Introduction
In a world where cyber threats are not just a possibility but a reality, healthcare organizations must confront the urgent need for robust cybersecurity measures. Effective cybersecurity evaluations go beyond mere compliance; they are essential for protecting sensitive data and preserving the trust of patients and stakeholders. With cyber threats evolving daily, the stakes have never been higher for healthcare organizations.
How can they ensure their security measures are not only robust but also adaptable to emerging risks? Let’s explore best practices for conducting thorough cybersecurity evaluations, providing actionable insights that help organizations navigate today’s complex cyber landscape.
Assess the Current Cyber Threat Landscape
In an era where cyber threats loom larger than ever, the healthcare sector stands at a critical juncture, facing unprecedented challenges in safeguarding sensitive data. To effectively conduct a cyber security evaluation, organizations must first assess the current cyber risk landscape. This involves recognizing common risks such as ransomware, phishing attacks, and insider threats. With ongoing surveillance, organizations can catch questionable actions early, stopping them before they escalate into serious threats, thereby safeguarding themselves from various cyber challenges. Utilizing resources like the 2026 Global Threat Report can provide insights into emerging risks and trends. Organizations should regularly assess security intelligence reports and collaborate with cybersecurity companies like Cyber Solutions to stay informed about the latest attack vectors. By recognizing the particular risks they encounter, businesses can conduct a cyber security evaluation in collaboration with cybersecurity experts, allowing them to tailor their security strategies and effectively address their unique vulnerabilities.
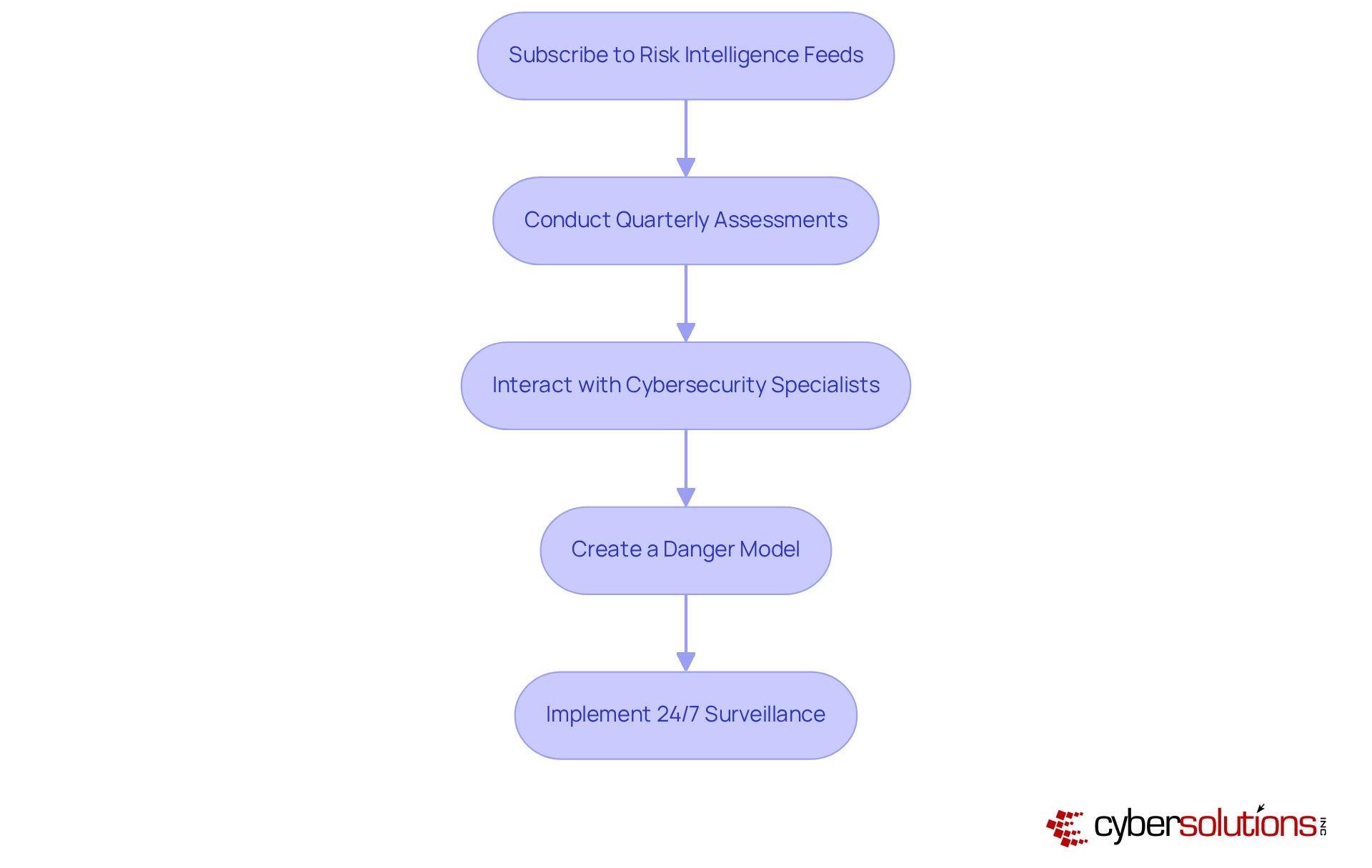
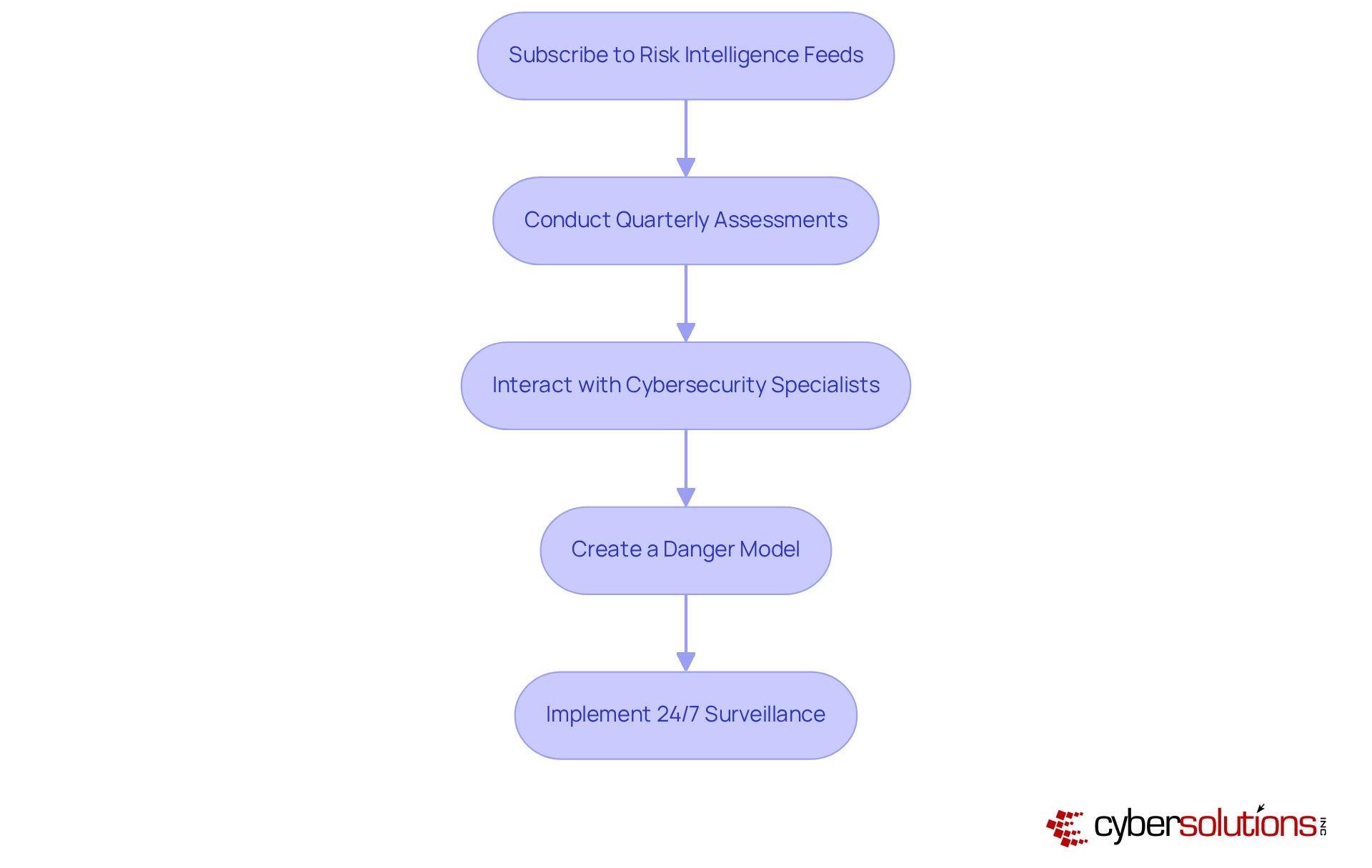
Actionable Steps:
- Subscribe to risk intelligence feeds and reports.
- Conduct quarterly assessments of the risk landscape.
- Interact with cybersecurity specialists to analyze risk information pertinent to your industry.
- Create a danger model that represents the distinctive challenges your organization encounters.
- Implement 24/7 surveillance to proactively safeguard against ransomware and phishing attacks.
By taking proactive measures, organizations can not only protect their assets but also ensure the trust of their patients and stakeholders in an increasingly digital world.
Conduct Comprehensive Risk Assessments
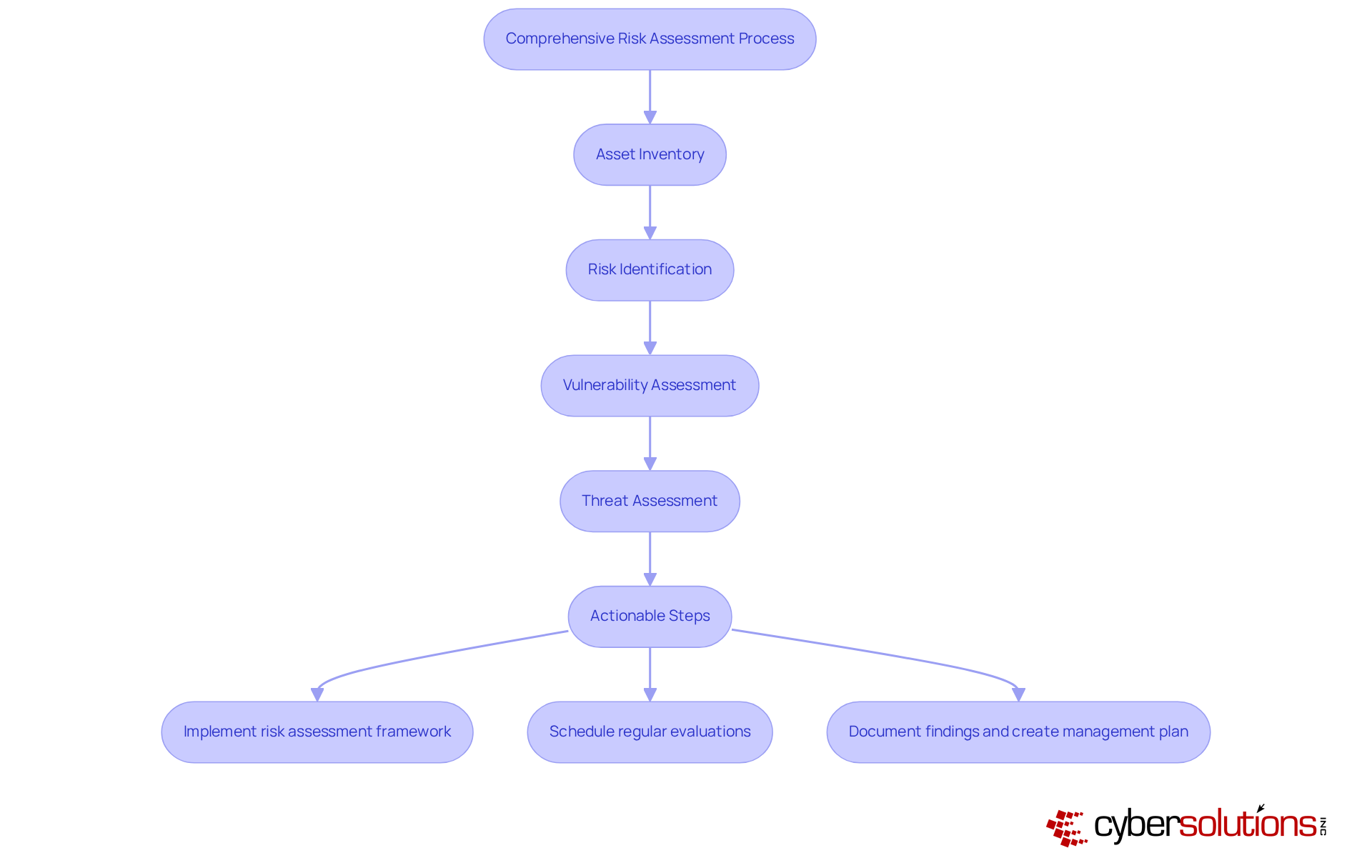
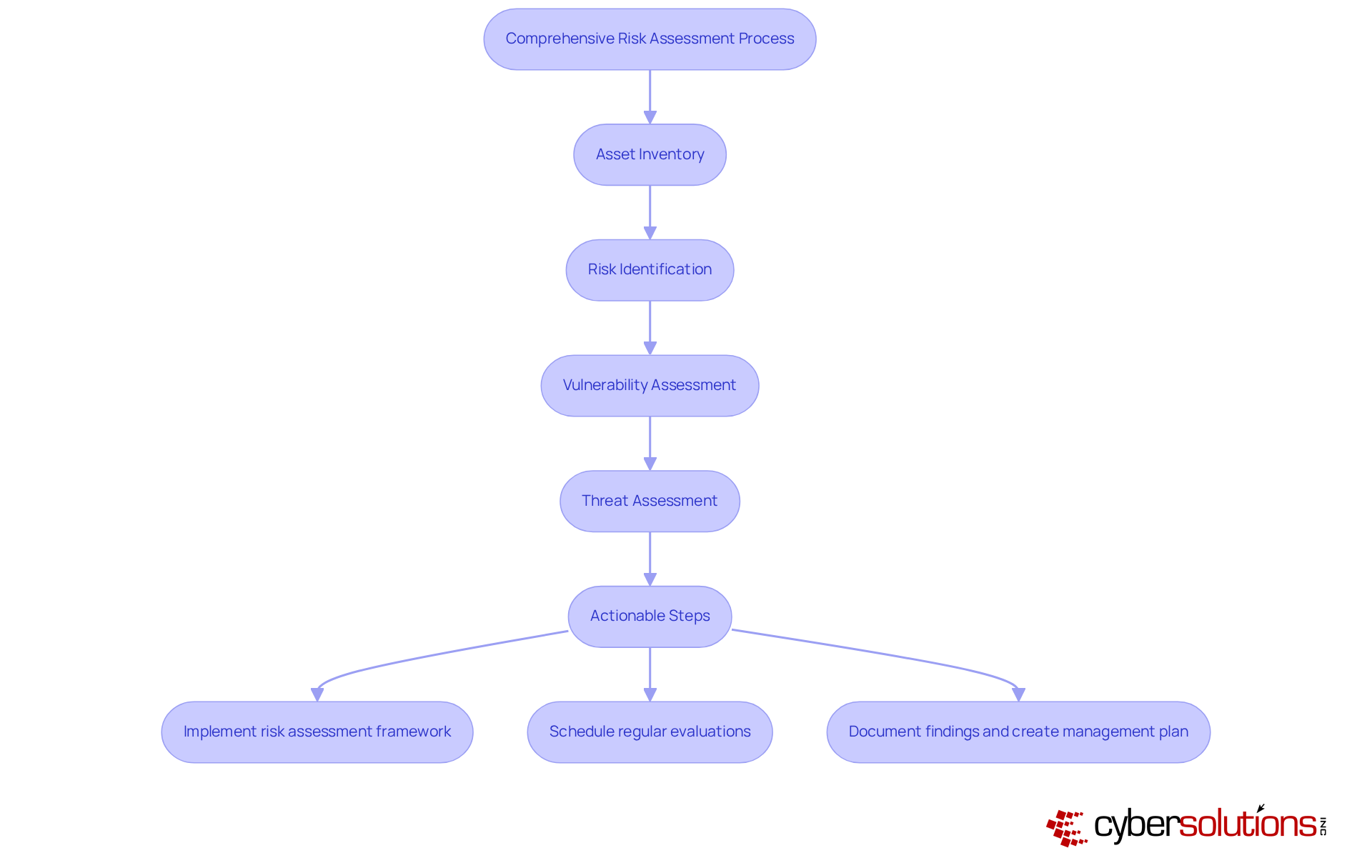
In an era where healthcare data breaches are on the rise, the need for robust cybersecurity measures has never been more critical. Comprehensive risk assessments are foundational to effective cyber security evaluation. To effectively tackle these challenges, organizations must focus on the following key areas:
- Asset Inventory: Maintain a detailed catalog of all critical assets, including hardware, software, and sensitive data. This inventory is vital for understanding what needs protection and for identifying potential vulnerabilities.
- Risk Identification: Analyze potential risks specific to your industry, such as data breaches or compliance violations. Understanding these threats is crucial for developing targeted defense strategies.
- Vulnerability Assessment: Utilize established frameworks like NIST SP 800-30 to systematically identify weaknesses in your security posture. This framework offers a thorough methodology for cyber security evaluation of weaknesses and is widely embraced across different sectors.
- Threat Assessment: Assess the probability and possible effect of identified hazards to prioritize mitigation efforts effectively. This analysis helps organizations allocate resources where they are most needed, enhancing overall security.
Furthermore, Cyber Solutions performs thorough cyber security evaluations to pinpoint compliance gaps and threats within your systems, offering practical suggestions to mitigate vulnerabilities. We help you create HIPAA-compliant policies and procedures, ensuring your organization aligns with administrative, physical, and technical safeguards.
Actionable Steps:
- Implement a risk assessment framework that aligns with industry standards to ensure comprehensive coverage of potential risks. For example, almost 75% of businesses encountered at least one significant hazard event in the past year, highlighting the urgency of carrying out these evaluations.
- Schedule regular cyber security evaluations, ideally at least annually, to adapt to evolving threats and vulnerabilities.
- Document findings thoroughly and create a management plan that outlines clear mitigation strategies, ensuring accountability and ongoing enhancement in cybersecurity practices. Furthermore, organizations should be mindful of typical pitfalls in evaluations, such as neglecting to update asset inventories or overlooking to include key stakeholders in the process.
Without proactive measures, organizations risk not only financial loss but also the trust of their patients and stakeholders.
Implement Robust Compliance Measures
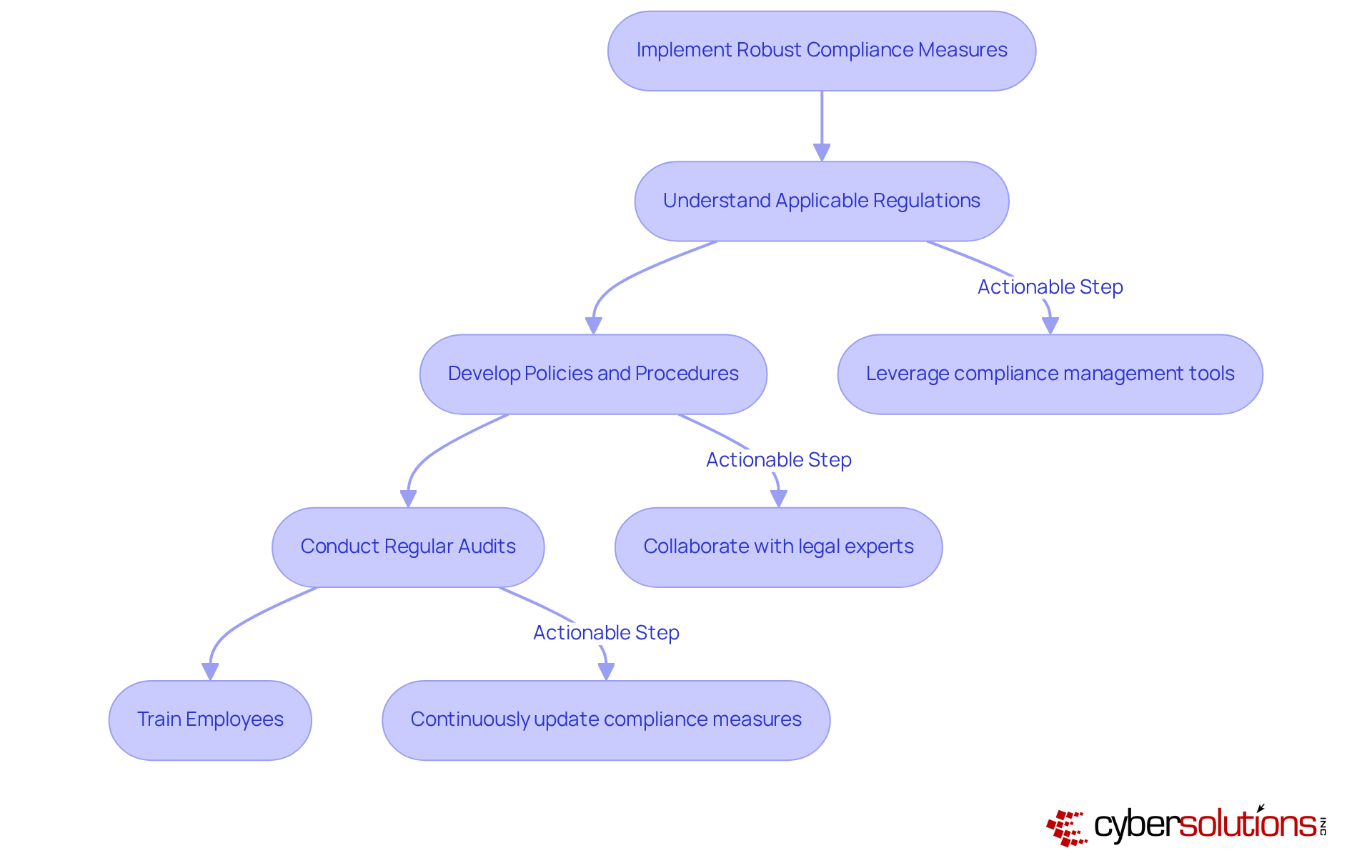
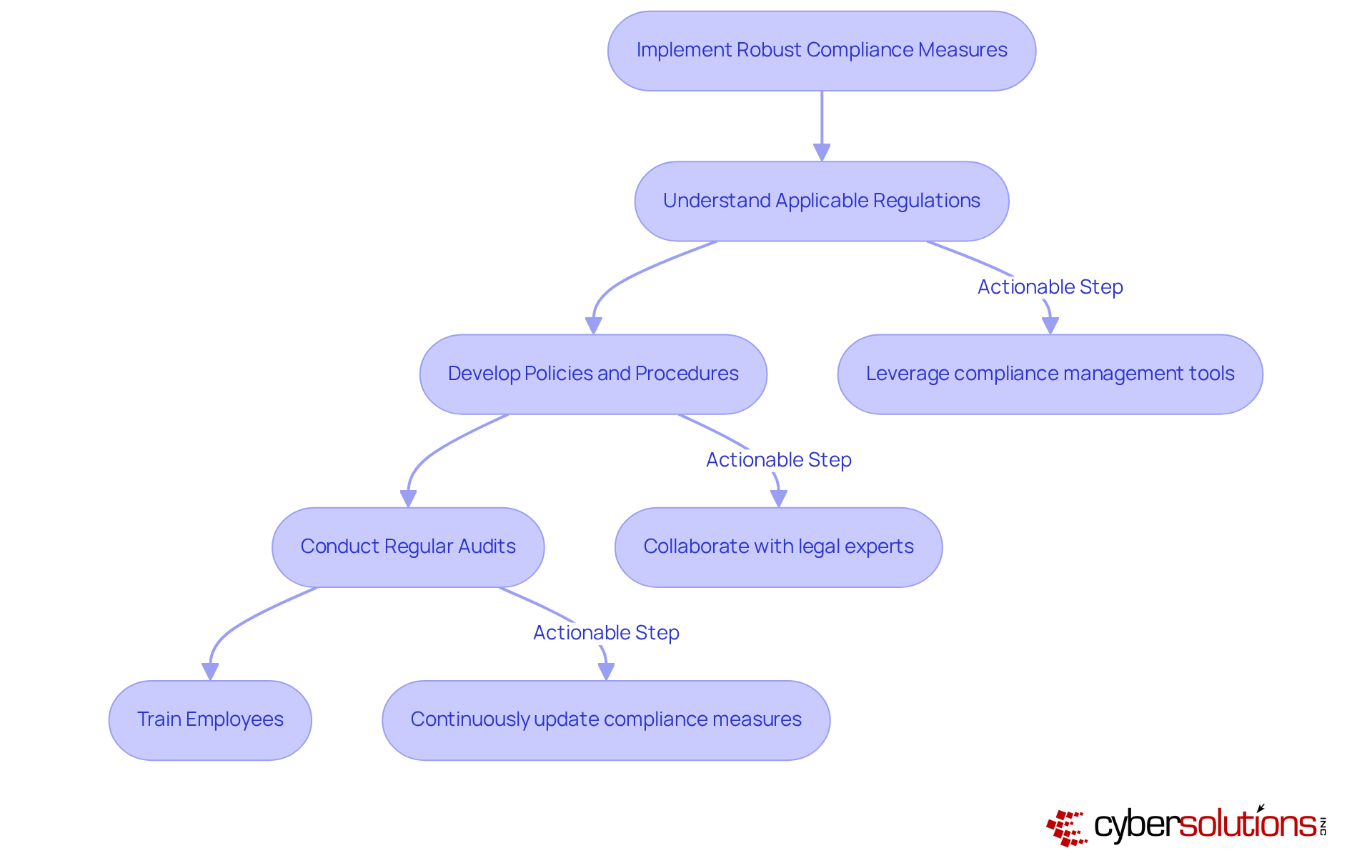
In an era where healthcare data breaches are on the rise, robust compliance measures are not just necessary; they are critical for safeguarding sensitive information and maintaining trust. Organizations must implement key compliance frameworks such as GDPR, HIPAA, and PCI-DSS to ensure they meet regulatory requirements and protect their data.
To effectively navigate compliance, organizations must:
- Understand Applicable Regulations: Identify which regulations apply to your organization based on industry and data types.
- Develop Policies and Procedures: Create comprehensive policies that outline security practices and compliance protocols, leveraging Cyber Solutions' Compliance as a Service (CaaS) to streamline this process.
- Conduct Regular Audits: Schedule audits to assess compliance with established policies and identify areas for improvement, utilizing our ongoing compliance monitoring services.
- Train Employees: Ensure that all staff are aware of compliance requirements and their roles in maintaining security.
Actionable Steps:
- Leverage compliance management tools to simplify reporting and documentation, backed by Cyber Solutions' comprehensive risk assessments.
- Collaborate with legal experts to navigate complex regulations effectively.
- Continuously update compliance measures to align with evolving laws and industry standards, including the implementation of application allowlisting to proactively block unauthorized software execution and strengthen security posture.
By prioritizing compliance, organizations not only protect their data but also enhance their reputation and operational resilience in a challenging regulatory landscape.
Establish Continuous Monitoring and Incident Response Strategies
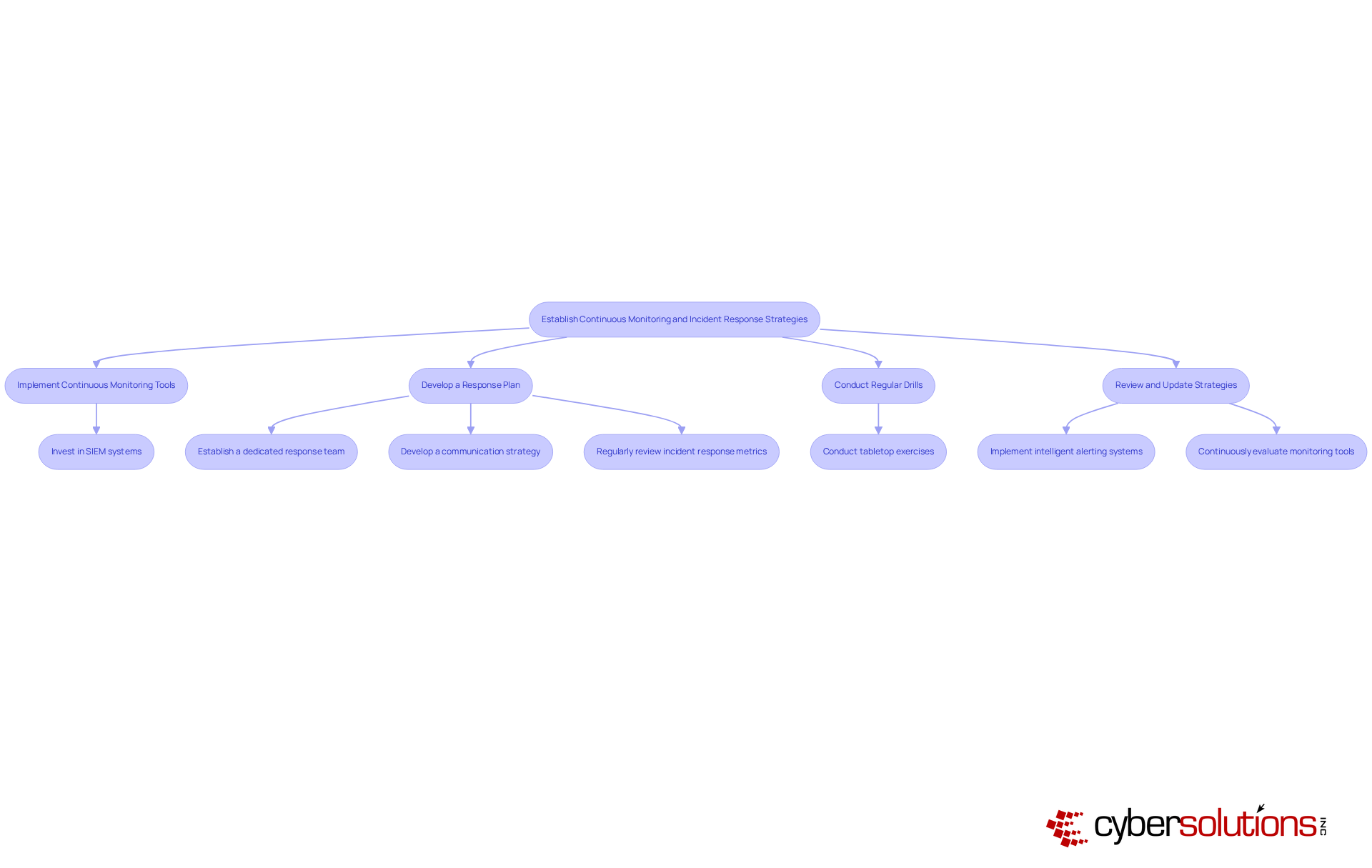
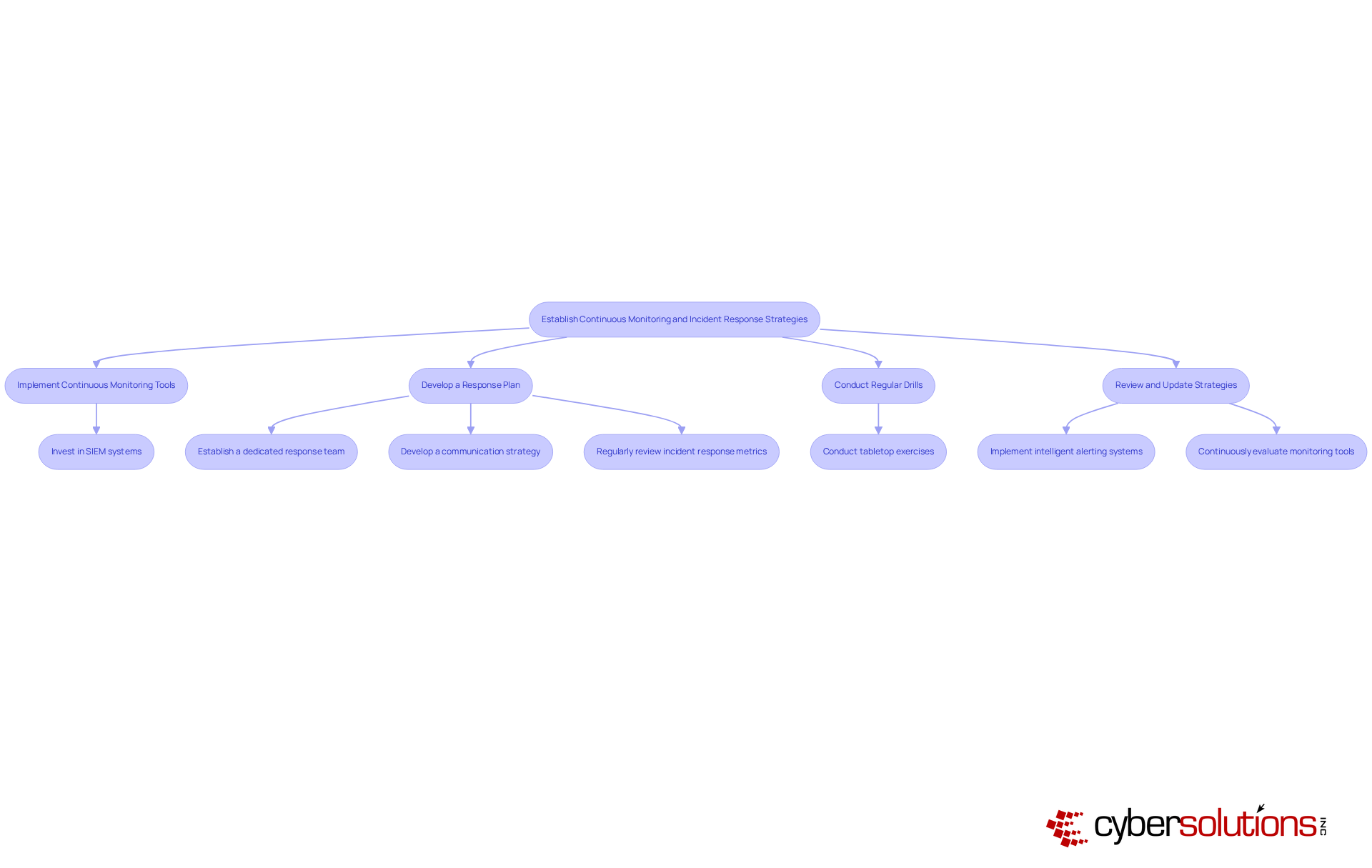
In an era where cyber threats are evolving at an unprecedented pace, the healthcare sector stands at a critical juncture, facing unique vulnerabilities that demand immediate attention. Establishing continuous monitoring and incident response strategies is essential for a robust cyber security evaluation in 2026. Organizations should focus on the following best practices:
- Implement Continuous Monitoring Tools: Utilize automated tools to observe network traffic, user behavior, and system weaknesses. With new weaknesses popping up daily, it’s crucial to stay ahead of attackers who can exploit these vulnerabilities within minutes of their discovery. Cyber Solutions provides 24/7 monitoring of your network to detect anomalies and potential vulnerabilities, ensuring that suspicious activities are identified and addressed before they escalate into threats.
- Develop a Response Plan: Create a comprehensive strategy that clearly outlines roles, responsibilities, and procedures for addressing security events. An efficient response team should consist of a Commander, a Technical Lead, a Communications Lead, and Subject Matter Experts to guarantee comprehensive oversight and expertise. Case studies reveal that a quick response can significantly mitigate damage during a cyber event, leading to effective recovery and stronger security measures.
- Conduct Regular Drills: Regularly evaluate the response plan through simulations to ensure preparedness and identify gaps. Tabletop exercises should include realistic scenarios, such as ransomware attacks and supply chain breaches, to prepare teams for high-probability situations. This proactive approach is vital for enhancing cybersecurity readiness and involves a comprehensive cyber security evaluation to ensure teams are equipped to handle potential threats with confidence.
- Review and Update Strategies: Continuously evaluate monitoring tools and response protocols to adjust to changing dangers. Organizations should implement intelligent alerting systems that prioritize alerts based on real business impacts, reducing noise and ensuring critical issues are addressed promptly. Cyber Solutions' cutting-edge attack intelligence can assist organizations in safeguarding against ransomware, phishing, and other malware incidents, adjusting security measures as business operations grow.
Actionable Steps:
- Invest in Security Information and Event Management (SIEM) systems for real-time threat detection, as these tools can significantly enhance incident management effectiveness.
- Establish a dedicated response team trained to manage various types of cyber events, ensuring that team members are familiar with defined runbooks and escalation procedures.
- Develop a communication strategy to inform stakeholders during and after an occurrence, ensuring transparency and maintaining trust.
- Regularly review incident response metrics, such as Mean Time to Recovery (MTTR) and Mean Time to Acknowledge (MTTA), to monitor and improve response times and overall effectiveness.
Without proactive measures, healthcare organizations may find themselves not just reacting to incidents, but grappling with the fallout of preventable breaches that could compromise patient safety and trust.
Conclusion
In an era where cyber threats are increasingly sophisticated, organizations must take decisive action to safeguard their digital assets. To effectively navigate the complexities of cybersecurity evaluation, organizations need to take a proactive and comprehensive approach. This involves:
- Understanding the current cyber threat landscape
- Conducting thorough risk assessments
- Implementing robust compliance measures
- Establishing continuous monitoring and incident response strategies
When organizations adopt these best practices, they can greatly improve their security and better withstand evolving threats.
Key insights from the article emphasize the importance of:
- Staying informed about emerging risks
- Regularly assessing vulnerabilities
- Ensuring compliance with relevant regulations
Organizations are encouraged to develop tailored strategies that address their unique challenges, engage with cybersecurity experts, and prioritize continuous improvement through regular evaluations and updates. The actionable steps outlined provide a clear roadmap for organizations aiming to bolster their cyber defenses.
The importance of a strong cybersecurity evaluation is clear and pressing. As cyber threats continue to evolve, many organizations struggle to keep pace with the rapid evolution of these threats, often feeling overwhelmed by the complexity of compliance and risk management. By prioritizing these best practices, organizations not only protect sensitive data and maintain stakeholder trust but also position themselves as leaders in a secure digital landscape. By taking action now, organizations can ensure a safer future in cybersecurity.
Frequently Asked Questions
What is the current state of cyber threats in the healthcare sector?
The healthcare sector is facing unprecedented challenges in safeguarding sensitive data due to a growing cyber threat landscape, including risks like ransomware, phishing attacks, and insider threats.
How can organizations assess their cyber risk landscape?
Organizations can assess their cyber risk landscape by recognizing common risks, conducting regular evaluations, and utilizing resources such as the 2026 Global Threat Report to understand emerging risks and trends.
Why is ongoing surveillance important for organizations?
Ongoing surveillance allows organizations to catch questionable actions early, preventing them from escalating into serious threats and helping to safeguard against various cyber challenges.
What resources can organizations use to stay informed about cyber threats?
Organizations should regularly assess security intelligence reports and collaborate with cybersecurity companies like Cyber Solutions to stay informed about the latest attack vectors.
What actionable steps can organizations take to improve their cybersecurity?
Organizations can take several steps, including subscribing to risk intelligence feeds, conducting quarterly assessments, interacting with cybersecurity specialists, creating a danger model specific to their challenges, and implementing 24/7 surveillance.
How can proactive measures benefit organizations in the healthcare sector?
By taking proactive measures, organizations can protect their assets and ensure the trust of their patients and stakeholders in an increasingly digital world.
List of Sources
- Assess the Current Cyber Threat Landscape
- Navigating the Cyber Threat Landscape: 2026 Outlook and Emerging Risks (https://panorays.com/blog/cyber-threat-landscape-2026-emerging-risks)
- 2026 Global Threat Report | Latest Cybersecurity Trends & Insights | CrowdStrike (https://crowdstrike.com/en-us/global-threat-report)
- 2026 Cyber Threat Assessment | NJCCIC (https://cyber.nj.gov/threat-landscape/2026-cyber-threat-assessment)
- Huntress 2026 Cyber Threat Report | Huntress (https://huntress.com/resources/2026-cyber-threat-report)
- Conduct Comprehensive Risk Assessments
- Navigating the Cyber Threat Landscape: 2026 Outlook and Emerging Risks (https://panorays.com/blog/cyber-threat-landscape-2026-emerging-risks)
- Why and How to Perform Cybersecurity Risk Assessments in 2026 (https://maddevs.io/blog/how-to-perform-cybersecurity-risk-assessments)
- 50+ Risk Management Statistics to Know in 2026 (https://secureframe.com/blog/risk-management-statistics)
- The Top Cybersecurity Threats in 2026 & How to Prevent Them | Prime Secured (https://primesecured.com/top-cybersecurity-threats-2026-and-prevention)
- Implement Robust Compliance Measures
- New HIPAA Regulations in 2026 (https://hipaajournal.com/new-hipaa-regulations)
- Cloud Compliance Testing 2026: HIPAA, GDPR, SOC 2, PCI-DSS (https://vervali.com/blog/cloud-testing-services-security-compliance-requirements-2026-guide-for-hipaa-gdpr-soc-2-pci-dss)
- HIPAA Security Rule 2026: New Gaps & Compliance Risks You Can’t Ignore (https://accorian.com/hipaa-security-rule-2026-this-is-going-to-expose-some-gaps)
- Data Security Compliance: All You Need to Know in 2026 (https://snowflake.com/en/fundamentals/data-security-compliance)
- HIPAA, SOC 2, and GDPR in 2026: The SaaS Security and Backup Checklist for Multi-Cloud Compliance Teams | Spin.AI (https://spin.ai/blog/saas-security-backup-checklist-hipaa-soc2-gdpr)
- Establish Continuous Monitoring and Incident Response Strategies
- Cyber Incident Response Playbook Examples for 2026 (https://cm-alliance.com/cybersecurity-blog/cyber-incident-response-playbook-examples-for-2026)
- 10 Incident Response Best Practices for 2026 (https://taskcallapp.com/blog/incident-response-best-practices)
- CISO Survey 2026: The State of Incident Response Readiness (https://sygnia.co/ciso-survey-2026)
- Incident Response in 2026: A Complete Enterprise Guide (https://uscsinstitute.org/cybersecurity-insights/resources/incident-response-in-2026-a-complete-enterprise-guide)