
In an increasingly complex digital landscape, small businesses encounter unique challenges that necessitate robust and tailored IT solutions. Managed IT services have emerged as a critical lifeline, providing not only enhanced cybersecurity but also operational efficiency that enables these enterprises to thrive. As organizations grapple with the pressing need for advanced technology and expert support, one pivotal question arises: how can small businesses effectively leverage managed IT services to secure their future and drive growth in a competitive market? This article delves into ten essential managed IT services that can empower small businesses, ensuring they remain agile and resilient in the face of evolving threats and challenges.
Tech Services Inc. stands at the forefront of delivering tailored solutions that specifically address the unique requirements of small enterprises. In an era where cybersecurity is paramount, Cyber Solutions recognizes the distinct challenges these organizations encounter, offering a range of services such as:
This strategic approach empowers small enterprises to focus on their core operations while we expertly manage their IT needs.
Current trends reveal a significant shift toward managed IT services among small enterprises, driven by an imperative for operational efficiency. As organizations increasingly embrace these services, they reap the benefits of improved productivity, reduced downtime, and access to advanced technology—all without the burden of maintaining in-house expertise.
Industry leaders emphasize the necessity of managed IT services, asserting that such services are no longer a luxury but an essential component for startups striving to succeed in a competitive landscape. By partnering with Tech Services, small enterprises can leverage enterprise-grade IT functionalities, ensuring they remain agile and secure in a rapidly evolving digital environment. Our pricing model simplifies budgeting, eliminating unexpected IT expenses and providing financial predictability.
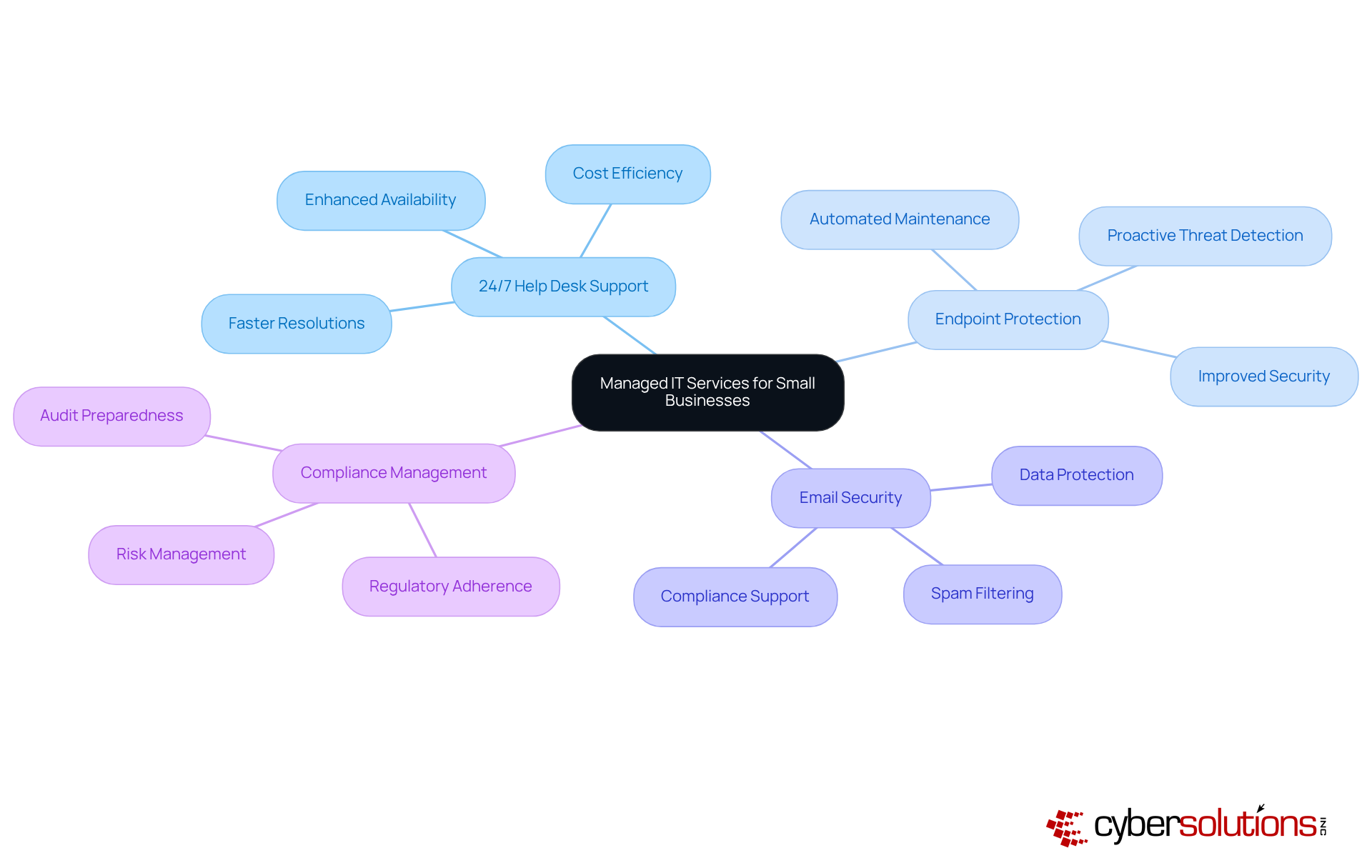
In today's fast-paced digital landscape, Cyber Solutions stands out by offering help desk support, which include services to enable minor enterprises to swiftly address and resolve issues. This constant availability allows employees to focus on their core responsibilities, free from the distractions of technical problems, ultimately enhancing overall productivity. Furthermore, the support team not only tackles urgent matters but also employs proactive monitoring to identify potential problems before they escalate, ensuring seamless operational continuity.
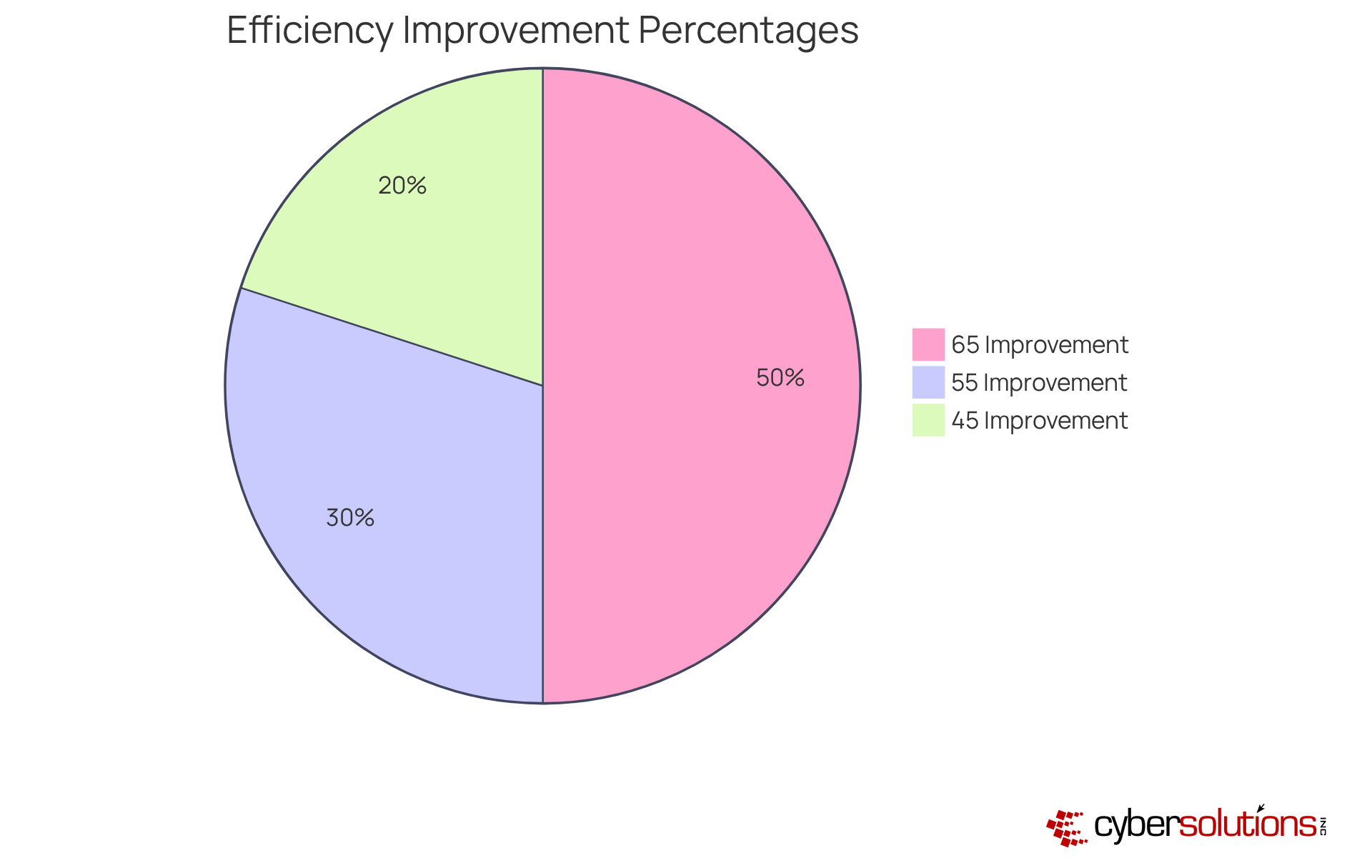
Statistics reveal that organizations leveraging help desk support experience a remarkable decrease in downtime, with many reporting improvements in efficiency ranging from 45% to 65%. By investing in help desk support, minor enterprises not only maintain a competitive edge but also enhance their operational capabilities. This strategic approach not only improves productivity but prepares businesses for future challenges, solidifying their position in an increasingly competitive market.
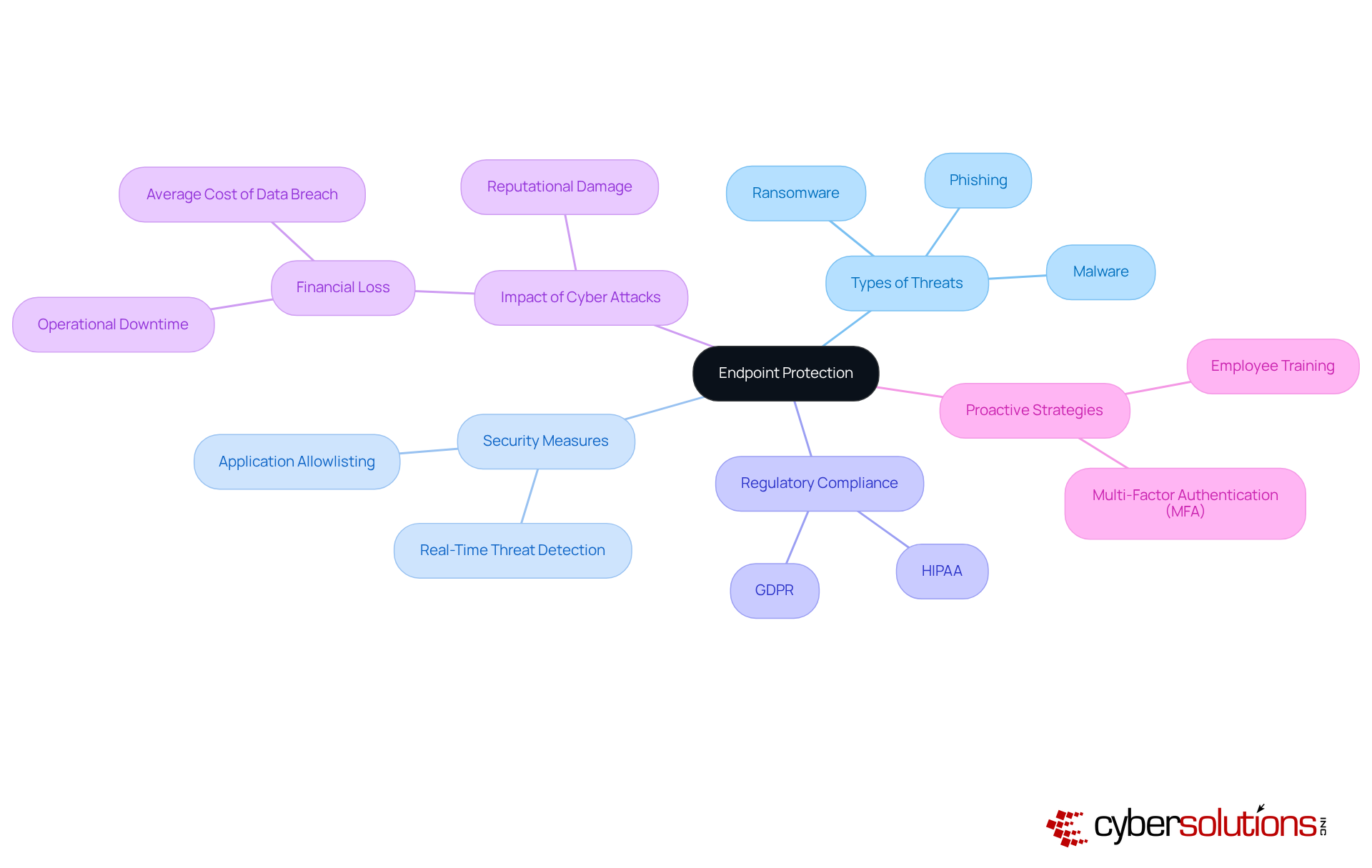
In today's digital landscape, endpoint protection is a necessity for local businesses, particularly in the healthcare sector. Endpoint protection serves as a critical service that shields organizations from a myriad of online threats, including malware, ransomware, and phishing attacks. By implementing security measures, such as application allowlisting, which proactively prevents unauthorized software from executing, companies can significantly enhance their endpoint security and minimize vulnerabilities.
Moreover, security solutions are vital for safeguarding sensitive data while ensuring compliance. This proactive approach not only mitigates risks but also bolsters the overall security posture of smaller organizations. Ultimately, this strategy maximizes return on investment (ROI) through effective risk management, addressing the unique challenges faced by CFOs in the healthcare industry. Are you prepared to protect your organization from cyber threats?
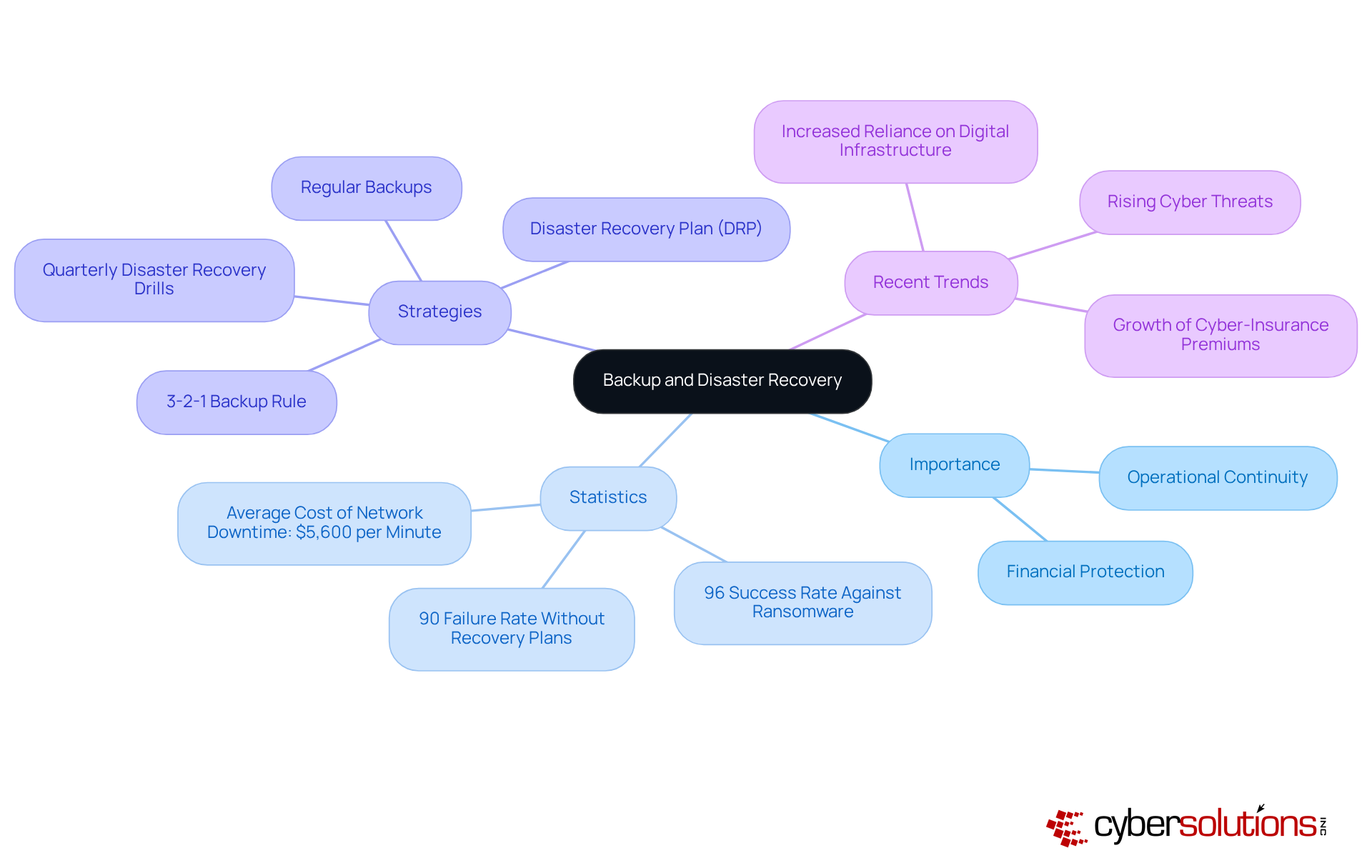
In today's digital landscape, Cyber Solutions offers indispensable services, crucial for ensuring business continuity. When faced with data loss, hardware failures, or natural disasters, these services empower entrepreneurs to swiftly recover and resume operations.
Regular backups, combined with a well-defined recovery plan, can significantly reduce downtime and protect financial investments. Notably, 90% of companies without a recovery plan fail within a year following a major incident, underlining the critical need for disaster recovery solutions.
Moreover, organizations with a backup and disaster recovery strategy boast a 96% success rate in surviving ransomware attacks, demonstrating the effectiveness of these solutions. As industry leaders assert, a robust disaster recovery plan is not merely an option; it is a necessity for ensuring operational resilience.
Recent incidents in 2025 have highlighted the escalating threats faced by local enterprises, making it imperative to prioritize cybersecurity measures. By implementing comprehensive backup solutions, organizations can maintain operations and protect their reputation in an increasingly digital world.
Cyber Solutions offers co-managed IT support, empowering local enterprises to augment their teams with additional resources and specialized expertise. This not only enables organizations to tackle challenges effectively but also allows their internal staff to focus on core activities.
By strategically allocating responsibilities, organizations can reduce costs and achieve significant savings—often ranging from 30-50% compared to hiring full-time staff—while strengthening their overall IT capabilities. As highlighted by industry experts, this partnership cultivates a culture of continuous improvement, ensuring that internal teams feel supported rather than overwhelmed.
For example, small enterprises that have adopted co-managed IT support report improved project delivery timelines and fortified security measures, illustrating the tangible benefits of this strategic approach.

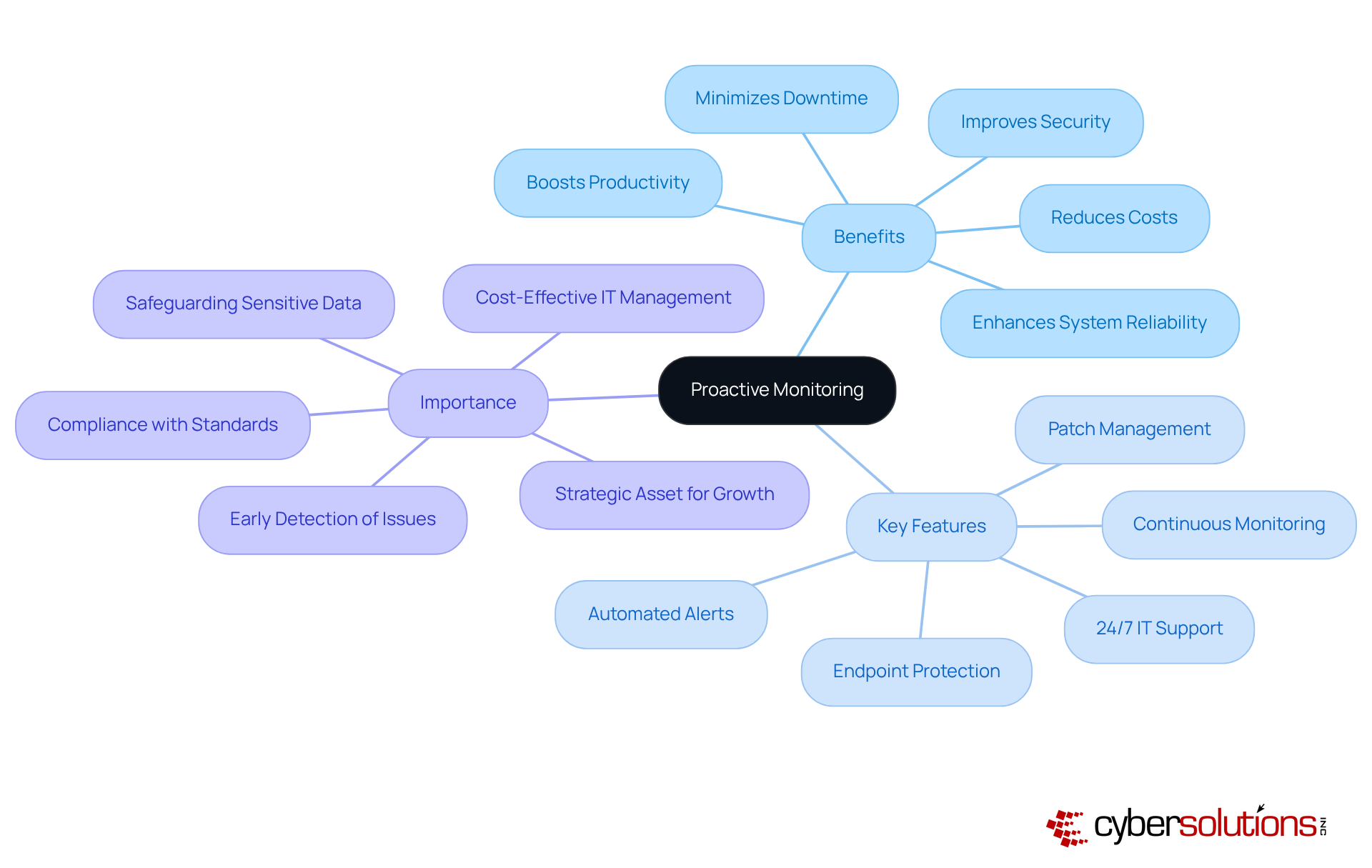
Proactive monitoring serves as a cornerstone of IT services near me, enabling small enterprises to identify and resolve IT issues before they escalate into crises. By implementing continuous monitoring of systems and networks, Cyber Solutions adeptly detects anomalies and potential threats, facilitating timely interventions. This proactive strategy not only enhances system reliability but also mitigates the risk of downtime, which can drain 11% of annual revenues from large companies. In fact, proactive monitoring can lead to an impressive 98% reduction in system outages, allowing organizations to focus on growth rather than firefighting IT crises. As IT security experts emphasize, early detection is crucial; addressing issues promptly can prevent minor glitches from evolving into major disruptions.
Small enterprises that utilize proactive monitoring near me not only enhance their operational efficiency but also cultivate a secure environment, ensuring compliance with cybersecurity standards and safeguarding sensitive data. This approach is particularly vital for organizations managing federal data, as it aligns with the essential compliance standards necessary for maintaining government contract eligibility. Key features of Cyber Solutions' proactive monitoring include:
All designed to bolster security and operational continuity. Additionally, case studies illustrate how proactive monitoring has successfully minimized disruptions for clients, reinforcing its value.
Ultimately, investing in proactive monitoring transforms technology from a reactive cost into a strategic asset, driving organizational success. Consider implementing a proactive monitoring solution to shield your organization against potential disruptions.
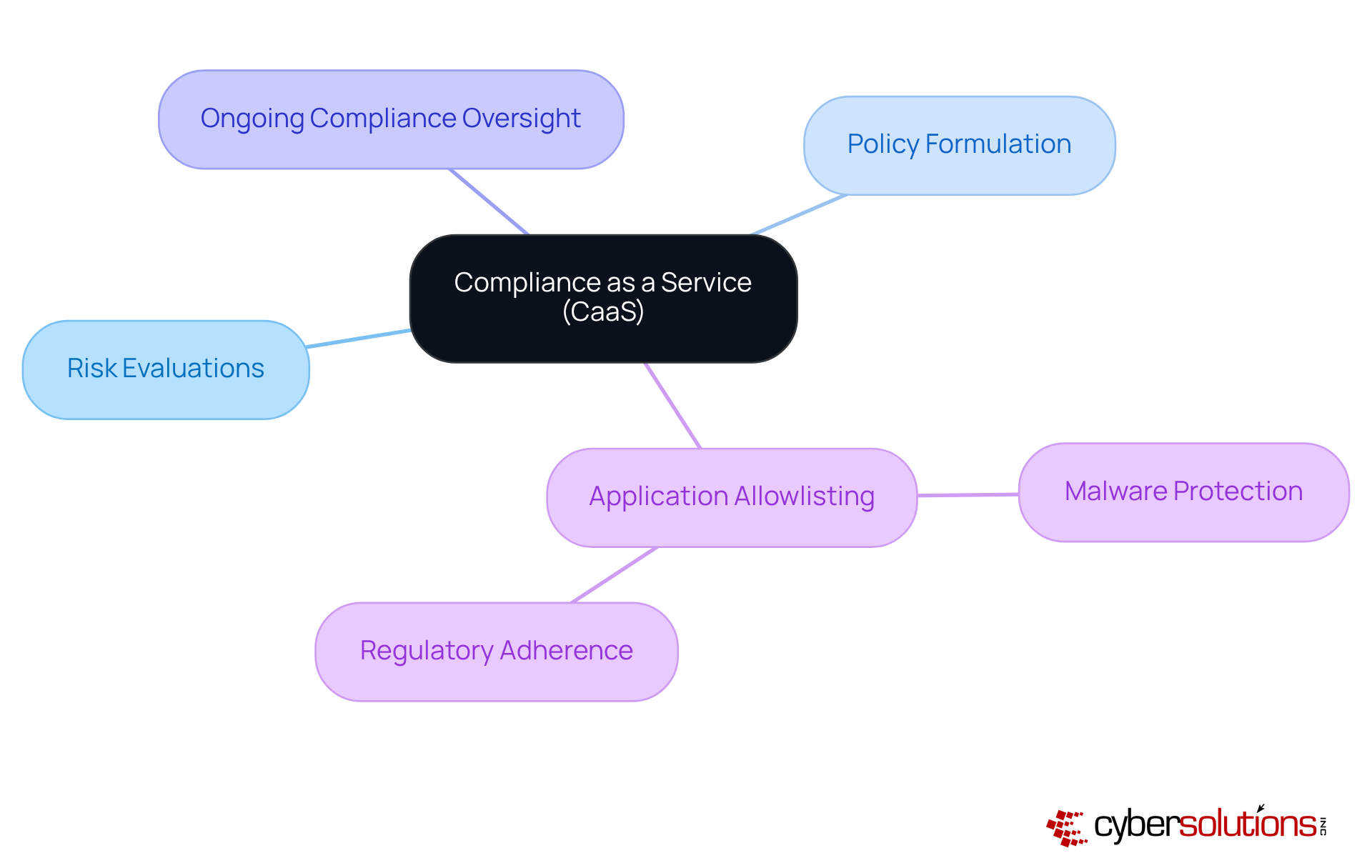
Cyber Solutions provides compliance as a service, an essential resource for minor enterprises navigating the intricate landscape of regulations. As regulations become increasingly complex in 2025—featuring updates to HIPAA, PCI DSS, and GDPR—organizations face intensified scrutiny and potential penalties for non-compliance. Indeed, statistics reveal that over 60% of minor enterprise owners struggle to keep pace with these evolving regulations, underscoring the necessity for compliance management.
Utilizing CaaS, which includes regulatory guidance, organizations can effectively outsource their compliance management. This strategic approach allows them to focus on core business activities while significantly mitigating the risk of legal penalties and reputational damage. For example, small enterprises that have embraced CaaS report enhanced compliance outcomes and improved operational efficiency, showcasing the service's effectiveness in meeting industry standards.
In addition to CaaS, Cyber Solutions highlights the critical role of endpoint protection as a cybersecurity measure. Recognized as the gold standard in cybersecurity, endpoint protection prevents unauthorized software from executing, thereby reducing the attack surface and minimizing vulnerabilities. This method not only safeguards against malware and ransomware but also assists organizations in meeting stringent compliance requirements, ensuring adherence to data protection protocols.
Experts in regulatory compliance assert that navigating these industry standards is no longer optional; it is a necessity. As compliance increasingly intertwines with operational strategy, CaaS emerges as a transformative solution, enabling organizations to uphold compliance without the burden of in-house expertise. This proactive approach not only mitigates risks but also cultivates trust and credibility with customers—an essential element for long-term success in today’s competitive landscape.
Moreover, the consequences of non-compliance can be devastating, with penalties potentially crippling minor enterprises. By adopting CaaS and implementing best practices alongside technology solutions, organizations can avoid these pitfalls and ensure they remain compliant, thereby protecting their future in an ever-evolving regulatory environment.
In today's dynamic business environment, pricing models are crucial for minor enterprises. Cyber Solutions provides services that significantly enhance budgeting capabilities, allowing organizations to avoid unexpected costs and manage IT expenditures more effectively. By implementing a consistent monthly fee structure, our services cover everything from email licenses to software updates, providing a comprehensive solution that instills peace of mind. This transparency not only facilitates better financial planning but also ensures that minor enterprises receive support for small business near me, without the burden of financial stress.
Financial experts emphasize the necessity of reliable pricing models for minor enterprises, as they provide a clear framework for budgeting. For example, a modest enterprise that utilizes managed IT services can confidently forecast its annual IT budget, knowing that expenses will remain stable despite fluctuations in usage. This approach empowers companies to focus on growth and operational efficiency, rather than being hindered by unpredictable costs.
Furthermore, testimonials from local entrepreneurs reveal that adopting managed IT services has led to improved efficiency and strategic resource distribution. This underscores the importance of stability in today’s competitive landscape. As organizations navigate the complexities of IT management, Cyber Solutions stands ready to deliver the stability and support that they need through managed IT services to thrive.
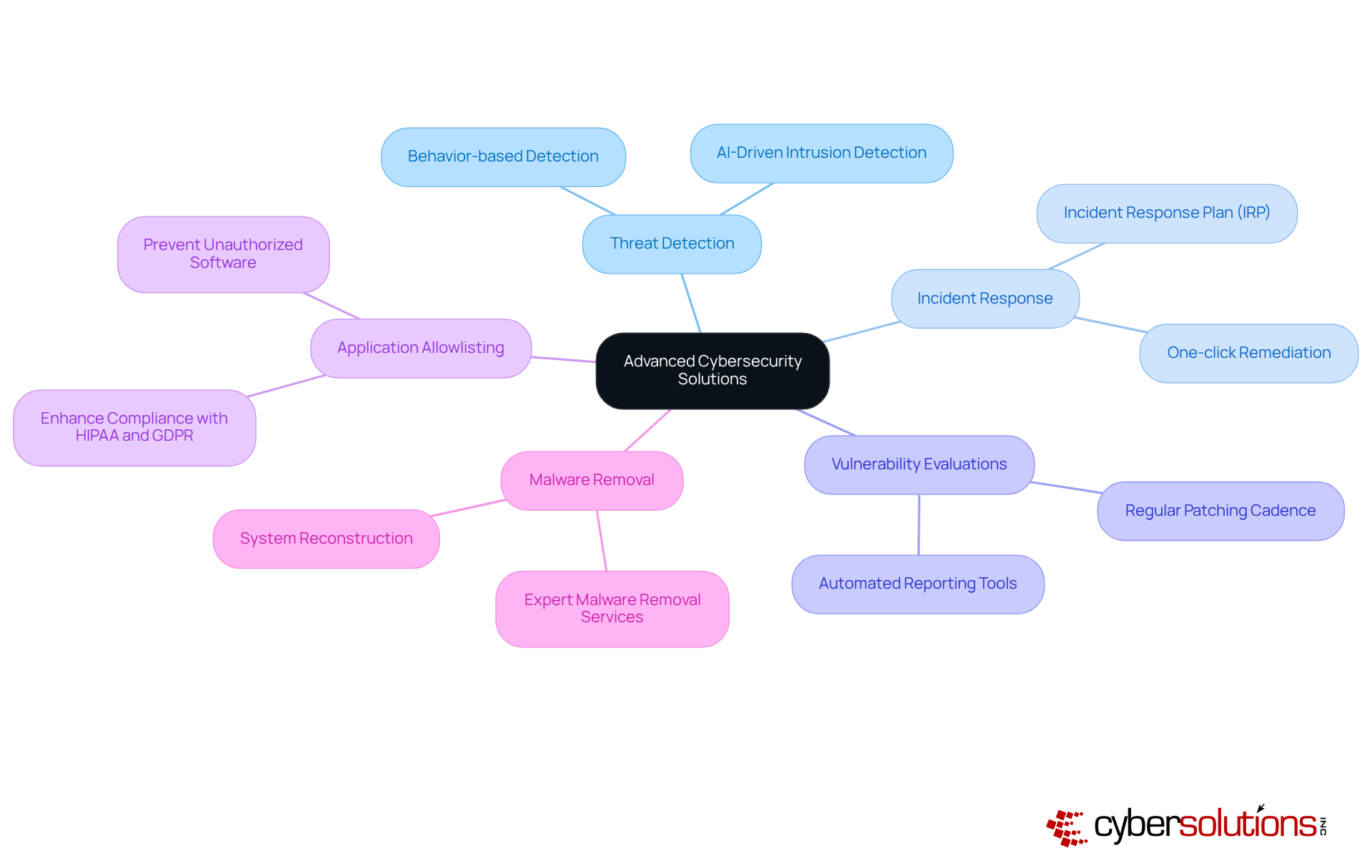
In today's digital landscape, cybersecurity is paramount, especially in healthcare. This company provides services designed to protect against emerging threats, ensuring that small enterprises can effectively defend against cyberattacks. Our comprehensive solutions include firewalls, intrusion detection systems, and encryption, which are crucial for maintaining the integrity of healthcare data.
One of the cornerstones of our approach is endpoint protection. This proactive measure prevents unauthorized software from executing, significantly reducing vulnerabilities and enhancing compliance with essential standards such as HIPAA. By implementing these advanced strategies, organizations can fortify their defenses and ensure that critical information remains secure.
Additionally, our data recovery and system reconstruction services guarantee that systems are meticulously cleaned, patched, and optimized. This reinforces security protocols, which is vital in maintaining customer trust. As the threats to cybersecurity continue to evolve, organizations must take decisive action to protect their sensitive information and uphold their reputation in an increasingly digital world.
Managed IT services from a technology provider significantly enhance operational efficiency by streamlining IT processes and reducing the workload on internal teams. This strategic partnership not only fosters efficiency but also generates cost savings, enabling organizations to allocate resources more effectively.
By utilizing managed IT services, minor enterprises can improve their IT infrastructure for small business near me and focus on growth initiatives. As highlighted by ALI DHOON, CEO OF CORE TECHNOLOGIES SERVICES, "The way IT is managed directly impacts an organization's agility, risk, and productivity," making it essential for emerging enterprises to embrace these services.
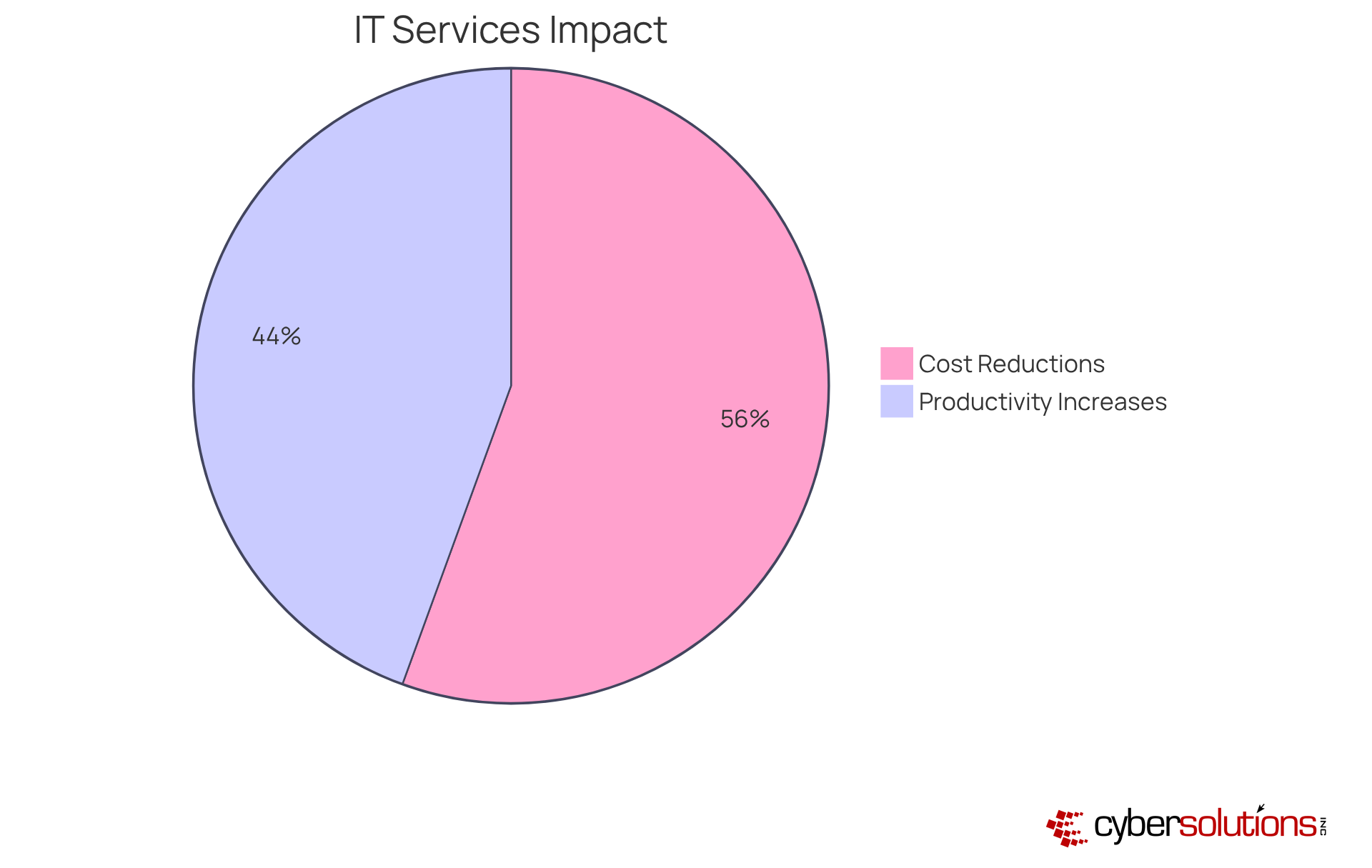
Organizations that utilize managed IT services near me can achieve IT cost reductions of 20-30% and increased productivity by 15-25%. Such enhancements empower small enterprises to tackle challenges, including cybersecurity threats, while capitalizing on growth opportunities with managed IT services near me, ultimately driving success.
A comprehensive cybersecurity strategy employs a layered approach that includes:
This approach ensures that businesses are not only protected but also positioned for sustainable growth.
Embracing managed IT services is crucial for small businesses striving to excel in a competitive environment. These services not only relieve the burden of IT management but also empower organizations to concentrate on their core operations while ensuring robust security and operational efficiency. By partnering with providers like Cyber Solutions, small enterprises can access a comprehensive suite of tailored services designed to meet their unique needs.
The article delineates various critical components of managed IT services, including:
Each of these elements plays a vital role in enhancing operational resilience, mitigating risks, and ensuring compliance with regulatory standards. The significance of predictable pricing models further underscores the necessity for small businesses to manage their IT budgets effectively, enabling them to allocate resources strategically and avoid unexpected costs.
Ultimately, investing in managed IT services transcends merely addressing immediate IT needs; it is a strategic initiative that can propel sustained growth and operational efficiency. As small businesses navigate the complexities of today's digital landscape, leveraging these services will be essential in safeguarding sensitive data, enhancing productivity, and positioning themselves for future success. The time to act is now—embracing managed IT solutions can transform technology from a reactive cost into a strategic asset, paving the way for long-term success and stability.
What services does Cyber Solutions Inc. offer to small businesses?
Cyber Solutions Inc. offers a suite of tailored managed IT services that includes 24/7 help desk support, endpoint protection, email security, and compliance management.
How does Cyber Solutions Inc. help small businesses with their IT needs?
Cyber Solutions Inc. helps small businesses by managing their IT needs, allowing them to focus on their core operations. This includes providing continuous support and addressing cybersecurity challenges.
Why are small businesses increasingly adopting managed IT services?
Small businesses are adopting managed IT services to enhance security and operational efficiency, improve risk management, reduce downtime, and access advanced technology without the need for in-house expertise.
What are the benefits of 24/7 help desk support for small businesses?
24/7 help desk support helps small businesses swiftly address IT challenges, reduce operational interruptions, and enhance overall productivity. It also includes proactive monitoring to identify potential issues before they escalate.
What impact does 24/7 IT support have on operational efficiency?
Organizations that leverage 24/7 IT support experience a significant decrease in downtime, with improvements in operational efficiency ranging from 45% to 65%.
What is endpoint protection and why is it important for small businesses?
Endpoint protection is a cybersecurity service that safeguards organizations from online threats like malware, ransomware, and phishing attacks. It is important for small businesses to enhance their security posture and comply with regulatory standards.
How does Cyber Solutions Inc. ensure compliance with regulatory standards?
Cyber Solutions Inc. implements robust security measures, including real-time threat detection and response capabilities, to safeguard sensitive data and ensure compliance with regulations such as HIPAA and GDPR.
What pricing model does Cyber Solutions Inc. use for its services?
Cyber Solutions Inc. employs a flat-rate pricing model, which simplifies budgeting, eliminates unexpected IT expenses, and provides peace of mind for small businesses.