
In an era where cybersecurity threats loom large, healthcare organizations must prioritize robust defenses to safeguard sensitive patient data. Local IT services providers play a crucial role in this endeavor, offering tailored solutions that not only meet regulatory requirements but also enhance operational efficiency. As threats to sensitive data grow more sophisticated, businesses struggle to keep pace with compliance demands. But how can businesses really tap into local IT expertise to drive growth? Without effective local IT partnerships, organizations risk falling victim to breaches and regulatory penalties.
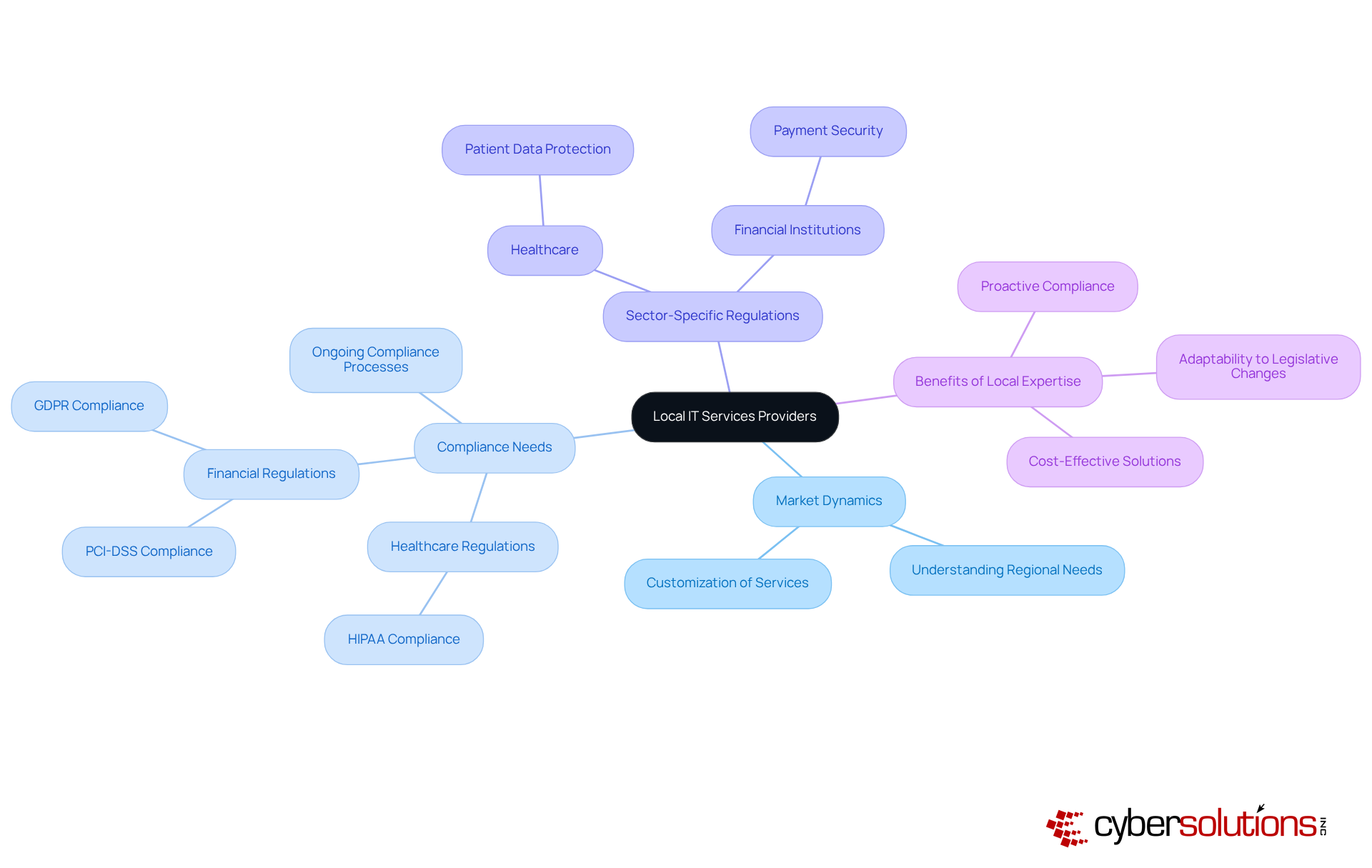
In an era where cybersecurity threats loom large, the stakes for healthcare organizations have never been higher. Local IT services providers possess a deep understanding of the market dynamics and compliance requirements specific to their regions. This localized expertise allows them to customize their services to address the distinct requirements of enterprises across various sectors.
For instance, healthcare organizations must comply with stringent regulations such as HIPAA, while financial institutions are required to adhere to PCI-DSS and GDPR standards. By collaborating with a local IT services provider, companies can ensure that their IT infrastructure is not only secure but also complies with these essential regulations.
Furthermore, local suppliers are often more adaptable in responding to legislative changes, enabling companies to remain ahead of compliance challenges and evade potential fines or legal troubles. Navigating the complex landscape of compliance can be daunting for many organizations, but a local IT services provider offers the expertise needed to ensure operational integrity and protect sensitive data.
Local IT services providers offer comprehensive solutions, including Compliance as a Service (CaaS), which simplifies the compliance process for small and medium-sized enterprises by providing access to enterprise-level expertise without the high costs of in-house staff. Proactive compliance can also reduce downtime from security or audit-related disruptions, further enhancing organizational resilience.
According to Cyber Solutions, their customized cybersecurity tools, such as endpoint protection and threat detection, are designed to assist organizations in navigating compliance with ease. This underscores how crucial regional IT expertise is for fostering compliance and resilience in today's corporate landscape. Embracing local IT support is not just a strategic advantage; it's a necessity for safeguarding your organization against evolving threats.
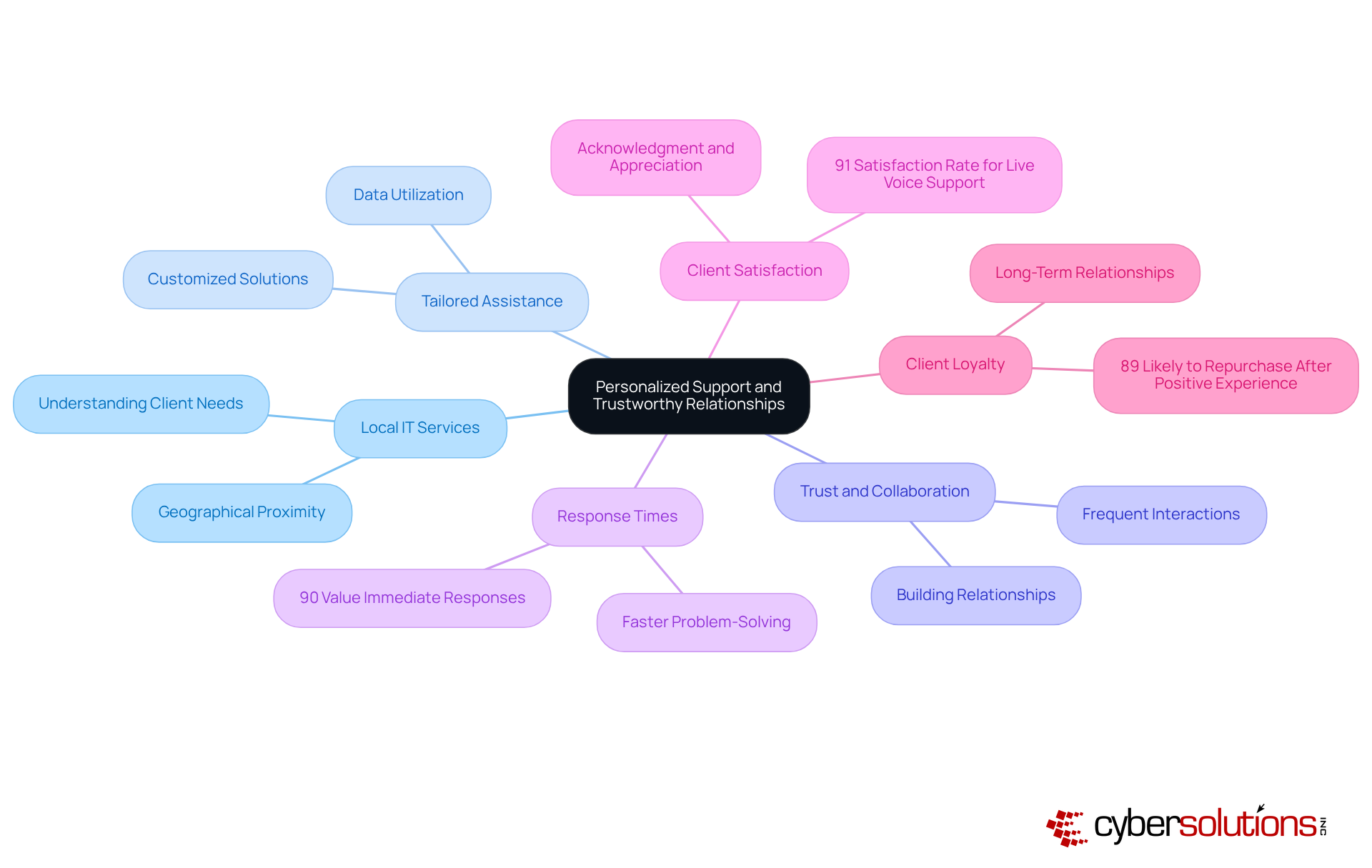
In an era where cybersecurity threats loom large, the role of local IT services provider in healthcare cannot be overstated. Collaborating with a local IT services provider presents a unique benefit in creating tailored assistance and cultivating reliable relationships. These suppliers dedicate time to thoroughly understand their clients' distinct operational processes, challenges, and objectives. This deep insight enables them to deliver tailored solutions that precisely meet the specific needs of each organization.
The geographical proximity of nearby providers facilitates more frequent face-to-face interactions, enhancing trust and collaboration. Without local IT support, organizations risk delays in addressing critical issues. As a result, companies gain from faster response times and improved problem-solving, as local IT teams are easily accessible to address issues as they occur. Consider this: 90% of customers value immediate responses in support, highlighting the critical role of timely assistance in personalized care.
This tailored approach enhances operational efficiency. It also significantly improves client satisfaction, as organizations feel acknowledged and appreciated by their IT partners. Furthermore, utilizing data to improve tailored assistance can further reinforce these connections, ensuring that local IT specialists stay aligned with their clients' changing requirements. This leads to a significant increase in client loyalty and repeat business. Ultimately, 89% of consumers are more likely to make another purchase after a positive customer assistance experience, underscoring the critical link between personalized support and company success.
In the healthcare sector, the stakes are higher than ever when it comes to cybersecurity, as breaches can jeopardize both finances and patient safety. Local IT services providers excel in enhancing operational efficiency by offering rapid response times and customized solutions. In a time when downtime can lead to significant financial losses, having a local IT services provider like Cyber Solutions ensures that technical issues are resolved quickly, minimizing interruptions to operations.
With Cyber Solutions' round-the-clock IT support, you can rest easy knowing that help is just a call away, no matter when an incident occurs. Furthermore, their capability to tailor solutions according to the specific requirements of an organization means that IT services can be aligned with operational objectives, resulting in increased productivity and improved ROI.
For example, Cyber Solutions might implement a tailored cybersecurity strategy that not only protects sensitive data but also enhances overall system performance through proactive monitoring and endpoint protection. This layered approach to IT management not only safeguards against potential threats but also empowers businesses to operate more efficiently, ultimately driving growth and success.
By partnering with Cyber Solutions, healthcare organizations can not only mitigate risks but also enhance their operational efficiency and patient trust.
In an era where cybersecurity threats are increasingly sophisticated, the role of local IT service providers has never been more critical. Local IT services play a pivotal role in ensuring the success of businesses, particularly in navigating the complexities of compliance and cybersecurity. Their localized expertise enables organizations to customize IT solutions that address specific market dynamics and regulatory needs. This approach safeguards sensitive data and enhances operational integrity.
Throughout this discussion, we’ve highlighted the importance of personalized support and the establishment of trustworthy relationships between local IT providers and businesses. By understanding unique operational challenges, local providers can deliver tailored solutions that improve response times, operational efficiency, and client satisfaction. This relationship builds loyalty and encourages repeat business, showing that partnering with a local IT service provider is crucial for growth.
In a landscape where cybersecurity threats are ever-evolving, the value of local IT services cannot be overstated. Many organizations struggle to keep up with the rapidly changing cybersecurity landscape, risking their sensitive data and operational integrity. Companies are encouraged to embrace these partnerships to not only protect their operations but also to drive innovation and success. Without local IT expertise, businesses may find themselves vulnerable to cyber threats, leading to potential data breaches and loss of customer trust. Investing in local IT expertise is a strategic move that positions organizations to thrive amidst challenges, ensuring they remain competitive and resilient in their respective industries.
Why is it important for healthcare organizations to collaborate with local IT services providers?
Local IT services providers possess a deep understanding of market dynamics and compliance requirements specific to their regions, allowing them to customize services to meet the distinct needs of healthcare organizations, which must comply with stringent regulations like HIPAA.
What compliance regulations do financial institutions need to adhere to?
Financial institutions are required to comply with regulations such as PCI-DSS and GDPR.
How do local IT services providers help organizations with compliance challenges?
Local suppliers are often more adaptable to legislative changes, enabling companies to stay ahead of compliance challenges and avoid potential fines or legal issues.
What is Compliance as a Service (CaaS)?
Compliance as a Service (CaaS) is a solution offered by local IT services providers that simplifies the compliance process for small and medium-sized enterprises by providing access to enterprise-level expertise without the high costs of maintaining in-house staff.
How can proactive compliance benefit organizations?
Proactive compliance can reduce downtime from security or audit-related disruptions, thereby enhancing organizational resilience.
What types of cybersecurity tools do local IT services providers offer?
Local IT services providers offer customized cybersecurity tools such as endpoint protection and threat detection, which assist organizations in navigating compliance with ease.
Why is regional IT expertise crucial for organizations today?
Regional IT expertise is essential for fostering compliance and resilience in today's corporate landscape, helping organizations safeguard against evolving cybersecurity threats.