
In today’s digital landscape, dark web security monitoring has become essential for organizations grappling with the complexities of modern cybersecurity threats. C-suite leaders can gain invaluable insights by mastering the art of monitoring these hidden online spaces, where stolen data and sensitive information are exchanged among cybercriminals.
But with the alarming rise in illicit web threats, a pressing question arises: how can executives ensure their organizations are not only aware of these risks but also equipped to counteract them?
This article explores vital practices and strategies that empower leaders to strengthen their defenses against the ever-evolving dangers lurking in the dark web.
Dark web security monitoring is crucial for C-suite leaders, as it involves the continuous surveillance of illicit online spaces where stolen data, credentials, and sensitive information are traded. Understanding this concept is essential, as it directly impacts an organization’s risk profile. The concealed web is a breeding ground for cybercriminals who exploit vulnerabilities to access corporate data. With a significant portion of entities expected to be affected by illicit web threats in 2026, the urgency of addressing this issue cannot be overstated.
By employing deep web surveillance, companies can proactively detect compromised information before it escalates into serious breaches. This not only protects their reputation but also ensures financial stability. Such a proactive approach reduces risks and meets compliance requirements, keeping organizations vigilant against evolving cyber threats. Case studies reveal that organizations with breached credentials found on the hidden web face a 2.56 times greater risk of experiencing a cyberattack. This statistic underscores the necessity for robust strategies in dark web security monitoring.
Expert opinions further emphasize that effective risk management in today’s digital landscape requires a comprehensive understanding of underworld web activities and their potential impact on corporate security. As cyber threats continue to evolve, it’s imperative for executives to stay informed and take decisive action to safeguard their organizations.

When it comes to safeguarding your organization against the lurking threats of the dark web, C-suite leaders must prioritize several key features in monitoring solutions:
By focusing on these critical aspects, executives can ensure they select a solution that effectively mitigates risks associated with dark web security monitoring, ultimately safeguarding their organizations against evolving cyber threats.

To effectively implement deep web security oversight, C-suite leaders must recognize the critical importance of cybersecurity in today’s digital landscape.
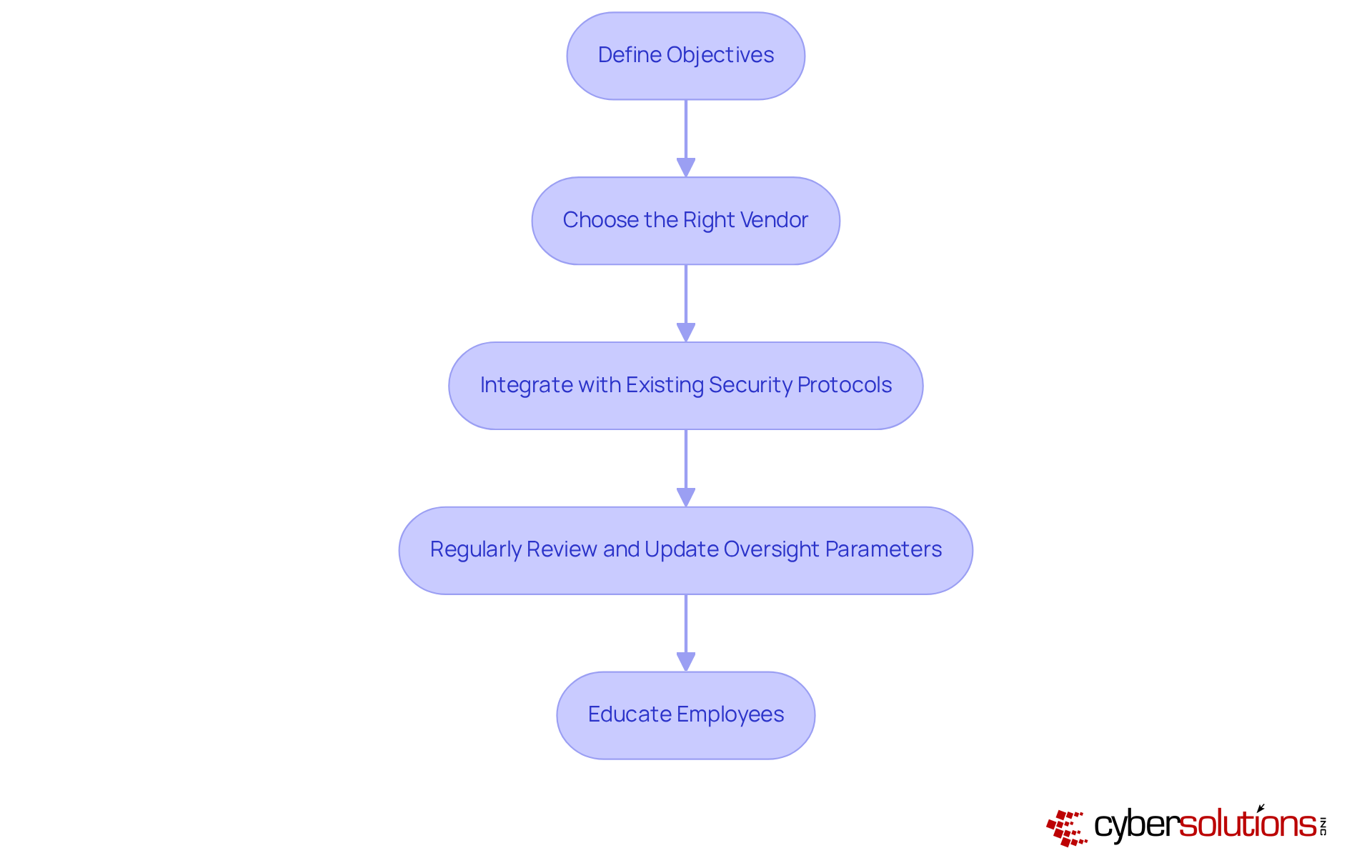
By adhering to these optimal methods, organizations can establish a robust framework for hidden web surveillance that effectively reduces risks and strengthens their security stance.
Investing in dark web security monitoring is crucial for organizations, particularly for C-suite leaders who prioritize risk management and compliance. In today’s digital landscape, where threats are ever-evolving, understanding the benefits of dark web security monitoring can significantly enhance an organization’s overall security posture.
By recognizing and communicating these advantages, C-suite leaders can make informed decisions regarding their cybersecurity investments, ensuring their organizations remain secure in an increasingly complex digital environment.

Dark web security monitoring stands as a crucial pillar for C-suite leaders, fundamentally shaping an organization's capacity to protect sensitive information and mitigate the risks posed by cyber threats. In a landscape where cyber threats are ever-evolving, understanding the significance of monitoring illicit online spaces is not just beneficial - it's imperative. Executives who grasp this can implement proactive measures that not only shield their organizations but also bolster their overall security posture.
Key points throughout this discussion underscore the necessity of comprehensive coverage, real-time alerts, and actionable intelligence in effective monitoring solutions. By adopting best practices - such as defining clear objectives, selecting the right vendors, and cultivating a culture of cybersecurity awareness - organizations can adeptly navigate the complexities of dark web threats. The advantages of investing in these monitoring solutions are manifold, ranging from early threat detection to enhanced compliance and reputation management, further emphasizing their critical value in today’s digital landscape.
The importance of dark web security monitoring cannot be overstated. As cyber threats continue to evolve, C-suite leaders must prioritize these strategies to ensure their organizations remain resilient. By embracing robust monitoring practices, executives not only safeguard their assets but also foster trust and confidence among stakeholders, paving the way for sustainable success in an increasingly challenging environment.
What is dark web monitoring?
Dark web monitoring involves the continuous surveillance of illicit online spaces where stolen data, credentials, and sensitive information are traded, helping organizations detect compromised information before it escalates into serious breaches.
Why is dark web monitoring important for organizations?
It is crucial for organizations as it directly impacts their risk profile, protects their reputation, ensures financial stability, and helps meet compliance requirements against evolving cyber threats.
What are the risks associated with not implementing dark web monitoring?
Organizations that do not implement dark web monitoring face a significantly higher risk of cyberattacks, with those having breached credentials found on the hidden web facing a 2.56 times greater risk of experiencing such attacks.
How can dark web monitoring benefit C-suite leaders?
Dark web monitoring provides C-suite leaders with essential insights into potential threats, enabling them to take proactive measures to safeguard their organizations and manage risks effectively.
What does deep web surveillance entail?
Deep web surveillance entails actively monitoring the hidden web for compromised information, allowing organizations to identify and address vulnerabilities before they lead to serious security breaches.
What is the expected trend regarding illicit web threats by 2026?
A significant portion of entities is expected to be affected by illicit web threats by 2026, highlighting the urgency for organizations to address dark web security monitoring.
How do expert opinions view the importance of understanding dark web activities?
Experts emphasize that effective risk management in today’s digital landscape requires a comprehensive understanding of underworld web activities and their potential impact on corporate security.