Introduction
In an era where cyber threats are more prevalent than ever, businesses must prioritize their digital security strategies. Two-factor authentication (2FA) stands out as a vital line of defense, providing enhanced protection against unauthorized access and data breaches. This article explores the leading 2FA service providers, comparing their features, benefits, and costs to assist organizations in navigating the intricate landscape of cybersecurity solutions. As companies grapple with the increasing demand to protect sensitive information, one question looms large: which 2FA provider will best fulfill their unique security needs while ensuring user satisfaction and compliance?
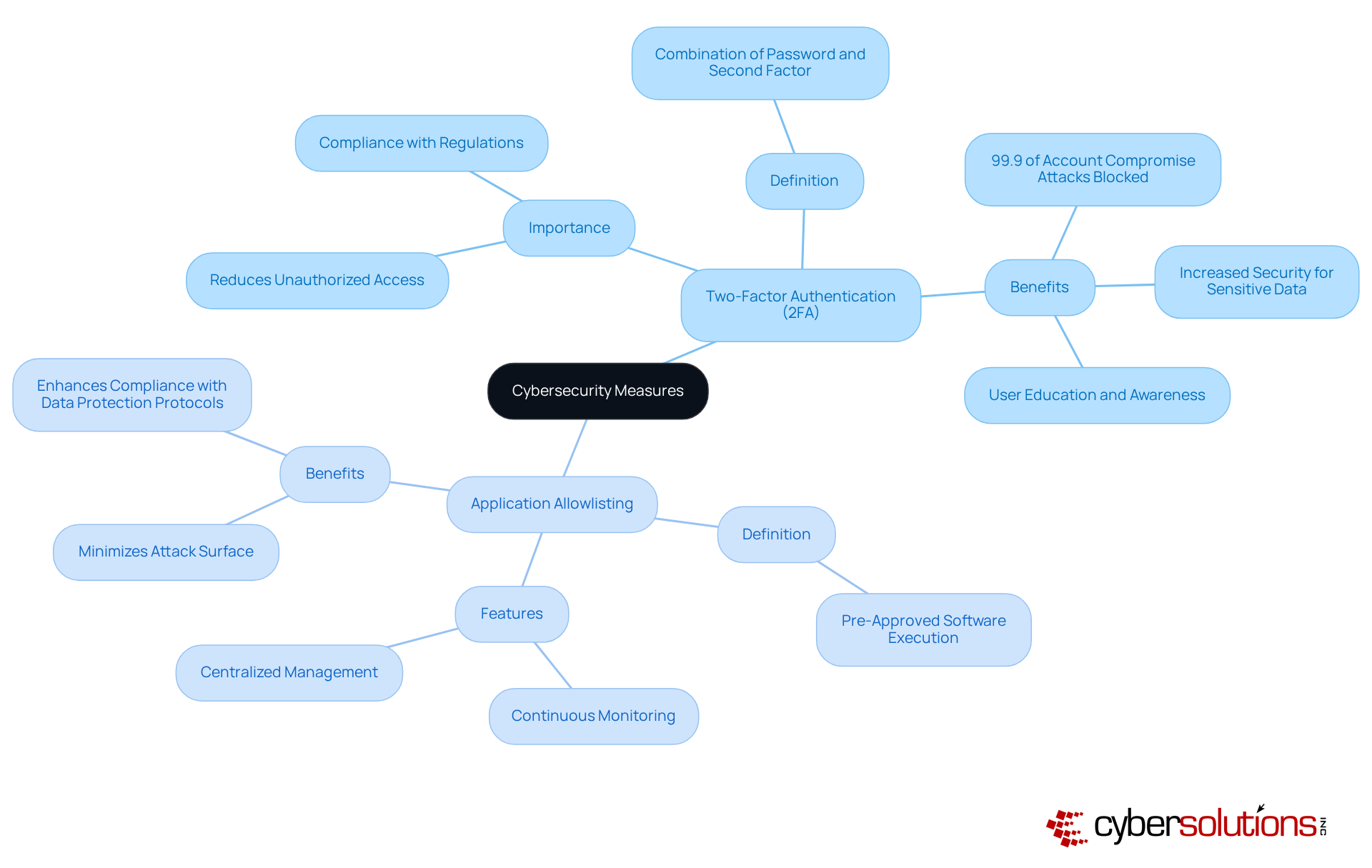
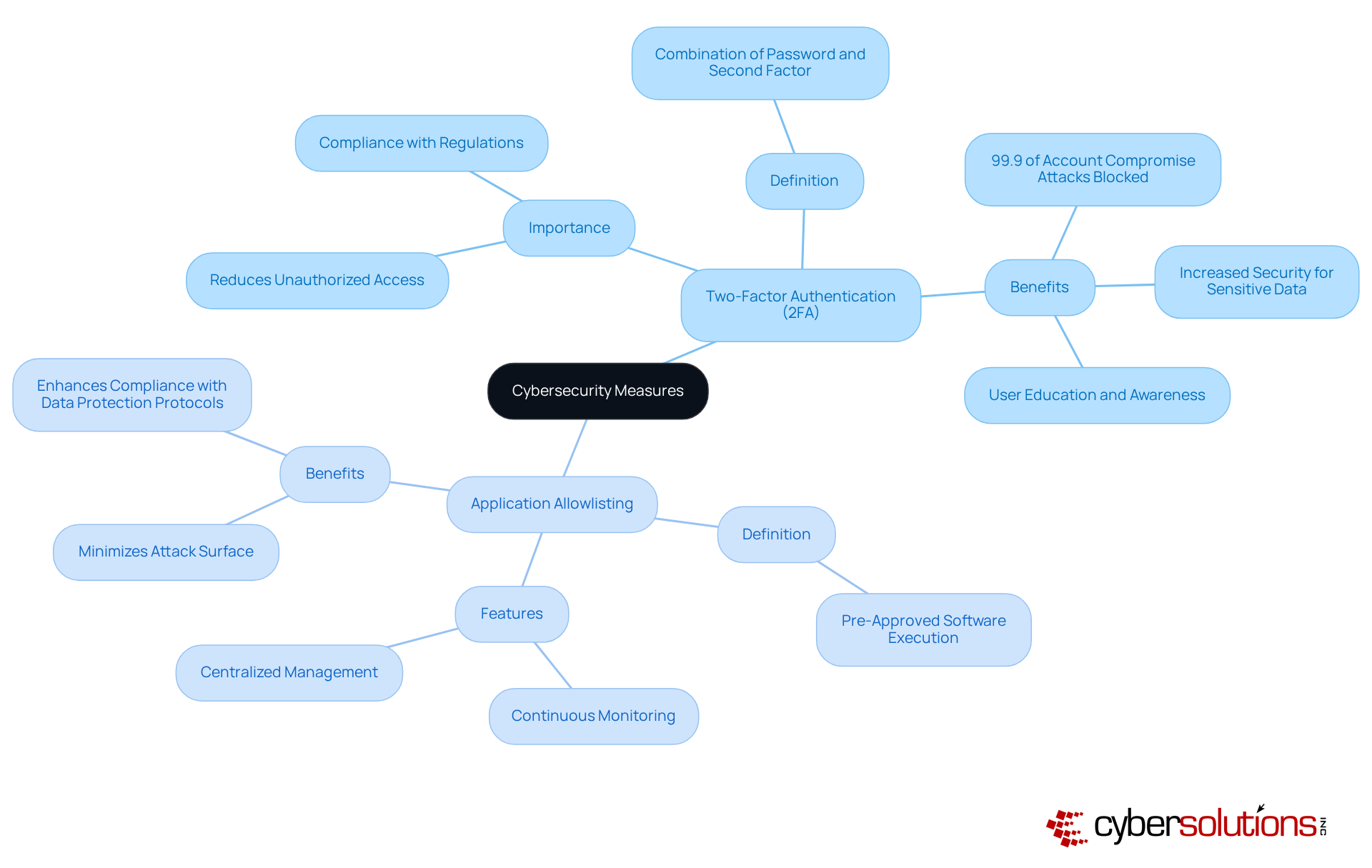
Understanding Two-Factor Authentication: Definition and Importance
In today’s digital landscape, cybersecurity is not just an option; it’s a necessity, especially in healthcare. Two-factor authentication (2FA), as highlighted by two factor authentication service providers, stands out as a vital security measure, requiring individuals to provide two distinct forms of identification to access an account or system. This typically combines something the user knows, like a password, with something the user possesses, such as a smartphone app that generates a one-time code. The significance of two factor authentication service providers is clear: they drastically reduce the risk of unauthorized access, even when passwords are compromised. Did you know that 99.9% of account compromise attacks can be thwarted by implementing multi-factor authentication (MFA)? This makes it an essential strategy for businesses aiming to protect sensitive data and comply with industry regulations by working with two factor authentication service providers.
Complementing 2FA, application allowlisting serves as a proactive cybersecurity measure that prevents unauthorized or malicious applications from executing on systems. By allowing only pre-approved software to run, organizations can significantly reduce their attack surface and minimize vulnerabilities. Features such as continuous monitoring of application activity and centralized management of allowlists enhance protection by ensuring prompt identification and blocking of threats. This dual approach not only improves safety but also assists in meeting stringent compliance requirements, ensuring that businesses adhere to data protection protocols. Together, two factor authentication service providers and application allowlisting create a robust defense against cyber threats, effectively safeguarding sensitive information from ransomware and phishing attacks.
Comparing Features of Leading Two-Factor Authentication Providers
In today’s digital landscape, the importance of robust cybersecurity cannot be overstated, especially when it comes to protecting sensitive information. When evaluating two-factor authentication (2FA) providers, several key features should be prioritized to ensure both security and user satisfaction:
- Authentication Methods: Leading providers like Google Authenticator and Authy offer app-based authentication, while others, such as Cisco Duo, provide hardware tokens. This variety enables companies to select approaches that best suit their protection requirements.
- Integration Capabilities: Solutions like Okta and Microsoft Entra ID excel in seamlessly connecting with existing enterprise systems. This makes them particularly suitable for larger organizations that require cohesive protection frameworks across multiple platforms.
- User Experience: A user-friendly interface is critical for adoption. Providers like LastPass MFA highlight simplicity, guaranteeing that the authentication process is straightforward and reduces friction for individuals.
- Security Features: Advanced options, including biometric authentication and adaptive risk-based authentication, are offered by providers like Cisco Duo. These traits improve protection while preserving a seamless experience, adjusting to the context of each login attempt.
- Support and Documentation: Comprehensive support and clear documentation are essential for smooth implementation and ongoing use. Providers like Ping Identity are recognized for their strong support systems, which enable effective deployment and training for individuals.
By evaluating these characteristics, organizations can choose a solution from two-factor authentication service providers that not only fulfills their protection needs but also enhances user satisfaction and operational effectiveness.

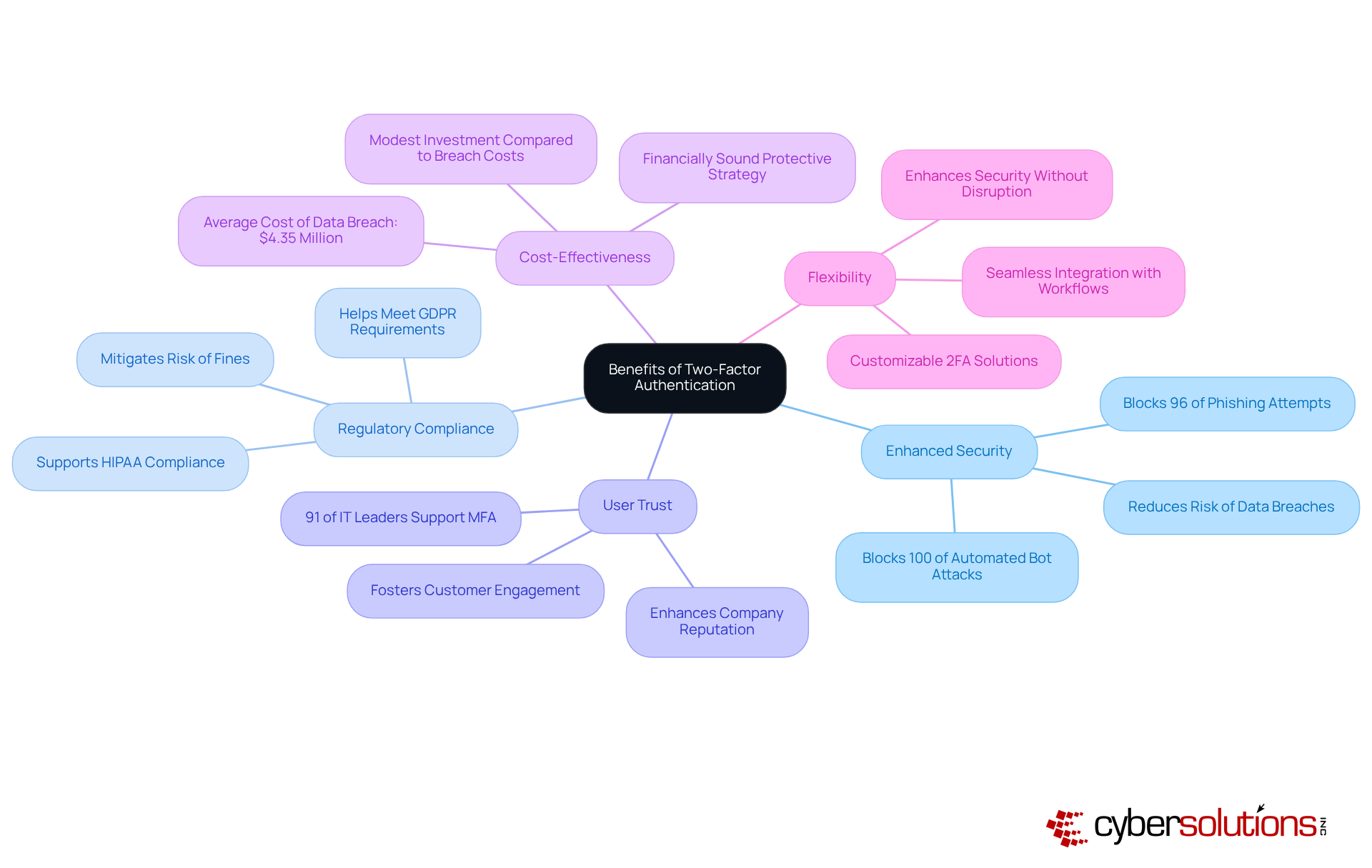
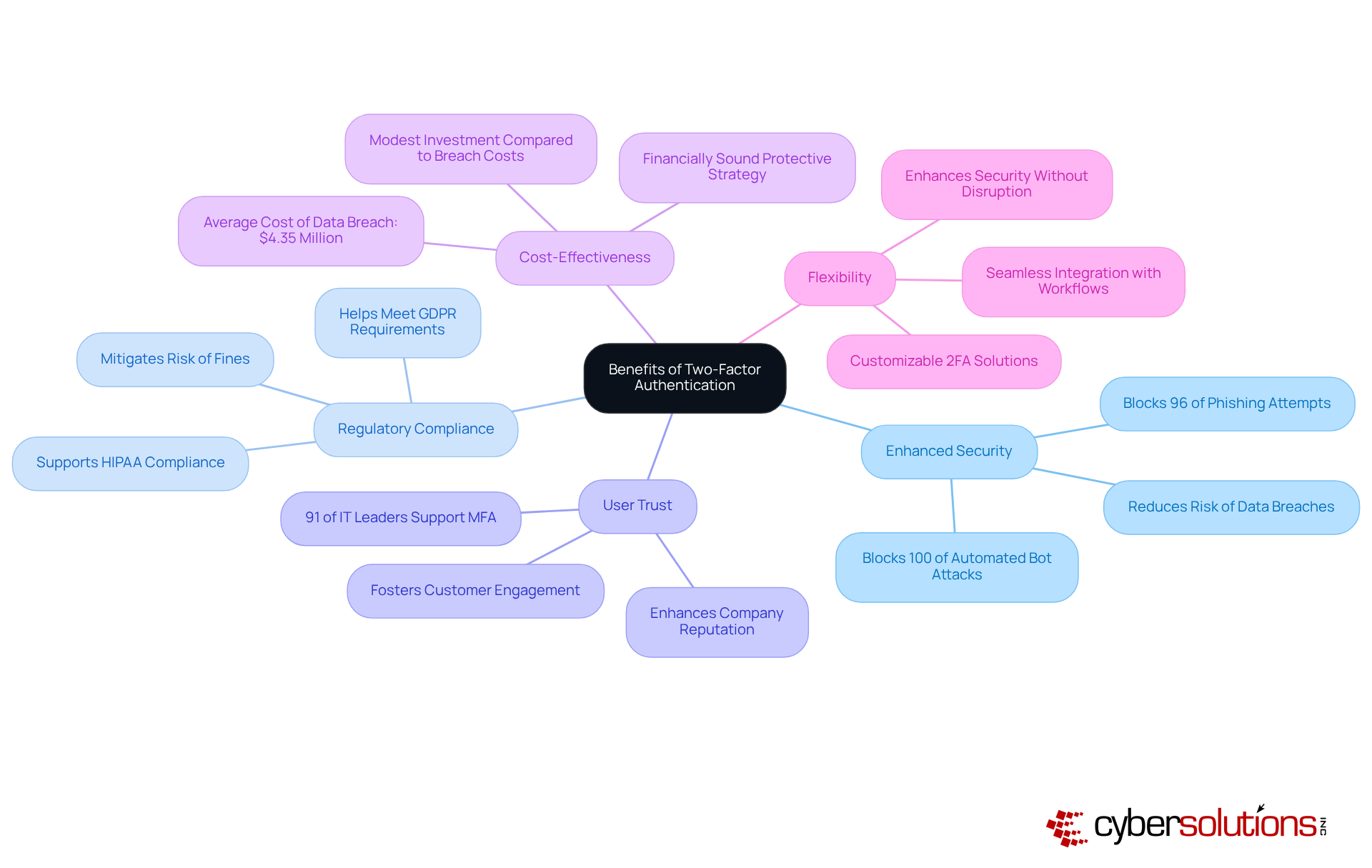
Evaluating Benefits of Two-Factor Authentication Solutions
Implementing two-factor authentication (2FA) is not just a technical upgrade; it’s a crucial step in fortifying your business against the ever-evolving landscape of cybersecurity threats. In today’s digital age, where breaches can lead to devastating consequences, the importance of robust security measures cannot be overstated.
- Enhanced Security: By requiring two distinct forms of verification, 2FA drastically lowers the risk of unauthorized access, effectively safeguarding sensitive data from breaches. Research indicates that 2FA can block 100% of automated bot attacks and 96% of phishing attempts. Isn’t it time to take a stand against modern cyber threats?
- Regulatory Compliance: Many sectors face stringent regulations demanding strong protective measures. Adopting 2FA not only helps organizations meet these compliance mandates but also mitigates the risk of fines and legal repercussions. For instance, implementing 2FA demonstrates proactive efforts to comply with GDPR and HIPAA requirements, essential for maintaining trust and avoiding costly penalties.
- User Trust: Companies that prioritize protection through 2FA are more likely to foster customer engagement. Enhanced security measures not only protect sensitive information but also bolster the company’s reputation, leading to increased trust among clients. A survey revealed that 91% of IT leaders agree that multi-factor authentication is vital for organizational safety, underscoring its role in building customer confidence.
- Cost-Effectiveness: The investment in 2FA solutions is relatively modest compared to the potential financial fallout from data breaches, which averaged $4.35 million globally in 2022. By implementing 2FA, businesses can significantly reduce the likelihood of such breaches, making it a financially sound protective strategy.
- Flexibility: Many 2FA solutions offer customizable options tailored to the unique needs of businesses, ensuring that security measures integrate seamlessly with operational workflows. This flexibility allows companies to enhance their security posture without disrupting existing processes.
Analyzing Costs of Two-Factor Authentication Services
In today's digital landscape, the costs associated with two factor authentication service providers can vary significantly based on the provider and the features offered. Understanding these costs is crucial for organizations aiming to bolster their cybersecurity measures. Here are some key considerations:
- Pricing Models: Most providers operate on a subscription basis, typically charging between $3 to $6 per user per month. For instance, Duo's Essentials plan starts at $3/user/month, while its Business plan costs $6/user/month. This pricing model allows companies to budget effectively while ensuring robust protection. With Cyber Solutions, you can simplify your budgeting with our flat-rate pricing model, which covers everything from email licenses to advanced cybersecurity. This approach eliminates unexpected IT expenses and guarantees predictable monthly costs for your business.
- Setup Fees: Initial setup fees can significantly impact your overall investment, especially for customized solutions. Some providers may impose these fees, which should be factored into your cost assessment. Implementing MFA often requires engineering time for integration, testing, and ongoing maintenance, adding to the initial investment.
- Hidden Costs: Businesses must remain vigilant about potential hidden costs, such as additional charges for premium features or support services. Providers frequently charge per attempt for message delivery rather than per successful delivery, leading to unexpected expenses, particularly if there are issues with message delivery.
- Long-Term Value: While initial expenses are important, organizations should also consider the long-term benefits of investing in a reliable 2FA solution. The average data breach costs approximately $4.88 million, underscoring the significant ROI of MFA by potentially preventing serious incidents. Each phishing or credential theft attack blocked by MFA can save companies millions in breach-related costs.
- Scalability: As companies grow, their protection requirements may evolve. Selecting one of the two factor authentication service providers that offers scalable solutions is essential for managing costs effectively over time. For example, SuperTokens can accommodate user growth from a few hundred to millions without the need to rearchitect existing authentication flows, ensuring that organizations can adapt their security measures as needed.

Conclusion
Implementing two-factor authentication (2FA) is not just a recommendation; it’s a crucial necessity for businesses aiming to bolster their cybersecurity defenses. In a landscape rife with cyber threats, requiring users to provide two distinct forms of identification can drastically reduce the risk of unauthorized access and safeguard sensitive data. Choosing the right two-factor authentication service provider is paramount, as it directly influences the effectiveness of these security measures.
Key features of leading 2FA providers have been examined, showcasing various authentication methods, integration capabilities, user experience, security features, and support systems. The advantages of 2FA extend well beyond enhanced security; they encompass regulatory compliance, increased user trust, cost-effectiveness, and implementation flexibility. Collectively, these factors highlight the urgent need for robust 2FA solutions to defend against the ever-evolving cyber threat landscape.
Given the substantial risks tied to data breaches and their financial repercussions, investing in a reliable two-factor authentication service is a wise choice for any organization. By prioritizing cybersecurity through 2FA, businesses not only protect their assets but also cultivate a security-centric culture that enhances customer trust and ensures compliance with industry regulations. Embracing these protective measures is more than a defensive tactic; it’s a proactive strategy that positions businesses for success in an increasingly digital world.
Frequently Asked Questions
What is two-factor authentication (2FA)?
Two-factor authentication (2FA) is a security measure that requires individuals to provide two distinct forms of identification to access an account or system. This typically combines something the user knows, like a password, with something the user possesses, such as a smartphone app that generates a one-time code.
Why is two-factor authentication important?
Two-factor authentication is important because it drastically reduces the risk of unauthorized access, even if passwords are compromised. It is a critical strategy for businesses to protect sensitive data and comply with industry regulations.
How effective is multi-factor authentication (MFA) in preventing account compromise?
Implementing multi-factor authentication (MFA) can thwart 99.9% of account compromise attacks, making it an essential security strategy.
What is application allowlisting?
Application allowlisting is a proactive cybersecurity measure that prevents unauthorized or malicious applications from executing on systems by allowing only pre-approved software to run.
How does application allowlisting enhance cybersecurity?
Application allowlisting enhances cybersecurity by significantly reducing the attack surface and minimizing vulnerabilities. Features such as continuous monitoring of application activity and centralized management of allowlists help in promptly identifying and blocking threats.
How do two-factor authentication and application allowlisting work together?
Together, two-factor authentication and application allowlisting create a robust defense against cyber threats, effectively safeguarding sensitive information from ransomware and phishing attacks while helping organizations meet compliance requirements.
List of Sources
- Understanding Two-Factor Authentication: Definition and Importance
- Two‑Factor Authentication (2FA): Why It Matters in 2026 (https://qwertytechnicalsolutions.com/passwords-arent-enough-why-you-need-two-factor-authentication-in-2026)
- Microsoft Confirms New And Widespread 2FA Code Attacks Ongoing (https://forbes.com/sites/daveywinder/2026/04/08/microsoft-warning-new-and-widespread-2fa-code-attacks-confirmed)
- Multi-Factor Authentication Statistics and Facts (2026) (https://scoop.market.us/multi-factor-authentication-statistics)
- Multi-Factor Authentication Adoption Rates: Are We Doing Enough? (https://patentpc.com/blog/multi-factor-authentication-adoption-rates-are-we-doing-enough)
- Digital Trust Index 2026: AI Skepticism and Identity Access Friction Are Costing Revenue (https://finance.yahoo.com/sectors/technology/articles/digital-trust-index-2026-ai-120000839.html)
- Comparing Features of Leading Two-Factor Authentication Providers
- 10 Best Multi-Factor Authentication Solutions of 2026 | OLOID (https://oloid.com/blog/multi-factor-authentication-solutions)
- Top 5 Multi-Factor Authentication (MFA) Providers for 2026 (https://blog.scalefusion.com/best-multi-factor-authentication-solutions)
- Top 5 MFA providers for securing your app in 2026 — WorkOS (https://workos.com/blog/top-mfa-providers-2026)
- Multi-Factor Authentication Statistics and Facts (2026) (https://scoop.market.us/multi-factor-authentication-statistics)
- Top 13 MFA Providers in 2026: Features, Pricing & Comparison (https://miniorange.com/blog/mfa-providers)
- Evaluating Benefits of Two-Factor Authentication Solutions
- Two-Factor Authentication (2FA): Why Your Business Needs It 2026 (https://silver-lining.com/two-factor-authentication-2fa-why-your-business-needs-it)
- How Can 2FA Help Businesses Comply with Regulations like GDPR and HIPAA? | BSG Blog (https://bsg.world/blog/guides/how-can-2fa-help-businesses-comply-with-regulations-like-gdpr-and-hipaa)
- electroiq.com (https://electroiq.com/stats/multifactor-authentication-statistics)
- Multi-Factor Authentication Statistics and Facts (2026) (https://scoop.market.us/multi-factor-authentication-statistics)
- 2FA: A Small Habit, Big Protection – Why Two-Factor Authentication Matters - Star Computer Services (https://starcomputerservice.com/2026/04/13/2fa-a-small-habit-big-protection-why-two-factor-authentication-matters)
- Analyzing Costs of Two-Factor Authentication Services
- Breaking Down the Cost of Multi-Factor Authentication: Is It Worth It? (https://supertokens.com/blog/multi-factor-auth-cost)
- How Much Does Two-Factor Authentication Cost? (2026) - Authgear (https://authgear.com/post/two-factor-authentication-cost)
- The Cost & ROI of Multi-Factor Authentication (https://trustedtechteam.com/blogs/security/the-cost-roi-of-multi-factor-authentication)
- How Much Does Two-Factor Authentication Cost? A Complete Breakdown (https://dexatel.com/blog/two-factor-authentication-cost)
- Duo Blog: Discover Security Insights and News | Cisco Duo (https://duo.com/blog/how-to-evaluate-the-true-costs-of-mfa)