Introduction
In a time when cybersecurity threats are more pronounced than ever, organizations grapple with the formidable challenge of navigating intricate compliance landscapes to protect their operational integrity. The Cybersecurity Maturity Model Certification (CMMC) stands out as a vital framework, setting forth stringent standards that organizations must adhere to in order to safeguard sensitive information and retain eligibility for lucrative government contracts.
This article explores the ten essential CMMC controls that not only pave the way for compliance success but also enhance an organization’s overall cybersecurity posture.
As the stakes escalate, how can entities ensure they are not merely compliant, but also resilient against the ever-evolving threats?
Cyber Solutions: Comprehensive CMMC Compliance Services
In today's rapidly evolving digital landscape, cybersecurity is not just a necessity; it's a critical component of operational integrity, especially for organizations striving to meet stringent compliance standards. Cyber Solutions Inc. stands at the forefront, offering a comprehensive suite of services designed to empower entities in achieving and maintaining cybersecurity excellence.
- 24/7 Help Desk Support: Our dedicated support team is available around the clock, ensuring that compliance-related inquiries are addressed promptly. This continuous assistance allows organizations to tackle issues head-on, maintaining compliance without disruption.
- Incident Response Planning: Developing robust strategies for managing potential security breaches is essential for CMMC adherence. With our expertise, organizations can respond effectively to incidents, minimizing impact and ensuring swift recovery.
- Vulnerability Assessments: Regular evaluations are crucial in identifying system flaws that could jeopardize compliance. By proactively addressing these vulnerabilities, organizations can remediate issues before they escalate into significant problems.
- Co-managed IT Support: Collaborating with internal teams enhances adherence efforts without straining existing resources. This integrated approach to cybersecurity fosters a more cohesive strategy, ensuring that compliance with the cmmc controls list is a shared responsibility.
- Managed Security Services: Continuous oversight and administration of security measures are vital for upholding CMMC standards. Our services guarantee that entities remain vigilant against emerging threats by adhering to the cmmc controls list, thus safeguarding their operations.
- Firewall Management: Maintaining secure network boundaries is a fundamental aspect of compliance. Our firewall management services help entities uphold these critical defenses, ensuring robust protection against unauthorized access.
- User Awareness Training: Educating employees on cybersecurity best practices is essential for minimizing risks. Our training programs empower staff to recognize and respond to potential threats, reinforcing the organization's commitment to compliance.
These services simplify the regulatory process, making it easier for entities to meet the rigorous criteria established by the cmmc controls list. As of 2026, organizations leveraging managed IT assistance have seen a remarkable increase in their adherence success rates, reflecting the nearly 200% growth in Level 2 Certified OSCs within the defense sector over the past six months. This trend underscores the growing importance of integrating comprehensive IT solutions into regulatory strategies.
However, with only 1% of Defense Industrial Base contractors fully prepared for audits, it is imperative for entities to proactively confront regulatory challenges. By partnering with Cyber Solutions Inc., organizations can secure their positions in this dynamic landscape, ensuring they are not just compliant but also resilient against future threats.

Incident Response Controls: Essential for CMMC Compliance
Effective incident response controls are crucial for achieving compliance with the CMMC controls list, particularly regarding Level 2 requirements. Consider the following key components:
- Incident Detection: Organizations must implement robust systems to promptly identify potential security incidents. Did you know that the average time to identify incidents in entities adhering to CMMC is significantly lower than in non-compliant ones? This highlights the importance of proactive detection measures.
- Incident Reporting: Establishing clear protocols for reporting incidents to relevant stakeholders is essential. Engaging key personnel in the reporting process not only fosters a culture of security awareness but also enhances overall detection capabilities.
- Containment Strategies: Developing effective methods to contain incidents quickly minimizes damage and supports business continuity. Organizations that achieve detection under 200 days can save an average of $1.14 million compared to those with longer detection cycles. This underscores the financial benefits of swift containment.
- Post-Incident Analysis: Conducting thorough reviews after incidents is vital for improving future response efforts. This analysis helps entities refine their incident response strategies, ensuring they are better prepared for future threats.
Real-world examples underscore the necessity of these controls. Recent events have shown that entities lacking effective incident response plans face prolonged recovery times and increased expenses. As the cybersecurity landscape evolves, particularly with ransomware attacks occurring every 19 seconds worldwide, organizations must ensure their incident response plans are well-documented and regularly tested to comply with the CMMC controls list.

Identification and Authentication Controls: Key to CMMC Success
In today's digital landscape, the importance of robust cybersecurity measures cannot be overstated, especially in the healthcare sector where sensitive data is at stake. Identification and authentication controls are vital for safeguarding sensitive data and ensuring that only authorized users gain access, particularly when it comes to protecting Controlled Unclassified Information (CUI) and Federal Contract Information (FCI). Here are key practices that every organization should implement:
- Unique User IDs: Assigning distinct identifiers to each user is crucial for tracking access and actions. This practice enhances accountability within the organization and ensures compliance with stringent cybersecurity standards.
- Strong Password Policies: Enforcing complex password requirements significantly boosts security. Research shows that approximately 67% of companies face challenges due to employees using weak passwords. Moreover, 81% of hacking-related breaches exploit either stolen or weak passwords, underscoring the necessity of robust password policies to maintain eligibility for lucrative government contracts.
- Multi-Factor Authentication (MFA): Implementing MFA adds an essential layer of security beyond traditional passwords. This method is particularly important for achieving security standards, as it mitigates risks associated with compromised or weak passwords. Entities employing MFA can greatly reduce the chances of unauthorized access, making it a recommended approach in cybersecurity.
Regular Access Reviews, which involve conducting periodic audits of user access, are vital for maintaining compliance with the CMMC controls list. These evaluations ensure that only authorized individuals retain access to confidential information, further strengthening the entity's security posture and commitment to enhancing cybersecurity measures.
These controls not only protect sensitive information but also demonstrate a company's commitment to adhering to cybersecurity best practices. As Sean Blanton emphasizes, "Writing and enforcing password policies is one of the best first lines of defense against hackers," highlighting the necessity of these practices. To effectively implement these measures, companies should consider utilizing password managers and conducting regular password audits.

System and Communications Protection Controls: Safeguarding Data
To achieve compliance with CMMC, organizations must implement robust system and communications protection controls, which include:
- Boundary Protection: Monitoring and controlling communications at system boundaries is essential to prevent unauthorized access. Effective boundary protection safeguards sensitive information from external threats, ensuring that your organization remains secure.
- Data Encryption: Encrypting sensitive data both in transit and at rest is vital to protect against interception. Current information shows that 97% of data protection officers employ end-to-end encryption to safeguard data, emphasizing its significance in regulatory efforts. As noted by industry experts, "End-to-end encryption is essential for protecting sensitive information from unauthorized access during transmission."
- Access Control Mechanisms: Implementing strict access controls is crucial to limit who can access sensitive systems and data. This ensures that only authorized personnel can interact with critical information, significantly reducing the risk of data breaches.
- Regular Security Assessments: Conducting regular assessments helps identify and address vulnerabilities in systems and communications. Ongoing monitoring is essential to adjust to emerging threats and uphold regulatory readiness. Organizations should contemplate performing a CMMC controls list, ensuring they efficiently achieve compliance with required regulations.
These measures are fundamental for maintaining the confidentiality and integrity of sensitive information, particularly in the context of evolving regulatory requirements and the increasing sophistication of cyber threats. Reaching Level 3 certification not only enhances your entity's cybersecurity stance but also secures federal contracts, showcasing a dedication to safeguarding Controlled Unclassified Information (CUI) and Federal Contract Information (FCI). Furthermore, by achieving CMMC certification, organizations gain a competitive advantage in the defense contracting industry.
Moreover, creating a cross-functional team to supervise adherence efforts can improve collaboration and efficiency in applying these controls. Consider setting up regular training sessions to keep your team informed and engaged in regulatory procedures.

Control Validation: Ensuring Compliance with CMMC Standards
Control validation is crucial for ensuring that security measures are effective and compliant with the CMMC controls list, particularly in safeguarding Controlled Unclassified Information (CUI) and Federal Contract Information (FCI). The following key steps are essential in this process:
- Regular Testing: Conducting tests of security controls is vital to verify their effectiveness. Organizations that prioritize regular testing can better identify vulnerabilities and enhance their security posture. Significantly, only 49% of entities characterize their adherence initiatives as developed and effective, underscoring the need for improvement in testing methods.
- Documentation Review: Keeping control documentation current and accurately reflecting implemented measures is crucial. Efficient documentation practices correlate with increased adherence rates, as entities that frequently assess their documentation are better prepared for audits.
- Audit Trails: Maintaining comprehensive logs of access and modifications to systems supports audits and helps entities monitor compliance over time. This method is critical for demonstrating adherence to the CMMC controls list and ensuring eligibility for lucrative government contracts.
- Continuous Monitoring: Implementing tools for continuous monitoring enables entities to detect signs of failure or compromise in real-time. Ongoing observation is increasingly recognized as a best practice for upholding regulations, allowing for proactive responses to potential threats.
Entities that delay readiness for 2.0 may face operational disruptions and potential loss of contracts. Frequent validation not only helps organizations identify shortcomings in their adherence efforts but also ensures timely corrective actions, ultimately fostering ongoing compliance with required standards. The typical yearly audit preparation cost per entity is $210,000, highlighting the financial implications of inadequate adherence practices. Therefore, for contractors, the message is clear: begin preparations now, before compliance requirements arise in a contract.

Domain Grouping: Streamlining CMMC Control Implementation
Cybersecurity is paramount in today’s healthcare landscape, where threats are ever-evolving and increasingly sophisticated. Domain grouping serves as a tactical method for applying the cmmc controls list, enabling organizations to focus on specific regulatory areas that are crucial for compliance and security. The key domains include:
- Access Control: This domain encompasses measures designed to restrict access to sensitive information, ensuring that only authorized personnel can view or manipulate critical data. Effective access control is vital for safeguarding sensitive information and is a foundational element of CMMC compliance.
- Incident Response: This domain outlines protocols for managing security incidents, detailing the steps entities must take to detect, respond to, and recover from breaches. A well-defined incident response plan can significantly reduce the impact of security incidents, with breaches contained within 200 days costing an average of $1.14 million less than those with longer dwell times.
- System Integrity: This domain focuses on ensuring that systems are secure and functioning as intended. Regular audits and monitoring are essential to maintain system integrity, as 60% of cybersecurity breaches involve human factors, highlighting the need for ongoing vigilance.
- Media Protection: This domain emphasizes the safeguarding of both physical and digital media that contains sensitive information. Implementing strong media protection measures is essential, particularly as entities encounter rising threats from data breaches, with 74% of breaches involving human elements.
By organizing the cmmc controls list into these areas, organizations can prioritize their regulatory efforts and allocate resources more efficiently. This organized strategy not only improves adherence readiness but also aligns with best practices recognized by cybersecurity leaders, ensuring that healthcare organizations are well-prepared to meet requirements.

CMMC Level 2 Requirements: What You Need to Know
In today's digital landscape, safeguarding Controlled Unclassified Information (CUI) is paramount for organizations, particularly in the healthcare sector. CMMC Level 2 requirements are designed to bolster cybersecurity measures, focusing on the following critical areas:
- 110 Security Controls: Organizations must implement all 110 controls outlined in NIST SP 800-171 to ensure robust protection of sensitive information.
- Documentation: Comprehensive documentation of security policies and procedures is crucial. This includes a complete System Security Plan (SSP) that details the implementation and maintenance of each control.
- Regular Assessments: Conducting self-evaluations is essential for verifying adherence to all controls and identifying areas for improvement.
- Incident Response Plans: Developing and rigorously testing incident response plans is vital for swiftly addressing potential breaches.
In addition to these requirements, entities should adopt application allowlisting as a proactive measure to enhance their cybersecurity posture. By preventing unauthorized or malicious applications from executing, application allowlisting effectively reduces the attack surface and minimizes vulnerabilities. This approach not only protects sensitive information but also ensures compliance with regulatory standards such as HIPAA, PCI-DSS, and GDPR. Understanding these requirements and the role of application allowlisting is essential for entities aiming to maintain eligibility for DoD contracts.

CMMC Level 2 vs. Level 1: Understanding the Differences
Use english for answers
Navigating CMMC Levels: A Critical Imperative for Organizations
In today’s landscape, cybersecurity is not just a necessity; it’s a critical imperative for organizations aiming to secure government contracts. CMMC Level 1 lays the groundwork with 17 essential practices focused on basic cybersecurity hygiene, specifically designed to protect Federal Contract Information (FCI). Compliance is straightforward, requiring an annual self-assessment and affirmation submitted in the Supplier Performance Risk System (SPRS). Alarmingly, only 1% of contractors are currently CMMC-ready, underscoring the urgent need for organizations to prepare for compliance. Meeting stringent cybersecurity standards is vital for safeguarding Controlled Unclassified Information (CUI) and FCI, which is essential for maintaining eligibility for lucrative government contracts.
Transitioning to Level 2: A Comprehensive Approach
Conversely, CMMC Level 2 presents a more robust framework, incorporating 110 practices aligned with NIST SP 800-171, with a focus on protecting CUI. Achieving Level 2 compliance necessitates a formal third-party evaluation, making it crucial for organizations that handle sensitive data. Typically, the preparation period for CMMC certification ranges from 12 to 18 months, highlighting the importance of early action to mitigate risks associated with delayed compliance efforts. Organizations must critically assess their data handling practices to determine the appropriate level of adherence required for their operations.
As we look toward 2026, the landscape is evolving, with many contractors recognizing the importance of early preparation to avoid the pitfalls of postponed compliance. Those advancing from Level 1 to Level 2 are often motivated by the competitive advantage gained through enhanced security measures and readiness, positioning themselves favorably in the defense contracting market. Additionally, the challenges of documentation and the existing readiness gap further emphasize the need for proactive compliance strategies.

Self-Assessment for CMMC Level 2: Steps to Compliance
Conducting a self-assessment for CMMC Level 2 is not just a regulatory requirement; it’s a vital step in safeguarding your organization’s future. With the increasing complexity of cybersecurity threats, understanding and adhering to compliance standards is essential for any organization handling Controlled Unclassified Information (CUI).
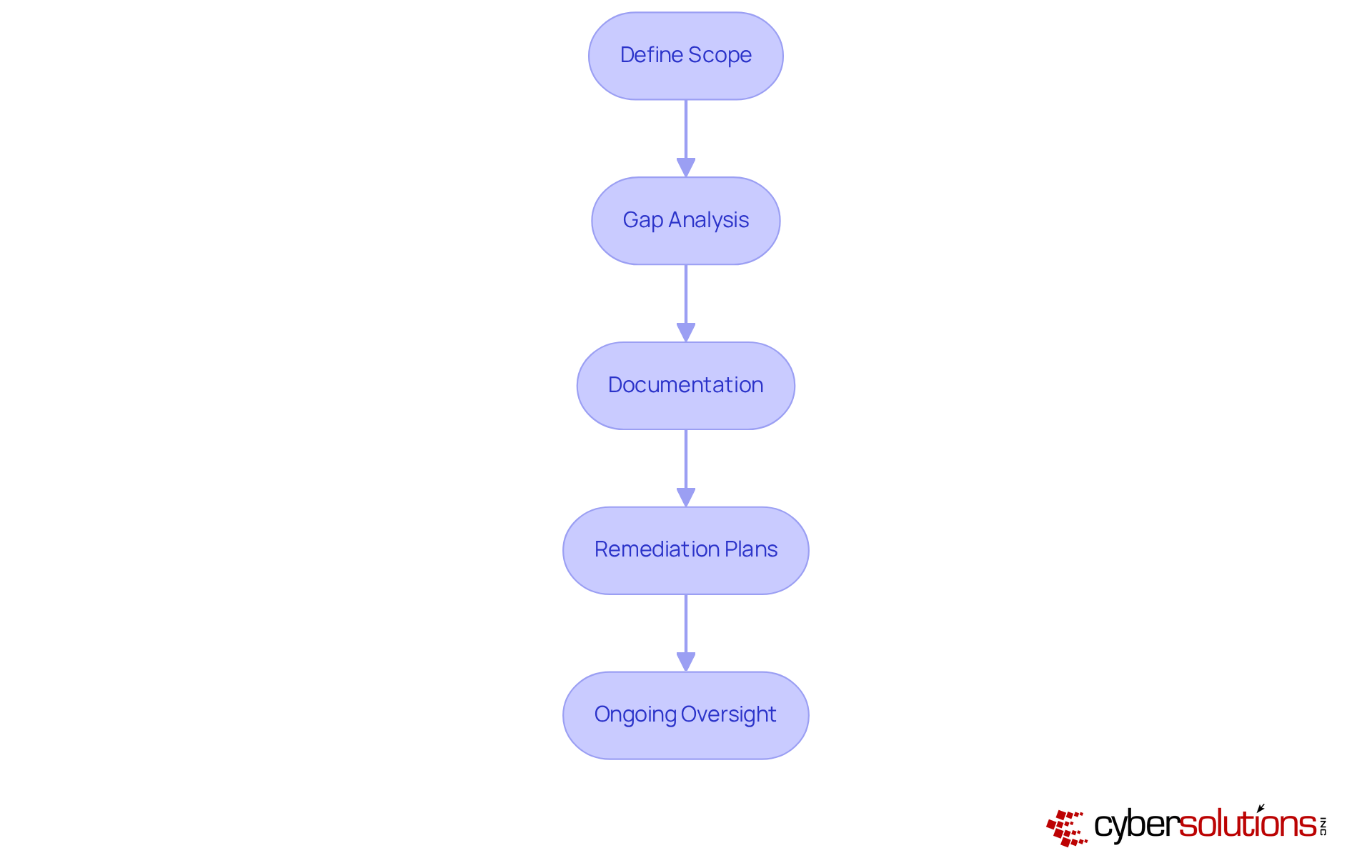
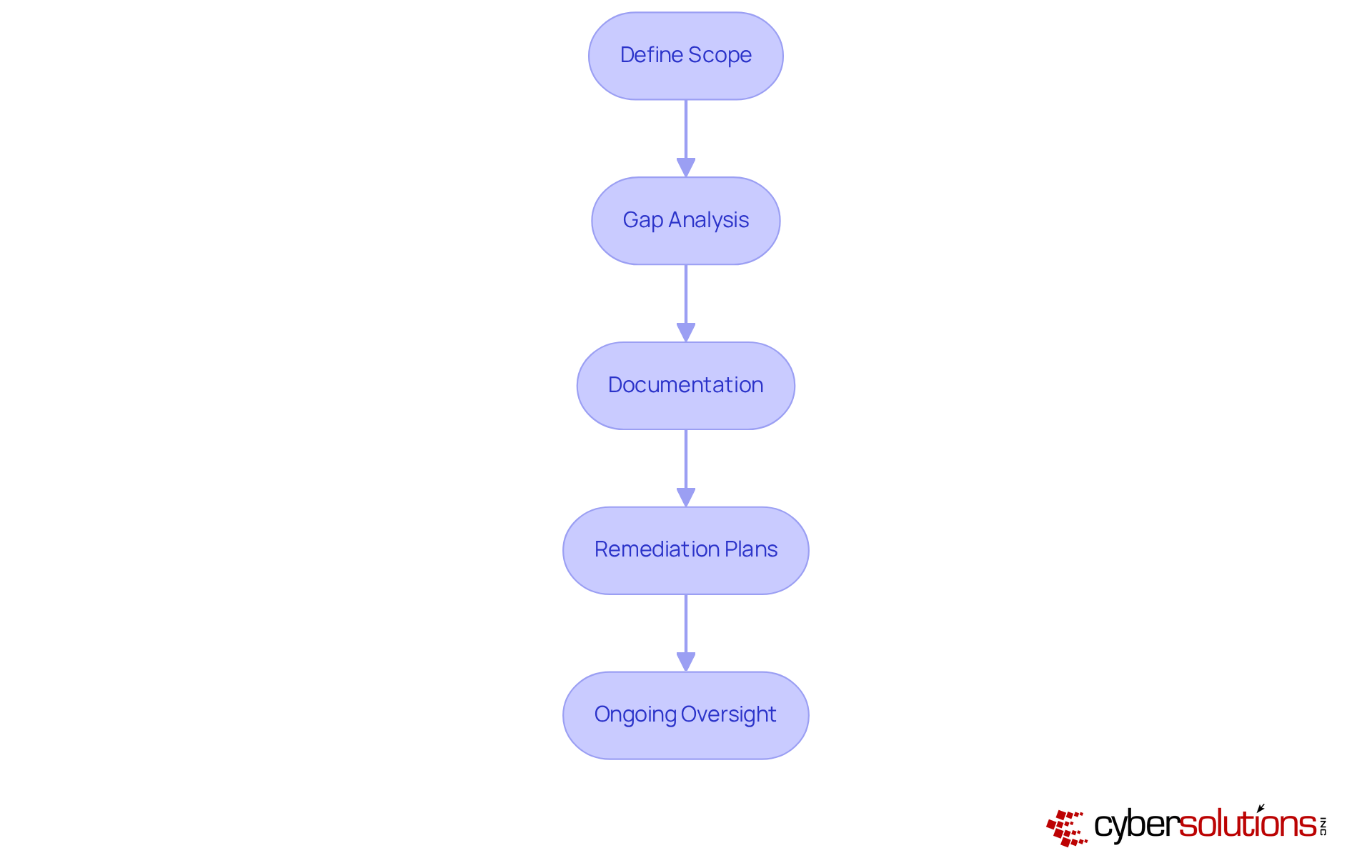
- Define Scope: Start by clearly identifying all systems and processes that manage CUI. This foundational step is crucial for grasping the full extent of regulatory requirements and ensuring that no critical area is overlooked.
- Gap Analysis: Next, conduct a thorough evaluation of your current practices against Level 2 requirements. This analysis is essential, especially considering that nearly one-third of contractors are unaware of which cybersecurity maturity model level applies to them. Identifying shortcomings early on can clarify your adherence efforts and set the stage for effective remediation.
- Documentation: Collect and organize all relevant documentation related to your security controls and policies. Keeping precise records is vital for demonstrating compliance during evaluations. Prepare comprehensive documentation, including security policies, procedures, and supporting evidence, as outlined in Cyber Solutions' proven process. This preparation will showcase your commitment to compliance during audits.
- Remediation Plans: Develop tailored remediation strategies to address any identified gaps before the formal assessment. This may include policy updates, system upgrades, and process improvements. Organizations that delay remediation risk facing increased costs and operational disruptions; in fact, 50% of assessors report turning away clients due to readiness gaps. Conducting a mock audit can also ensure your organization is fully prepared for the official CMMC assessment, addressing any remaining issues.
Ongoing oversight of changes in the compliance framework is crucial for maintaining adherence over time. Frequent self-evaluations not only help organizations stay aligned with regulatory efforts but also prepare them for external assessments, which are increasingly essential as CMMC requirements evolve. Engaging in proactive adherence measures can significantly enhance your organization’s preparedness and mitigate risks associated with non-conformance. As emphasized by the Department of Defense, cybersecurity compliance is now a gating factor for DoD contract eligibility, making timely preparation not just important, but essential.
Penalties for Non-Compliance: The Risks of Ignoring CMMC Controls
Organizations that neglect compliance standards face severe repercussions that can threaten their operational viability and market position. The penalties are significant and multifaceted:
- Loss of Contracts: Non-compliance can render organizations ineligible for bidding on or retaining Department of Defense (DoD) contracts, effectively cutting off access to lucrative government opportunities. For example, contractors failing to meet CMMC Level 2 certification requirements risk having their proposals deemed non-responsive, leading to immediate disqualification from the bidding process.
- Financial Penalties: The financial fallout from non-compliance can be staggering. Organizations may incur fines ranging from thousands to millions of dollars, especially if they misrepresent their compliance status. Legal actions under the False Claims Act can impose penalties that are triple the amount of the contract payments, underscoring the high stakes involved.
- Reputational Damage: Beyond immediate financial losses, non-compliance can inflict lasting harm on an organization’s reputation. Companies that do not adhere to CMMC standards may struggle to regain trust with prime contractors and clients, hindering future business opportunities.
- Legal Consequences: Misrepresentation of adherence status can lead to significant legal repercussions. Under the Department of Justice’s Civil Cyber-Fraud Initiative, contractors that inaccurately self-assess their cybersecurity posture may face severe penalties, including treble damages and civil fines.
Understanding these risks is crucial for organizations aiming to prioritize their regulatory efforts and safeguard their business interests in an increasingly regulated environment. As industry leaders emphasize, ignoring the CMMC controls list is not just a compliance issue; it represents a substantial business risk that can result in lost opportunities and legal liabilities.

Conclusion
Achieving compliance with the CMMC controls list is not just a regulatory obligation; it’s a strategic necessity for organizations determined to protect sensitive information and secure government contracts. In today’s complex cybersecurity landscape, the comprehensive suite of controls outlined here serves as a vital roadmap for entities looking to bolster their cybersecurity posture. By prioritizing these essential controls, organizations can position themselves as resilient competitors in an increasingly challenging environment.
Key areas of focus include:
- Incident response planning
- Identification and authentication controls
- System and communications protection
- The critical importance of continuous monitoring and control validation
Each of these elements is crucial for safeguarding Controlled Unclassified Information (CUI) and ensuring that organizations are audit-ready. Furthermore, the growing emphasis on proactive compliance strategies highlights the necessity for organizations to address vulnerabilities before they escalate into significant risks.
As the cybersecurity landscape evolves, the need for organizations to adopt a proactive approach to CMMC compliance cannot be overstated. Engaging in thorough self-assessments, implementing robust security measures, and fostering a culture of compliance will not only mitigate risks but also enhance an organization’s reputation and competitive edge. Organizations must take immediate action to evaluate their current practices against the CMMC controls list, ensuring they are not only compliant but also prepared to thrive in a landscape where cybersecurity is paramount.
Frequently Asked Questions
What services does Cyber Solutions Inc. offer for CMMC compliance?
Cyber Solutions Inc. offers a comprehensive suite of services including 24/7 help desk support, incident response planning, vulnerability assessments, co-managed IT support, managed security services, firewall management, and user awareness training to help organizations achieve and maintain cybersecurity excellence.
How does 24/7 help desk support benefit organizations?
The dedicated support team is available around the clock to address compliance-related inquiries promptly, allowing organizations to tackle issues head-on and maintain compliance without disruption.
What is the importance of incident response planning in CMMC compliance?
Incident response planning is essential for managing potential security breaches effectively, minimizing impact, and ensuring swift recovery, which is crucial for adhering to CMMC standards.
Why are vulnerability assessments necessary for organizations?
Regular evaluations help identify system flaws that could jeopardize compliance, allowing organizations to proactively address vulnerabilities before they escalate into significant problems.
How does co-managed IT support enhance compliance efforts?
Co-managed IT support collaborates with internal teams to enhance adherence efforts without straining existing resources, fostering a cohesive cybersecurity strategy and shared responsibility for compliance.
What role do managed security services play in CMMC compliance?
Managed security services provide continuous oversight and administration of security measures, ensuring organizations remain vigilant against emerging threats and adhere to CMMC standards.
What is the significance of firewall management in maintaining compliance?
Firewall management is crucial for maintaining secure network boundaries, helping organizations protect against unauthorized access and uphold compliance with CMMC requirements.
How does user awareness training contribute to cybersecurity?
User awareness training educates employees on cybersecurity best practices, empowering them to recognize and respond to potential threats, thereby reinforcing the organization’s commitment to compliance.
What trends have been observed regarding CMMC compliance in the defense sector?
As of 2026, organizations leveraging managed IT assistance have seen a significant increase in adherence success rates, with nearly 200% growth in Level 2 Certified OSCs within the defense sector over the past six months.
What are the key components of effective incident response controls for CMMC compliance?
Key components include incident detection, incident reporting, containment strategies, and post-incident analysis, all of which are vital for improving response efforts and achieving compliance.
Why is incident detection important for organizations?
Implementing robust systems for incident detection allows organizations to promptly identify potential security incidents, significantly reducing the average time to detect incidents compared to non-compliant entities.
What financial benefits are associated with swift incident containment?
Organizations that achieve detection under 200 days can save an average of $1.14 million compared to those with longer detection cycles, highlighting the financial incentives for effective incident response.
What practices should organizations implement for identification and authentication controls?
Organizations should assign unique user IDs, enforce strong password policies, implement multi-factor authentication (MFA), and conduct regular access reviews to safeguard sensitive data and maintain compliance.
How do strong password policies impact cybersecurity?
Enforcing complex password requirements helps prevent breaches, as approximately 81% of hacking-related incidents exploit stolen or weak passwords, making robust password policies essential for compliance.
What is the role of multi-factor authentication (MFA) in cybersecurity?
MFA adds an essential layer of security beyond traditional passwords, significantly reducing the risk of unauthorized access and enhancing compliance with security standards.
List of Sources
- Cyber Solutions: Comprehensive CMMC Compliance Services
- Why CMMC compliance may matter for your company in 2026 (https://integrisit.com/blog/why-cmmc-compliance-may-matter-for-your-company-in-2026)
- CMMC Compliance in 2026: How Did We Get Here and What’s Coming Next (https://112cyber.com/blog/cmmc-compliance-in-2026)
- 2026 GAO Report Finds Critical Concerns with CMMC Ecosystem | Alluvionic (https://alluvionic.com/2026-gao-report-finds-critical-concerns-with-cmmc-ecosystem)
- CMMC 2.0 in 2026: What Defense Contractors Must Do Now (https://trustconsultingservices.com/cmmc-2-0-in-2026-defense-compliance-guide)
- CMMC 2.0 in 2026: What’s New and What Organizations Must Know - Accorian (https://accorian.com/cmmc-2-0-in-2026-whats-new-and-what-organizations-must-know)
- Incident Response Controls: Essential for CMMC Compliance
- Average Time to Detect a Cyber Attack 2025: Critical Detection Statistics Every Business Must Know (https://totalassure.com/blog/average-time-to-detect-cyber-attack-2025)
- Essential Metrics for Effective Incident Response Strategies (https://cybercentaurs.com/blog/essential-metrics-for-effective-incident-response-strategies)
- 205 Cybersecurity Stats and Facts for 2026 (https://vikingcloud.com/blog/cybersecurity-statistics)
- Navigating CMMC Compliance Now That It’s 2026 - Helixstorm (https://helixstorm.com/compliance/navigating-cmmc-compliance-now-that-its-2026)
- Identification and Authentication Controls: Key to CMMC Success
- How Strong Passwords Protect Your Data | CSA (https://cloudsecurityalliance.org/blog/2024/10/18/a-look-at-strong-password-practices-a-shield-for-your-digital-life)
- Password Hygiene Stats: How Weak Are Most Passwords? (https://patentpc.com/blog/password-hygiene-stats-how-weak-are-most-passwords)
- Why strong passwords and MFA are crucial for cybersecurity | Don J. posted on the topic | LinkedIn (https://linkedin.com/posts/jamieson-don_weak-passwords-remain-a-significant-source-activity-7338656537151795200-i1Cz)
- 50+ Password Statistics & Trends to Know in 2024 (https://jumpcloud.com/blog/password-statistics-trends)
- 36 Must-Know Password Statistics for 2026 | Huntress (https://huntress.com/blog/password-statistics)
- System and Communications Protection Controls: Safeguarding Data
- New cybersecurity rules for US defense industry create barrier for some small suppliers (https://reuters.com/business/aerospace-defense/new-cybersecurity-rules-us-defense-industry-create-barrier-for-some-small-2026-02-20)
- Data Privacy Statistics: US 2025 | Infrascale (https://infrascale.com/data-privacy-statistics-usa)
- CMMC 2.0 in 2026: What Defense Contractors Must Do Now (https://trustconsultingservices.com/cmmc-2-0-in-2026-defense-compliance-guide)
- Achieve CMMC Compliance Effectively (https://infotech.com/research/ss/achieve-cmmc-compliance-effectively)
- CMMC 2.0 Governance Crisis: Data Shows 62% of Defense Contractors Lack Critical Controls for Certification Success (https://kiteworks.com/cmmc-compliance/over-half-dod-cmmc-suppliers-fail-governance)
- Control Validation: Ensuring Compliance with CMMC Standards
- 2026 GAO Report Finds Critical Concerns with CMMC Ecosystem | Alluvionic (https://alluvionic.com/2026-gao-report-finds-critical-concerns-with-cmmc-ecosystem)
- CMMC 2.0 in 2026: What Defense Contractors Must Do Now (https://trustconsultingservices.com/cmmc-2-0-in-2026-defense-compliance-guide)
- 280+ Cybersecurity Compliance Statistics for 2026 (https://brightdefense.com/resources/cybersecurity-compliance-statistics)
- CMMC 2.0 Governance Crisis: Data Shows 62% of Defense Contractors Lack Critical Controls for Certification Success (https://kiteworks.com/cmmc-compliance/over-half-dod-cmmc-suppliers-fail-governance)
- 100+ Compliance Statistics You Should Know in 2025 (https://sprinto.com/blog/compliance-statistics)
- Domain Grouping: Streamlining CMMC Control Implementation
- CMMC 2.0 in 2026: What Defense Contractors Must Do Now (https://trustconsultingservices.com/cmmc-2-0-in-2026-defense-compliance-guide)
- huntress.com (https://huntress.com/cmmc-compliance-guide/cmmc-controls)
- 110 security and compliance statistics for tech leaders to know in 2025 (https://vanta.com/resources/compliance-statistics)
- drata.com (https://drata.com/blog/compliance-statistics)
- secureframe.com (https://secureframe.com/blog/compliance-statistics)
- CMMC Level 2 Requirements: What You Need to Know
- Navigating CMMC Changes in 2026: What You Need to Know (https://vc3.com/blog/navigating-cmmc-changes-in-2026)
- CMMC Basics: A Practical 2026 Roadmap for CMMC Compliance (https://securitymetrics.com/blog/cmmc-compliance-roadmap)
- CMMC 2.0 Certification: DoD Contractor Guide for 2026 (https://elevateconsult.com/insights/cmmc-2-0-certification-for-dod-contractors-what-you-need-to-know-before-2026-deadlines)
- CMMC Level 2 in 2026: The Clock Is Ticking and the Line Is Already Long - CMMC Compliance (https://cmmccompliance.us/cmmc-level-2-in-2026-the-clock-is-ticking-and-the-line-is-already-long)
- CMMC 2.0 in 2026: What Defense Contractors Must Do Now (https://trustconsultingservices.com/cmmc-2-0-in-2026-defense-compliance-guide)
- CMMC Level 2 vs. Level 1: Understanding the Differences
- CMMC Level 1 vs Level 2: What You Need to Know for Compliance (https://bitlyft.com/resources/cmmc-level-2-vs-level-1-whats-the-difference-and-why-it-matters)
- Only 1% of DIB Contractors Are CMMC-Ready: What the Data Tells Us (https://deepfathom.ai/articles/cmmc-readiness-statistics)
- What small government contractors need to know about CMMC and FOCI - UCEDC (https://ucedc.com/what-small-government-contractors-need-to-know-about-cmmc-and-foci)
- CMMC Level 1 vs Level 2: Compliance Impact for DoD Contractors | MAD Security posted on the topic | LinkedIn (https://linkedin.com/posts/madsecurity_madsecurity-cmmc-cyberdefense-activity-7424855578096672768-jCai)
- CMMC 2.0 Compliance Levels Explained (Level 1, 2, 3) | Huntress (https://huntress.com/cmmc-compliance-guide/cmmc-compliance-levels)
- Self-Assessment for CMMC Level 2: Steps to Compliance
- 2026 GAO Report Finds Critical Concerns with CMMC Ecosystem | Alluvionic (https://alluvionic.com/2026-gao-report-finds-critical-concerns-with-cmmc-ecosystem)
- CMMC 2.0 in 2026: What Defense Contractors Must Do Now (https://trustconsultingservices.com/cmmc-2-0-in-2026-defense-compliance-guide)
- CMMC Compliance in 2026: How Did We Get Here and What’s Coming Next (https://112cyber.com/blog/cmmc-compliance-in-2026)
- CMMC - The True Cost of CMMC 2.0: Budget Breakdown by Level [2026] (https://cmmc.com/newsroom/cost-of-cmmc)
- CMMC Phase 2: What to Expect and How to Prepare [2026] (https://secureframe.com/blog/cmmc-phase-2-preparation)
- Penalties for Non-Compliance: The Risks of Ignoring CMMC Controls
- 2026 GAO Report Finds Critical Concerns with CMMC Ecosystem | Alluvionic (https://alluvionic.com/2026-gao-report-finds-critical-concerns-with-cmmc-ecosystem)
- The True Cost of CMMC Non-Compliance (https://3blmedia.com/news/true-cost-cmmc-non-compliance)
- $4.6M warning shot: DOJ ramps up cyber enforcement on defense contractors (https://defenseandmunitions.com/article/46m-warning-shot-doj-ramps-up-cmmc-enforcement-on-defense-contractors-sse)
- What Happens if You Ignore CMMC in 2026? (https://isidefense.com/blog/what-happens-if-you-ignore-cmmc-in-2026)
- The True Cost of a CMMC Non-Compliance Finding - VSO (https://vso-inc.com/the-true-cost-of-a-cmmc-non-compliance-finding)