Introduction
In an era where digital threats are more pronounced than ever, the healthcare sector stands at a pivotal crossroads. Cyber attacks not only endanger patient data but also inflict substantial financial repercussions, with healthcare organizations experiencing an average loss exceeding $11 million per incident. For CFOs, the stakes are particularly elevated as they navigate the intricate landscape of financial integrity and operational security.
How can they effectively shield their organizations from these persistent threats while ensuring compliance and preserving trust? This article explores essential strategies that CFOs must implement to mitigate the risk of cyber attacks, empowering them to bolster their defenses and safeguard their financial health.
Understand Cyber Attacks and Their Impact
In today's digital landscape, cybersecurity is not just important; it's essential. Cyber threats manifest in various forms, including:
- Phishing
- Denial-of-service incidents
Each presents unique challenges that can significantly impact healthcare organizations. Ransomware, for example, can encrypt critical data and demand hefty ransoms for its release, while phishing schemes often lead to unauthorized access to sensitive financial information. The costs are staggering; in 2025, healthcare entities reported an average expense of $11.45 million per incident, the highest across all industries. Direct costs encompass ransom payments, legal fees, and substantial losses due to operational downtime.
Consider this: 94% of hospitals affected by recent cyber incidents reported disruptions, with 33% indicating disruptions that affected more than half of their revenue. The reputational damage from such breaches can erode customer trust, leading to long-term revenue loss. Understanding these dynamics is crucial for CFOs aiming to develop a strategy that incorporates risk management while also safeguarding the financial health of their organizations.
To combat these threats, it is imperative to establish monitoring as a key strategy for cybersecurity. Continuous observation ensures that suspicious behaviors are detected and addressed before they escalate into significant risks, which is a key strategy in cybersecurity, protecting your organization from ransomware, phishing, and other forms of malware. Additionally, security measures designed specifically for the healthcare sector—including comprehensive firewall and network protection strategies—can further bolster your defenses against these evolving cyber threats.

Implement Key Cybersecurity Measures
CFOs must prioritize key measures that are essential for safeguarding their organizations to learn how to reduce the risk of cyber attack effectively. Cybersecurity in healthcare is not just a necessity; it is a critical component of operational integrity. With the rise of cyber threats, the implications for healthcare organizations are profound. Here are the vital strategies that can fortify defenses and promote a secure environment.
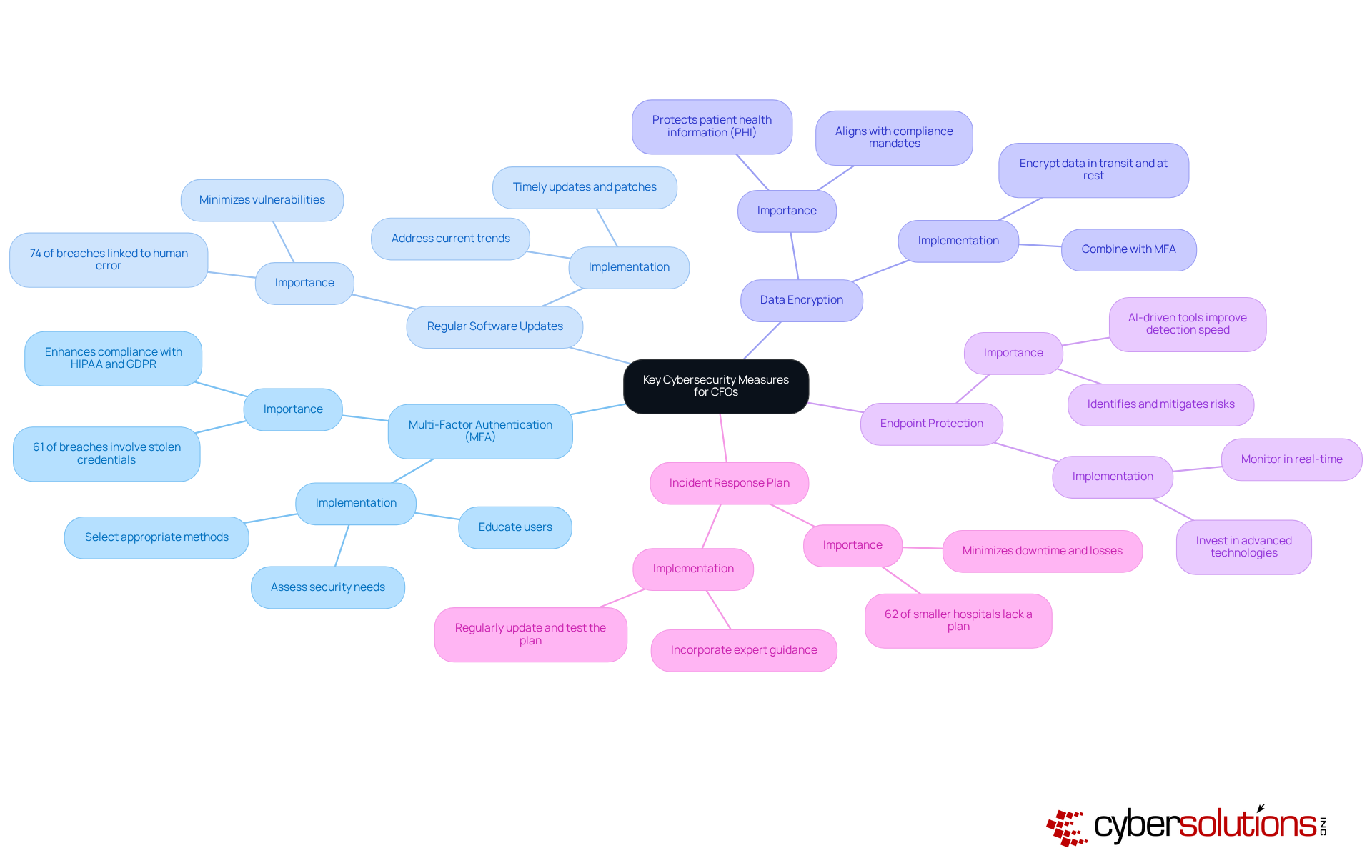
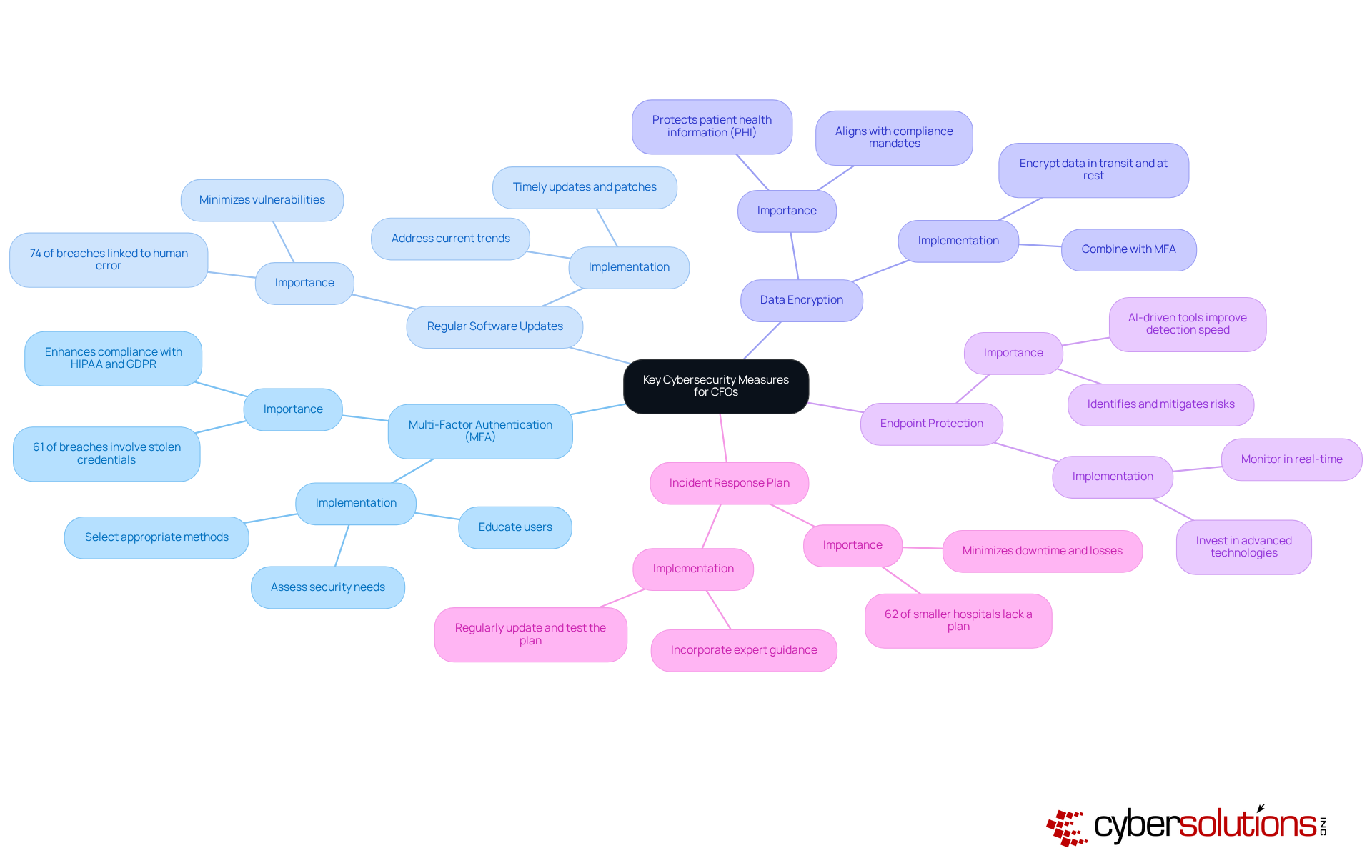
- Implementing MFA across all systems is essential for providing an additional layer of protection beyond conventional passwords. With 61% of healthcare breaches involving stolen or compromised credentials, MFA significantly reduces the risk of unauthorized access by requiring users to provide two or more verification factors. This not only improves safety but also assists companies in adhering to regulatory standards like HIPAA and GDPR. To implement MFA effectively, organizations should assess their security needs, select appropriate MFA methods, and educate users on the importance of this additional layer of protection.
- Keeping software up-to-date is crucial for protecting against vulnerabilities that cybercriminals exploit. Organizations that regularly implement updates can greatly minimize their vulnerability to risks. For instance, 74% of healthcare breaches are linked to human error or credential misuse, which can often be mitigated through timely updates and patches. Regular updates also help in addressing current trends in software vulnerabilities, ensuring that systems remain resilient against emerging threats.
- Protecting patient health information (PHI) through advanced encryption methods is vital for safeguarding sensitive data from unauthorized access. Encrypting data both in transit and at rest not only improves overall data protection but also aligns with compliance mandates, reinforcing trust among stakeholders. Implementing MFA alongside encryption further enhances the protection framework.
- Utilizing advanced monitoring solutions is essential for monitoring and responding to dangers in real-time. As the healthcare industry becomes more frequently targeted, implementing strong strategies can assist in identifying and mitigating risks before they escalate. Current trends suggest that entities utilizing AI-driven anomaly detection tools have reported up to 40% quicker identification of risks, highlighting the significance of investing in advanced protective technologies.
- Developing and regularly updating an incident response plan is essential for ensuring quick recovery from cyber incidents. A well-structured plan allows entities to respond effectively to breaches, minimizing downtime and financial losses. Routine exercises and revisions to the plan can assist staff in staying ready for potential threats, strengthening a culture of awareness. Notably, 62% of smaller hospitals lack a dedicated ransomware playbook, underscoring the urgency of having a robust plan in place. This structured approach, along with expert guidance from virtual CISO services, can significantly enhance a company's ability to manage incidents and maintain compliance with HIPAA standards.
By implementing these strategies, CFOs can greatly improve their entity’s protective stance, minimize the chances of successful breaches, and promote a culture of security that aligns with wider business goals, specifically focusing on how to reduce the risk of cyber attack. Additionally, it is important to recognize that cybersecurity is an ongoing process that requires continuous monitoring, updates, and expert oversight.
Educate Employees on Cybersecurity Best Practices
Informing staff about how to improve cybersecurity is essential for cultivating a robust security culture within the organization. In today's landscape, where cyber threats are ever-evolving, it is crucial to equip employees with the knowledge of how to respond to incidents to protect sensitive data. Here are some effective strategies that can significantly enhance your cybersecurity posture:
- Regular Training: Conduct training sessions covering vital topics such as phishing awareness, safe internet browsing, and secure password practices. This proactive approach empowers employees to identify and mitigate risks effectively, particularly in understanding how to respond to cyber threats.
- Simulated Phishing Exercises: Implement exercises to test employees' awareness and reinforce learning. Research indicates that organizations employing adaptive phishing simulations can reduce phishing risk by up to 30% among new hires, making this a critical component of your training strategy.
- Reporting Mechanisms: Establish channels for reporting suspicious activities or potential risks. Encouraging employees to report incidents without fear of judgment fosters a proactive environment that is essential for understanding how to respond to threats through early detection and response.
- Security Policies: Develop and distribute a comprehensive policy that outlines acceptable use of company resources and data handling procedures. A well-defined policy serves as a foundation for secure practices across the organization and is essential for understanding how to manage data securely.
- Continuous Learning: Encourage ongoing education by providing access to online resources and updates on emerging threats. Incorporating microlearning techniques can help maintain engagement and retention, allowing employees to absorb information in manageable doses.
By fostering a knowledgeable workforce, organizations can learn how to prevent breaches that may result from human error. The commitment to continuous improvement in cybersecurity practices not only protects sensitive data but also enhances overall organizational resilience.

Conduct Regular Security Assessments and Updates
In the rapidly evolving landscape of healthcare, it is essential to know how to assess and maintain a robust cybersecurity stance. Regular evaluations and updates are essential for understanding how to defend against emerging threats. Here’s how to implement this effectively:
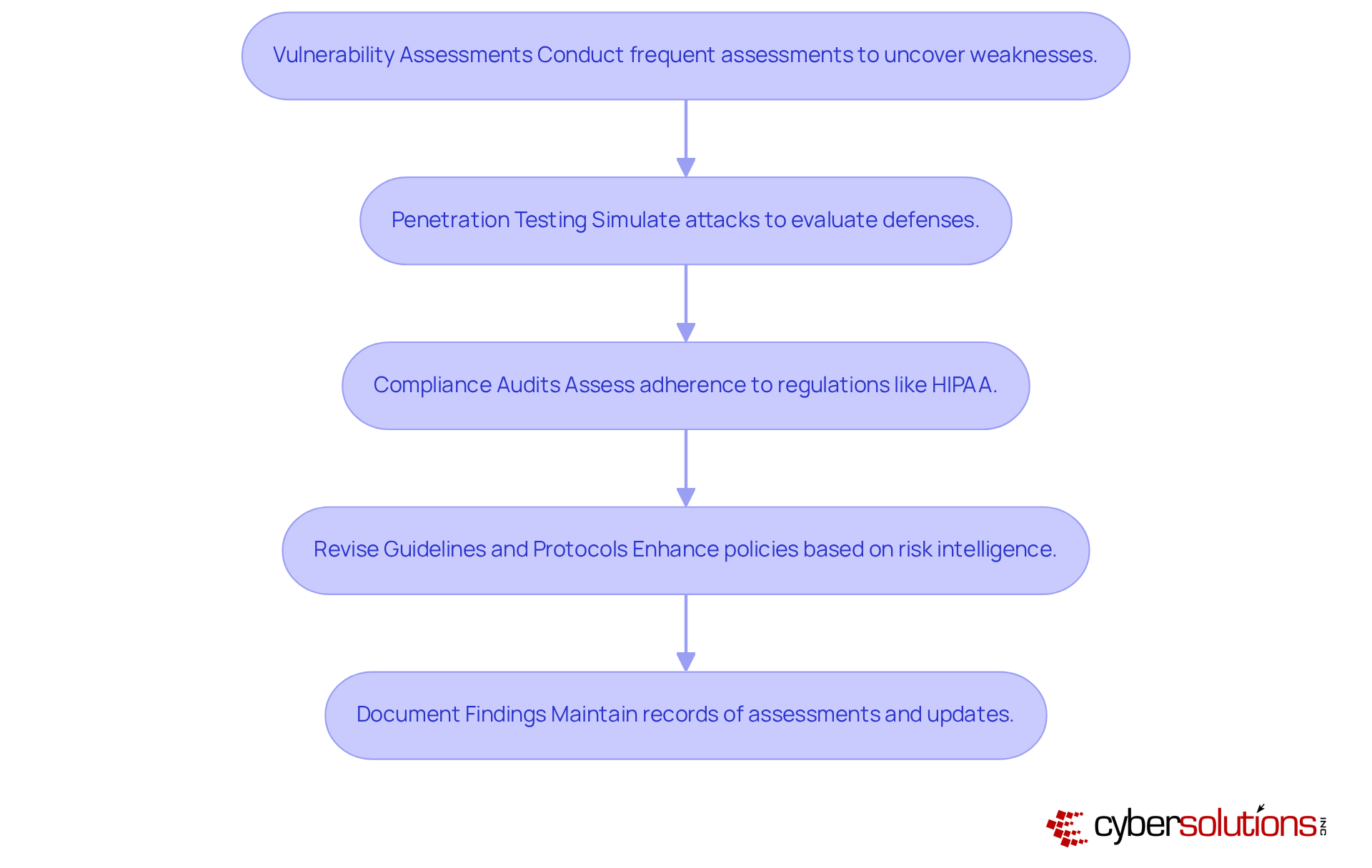
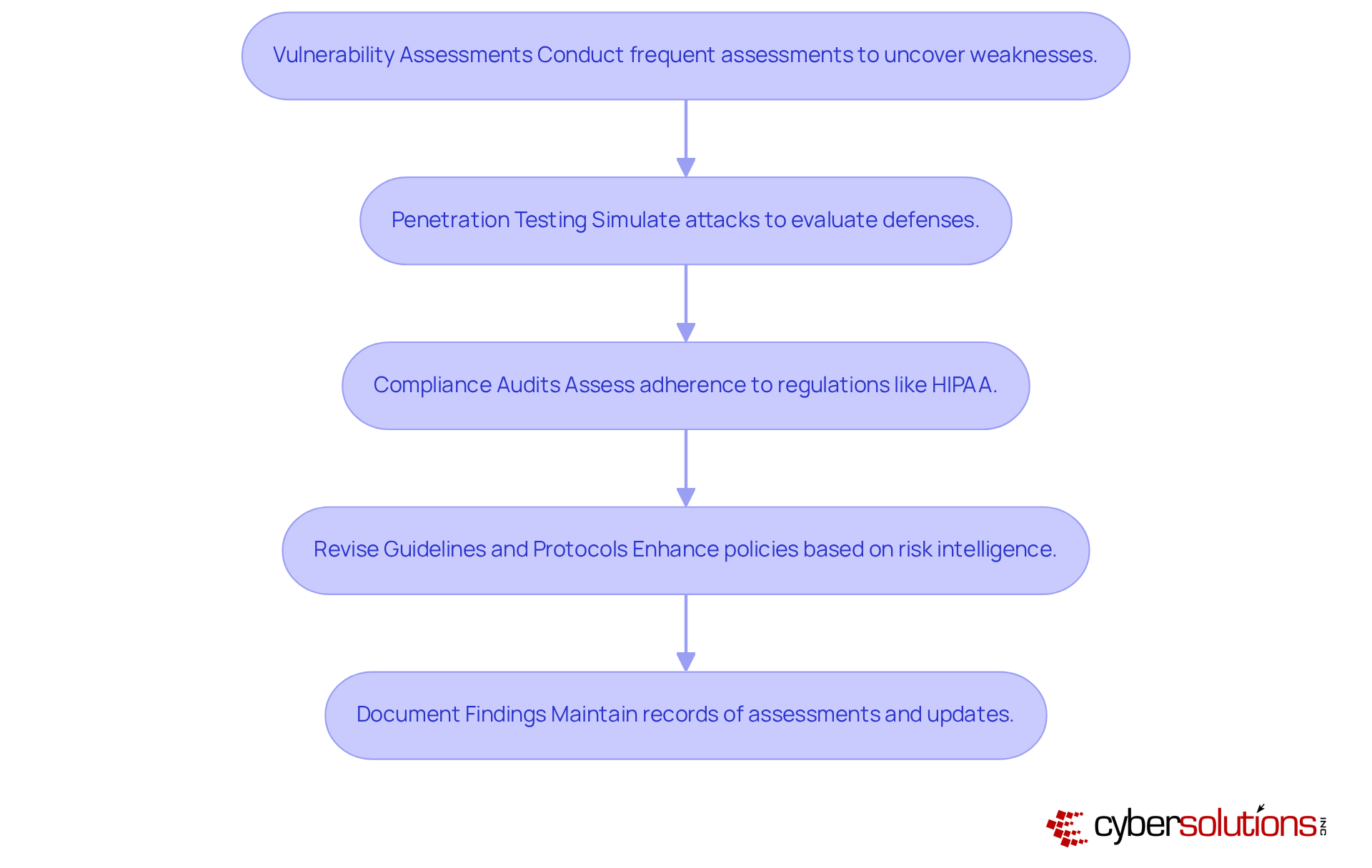
- Assess Vulnerabilities: Conduct frequent assessments using tools such as Nessus or Qualys to uncover and rectify weaknesses in your systems. Utilizing the latest tools can enhance the accuracy and efficiency of these assessments, ensuring comprehensive coverage of potential risks.
- Perform Penetration Testing: Collaborate with third-party experts to perform penetration testing. This process simulates real-world attacks, providing insights into the effectiveness of your defenses and identifying areas for improvement. Remarkably, entities that participate in routine testing have reported considerable decreases in vulnerabilities.
- Monitor Compliance: Regularly assess compliance with industry regulations such as HIPAA. This ensures that your entity adheres to necessary standards and mitigates the risk of expensive breaches, which in healthcare can average over $9.77 million per incident. Application control plays a key role here, as it helps enforce strict control over software usage, ensuring that only approved applications run on your systems, thereby enhancing compliance with regulations. Features such as centralized management and continuous monitoring of application activity further strengthen this compliance framework.
- Revise Guidelines and Protocols: Continuously enhance protective policies and procedures based on the most recent risk intelligence and evaluation results. This proactive strategy assists organizations in learning how to adapt, particularly as the healthcare sector was the focus of approximately 25% of all documented cybersecurity incidents in 2024. Incorporating threat intelligence into your security strategy can significantly reduce the attack surface and minimize vulnerabilities, making it harder for attackers to exploit your systems.
- Document Findings: Maintain detailed records of all assessments and updates. This documentation not only tracks progress but also informs future strategies, enabling a more resilient cybersecurity framework.
By integrating these practices into the organizational routine, CFOs can ensure that their defenses evolve alongside emerging threats, ultimately protecting assets and maintaining trust.
Conclusion
In the face of escalating cyber threats, it is essential for CFOs to prioritize cybersecurity as a cornerstone of their organizational strategy. The article delineates crucial steps that can significantly mitigate the risk of cyber attacks, underscoring that a proactive approach is not merely advantageous but vital for the financial health and operational integrity of healthcare organizations.
The key arguments presented highlight the necessity of:
- Comprehending the diverse types of cyber threats
- Implementing robust cybersecurity measures—such as multi-factor authentication and regular software updates
- Cultivating a culture of security awareness among employees
By conducting regular security assessments and ensuring compliance with industry regulations, CFOs can empower their organizations to better manage potential breaches and reduce financial losses tied to cyber incidents.
Ultimately, the onus of safeguarding sensitive data and maintaining trust with stakeholders rests heavily on the shoulders of CFOs. By embracing these strategies and committing to continuous education and enhancement of cybersecurity practices, organizations can fortify themselves against the ever-evolving landscape of cyber threats. Adopting a comprehensive cybersecurity framework transcends mere defense; it emerges as a strategic imperative that will protect both financial and reputational assets in an increasingly digital world.
Frequently Asked Questions
What are the main types of cyber threats faced by healthcare organizations?
The main types of cyber threats in healthcare include phishing, ransomware, and denial-of-service incidents.
What are the potential impacts of ransomware on healthcare organizations?
Ransomware can encrypt critical data and demand large ransoms for its release, leading to significant operational downtime and financial losses.
How much do healthcare organizations spend on average per cyber incident?
In 2025, healthcare entities reported an average expense of $11.45 million per incident, making it the highest across all industries.
What percentage of hospitals reported financial impacts from cyber incidents?
94% of hospitals affected by recent cyber incidents reported financial impacts.
What are some of the direct costs associated with cyber attacks in healthcare?
Direct costs include ransom payments, legal fees, and substantial losses due to operational downtime.
How can cyber attacks affect a hospital's revenue?
33% of hospitals indicated that disruptions from cyber incidents affected more than half of their revenue.
What is the importance of understanding cyber threats for CFOs in healthcare?
Understanding these dynamics is crucial for CFOs to develop a robust cybersecurity strategy that reduces the risk of cyber attacks while safeguarding the financial health of their organizations.
What is a key strategy for reducing the risk of cyber attacks?
Establishing round-the-clock monitoring is a key strategy to detect and address suspicious behaviors before they escalate into significant risks.
What tailored IT solutions can help protect healthcare organizations from cyber threats?
Tailored IT solutions for healthcare, including comprehensive firewall and network protection strategies, can bolster defenses against evolving cyber threats.
List of Sources
- Understand Cyber Attacks and Their Impact
- industrialcyber.co (https://industrialcyber.co/medical/health-isac-heartbeat-flags-surge-in-ransomware-vpn-exploits-across-healthcare-systems)
- aha.org (https://aha.org/change-healthcare-cyberattack-underscores-urgent-need-strengthen-cyber-preparedness-individual-health-care-organizations-and)
- invensis.net (https://invensis.net/blog/cyber-threats-to-healthcare-data)
- hipaajournal.com (https://hipaajournal.com/change-healthcare-responding-to-cyberattack)
- Implement Key Cybersecurity Measures
- secureworld.io (https://secureworld.io/industry-news/healthcare-cybersecurity-market-soars)
- allcovered.com (https://allcovered.com/blog/5-reasons-multi-factor-authentication-is-a-must)
- 7 Reasons Why You Need MFA Security in 2026 (https://splashtop.com/blog/why-you-need-MFA-security)
- vivatechnology.com (https://vivatechnology.com/news/the-role-of-mfa-in-cybersecurity-strengthening-protection)
- Educate Employees on Cybersecurity Best Practices
- techxplore.com (https://techxplore.com/news/2025-09-cybersecurity-dont-employees-falling-phishing.html)
- paubox.com (https://paubox.com/blog/what-does-cybersecurity-training-look-like-in-2025)
- Out Phishing: How Health Systems Can Re-Evaluate Employee Security Training (https://healthtechmagazine.net/article/2025/09/out-phishing-how-health-systems-can-re-evaluate-employee-security-training)
- helpnetsecurity.com (https://helpnetsecurity.com/2025/07/23/phishing-simulations-effectiveness-in-organizations)
- lugpa.org (https://lugpa.org/cybersecurity-in-healthcare--2025)
- Conduct Regular Security Assessments and Updates
- Major Healthcare Data Security Trends in 2025 - Bluesight (https://bluesight.com/news/major-healthcare-data-security-trends-in-2025)
- censinet.com (https://censinet.com/perspectives/the-hipaa-wake-up-call-what-every-risk-analyst-needs-to-know-in-2025)
- cybersecuritydive.com (https://cybersecuritydive.com/news/healthcare-cybersecurity-risks-report-fortified/753077)
- Healthcare Cybersecurity in 2025—Time to Lead, Not Lag (https://healthcatalyst.com/learn/insights/healthcare-cybersecurity-2025-time-to-lead-not-lag)
- isaca.org (https://isaca.org/resources/news-and-trends/industry-news/2025/healthcares-growing-threat-landscape)