
In today's world, digital threats are more prominent than ever, placing C-suite leaders at the forefront of a complex landscape that requires both strategic foresight and operational agility. This article delves into ten essential practices for managed services providers, designed to empower executives in enhancing cybersecurity, nurturing robust client relationships, and driving operational efficiency. As organizations strive to implement these strategies, they often face a pressing question: How can leaders effectively balance innovation with compliance in a swiftly changing market?
Discover insights that can transform these challenges into opportunities for growth and stability. By understanding the current cybersecurity landscape, healthcare organizations can better navigate the unique challenges they encounter. Cyber Solutions stand ready to address these issues effectively, ensuring that leaders are equipped to thrive in this dynamic environment.
In today's digital landscape, cybersecurity is not just an IT issue; it's a critical concern for organizations. With the rise in cyber threats, CFOs must navigate a complex environment where the stakes are high. Collaborating with a provider like Cyber Solutions can be a game-changer, offering tailored IT and cybersecurity services.
Cyber Solutions understands the unique challenges faced by healthcare organizations. They provide sector-specific IT support that addresses the distinct security and regulatory requirements of the industry. Their offerings include:
These solutions are designed to defend against evolving threats, ensuring that sensitive data remains protected. By leveraging these tailored services, organizations can not only enhance their security posture but also ensure compliance. This proactive approach helps mitigate risks before they escalate, allowing healthcare providers to focus on their core objectives.
Ultimately, partnering with Cyber Solutions empowers healthcare organizations to thrive in a challenging environment. Are you ready to take the next step in securing your organization’s future?

C-suite leaders must take the lead in fostering strong client relationships through consistent communication and feedback mechanisms. By executing quarterly business reviews and providing tailored updates, they keep customers informed about performance and upcoming changes. This proactive approach not only builds trust and transparency but also significantly enhances client satisfaction and loyalty - both crucial for nurturing long-term partnerships.
Consider a leading managed services provider, which exemplifies this strategy by prioritizing client needs and continuously refining its offerings based on customer feedback. Such practices not only fortify relationships but also meet the rising demand for personalized services. By adopting these strategies, businesses can adeptly navigate the complexities of client engagement in the IT sector, ultimately leading to improved outcomes and bolstered client retention.

C-suite leaders must take the lead in adopting proactive security measures, such as regular assessments and planning. Why is this crucial? Because investing in cybersecurity solutions, like those offered by Cyber Solutions, allows organizations to identify potential threats before they escalate into significant breaches. For instance, regular assessments can reduce risk by up to 48%, according to industry research. This statistic underscores their financial impact.
Cyber Solutions provides monitoring and threat detection solutions that continuously monitor for suspicious activity, ensuring client data is safeguarded against evolving threats. Organizations that implement these measures not only enhance their security posture but also build greater trust with customers, demonstrating a commitment to protecting sensitive information. As cybersecurity experts emphasize, "Vulnerability assessments stand as one of the pillars of a robust security strategy," highlighting their essential role in identifying and mitigating security weaknesses.
Furthermore, with increasing cyber threats, these assessments are crucial for navigating the complexities of modern business environments. By prioritizing these proactive strategies, healthcare organizations can effectively address the unique challenges they face in today's digital landscape.

In today’s digital landscape, the importance of cybersecurity cannot be overstated. C-suite leaders must prioritize continuous monitoring and maintenance within their organizations to safeguard against ever-evolving threats. This includes:
For example, Cyber Solutions exemplifies this commitment by offering services that enable real-time issue detection and resolution. This proactive approach significantly improves response times and enhances overall service reliability.
Regular updates not only boost system performance but also strengthen defenses against emerging cyber threats, ensuring data integrity. Organizations that embrace these practices can effectively mitigate risks associated with outages. Consider this: 31% of corporate decision-makers view eight hours of downtime as catastrophic. This statistic underscores the urgency of addressing potential vulnerabilities.
Moreover, monitoring of potential issues, allowing for swift responses that prevent minor disruptions from escalating into major operational setbacks. By investing in robust security measures, organizations can not only protect their assets but also foster trust among stakeholders, ultimately driving success in an increasingly competitive environment.

C-suite leaders must prioritize the integration of sustainability practices within their companies. This commitment is not just a trend; it’s essential for long-term success. By adopting green technologies, minimizing e-waste, and encouraging remote work, organizations can significantly enhance their operational efficiency. Sustainability enhances brand image and meets the rising expectations of customers and regulators.
Consider this: organizations implementing energy-efficient solutions, such as solar energy systems, can achieve reductions of up to 90% in energy consumption compared to traditional methods. Companies like Cisco exemplify this commitment by optimizing their networks for greater efficiency and sustainability. As Santeri Palomäki, Manager of Industry & Built Environment, states, "Renewable technologies are fast displacing fossil fuels - and businesses that embrace these technologies can secure resilience, attract investment, and unlock long-term growth."
Moreover, by leveraging innovative strategies, Cyber Solutions Inc. empowers businesses to reduce costs and mitigate environmental impact. This reinforces their dedication to sustainability, demonstrating that integrating sustainability is not just beneficial but necessary for future success.

C-suite leaders must prioritize the development of recurring revenue streams to bolster financial stability. In today’s rapidly evolving landscape, establishing or adhering to subscription models is essential. These models provide customers with predictable billing, ensuring their IT needs are consistently met. For instance, Cyber Solutions exemplifies this approach by offering managed services, which not only facilitates operational efficiency but also delivers continuous IT support. This strategy not only stabilizes cash flow but also fosters client loyalty, enhancing both retention and satisfaction.
Financial specialists have observed that transitioning to a subscription-based model significantly boosts revenue growth. It cultivates a sense of collaboration and dependability in service delivery, which is crucial in the current climate. With subscription services emerging as the backbone of Managed Service Provider (MSP) offerings, projected to grow at 18% annually through 2026, adhering to best practices for ongoing IT support is more critical than ever. Moreover, a staggering 88% of small and midsize companies are turning to MSPs to access enterprise-level capabilities without the burden of maintaining internal IT teams. This trend underscores the importance of subscription-based options for smaller entities, making it clear that the time to act is now.

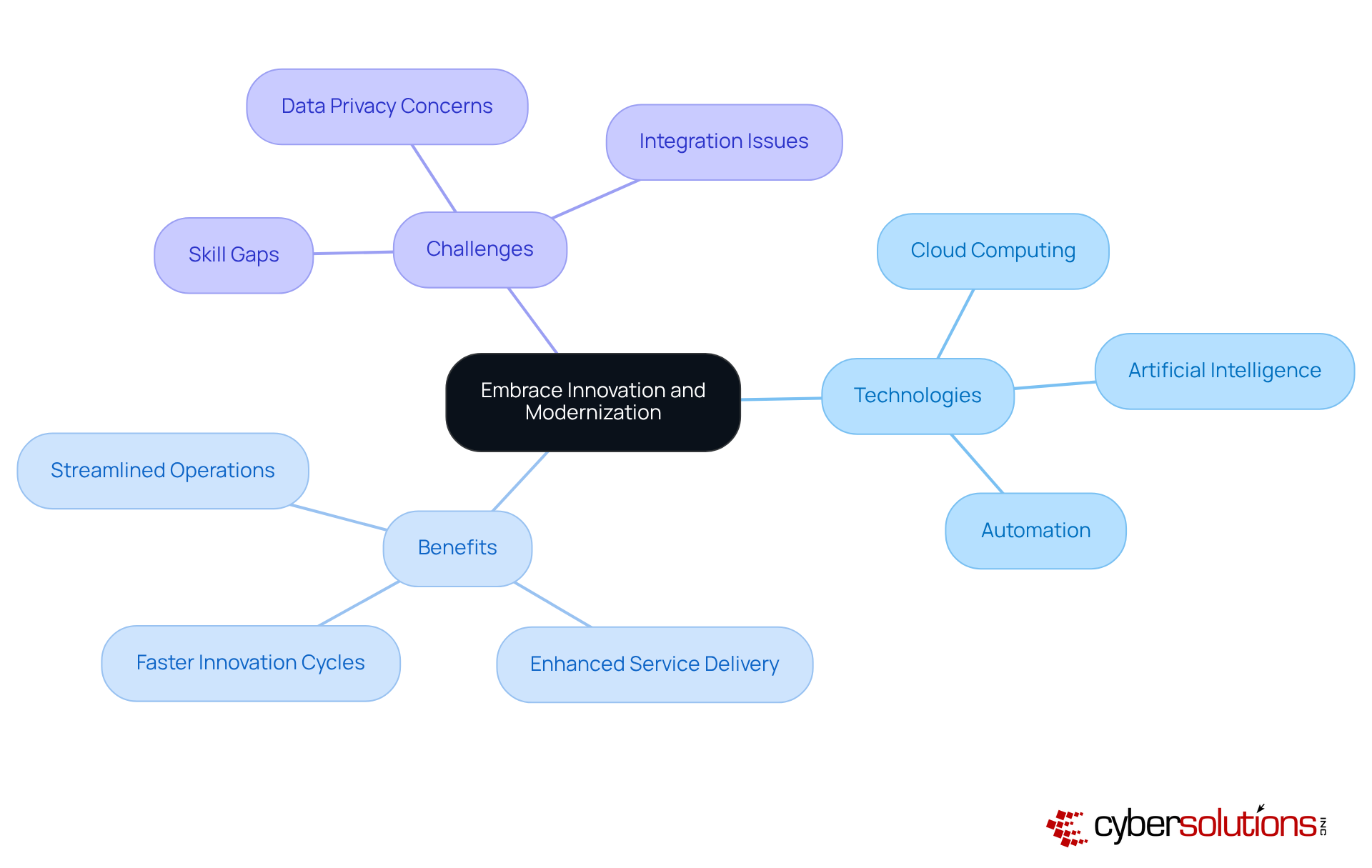
must champion the adoption of technology within their enterprises. In today’s fast-paced digital landscape, leveraging cloud computing, artificial intelligence, and automation is not just beneficial; it’s essential for streamlining operations and enhancing service delivery. Did you know that companies integrating AI into their cloud strategies report that 78 percent now utilize AI in at least one business function? This integration leads to improved efficiency, positioning organizations for success.
Cyber Solutions stands at the forefront, offering innovative solutions that empower companies to stay ahead of the curve, ensuring they remain competitive in an increasingly digital marketplace. However, the journey isn’t without its challenges. Organizations often grapple with:
when implementing these transformative technologies.
As Mike Alreend aptly states, "By enabling automation, AI in business is becoming a cornerstone of modern operations." This proactive approach not only mitigates risks but also drives growth, ensuring organizations remain agile and responsive to market demands. Embracing these technologies is not merely a choice; it’s a strategic imperative for thriving in the modern business environment.
C-suite leaders must prioritize the development of effective to enhance and ensure compliance. Why is this crucial? Clear and succinct documentation for processes, procedures, and is essential. Additionally, thorough documentation that addresses with tailored is vital for navigating today’s complex landscape.
By standardizing documentation, companies can significantly reduce errors, enhance communication, and streamline workflows. This is not just about compliance; it’s about fostering a and accountability. Cyber Solutions underscores the in its service provision, ensuring that all team members have access to current information that supports efficient operations and prepares them for compliance audits.
In a world where are ever-evolving, the implications for healthcare organizations are profound. Are your robust enough to withstand scrutiny? By addressing these challenges head-on, Cyber Solutions equips organizations with the tools they need to thrive in a demanding regulatory environment.
In today's digital age, the importance of cybersecurity cannot be overstated. With increasing threats targeting sensitive patient data, healthcare organizations face unique challenges that demand specialized solutions, focusing on specific sectors to tailor offerings that meet the distinct needs of their customers.
For instance, Cyber Solutions stands out by providing customized cybersecurity services. This approach ensures compliance, addressing the critical need for security in a highly regulated environment. By adopting such a targeted strategy, organizations not only enhance their service offerings but also position themselves as trusted partners, fostering long-term relationships.
Customizing IT services to meet industry-specific needs is crucial for healthcare providers. This focus ultimately leads to enhanced client satisfaction and loyalty. As healthcare organizations navigate the complexities of cybersecurity, they must consider how to implement effective measures and protect their most valuable asset: patient information.

C-suite leaders must recognize that strong adherence to regulations is not just a necessity but a strategic advantage in navigating today’s complex regulatory landscape. With regulations constantly evolving, staying informed and implementing essential measures is crucial for compliance.
Cyber Solutions offers compliance services, delivering comprehensive solutions that help organizations manage intricate regulatory frameworks like GDPR. By prioritizing compliance, companies can significantly reduce risk while enhancing their reputation in the marketplace. This positions them as leaders in an increasingly scrutinized business environment.
As regulations rise - particularly around data privacy and security - organizations that adopt a proactive compliance strategy will be better equipped to face challenges and seize growth opportunities. For example, regularly reviewing and updating compliance policies can dramatically enhance your organization’s readiness for audits and regulatory changes.
Are you prepared to meet these challenges head-on? Embrace a robust compliance program today and ensure your organization not only meets but exceeds expectations.

In today’s healthcare landscape, cybersecurity is not just an option; it’s a necessity. C-suite leaders must recognize the escalating threats that jeopardize patient data and organizational integrity. By prioritizing tailored cybersecurity solutions, they can not only protect their organizations but also enhance operational efficiency and client satisfaction.
The unique challenges faced by healthcare organizations demand specialized services and robust compliance strategies. Continuous monitoring and maintenance are essential to meet the evolving needs of clients, ensuring that organizations remain resilient against cyber threats. By embracing innovation and modernization, healthcare leaders can position their organizations as trusted partners in their clients' success, ultimately fostering strong relationships built on trust and accountability.
As the demand for managed services continues to rise, C-suite leaders must act decisively. Investing in proactive security measures and sustainable practices will not only safeguard their organizations but also cultivate a culture of accountability that resonates with clients. The call to action is clear: prioritize these strategies today to secure a competitive edge and ensure a resilient future for your organization.
Why is cybersecurity a critical concern for healthcare organizations?
Cybersecurity is critical for healthcare organizations due to the rise in cyber threats and the unique security and regulatory requirements of the industry. Protecting sensitive data is essential to ensure compliance and maintain trust.
What services does Cyber Solutions offer to healthcare organizations?
Cyber Solutions offers tailored IT and cybersecurity services, including 24/7 help desk support, endpoint protection, threat detection, data encryption, and secure access controls.
How do tailored cybersecurity solutions benefit healthcare organizations?
Tailored cybersecurity solutions enhance security posture, ensure compliance with regulatory standards, and help avert potential problems before they escalate, allowing healthcare providers to focus on their core objectives.
What role do C-suite leaders play in customer relationship management?
C-suite leaders are responsible for fostering strong customer relationships through consistent communication, feedback mechanisms, and conducting quarterly business evaluations (QBRs) to keep customers informed and enhance satisfaction.
How does Cyber Solutions exemplify effective customer relationship management?
Cyber Solutions prioritizes customer interaction and continuously refines its offerings based on client feedback, which fortifies relationships and meets the demand for personalized communication.
What proactive security measures should C-suite leaders adopt?
C-suite leaders should adopt proactive security measures such as regular vulnerability assessments and incident response planning to identify potential threats before they escalate into significant breaches.
What is the financial impact of regular vulnerability assessments?
Regular vulnerability assessments can cut the average cost of data breaches by up to 48%, highlighting their importance in mitigating financial risks associated with cybersecurity incidents.
How do proactive security measures build trust with customers?
Implementing proactive security measures demonstrates a commitment to protecting sensitive information, which enhances customer trust and showcases an organization's dedication to cybersecurity resilience.
Why are vulnerability assessments considered essential in cybersecurity?
Vulnerability assessments are essential as they help identify and mitigate security weaknesses, forming a pillar of a robust security posture and addressing the complexities of modern business environments.