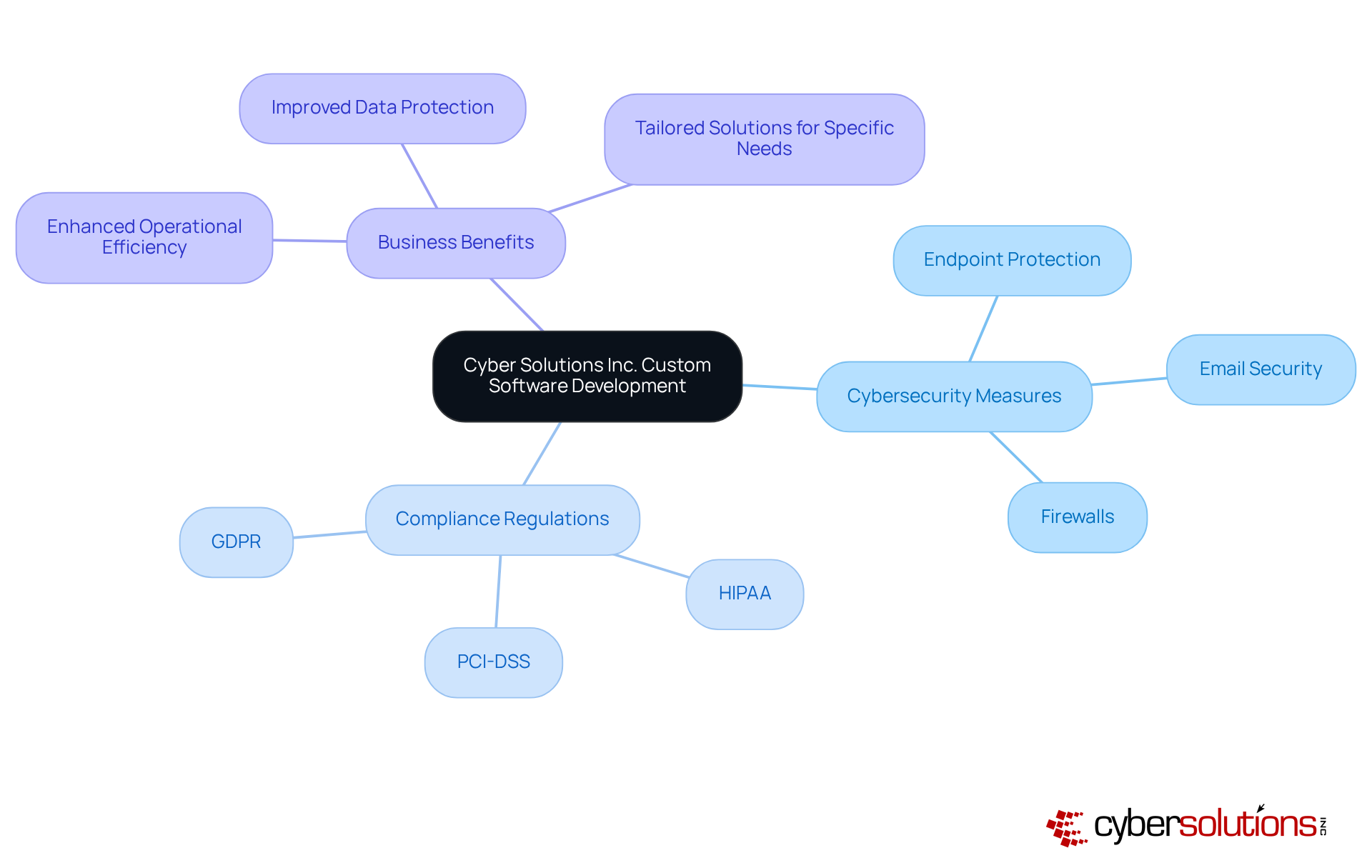
In today's digital landscape, the significance of custom software development cannot be overstated, particularly in sectors such as healthcare, finance, and legal. Cyber Solutions Inc. specializes in solutions that are personalized to enhance business efficiency while also integrating security measures, including:
By thoroughly understanding the unique needs of various industries, the company specializes in custom business software development to craft tailored solutions that improve operational workflows.
Our services, such as application allowlisting, proactively mitigate the risks of cyber threats, ensuring that all programs remain secure and compliant with critical industry regulations like:
This proactive stance not only minimizes vulnerabilities but also empowers organizations to meet stringent compliance requirements. Consequently, businesses can focus on their core functions without the burden of IT complexities.
With a steadfast commitment to innovation, Cyber Solutions empowers organizations to leverage technology effectively. By partnering with us, companies can navigate the complexities of cybersecurity with confidence, ensuring their operations are not only secure but also optimized for success.
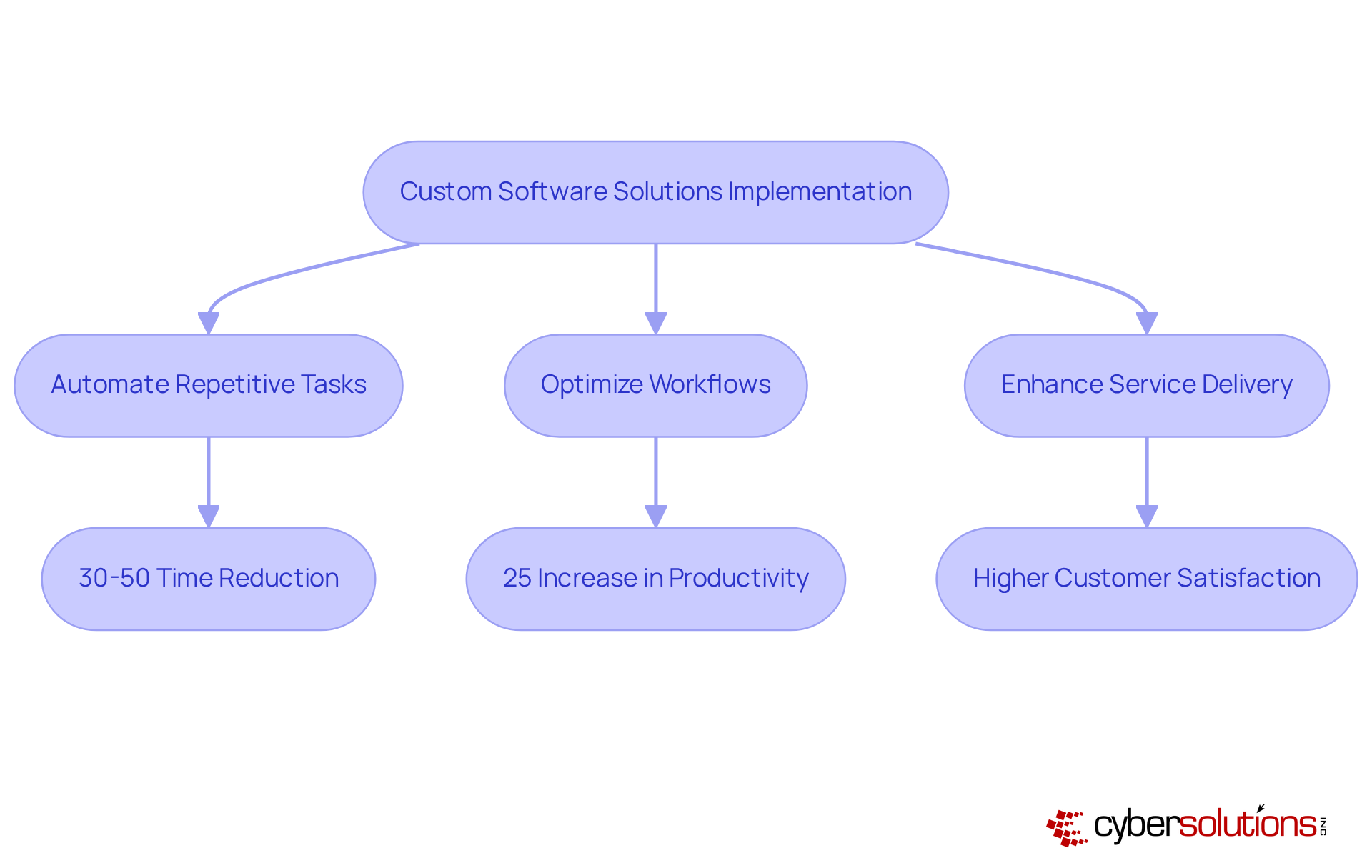
Custom software development is pivotal in streamlining operations by automating repetitive tasks and optimizing workflows. This automation not only leads to increased efficiency but also empowers employees to concentrate on higher-value activities. For instance, a custom software solution can automate stock tracking, significantly decreasing the time devoted to manual entries and reducing mistakes.
Companies that have implemented such systems report a 30% to 50% reduction in time spent on repetitive tasks, which translates into faster turnaround times and enhanced service delivery. This ultimately fosters customer satisfaction and loyalty, positioning organizations for sustained growth in competitive markets. Additionally, a McKinsey study shows that organizations investing in custom software experience a significant return on investment, highlighting the strategic importance of tailored applications in driving business success.
Moreover, a case study on an automation solution for a SaaS company demonstrates how tailored applications can greatly minimize billing mistakes and enhance customer satisfaction, further emphasizing the significance of automation in attaining operational excellence.
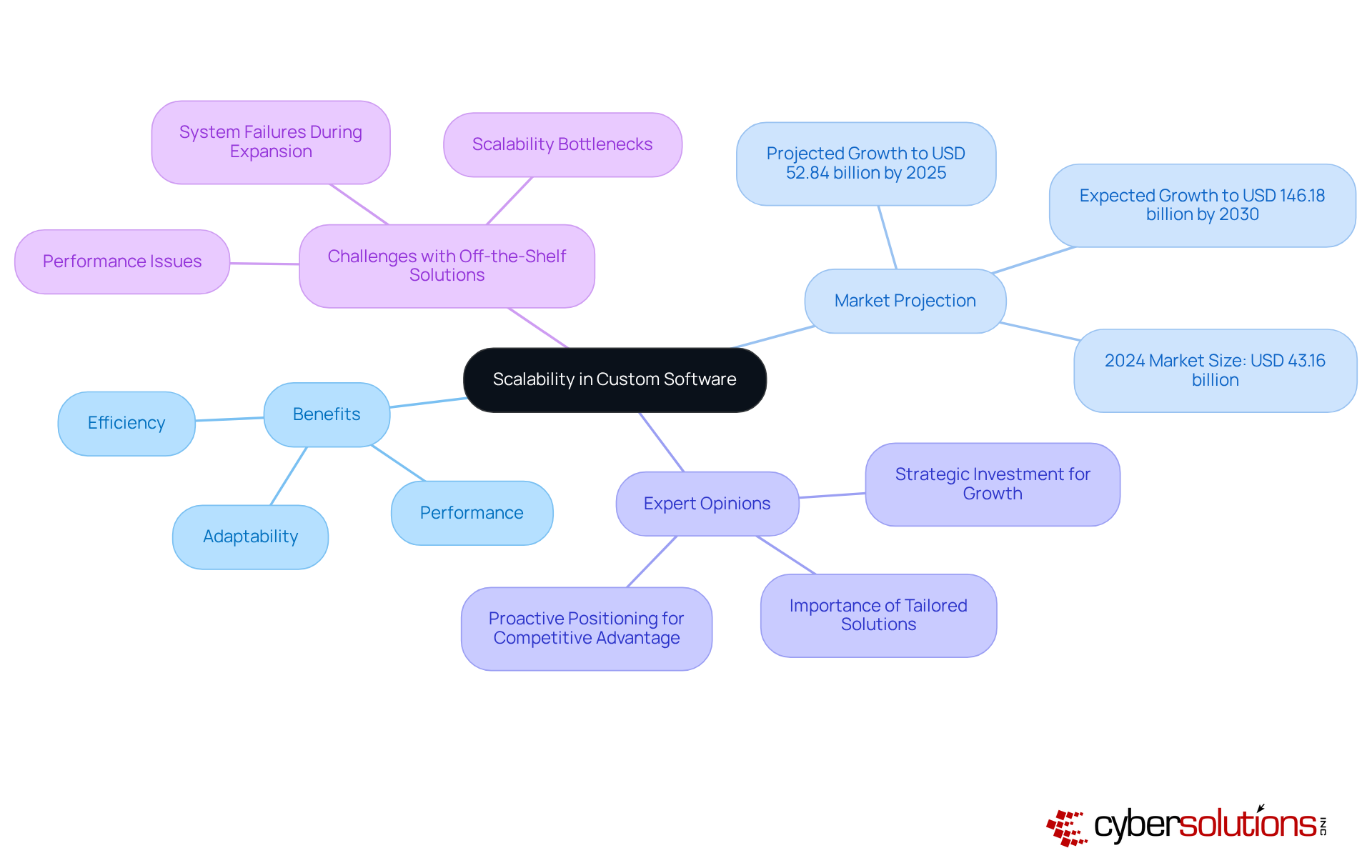
of custom software. Unlike off-the-shelf solutions that often necessitate expensive upgrades or replacements as an organization evolves, custom software is inherently designed to grow alongside your entity. This adaptability facilitates seamless modifications and enhancements, accommodating increased workloads and new functionalities. For instance, a custom application can be modified to manage a burgeoning customer base without sacrificing performance, ensuring that companies can scale efficiently and effectively.
As the global market for custom software is projected to reach USD 52.84 billion by 2025, organizations that prioritize scalability position themselves to navigate market fluctuations and maintain a competitive edge. Industry experts emphasize:
Moreover, companies relying on ready-made options may face challenges such as system failures and performance issues during expansion, underscoring the necessity for custom solutions. To effectively implement scalable technological strategies, consider partnering with skilled development teams that prioritize scalability from the outset.
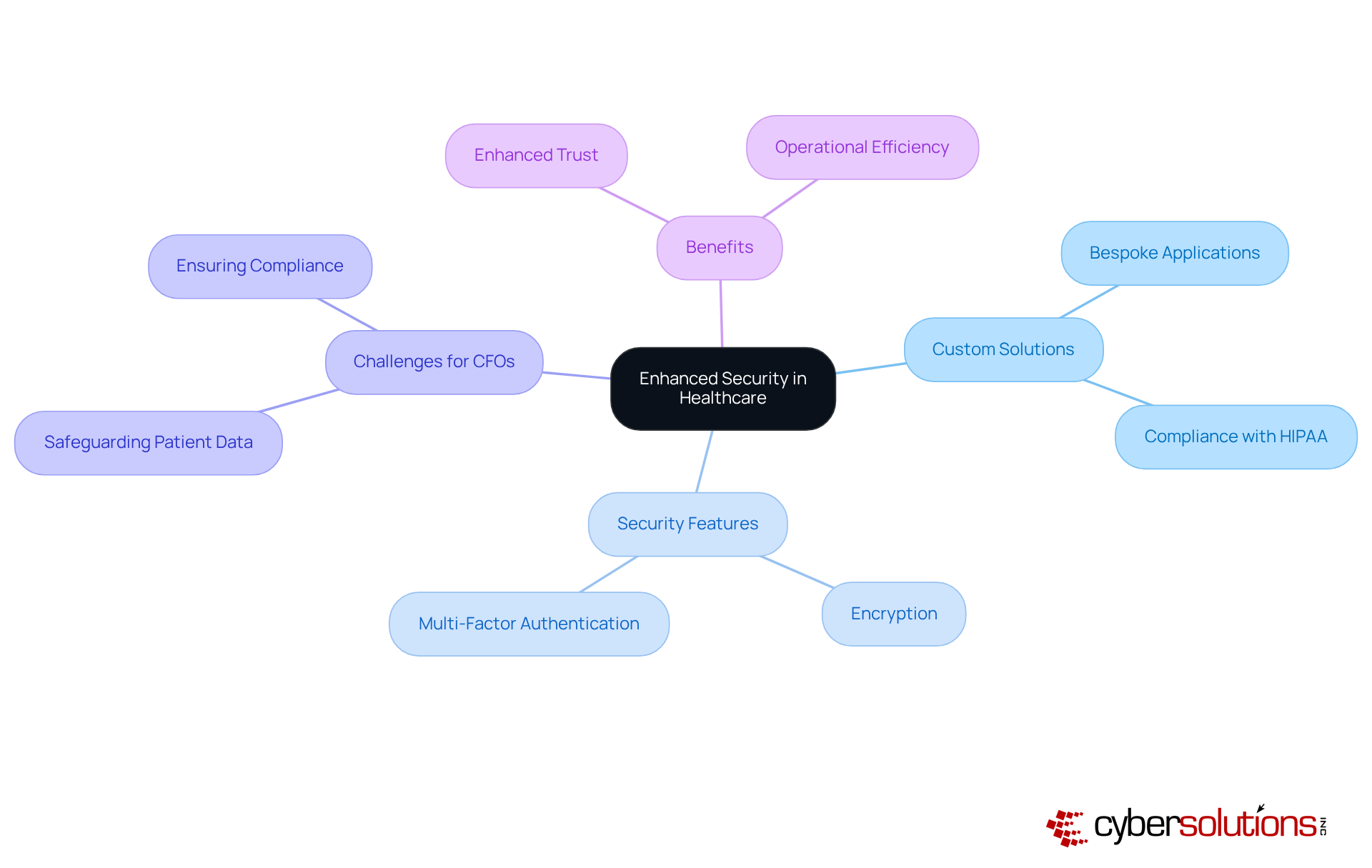
In today's digital landscape, the significance of cybersecurity in healthcare cannot be overstated. The software offers enhanced security features tailored to the unique requirements of healthcare organizations, addressing the growing threats posed by cybercriminals. By integrating advanced security protocols—such as encryption and multi-factor authentication—these solutions empower organizations to protect sensitive patient information from unauthorized access and potential breaches.
Healthcare CFOs face unique challenges in safeguarding sensitive data while ensuring compliance. For example, custom software can create a bespoke healthcare application that is meticulously designed to meet these stringent requirements, ensuring that patient information is not only securely managed but also stored in accordance with legal standards. This level of customization not only fortifies critical information but also fosters trust among clients and stakeholders, reinforcing the organization’s reputation.
As the landscape of cybersecurity continues to evolve, organizations must prioritize robust solutions that not only mitigate risks but also enhance operational efficiency. By investing in tailored cybersecurity measures, organizations can navigate the complexities of data protection, ultimately safeguarding their most valuable asset—patient trust.
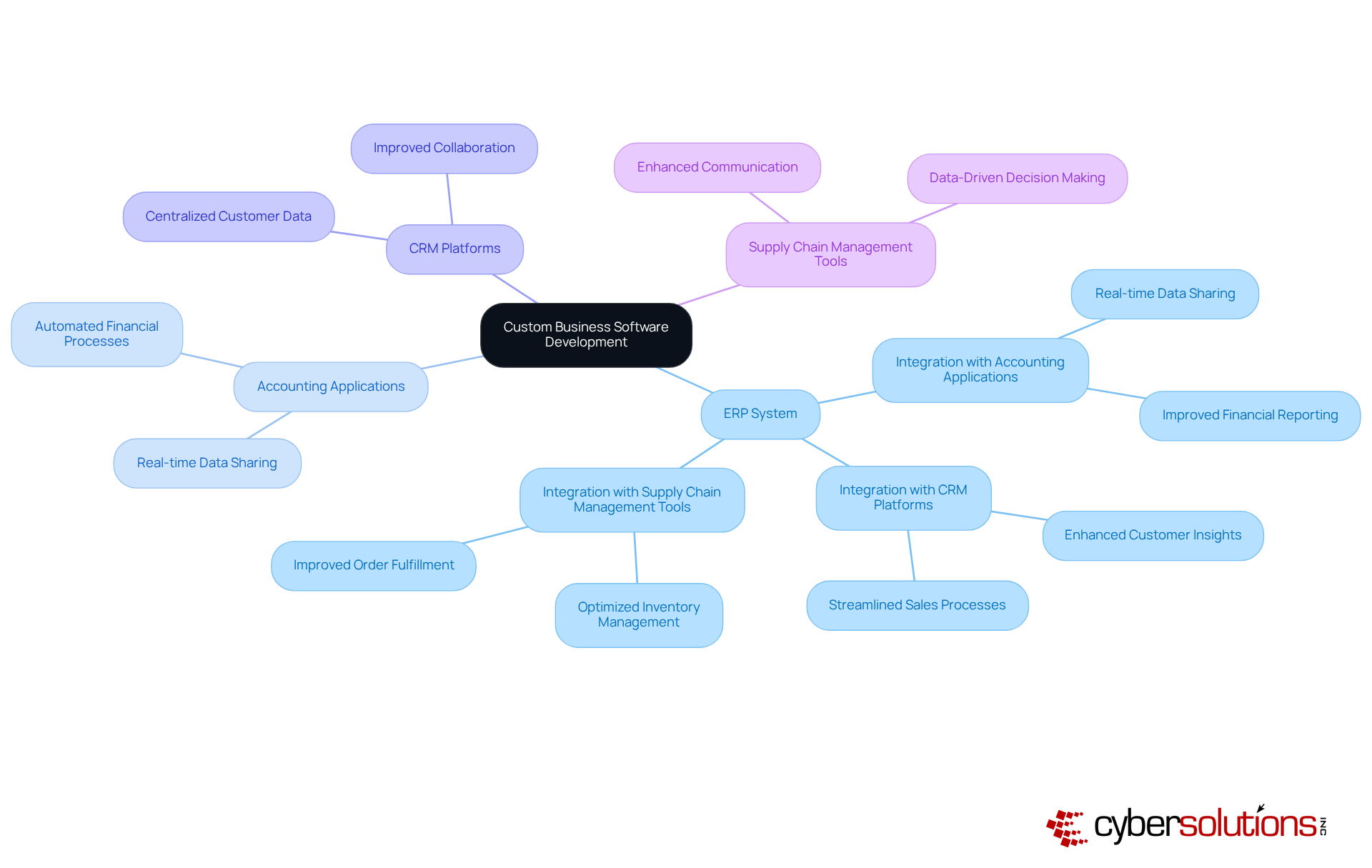
Custom software development allows for the creation of tailored applications that can integrate seamlessly with existing organizational tools and systems, significantly enhancing overall productivity. Consider, for instance, a customized ERP system that connects with CRM platforms and supply chain management tools. This integration facilitates communication and fosters improved collaboration across departments. By minimizing data silos, it ensures that all teams have access to the critical information necessary for informed decision-making, ultimately driving superior business outcomes.
While the initial investment in custom software may exceed that of off-the-shelf solutions, the potential long-term savings are significant. Custom software eliminates recurring licensing fees and minimizes costs associated with software maintenance and upgrades. Moreover, by enhancing productivity and reducing downtime, businesses can achieve a faster return on investment.
For example, a custom solution can optimize workflows, resulting in increased efficiency and reduced labor costs over time. CFOs frequently report benefits from adopting custom software, with some companies realizing savings of 30-50% over time. This trend aligns with the growing recognition among business leaders that investing in custom software not only addresses specific needs but also drives overall growth.
Custom software development empowers enterprises to carve out a distinctive competitive edge by integrating features that standard products cannot deliver. This approach to software allows companies to meet their customers' needs more effectively and adapt swiftly to market changes.
For example, a custom solution can incorporate personalized recommendations and optimized checkout processes, significantly enhancing the shopping experience. Such innovations not only attract more customers but also improve retention, as evidenced by a notable 30% increase in user satisfaction reported by companies leveraging custom software.
As Daniel Matusiak, CMO of KonsJez, articulated, 'This project serves as a prime example of how we can leverage UX/UI design to enhance the functionality of mobile banking apps, catering to today's fast-paced lifestyles.' By focusing on unique technological capabilities, organizations can differentiate themselves, ultimately establishing themselves as leaders in their respective markets.
Furthermore, entities in sectors such as retail have successfully utilized custom software to streamline operations and improve efficiency, further underscoring the adaptability and significance of personalized approaches.
User experience is crucial for organizations aiming to create solutions that align precisely with the unique needs and preferences of their users. By actively engaging end-users in the design process, companies can develop intuitive and navigable applications. For instance, a custom application can feature user-friendly interfaces that streamline onboarding and performance evaluations, significantly enhancing the overall experience. This not only boosts adoption rates but also drives productivity and employee satisfaction.
Research indicates that organizations utilizing custom software report a 20% rise in customer satisfaction, underscoring the importance of customizing applications to meet user requirements. Furthermore, firms that prioritize user feedback achieve an impressive 92% success rate in meeting project goals, highlighting the essential role of teamwork and input in crafting effective outcomes.
Moreover, flexibility enables companies to adapt to evolving demands while maintaining high performance. This adaptability is vital in today’s fast-paced business environment, where the ability to pivot quickly can determine success.
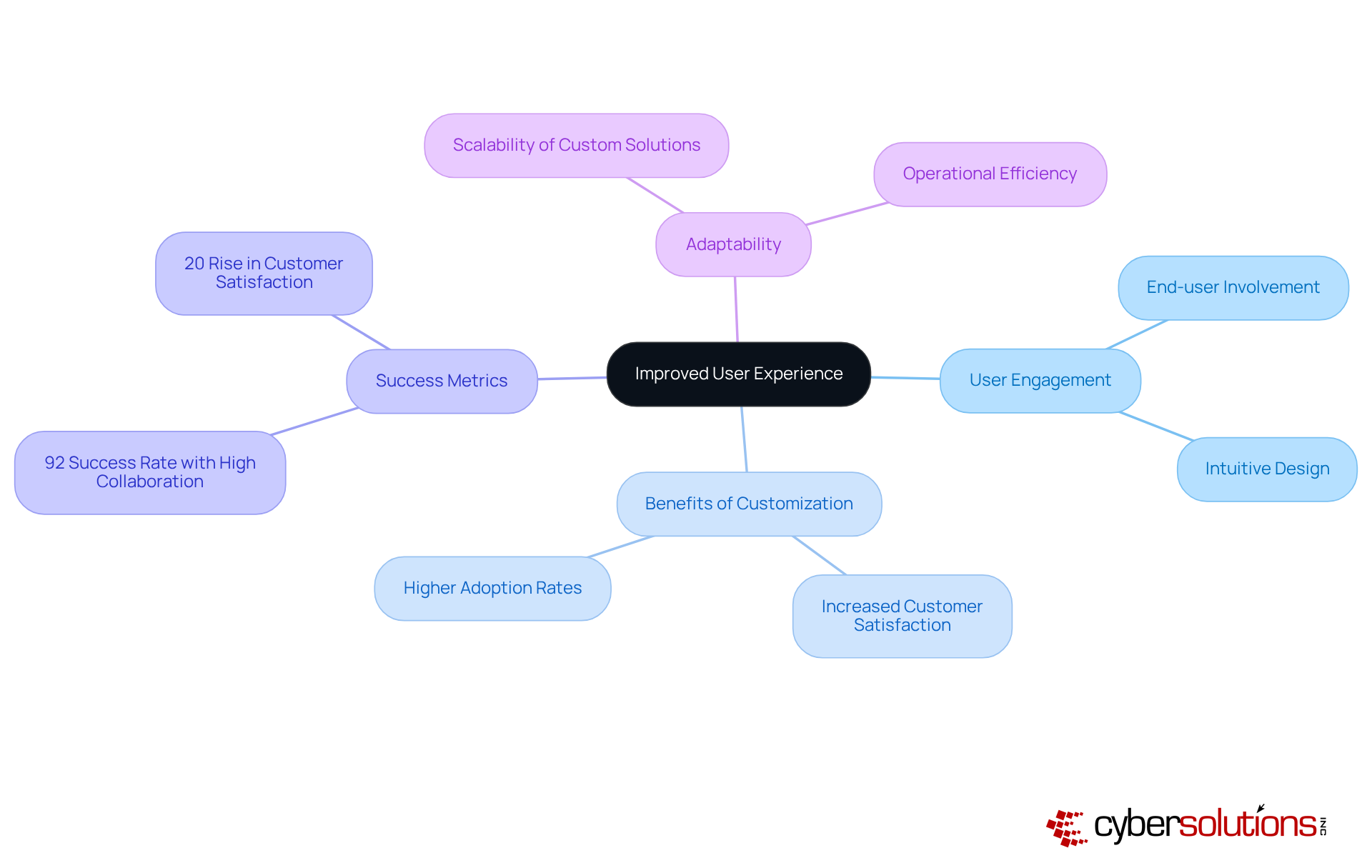
Organizations seeking to find that flexibility is essential for success. In a landscape where market conditions fluctuate and new technologies emerge, companies can seamlessly adjust their operations to incorporate innovations without the need to start from scratch.
For example, consider a software solution that can be updated to include new shipping options or integrate with cutting-edge technologies like AI for predictive analytics. This level of adaptability not only ensures that businesses remain competitive but also positions them to grow over time with evolving market demands.

Investing in custom business software development requires a robust framework for maintenance, which is essential for achieving long-term success. Regular updates, bug fixes, and enhancements are critical for ensuring that the application operates smoothly and securely. Cyber Solutions Inc. provides comprehensive maintenance packages that encompass:
Alongside that, these packages guarantee your systems are always optimized. This not only safeguards the initial investment but also adapts the system to meet the evolving requirements of the business environment, thereby enhancing its value over time.
Companies utilizing custom software solutions, including network monitoring and security alerts, have reported significant improvements in operational efficiency and reduced downtime. In fact, organizations leveraging tailored applications have achieved a 26% decrease in long-term expenses, reinforcing the vital role of ongoing support and maintenance. As Mahipal Nehra states, "Ongoing support is a powerful driver of success," highlighting the importance of comprehensive support in ensuring business continuity and security.
Custom business software development stands as a transformative solution for organizations striving to enhance operational efficiency, scalability, and security. By tailoring software to meet specific business needs, companies can streamline processes, reduce costs, and ultimately secure a competitive edge in their respective markets. The capacity to adapt to evolving requirements and integrate seamlessly with existing tools further emphasizes the necessity of investing in customized solutions.
Key benefits of custom software development include:
Moreover, the long-term cost-effectiveness of tailored solutions, coupled with ongoing support and maintenance, ensures that organizations can maximize their investment while adeptly navigating the complexities of the digital landscape.
In conclusion, embracing custom business software development is not merely a choice; it is a strategic imperative for organizations aiming to thrive in today’s fast-paced environment. By prioritizing tailored solutions, businesses can effectively address their unique challenges and position themselves for sustainable growth and success. Investing in custom software is an investment in the future, empowering organizations to innovate, adapt, and excel in an ever-evolving marketplace.
What services does Cyber Solutions Inc. offer?
Cyber Solutions Inc. specializes in custom business software development services that enhance business efficiency while integrating extensive cybersecurity protocols, including endpoint protection, email security, and firewalls.
How does Cyber Solutions Inc. ensure cybersecurity in its software solutions?
The company employs advanced cybersecurity measures such as application allowlisting to proactively mitigate risks of malware and unauthorized applications, ensuring compliance with industry regulations like HIPAA, PCI-DSS, and GDPR.
What benefits do custom software solutions provide for businesses?
Custom software solutions streamline operations by automating repetitive tasks and optimizing workflows, leading to significant time savings and allowing employees to focus on higher-value activities.
How much time can companies save by implementing custom software solutions?
Companies that have implemented custom software solutions report a 30% to 50% reduction in time spent on repetitive tasks, which enhances service delivery and customer satisfaction.
What is the projected growth of the custom business software development market?
The global market for custom business software development is projected to reach USD 52.84 billion by 2025.
What is the significance of scalability in custom software development?
Scalability allows custom software to grow alongside an organization, accommodating increased workloads and new functionalities without the need for expensive upgrades or replacements.
Why should companies prioritize custom software over off-the-shelf solutions?
Custom software is designed to adapt to an organization's evolving needs, reducing the risk of system failures and performance issues during expansion, which are common with off-the-shelf solutions.