
In today's world, where cyber threats are more prevalent than ever, effective cybersecurity documentation stands as a vital pillar for protecting sensitive information, especially in the healthcare sector. This article explores ten essential practices that not only bolster compliance with industry regulations but also strengthen organizational resilience against potential breaches. With a staggering percentage of cyber incidents arising from human error, one must ask: how can organizations ensure that their documentation transcends mere formality, evolving into a robust framework that actively mitigates risks and cultivates a culture of security?
The healthcare landscape is fraught with unique challenges, making it imperative for CFOs and decision-makers to prioritize cybersecurity. As the stakes rise, so does the need for comprehensive strategies that address these vulnerabilities head-on. By implementing effective documentation practices, organizations can not only comply with regulations but also foster a proactive approach to security that resonates throughout their operations.
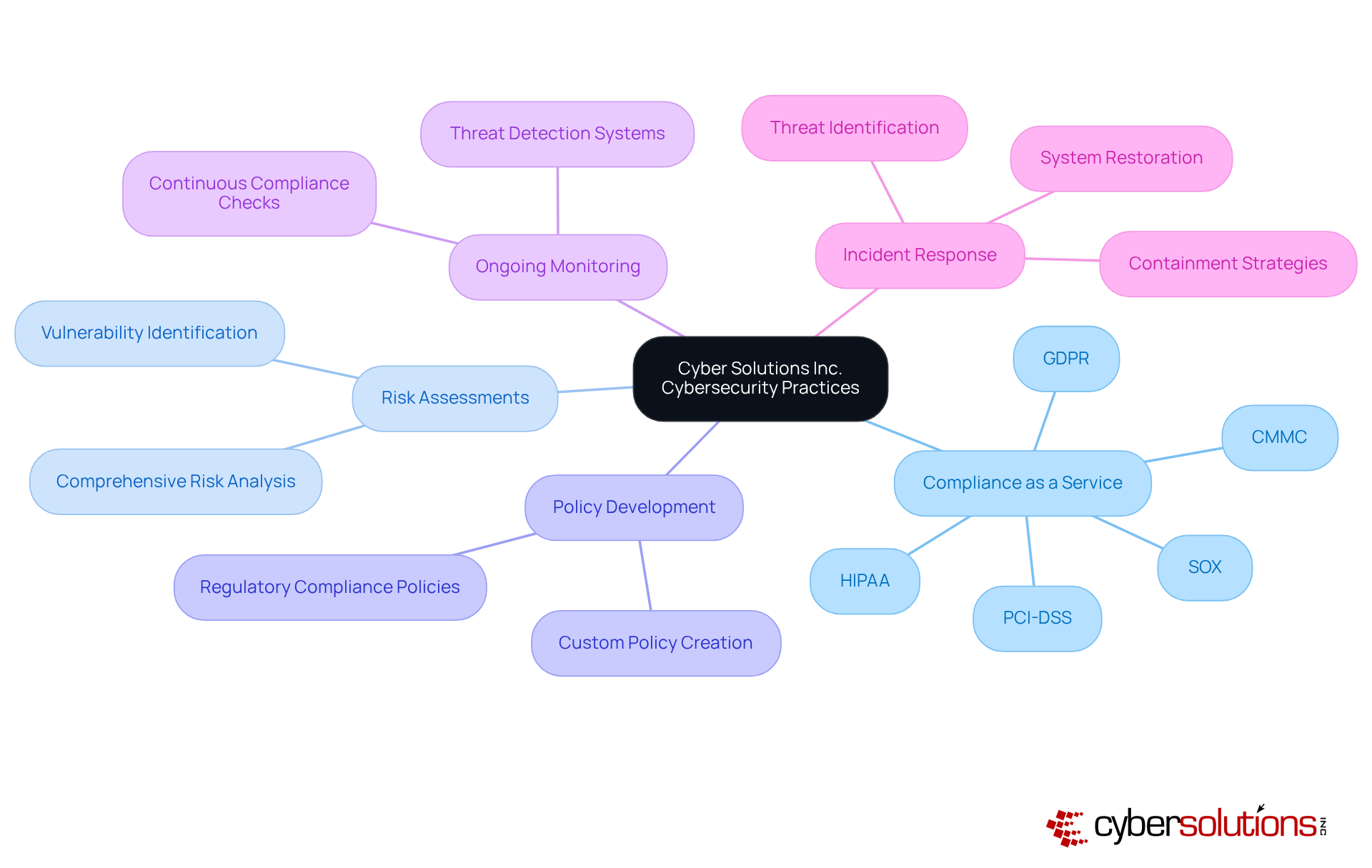
In today’s digital landscape, the importance of robust cybersecurity cannot be overstated, especially in the healthcare sector. Cyber Solutions Inc. specializes in creating tailored documentation that address the unique requirements of various industries, ensuring that organizations can navigate the complex web of regulations with ease. Our solutions simplify adherence to standards like HIPAA, PCI-DSS, CMMC, SOX, and GDPR, which are critical for maintaining patient trust and safety.
Healthcare organizations face unique challenges when it comes to cybersecurity. With sensitive data at stake, the consequences of a breach can be devastating, not just financially but also in terms of reputation. By providing comprehensive documentation, policy development, and ongoing compliance monitoring, we ensure that your documentation not only meets compliance requirements but also enhances operational efficiency. This customized strategy assists businesses in reducing risks while upholding a strong protective stance, ultimately enabling them to concentrate on their primary activities without the weight of IT complications.
Moreover, our services are designed to minimize the impact of cyberattacks. We rapidly identify, contain, and mitigate threats, restoring systems and ensuring business continuity. In a world where cyber threats are ever-evolving, having a proactive partner like Cyber Solutions can make all the difference. Are you ready to fortify your organization against potential cyber threats? Let us help you navigate the complexities of cybersecurity with confidence.
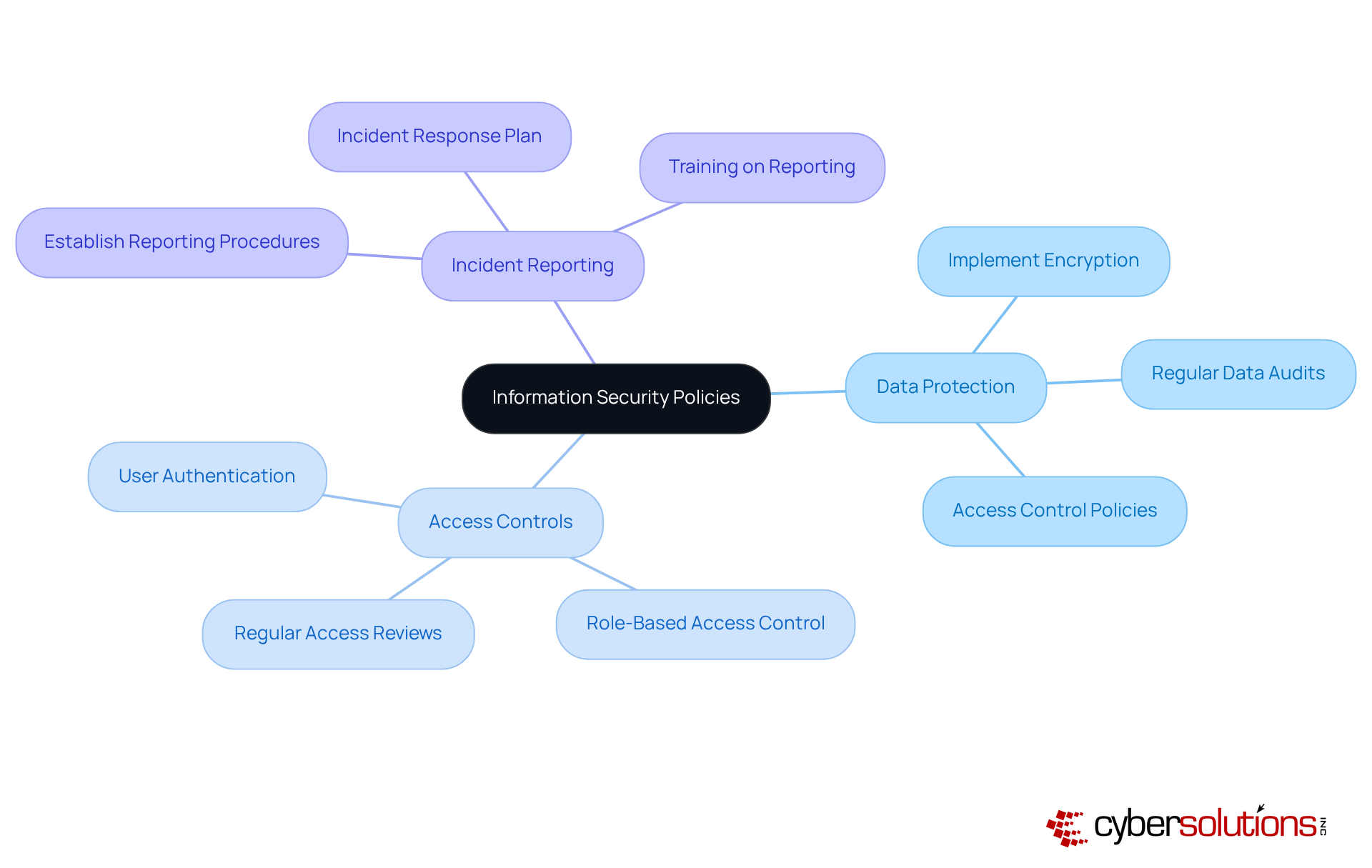
Creating explicit information security policies is not just important; it’s essential for outlining a company's safety objectives and expectations, particularly when it comes to cybersecurity. In a landscape where 88% of cyber incidents stem from human errors, organizations must thoroughly address:
This ensures adherence to stringent standards that are vital for protecting data and systems.
Organizations that implement robust measures showcase the effectiveness of well-defined policies in maintaining eligibility for lucrative government contracts. By ensuring that all employees comprehend these policies, organizations foster a culture of security, which is crucial for adhering to regulations. This proactive approach not only mitigates risks but also enhances the overall security posture.
Cybersecurity experts emphasize that effective documentation is foundational. As one expert noted, "Security is a culture, not merely a control," underscoring the necessity for a comprehensive approach. In today’s environment, fostering awareness and adherence to these policies is more critical than ever. Are your policies up to the challenge?
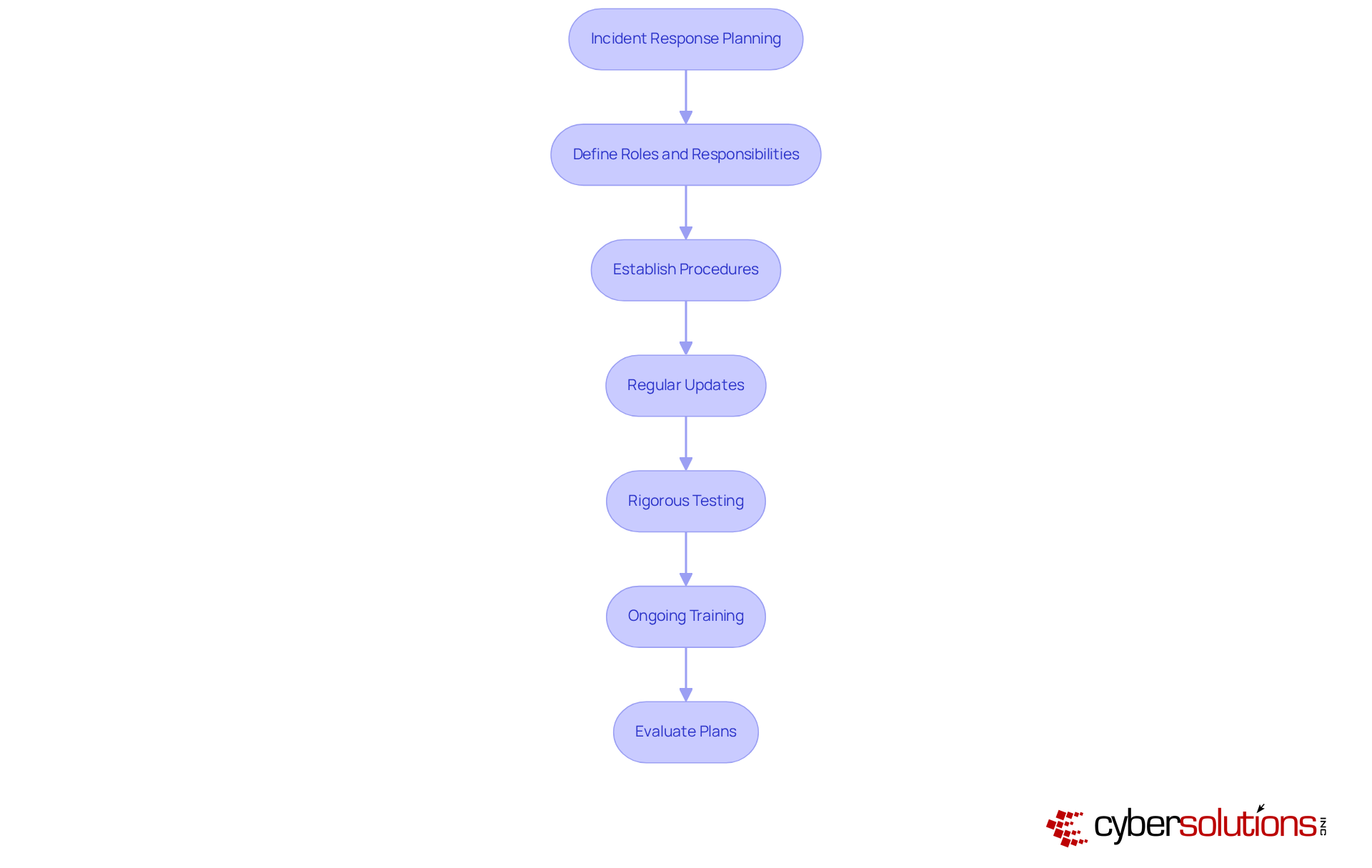
In today’s healthcare landscape, maintaining comprehensive incident response plans is not just important; it’s essential to effectively navigate cybersecurity incidents, especially under pressure. These plans must clearly define roles, responsibilities, and procedures for detecting, responding to, and recovering from incidents, ensuring that compliance with HIPAA standards. To keep them effective and relevant in an ever-evolving threat landscape, regular updates and rigorous testing of plans are crucial.
Organizations that prioritize incident response planning in their cybersecurity strategy can significantly minimize damage and enhance recovery speed following breaches. For instance, Suncor’s robust planning allowed for swift control of their breach, showcasing the effectiveness of proactive measures. As Tannu Jiwnani aptly puts it, "Preparation is the foundation," highlighting how proactive planning transforms a reactive mindset into a resilient posture.
Moreover, ongoing training and simulations are vital for maintaining readiness. They promote adaptability and ensure that all team members are prepared to react quickly and efficiently when incidents arise, particularly in accordance with established protocols. Alarmingly, just 30% of organizations evaluate their incident response plans, underscoring the critical need for regular assessments.
Furthermore, engaging all departments in the incident response process is crucial. A collaborative approach not only enhances adherence to HIPAA standards but also fosters a culture of security awareness. Neglecting this involvement can lead to prolonged exposure to threats and increased costs, reinforcing the necessity of a well-structured plan that aligns with HIPAA compliance.
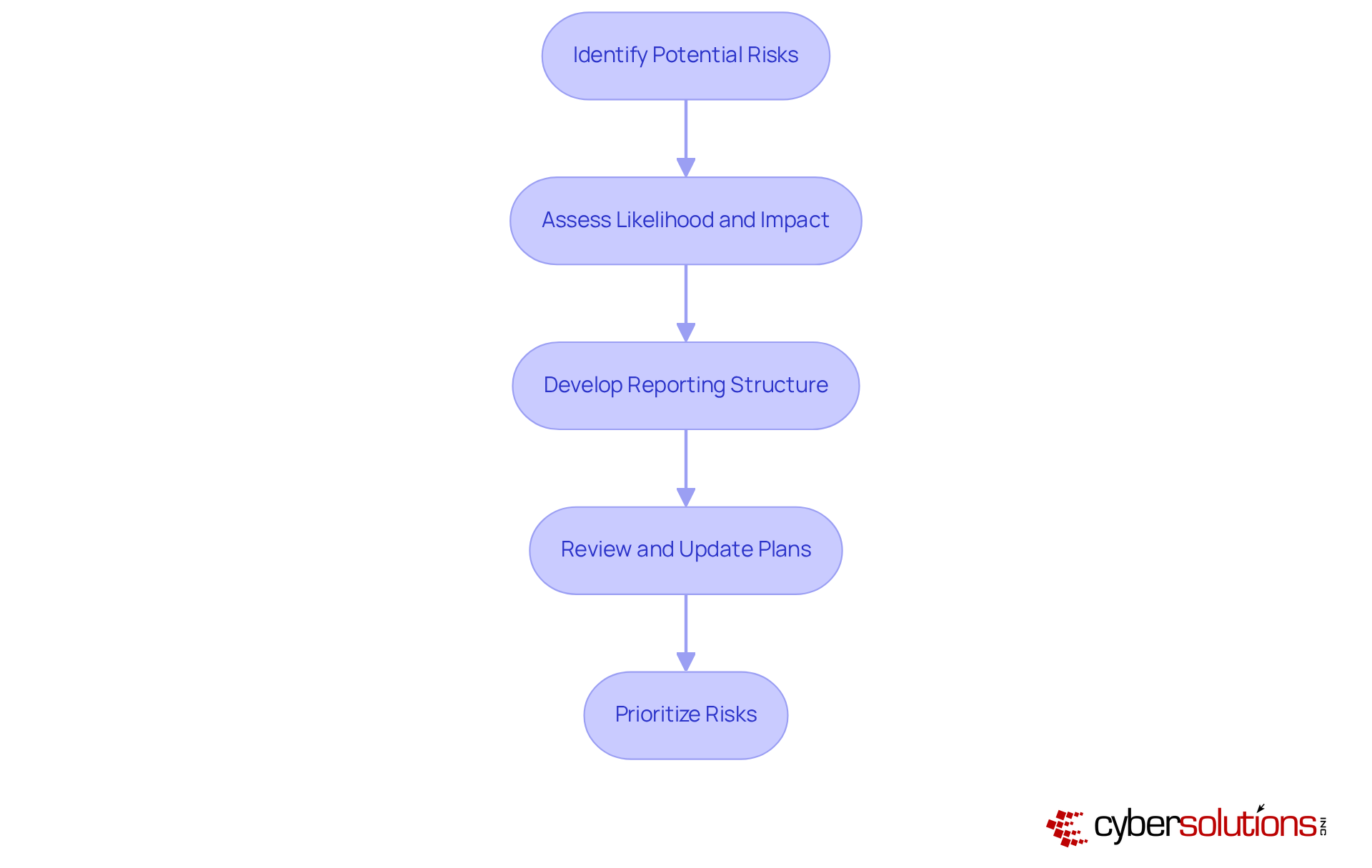
Conducting regular risk assessments is not just a best practice; it’s essential for identifying potential threats and vulnerabilities within a company. These assessments evaluate the likelihood and impact of various risks, enabling organizations to prioritize their cybersecurity efforts effectively. By integrating risk assessments into their security strategy, companies can allocate resources more efficiently and enhance their overall security posture.
Current trends indicate that organizations are increasingly recognizing the importance of these assessments. For example, a striking 94% of entities are evaluating risks, reflecting a significant shift towards proactive threat management. Industry leaders emphasize that without thorough assessments, organizations remain vulnerable to attacks and substantial losses. As Mekan Bairyev aptly states, "Without assessing risks, entities remain vulnerable to threats, legal consequences, and reputational damage."
To conduct effective risk assessments, organizations should follow a structured approach:
By prioritizing risks according to their significance, organizations can implement targeted strategies to mitigate threats effectively. This proactive stance not only enhances security but also ensures compliance, ultimately safeguarding sensitive data and maintaining operational integrity through comprehensive documentation. Notably, the average cost of a data breach is rising to around $4.88 million, underscoring the financial implications of inadequate cybersecurity measures.
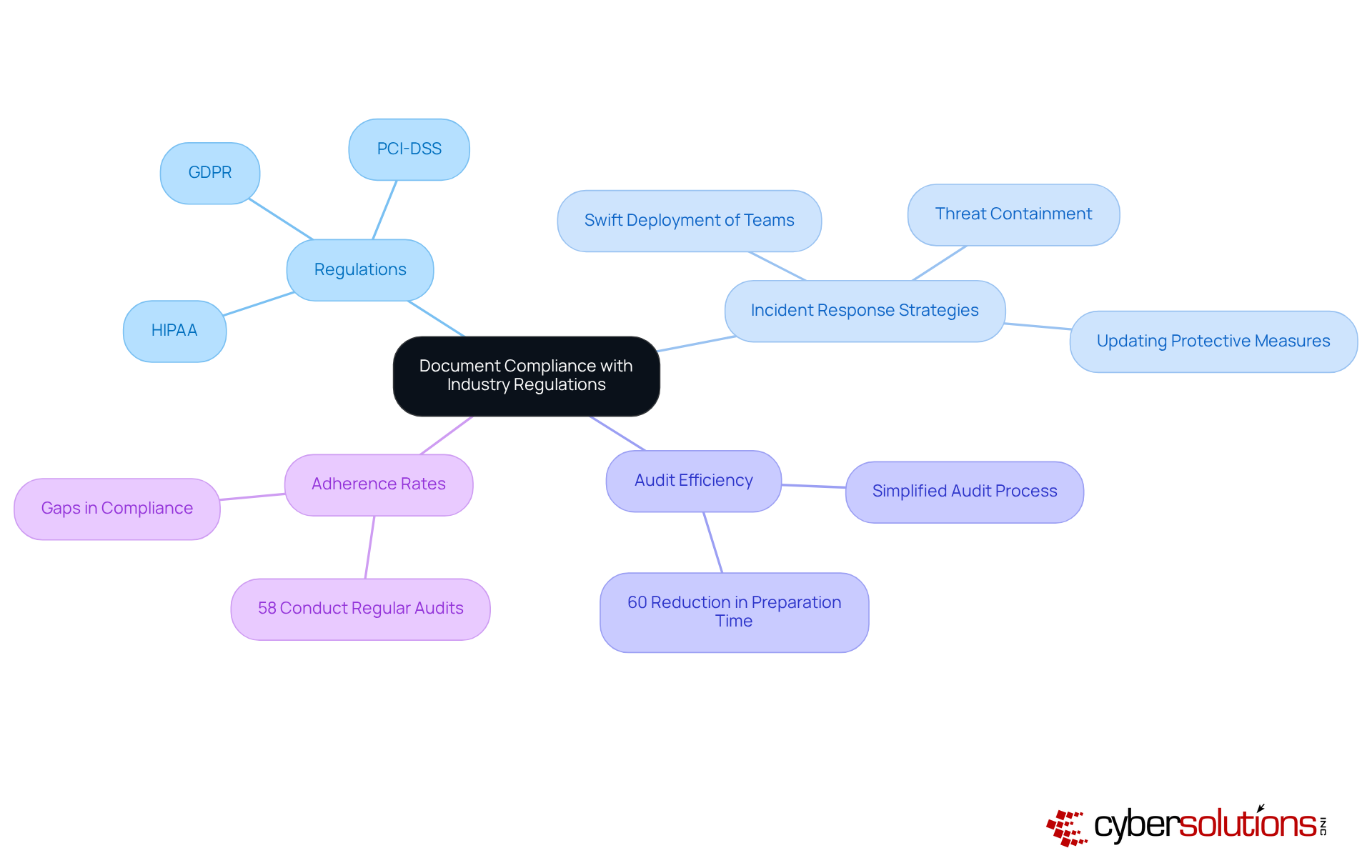
In today's digital landscape, recording adherence to industry regulations is not just important - it's essential for entities operating in regulated environments. This must contain clear evidence of compliance, as demonstrated in various case studies, show that organizations can significantly enhance their adherence efforts. For instance, the swift deployment of incident response teams not only aids in immediate threat containment but also fortifies adherence by ensuring that protective measures are promptly updated and documented.
Organizations that maintain comprehensive documentation have reported a remarkable reduction in incidents, with some achieving up to a 60% decrease. This efficiency and effectiveness reinforces a company’s commitment to security and compliance, safeguarding its reputation and financial interests. However, current adherence rates reveal a concerning trend: while many entities strive for conformity, gaps remain. For example, only 58% of organizations conduct regular audits with these critical regulations.
Compliance specialists emphasize that thorough records are not merely a regulatory requirement; they are a best practice and mitigates risks. By prioritizing compliance alongside effective incident response, organizations can more adeptly navigate the complexities of regulation and strengthen their cybersecurity posture. Are you ready to take the necessary steps to ensure your organization is not just compliant, but also resilient?
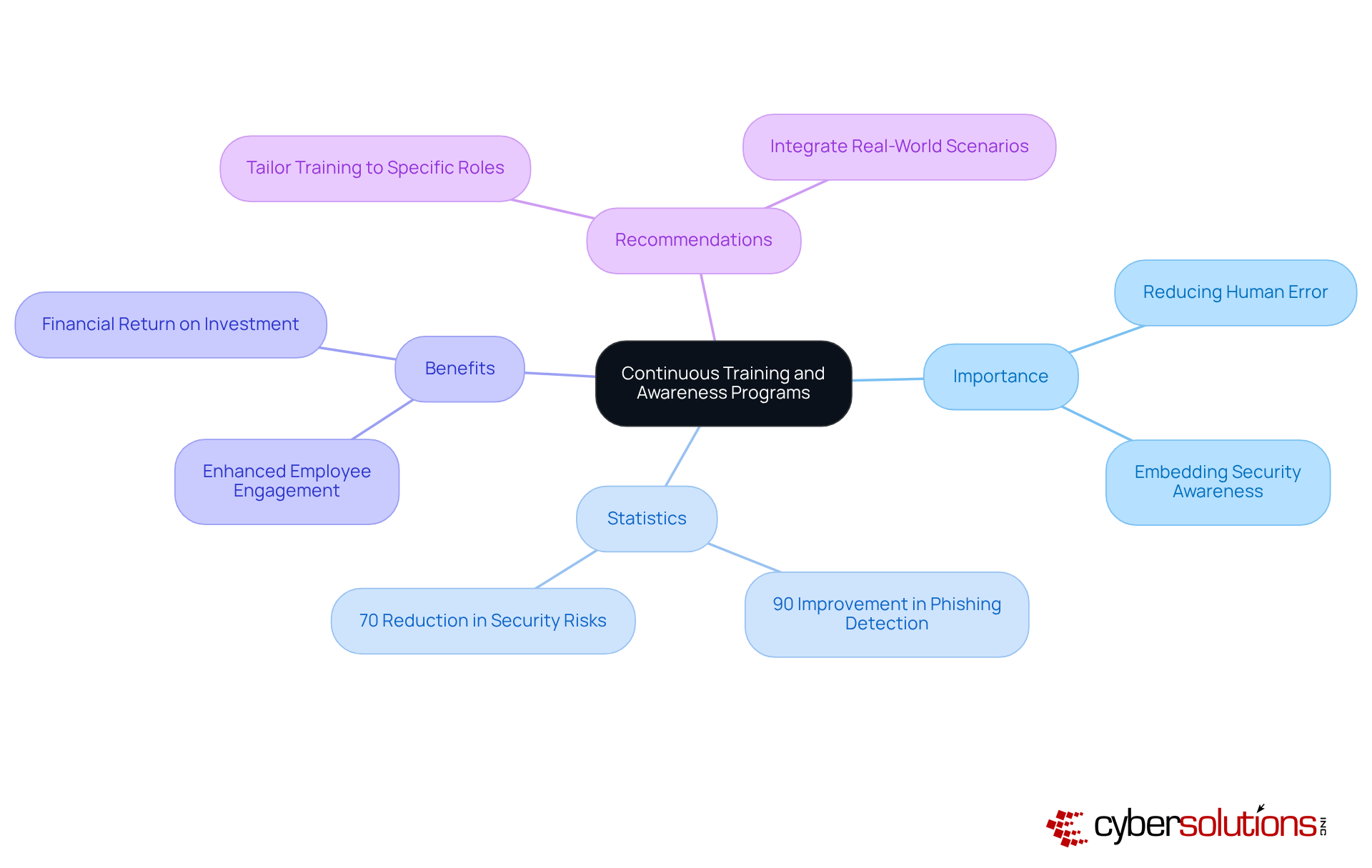
In today’s digital landscape, training programs are essential for equipping employees with the knowledge needed to combat evolving threats. Organizations must tailor these initiatives to their specific needs and ensure they are regularly updated to address new vulnerabilities. A robust security culture, nurtured through ongoing education, can lead to a significant improvement—one of the primary contributors to overall cybersecurity effectiveness.
Consider this: organizations that implement training programs have reported up to a 90% improvement in phishing threat detection within just six months. Furthermore, training has been shown to reduce security-related risks by 70%, as highlighted in the case study "Impact of Training Programs in 2024." With 95% of breaches linked to human error, it’s clear that training is not just beneficial; it’s essential.
By embedding security awareness into daily workflows, companies empower their employees and create a proactive defense against cyber threats. As Andrew Evers points out, connecting training to real-world scenarios is crucial for enhancing its effectiveness. Employees who are well-informed about potential threats serve as a vital line of defense against cybercrime.
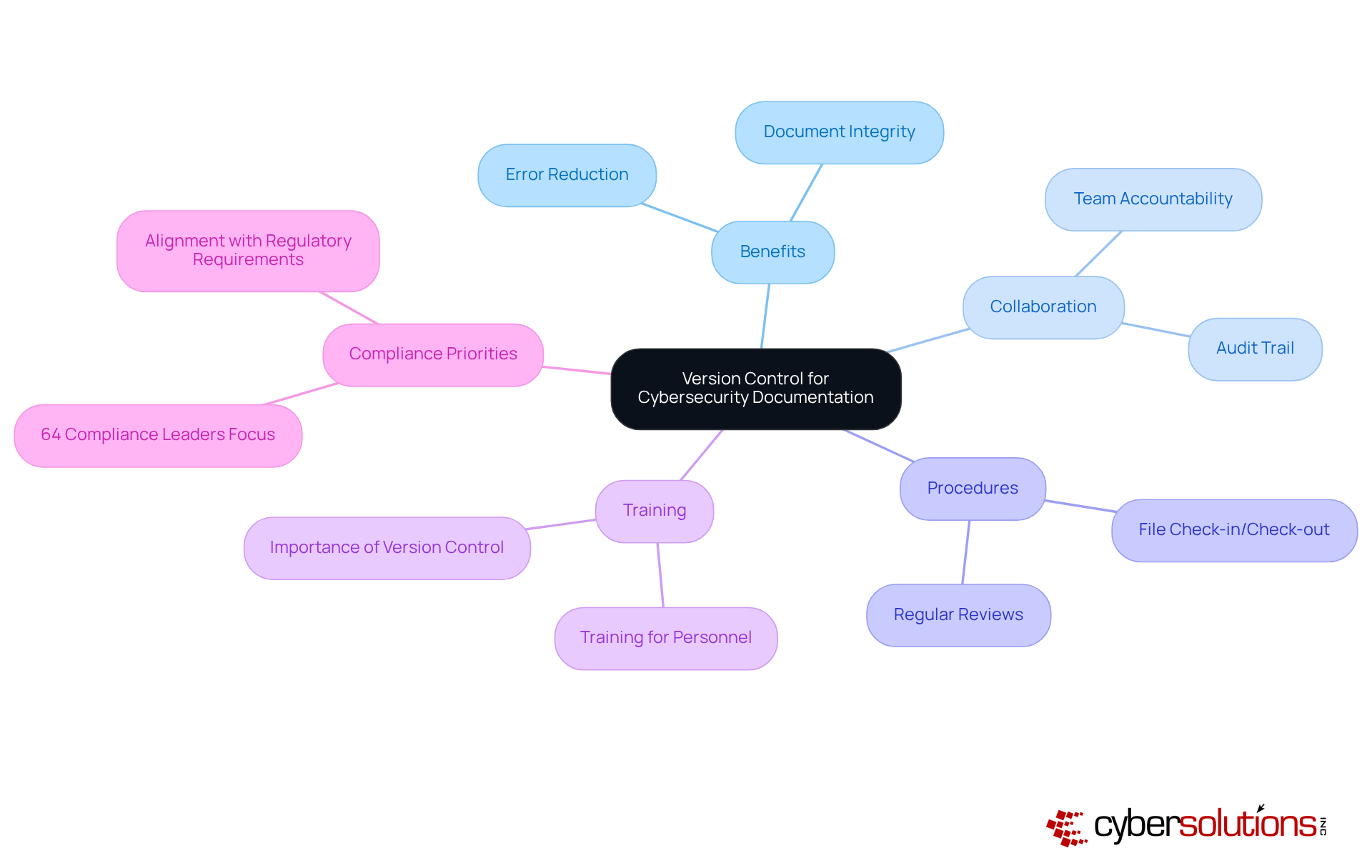
Implementing version control for documentation is not just a best practice; it’s a critical necessity that ensures every modification to policies and procedures is meticulously tracked and managed. This approach safeguards the integrity of documents and allows organizations to revert to previous versions when necessary, significantly reducing the risk of errors. For instance, companies like ABB have successfully adopted version control systems, streamlining their documentation processes and enhancing efficiency across various regions. ABB's utilization of ActiveDocs for document automation and template management showcases the tangible benefits of such systems.
Version control plays a pivotal role in fostering collaboration by providing a clear audit trail. In high-stakes environments where accuracy is non-negotiable, this clarity is essential. As highlighted by Docsvault, "This level of control not only prevents errors but also makes collaboration smoother by eliminating uncertainties about who is editing a document and when." Documentation specialists assert that a robust version control system cultivates a culture of accountability and transparency, empowering teams to work cohesively without the fear of overwriting each other's contributions.
To effectively manage changes in records, organizations should establish clear procedures for checking files in and out, ensuring that only the most relevant versions are accessible. Regular reviews of documentation are crucial to ensure alignment with evolving standards. Furthermore, it’s vital to prioritize training on the importance of version control; a well-informed team is better equipped to uphold high standards in record-keeping practices. With 64% of organizations indicating that this is a priority for 2025, implementing these strategies can significantly enhance documentation practices, ultimately leading to improved compliance and reduced risks.
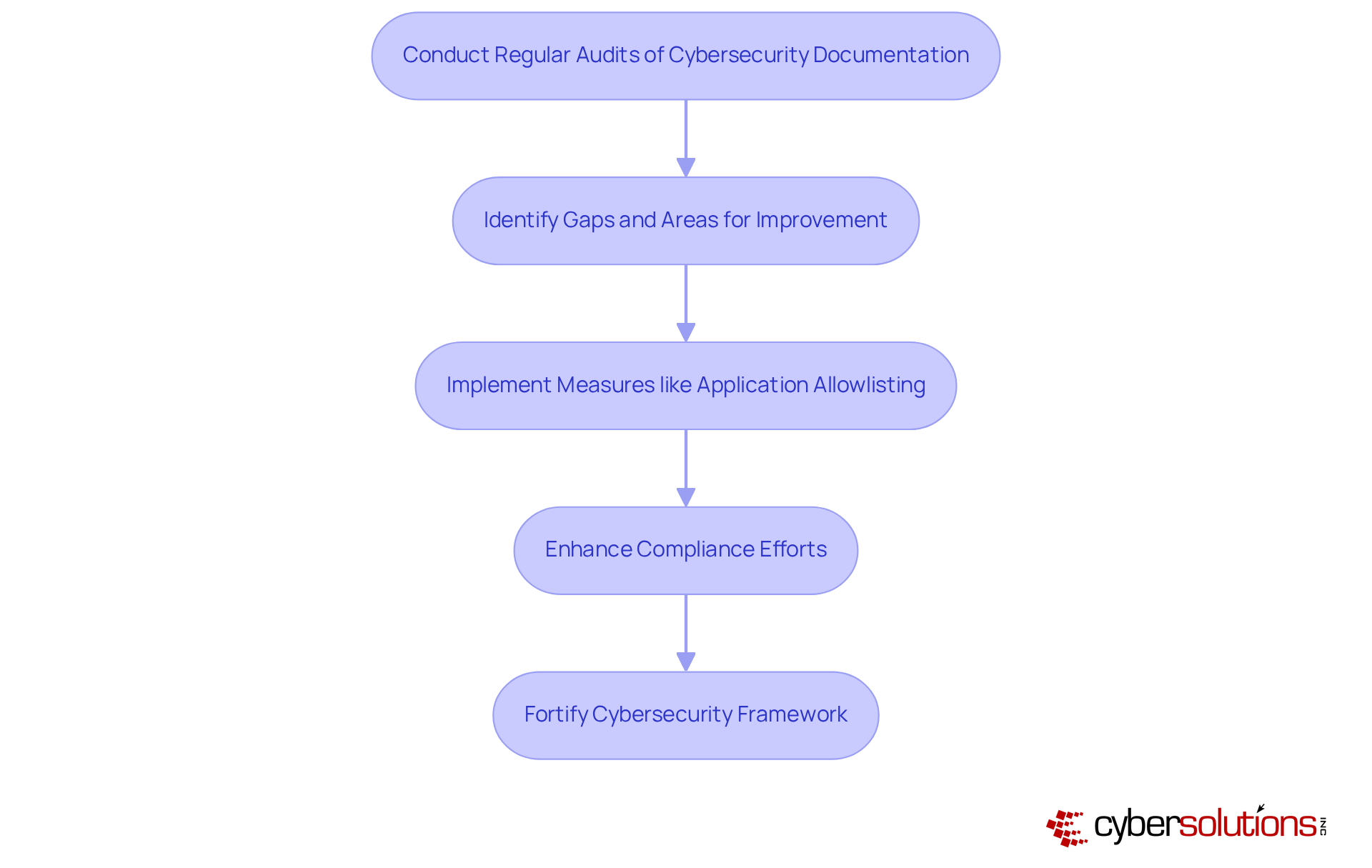
In today's healthcare landscape, regular audits of cybersecurity documentation are essential, not just important. These audits ensure that policies and procedures remain current and effective in the face of ever-evolving threats. By focusing on the relevance and accuracy of records, organizations can identify gaps and areas that need improvement.
Consider this: organizations that conduct structured documentation reviews often uncover shortcomings that, when addressed, enhance overall security. This is crucial, especially when integrating practices like risk management. Such measures can prevent unauthorized software from executing, thereby reducing vulnerabilities and ensuring compliance with regulations.
Centralized management offers features like continuous monitoring of application activity, which further strengthens protection by allowing only authorized applications to run. Comprehensive documentation not only helps organizations meet regulatory standards but also acts as a safeguard against potential breaches.
By committing to regular evaluations and implementing robust protective measures like access controls, companies can fortify their defenses against the ever-changing threat landscape. Are you ready to take action and ensure your organization is protected?
Integrating stakeholder feedback into cybersecurity practices is essential for fostering continuous improvement. By proactively seeking input from staff, management, and external collaborators, organizations can pinpoint opportunities for enhancement and ensure that protective measures effectively address the diverse needs of all stakeholders. This cultivates a culture of collaboration, significantly boosting the effectiveness of cybersecurity practices.
Consider this: companies that engage effectively with stakeholders are more likely to succeed. This statistic underscores the tangible benefits of collaboration. Furthermore, a manufacturing firm that implemented a peer-led 'Champions' program, which involved employees in protective processes, saw a remarkable increase in security awareness within just six months. This clearly illustrates the positive impact of engaging employees in protective initiatives.
Industry leaders consistently emphasize that strong stakeholder engagement can lead to improved financial outcomes. One expert noted that organizations with robust feedback mechanisms are better positioned to adapt to changes. By incorporating stakeholder input into cybersecurity documentation, companies can enhance their resilience against emerging threats and align their security strategies with broader business objectives.

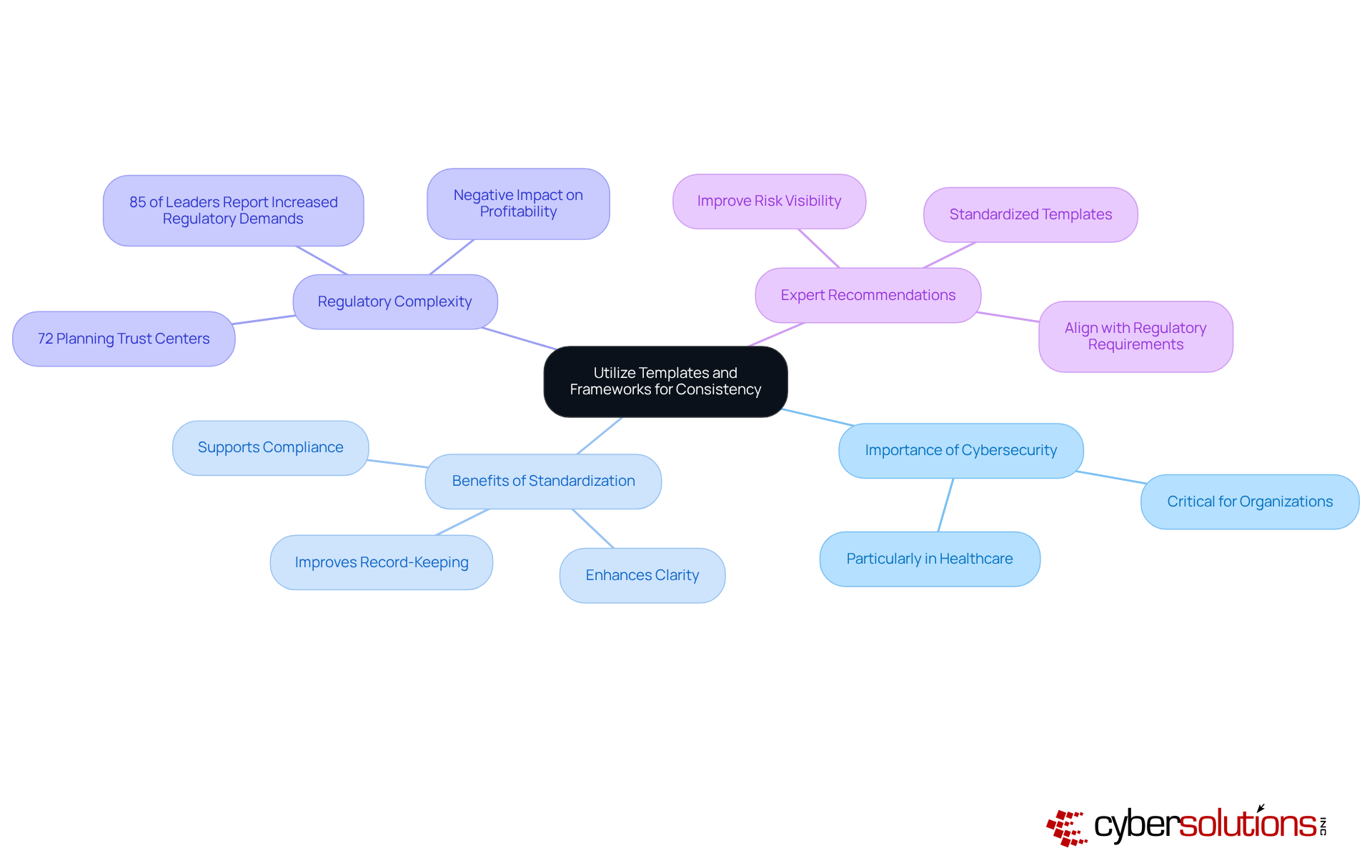
In today’s digital landscape, the importance of cybersecurity cannot be overstated. For organizations, particularly in healthcare, adopting templates and frameworks for documentation is crucial for ensuring consistency and clarity. Standardized formats not only make materials easily understood but also accessible to employees at all levels. This approach simplifies record-keeping and significantly enhances adherence efforts by providing a clear framework for policies and procedures.
Consider this: entities that implement a shared control library can simultaneously prepare for various threats. This capability is increasingly vital, as 85% of leaders report that cybersecurity challenges have become more intricate in recent years. Furthermore, 72% of organizations are either establishing or planning to create Trust Centers for data protection, underscoring the growing recognition of the need for standardized record-keeping practices.
Experts advocate for the use of templates, emphasizing their role in improving and expediting issue detection - both critical in today’s rapidly evolving threat landscape. As Anna Fitzgerald points out, the increasing complexity of regulatory demands has negatively impacted profitability for many enterprises. By leveraging established frameworks, organizations can enhance their documentation practices and align their cybersecurity strategies with regulatory requirements. This alignment not only fosters a culture of compliance and security but also positions organizations to navigate the complexities of the regulatory environment effectively.
Effective cybersecurity documentation stands as a cornerstone for organizations, especially in the healthcare sector, where the protection of sensitive data is non-negotiable. In a landscape fraught with complex regulatory demands, tailored practices empower businesses to navigate these challenges while boosting operational efficiency. The strategies outlined here not only ensure compliance with critical standards but also cultivate a culture of security awareness and accountability among employees.
Key practices include:
These are essential for building a robust cybersecurity framework. Furthermore, organizations must prioritize:
Engaging stakeholders and adopting standardized templates significantly enhance the effectiveness of cybersecurity documentation, ensuring it remains relevant and impactful against evolving threats.
In conclusion, organizations must grasp the importance of effective cybersecurity documentation as a proactive defense against potential cyber threats. By committing to these essential practices, businesses can not only safeguard their sensitive information but also establish a resilient cybersecurity posture that aligns with regulatory requirements. Are you ready to enhance your organization's cybersecurity documentation and protect your assets from future vulnerabilities?
What does Cyber Solutions Inc. specialize in?
Cyber Solutions Inc. specializes in creating tailored cybersecurity procedures for various industries, focusing on helping organizations navigate complex regulatory requirements, particularly in the healthcare sector.
How does Cyber Solutions Inc. assist with compliance?
Cyber Solutions Inc. offers Compliance as a Service (CaaS) solutions that simplify adherence to standards such as HIPAA, PCI-DSS, CMMC, SOX, and GDPR, which are crucial for maintaining patient trust and operational integrity.
What unique challenges do healthcare organizations face regarding cybersecurity?
Healthcare organizations face challenges related to the protection of sensitive patient data, where breaches can have devastating financial and reputational implications.
What services does Cyber Solutions Inc. provide to enhance operational efficiency?
Cyber Solutions Inc. provides comprehensive risk assessments, policy development, and ongoing compliance monitoring to ensure documentation meets compliance requirements and enhances operational efficiency.
What is the purpose of Incident Response services offered by Cyber Solutions Inc.?
The Incident Response services are designed to minimize the impact of cyberattacks by rapidly identifying, containing, and mitigating threats, restoring systems, and ensuring business continuity.
Why is clear information security policy documentation essential?
Clear information security policy documentation is essential for outlining a company's safety objectives and expectations, particularly for safeguarding federal data and adhering to cybersecurity standards.
What percentage of cyber incidents result from human errors?
Approximately 88% of cyber incidents stem from human errors.
How can organizations maintain eligibility for government contracts?
Organizations can maintain eligibility for government contracts by implementing robust data protection measures and ensuring all employees understand and comply with cybersecurity policies.
What is the importance of maintaining comprehensive incident response plans?
Comprehensive incident response plans are crucial for effectively navigating cybersecurity incidents, particularly under HIPAA regulations, and must define roles, responsibilities, and procedures for incident management.
What is emphasized by cybersecurity experts regarding documentation?
Cybersecurity experts emphasize that effective cybersecurity documentation is foundational and that security should be viewed as a culture, not merely a control.
How can organizations improve their incident response planning?
Organizations can improve incident response planning by regularly updating and rigorously testing their documentation, engaging all departments, and conducting ongoing training and simulations.
What is a concerning statistic about organizations evaluating their incident response plans?
Alarmingly, only 30% of organizations evaluate their incident response plans, highlighting the critical need for regular assessments to meet regulatory obligations.