
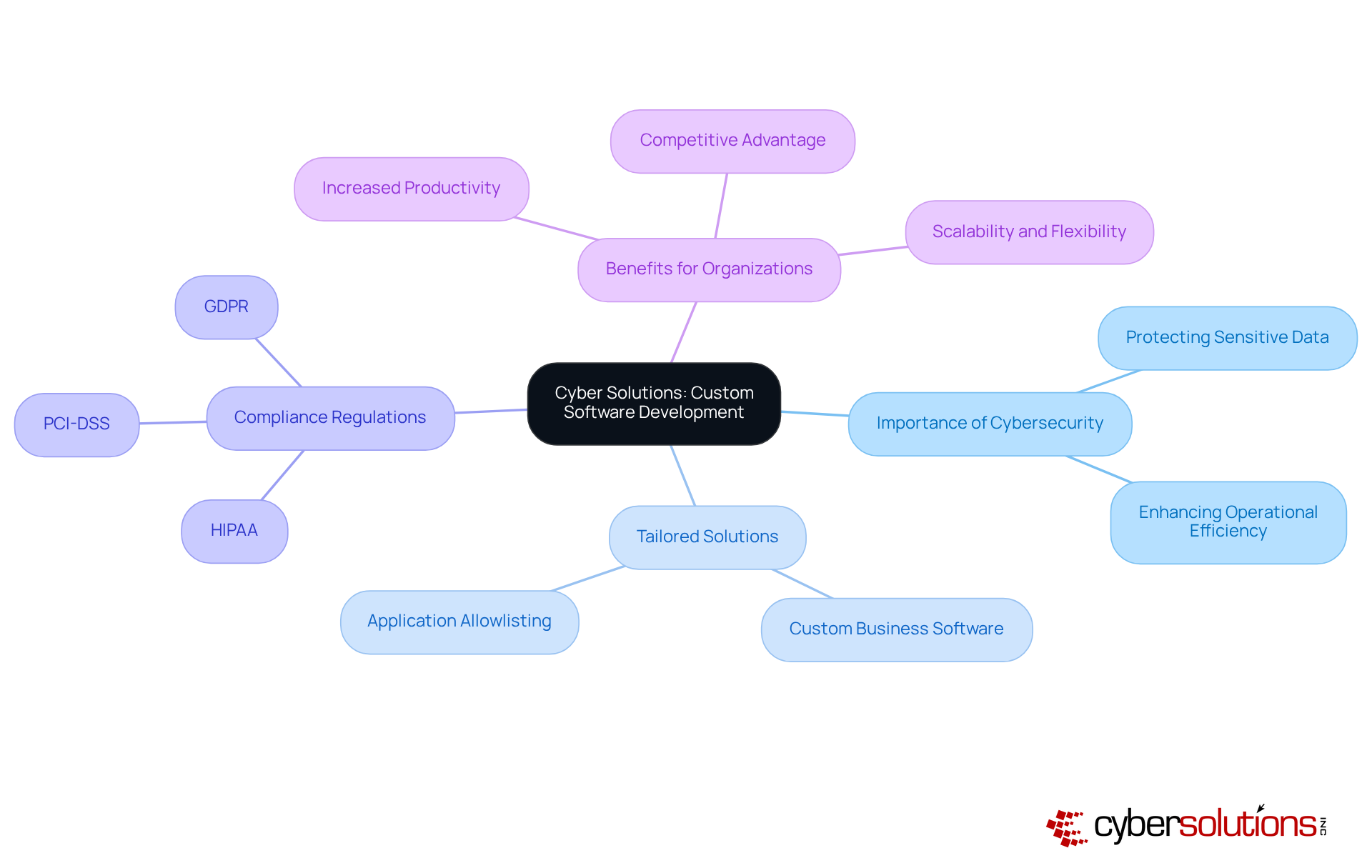
In an era where digital transformation is not merely an option but an imperative, C-suite leaders confront the urgent challenge of ensuring their organizations remain both competitive and secure. Custom business software emerges as a pivotal solution, providing tailored functionalities that align seamlessly with unique operational needs.
As the landscape evolves, one must consider: how can these bespoke solutions not only streamline processes but also enhance decision-making and fortify cybersecurity?
Delving into the compelling reasons for investing in custom software reveals a pathway to not only meet current demands but also to future-proof businesses against emerging challenges.
In today's rapidly evolving digital landscape, the significance of cybersecurity cannot be overstated, particularly within the healthcare sector. Cyber Solutions Inc. stands at the forefront of addressing the challenges by developing software that is meticulously tailored to meet their distinct needs. By gaining a comprehensive understanding of the specific obstacles that healthcare providers encounter, Cyber Solutions creates bespoke applications that not only enhance efficiency but also bolster security measures.
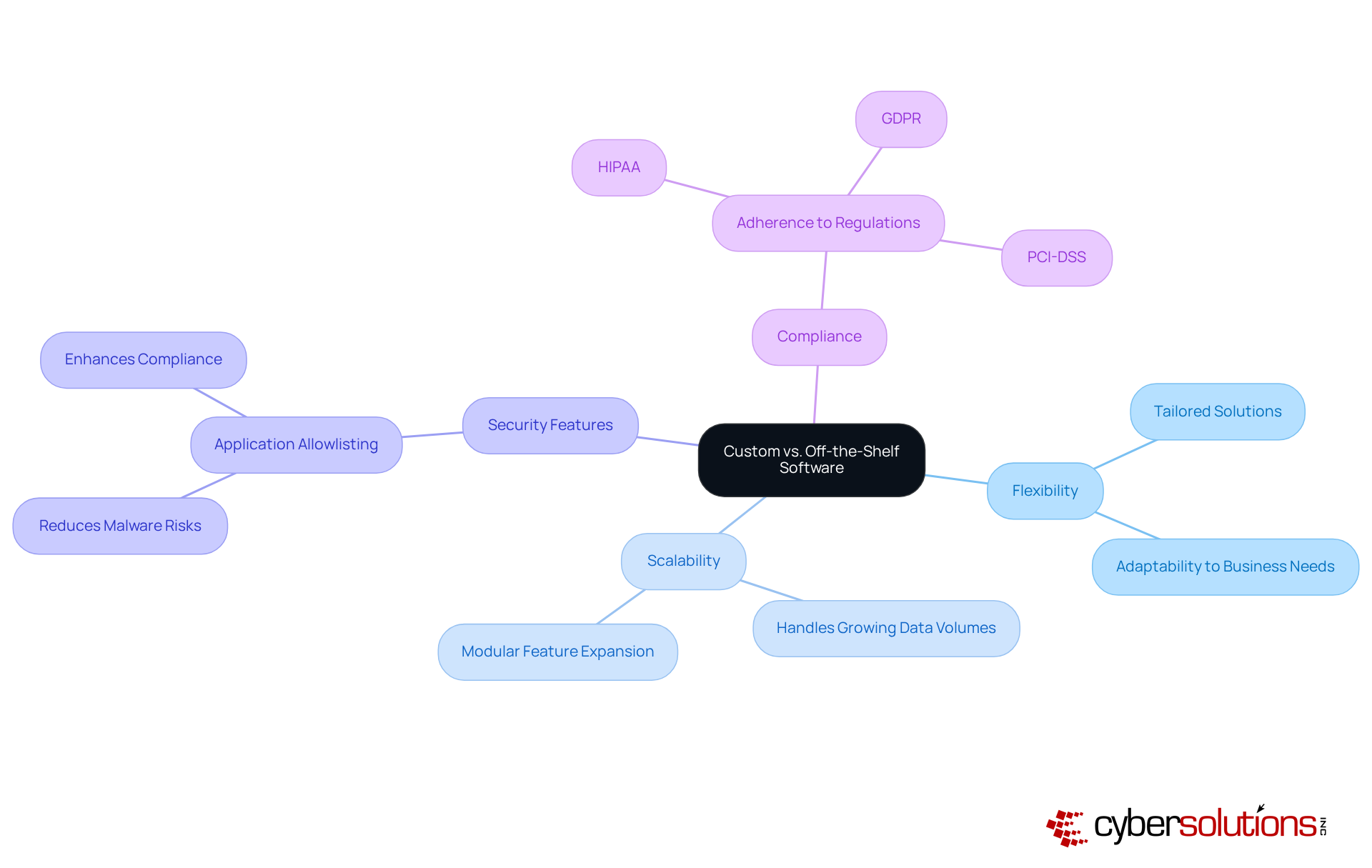
This personalized approach streamlines workflows, optimizes data management, and ensures compliance with stringent industry regulations, including GDPR.
One pivotal aspect of our security framework is application whitelisting, which proactively prevents unauthorized applications from executing. This not only safeguards sensitive data but also reinforces compliance with these critical regulations.
As the demand for personalized applications surges—forecasts indicate that up to 70% of new enterprise programs will be developed using Low Code/No Code platforms by 2025—organizations are increasingly recognizing the necessity of investing in custom solutions. Industry leaders assert that such investments can yield significant returns. By leveraging custom software, companies can enhance their operations, adapt to market fluctuations, and maintain a competitive edge in an ever-changing environment.
Moreover, integrating security measures, such as tailored risk assessments, is essential. This ensures that custom approaches not only meet operational needs but also protect sensitive information effectively. As organizations navigate the complexities of cybersecurity, Cyber Solutions Inc. offers the expertise and innovative solutions necessary to thrive in this challenging landscape.
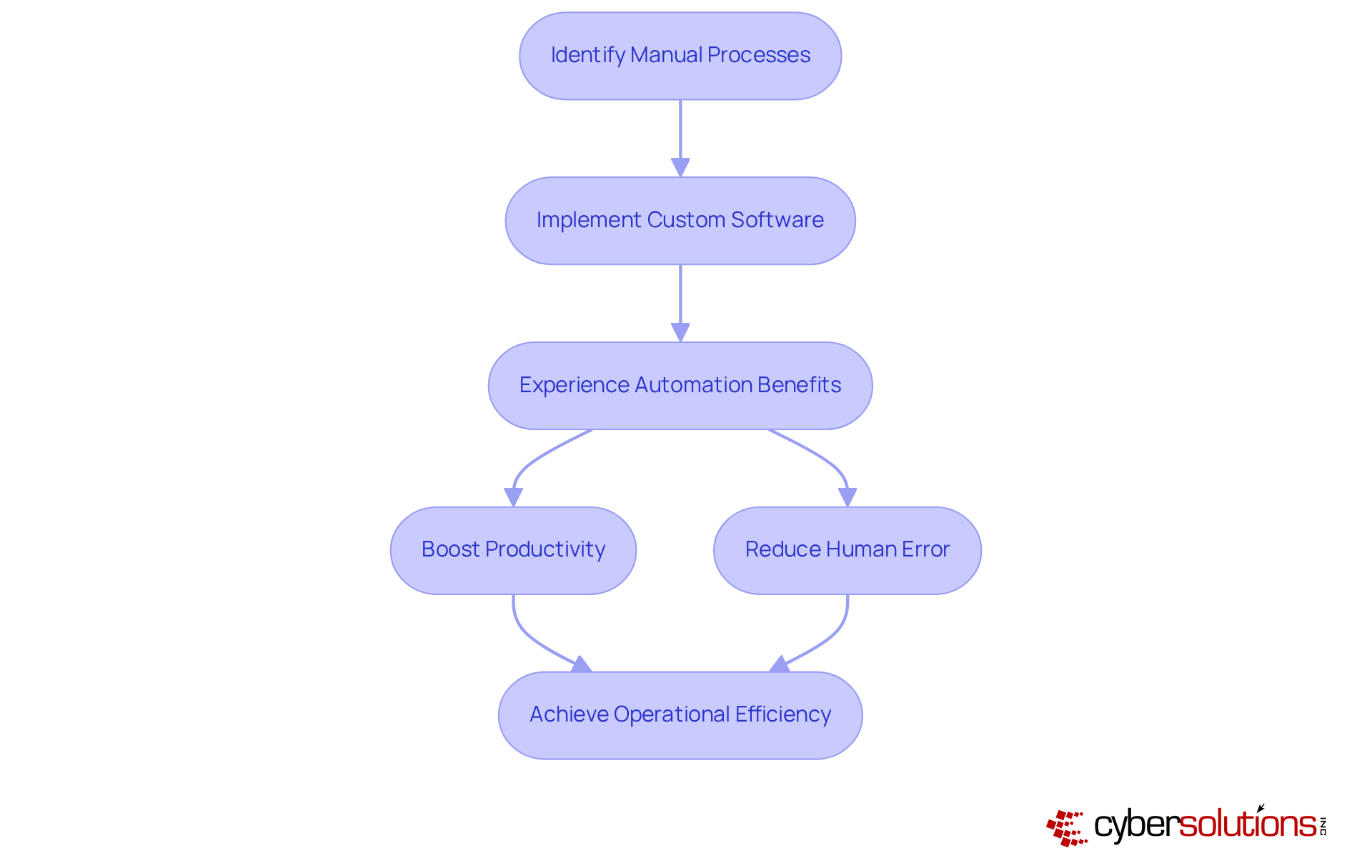
provides tailored technology solutions that empower companies to streamline operations, such as data entry and reporting. By optimizing these processes, organizations can liberate valuable employee time, enabling teams to concentrate on more strategic initiatives. Automation not only improves efficiency but also enhances accuracy, resulting in more accurate and reliable outcomes. This evolution in business operations is not merely advantageous; it is essential for organizations aiming to thrive in an increasingly competitive landscape.
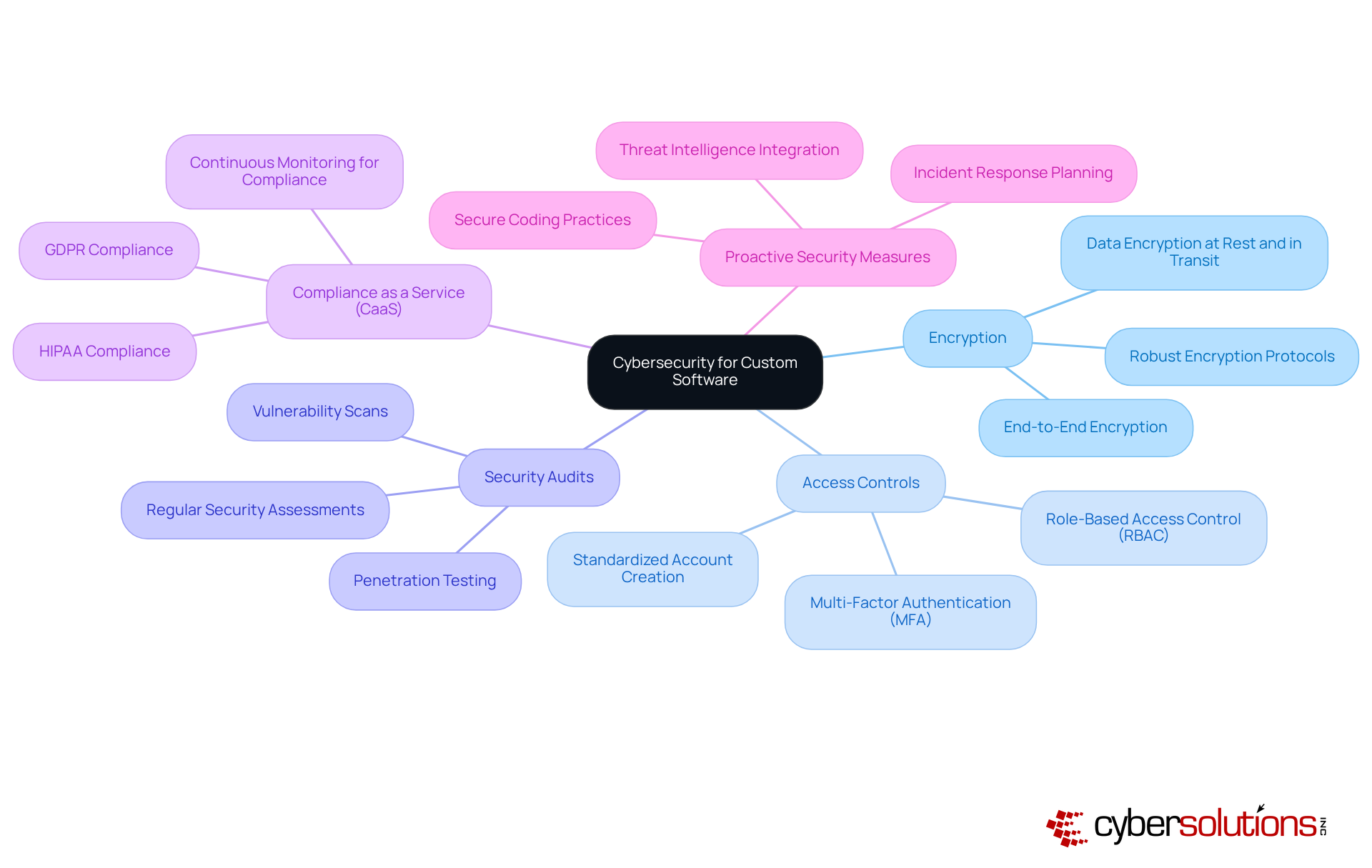
In today's digital landscape, the importance of cybersecurity cannot be overstated, especially for custom business software designed for organizations. These applications can be meticulously crafted with security features. This involves implementing stringent access controls, and conducting regular security audits. By integrating security into the development lifecycle, organizations can significantly mitigate the risk of data breaches and ensure compliance with GDPR and HIPAA.
Cybersecurity experts emphasize a proactive approach to security; as one expert noted, "Security isn’t just a box to check at the end of development—it’s something that should be woven into every step of the process." Furthermore, the integration of security protocols offers businesses comprehensive solutions to meet regulatory requirements, encompassing assessments, policy development, audit preparation, and continuous monitoring. Frequent updates and patches are essential for preserving system integrity against emerging threats.
Moreover, implementing security measures can proactively prevent unauthorized programs from executing, thereby reducing vulnerabilities and ensuring compliance with stringent standards. This tailored approach not only protects sensitive information but also enhances overall operational resilience, making custom business software a crucial investment for enterprises aiming to protect their assets in an increasingly intricate digital environment.
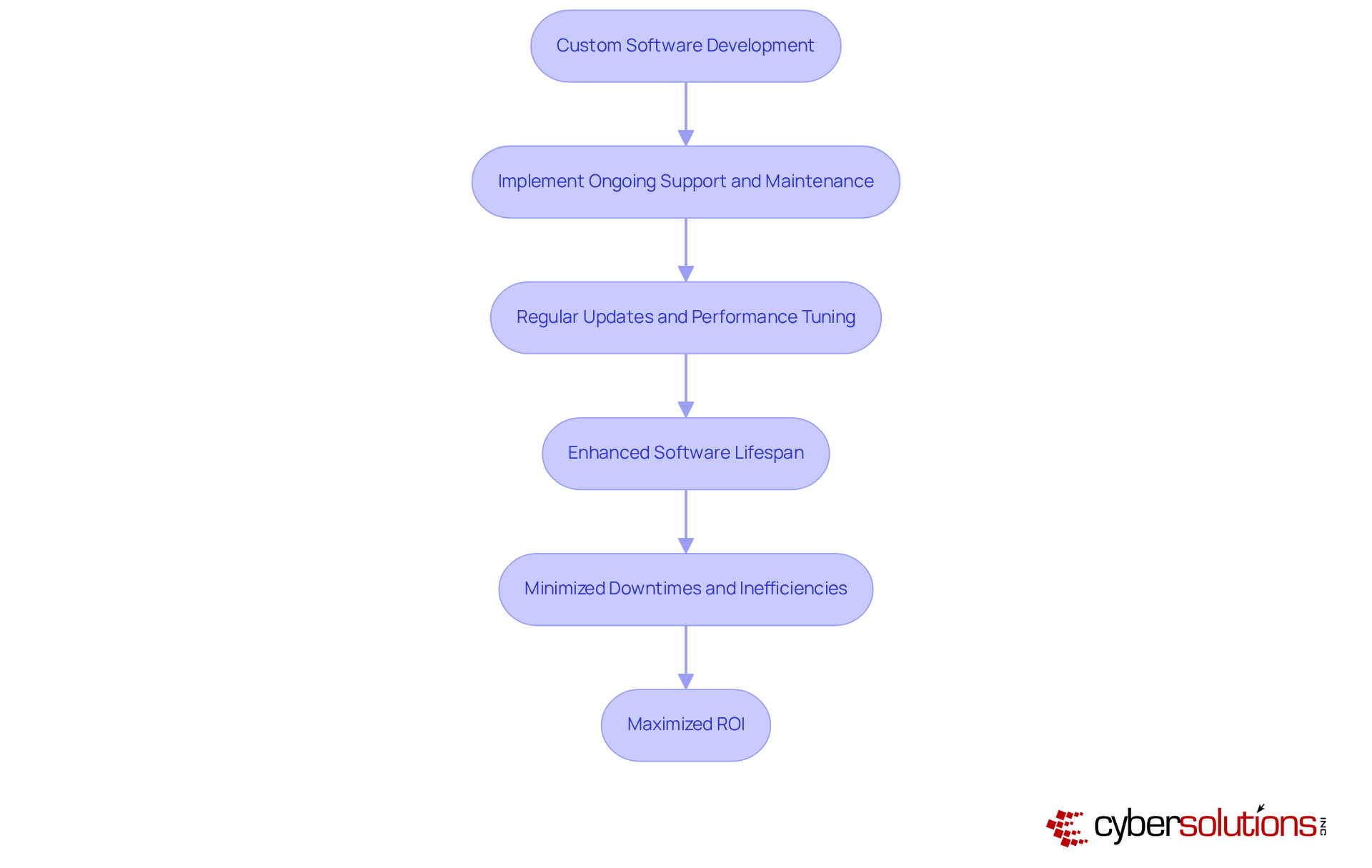
Investing in custom software demands a steadfast commitment to ongoing support. Maintenance practices are not merely beneficial; they are essential for keeping applications functional and secure, enabling them to adapt to the ever-evolving landscape of business needs and technological advancements. This not only extends the system's lifespan but also reduces costs by minimizing costly downtimes and inefficiencies. Consider a well-crafted maintenance schedule: it acts as a safeguard, preventing minor issues from escalating into major technological crises, thus significantly lowering long-term costs.
Moreover, the average lifespan of custom business software can be dramatically enhanced through consistent updates and performance tuning, ensuring it remains relevant and effective in a rapidly changing digital environment. As technologies such as AI and cloud computing reshape IT maintenance strategies, organizations that prioritize these practices are better positioned to leverage their applications for sustained growth and a competitive advantage. Industry specialists emphasize that 'Ongoing maintenance and support are crucial to the success of a business.' Neglecting these critical aspects can lead to frustrated users, diminished productivity, and lost sales, highlighting the urgent necessity for a maintenance plan.
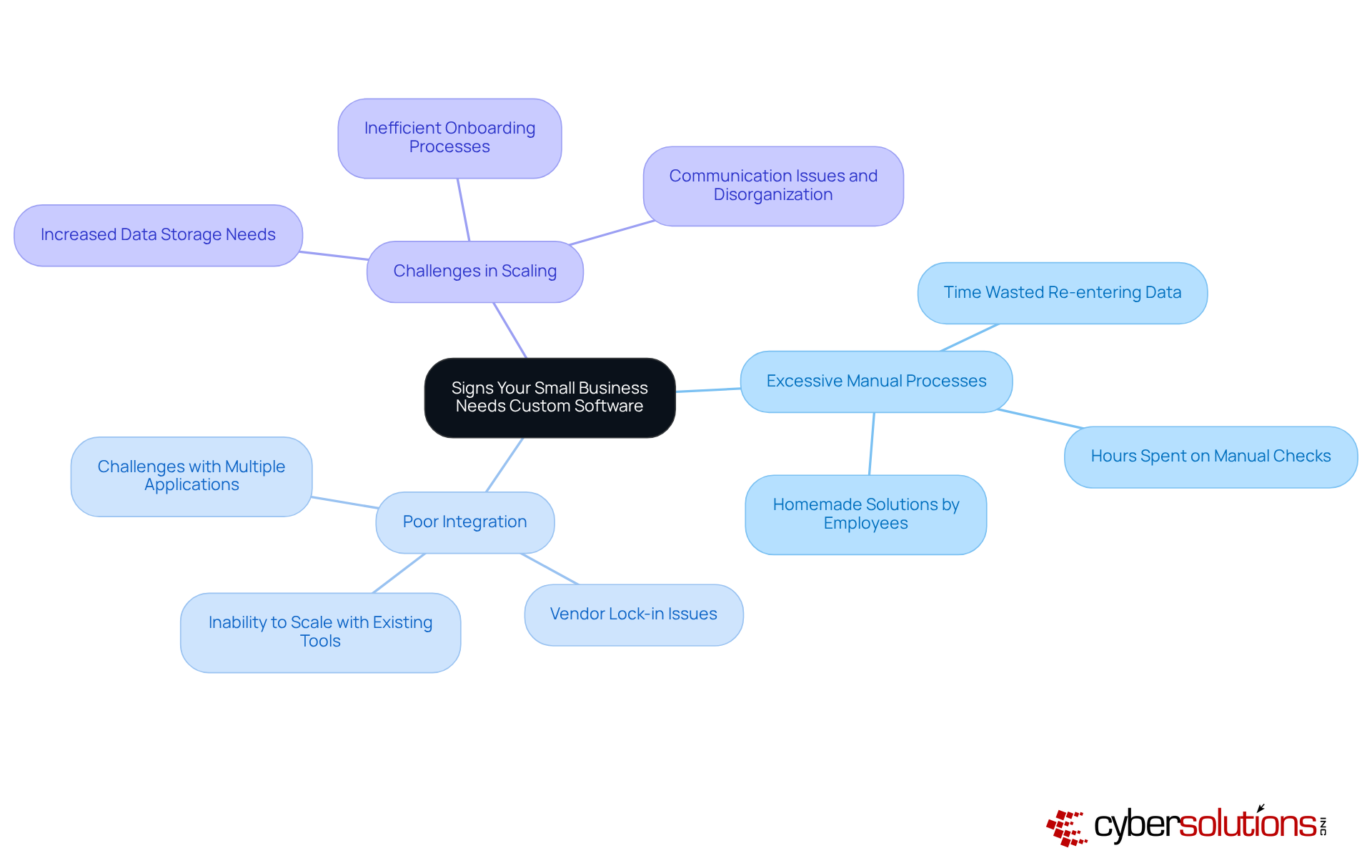
Small enterprises must actively evaluate when facing inefficiencies in their current systems. Common indicators of these inefficiencies include:
For instance, teams often find themselves investing hours re-entering data and managing various applications, leading to frustration and wasted resources. Recognizing these signs early is essential; businesses that neglect to address these issues risk stagnation and may struggle to adapt as they grow.
Industry specialists indicate that a trend of low workflow efficiency frequently signals the need for custom software that can streamline operations. By investing in custom solutions, organizations can align their technology with unique operational needs, ultimately positioning themselves for sustainable growth and enhanced service delivery.
In today's digital landscape, cybersecurity has become a paramount concern, particularly for businesses. While off-the-shelf solutions may offer prompt solutions, they frequently lack the flexibility and customization essential for companies seeking to scale efficiently with growth. Custom software is meticulously crafted to align with specific organizational needs, enabling seamless integration with existing systems and processes. This tailored approach not only enhances scalability but also facilitates the incorporation of new features, such as advanced security protocols.
Custom software is a proactive measure that significantly reduces the risk of cyber threats, and by ensuring that only approved applications can run. This strategy is particularly vital for organizations striving to adhere to compliance standards, including industry regulations. By continuously monitoring application activity, organizations can detect and block unauthorized attempts, thus fortifying their defenses against cyber threats.
Moreover, deploying tailored programs that incorporate security measures guarantees a robust defense, making personalized approaches a more secure and strategic option in the long term. As healthcare CFOs navigate the complexities of the industry, the necessity for custom solutions that address these vulnerabilities becomes increasingly clear. Investing in such tailored applications not only safeguards against potential breaches but also supports the overall integrity and trustworthiness of healthcare services.
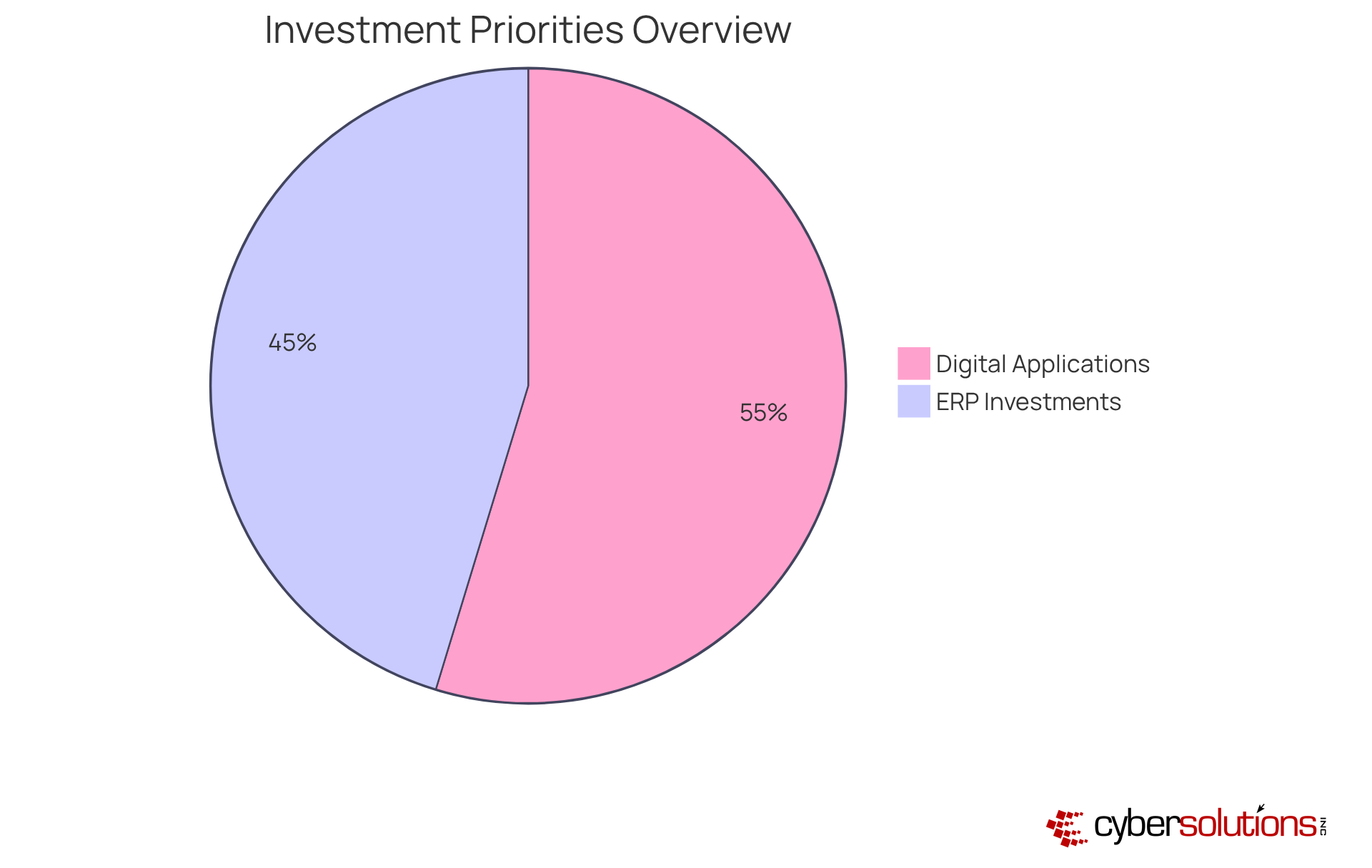
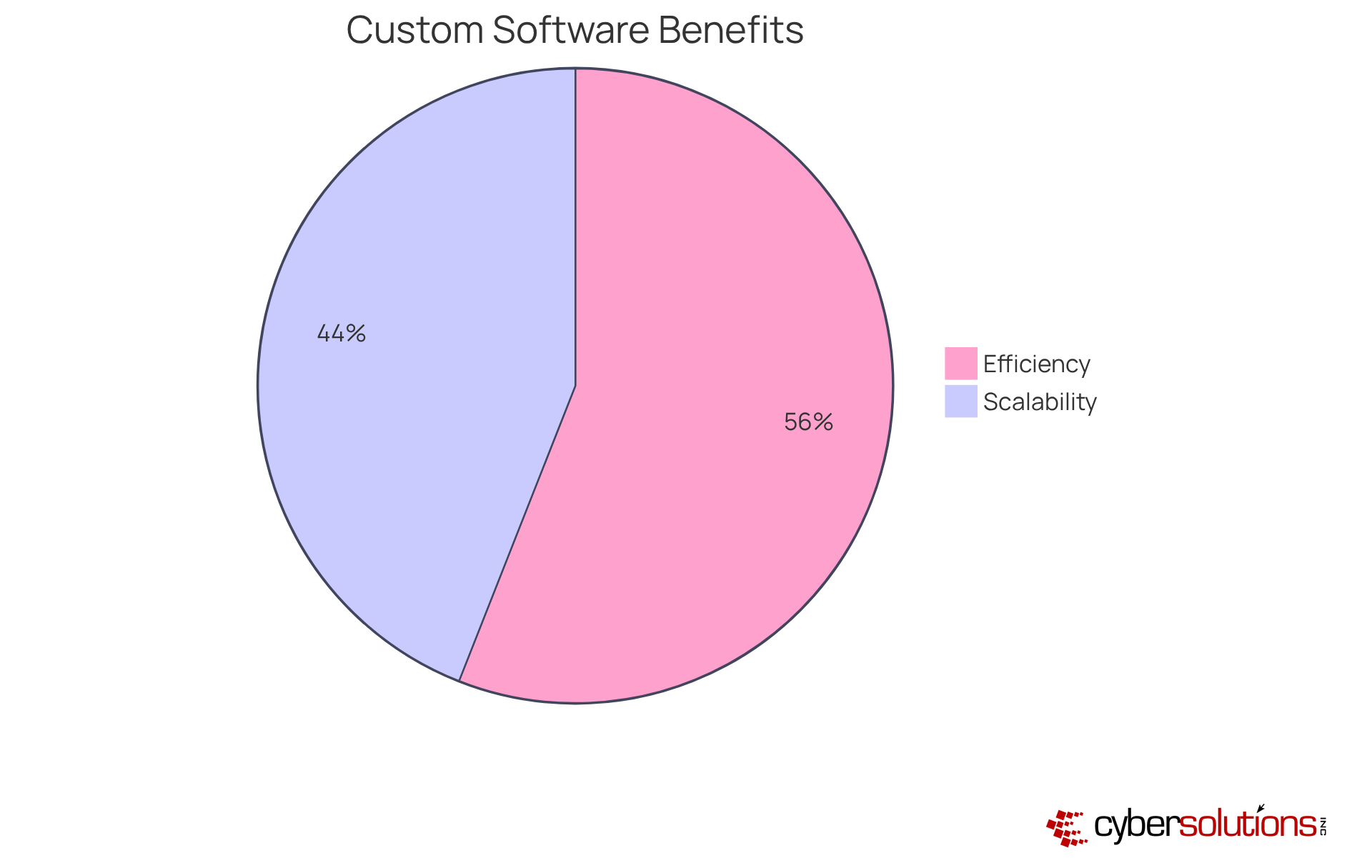
Minor enterprises stand to gain significantly from custom software, especially in areas like efficiency and productivity. These systems can be meticulously customized to align with each organization's specific workflows and processes, ensuring optimal efficiency and effectiveness. For instance, tailored CRM systems simplify customer interactions and data management, while ERP systems integrate various organizational functions, providing a comprehensive view of operations.
Current trends reveal that:
Industry leaders highlight the importance of customization. As one expert noted, 'custom software aligns with unique workflows, automates tasks, and scales with business growth, providing a competitive edge.' This perspective reflects a broader understanding that custom solutions not only enhance operations but also foster long-term growth and adaptability in a rapidly changing market landscape.
Furthermore, research indicates that users of custom software experience a 20% to 30% reduction in operational costs, further solidifying the case for tailored solutions. The projected cost range for CRM or ERP for small enterprises is between $15,000 and $40,000, a critical consideration for C-suite leaders evaluating these investments. Organizations can also expect a return on investment within three to five years, reinforcing the financial benefits of investing in tailored solutions.
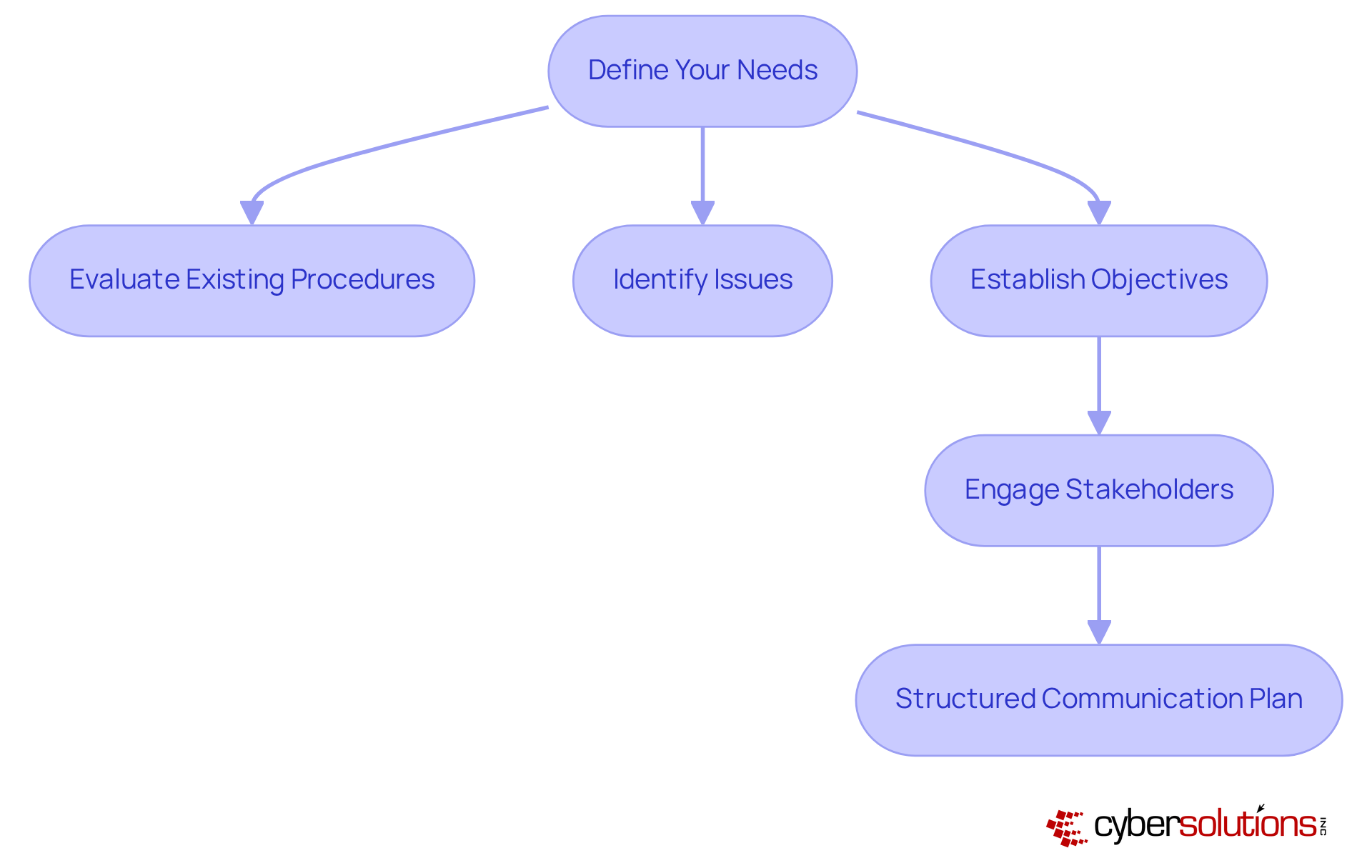
Before embarking on custom software development, it is crucial for companies to clearly outline their requirements. This begins with a comprehensive evaluation of existing procedures, identifying issues, and establishing goals. Engaging stakeholders in this process is essential, as it ensures that the final product aligns with the overall business strategy and meets user expectations. Effective communication significantly enhances development success rates; it fosters collaboration and trust among all parties involved.
Consider this: companies that actively involve stakeholders often experience smoother project execution and reduced risks of scope creep. As noted by industry experts, 'Software implementations involve more than just technology - they are complex endeavors.' This perspective underscores the importance of addressing the diverse requirements of stakeholders, ultimately resulting in more effective and user-friendly outcomes.
Furthermore, a project management plan is indispensable for managing expectations throughout the project lifecycle. This approach ensures that all voices are heard and considered, contributing to a more cohesive and successful development process.
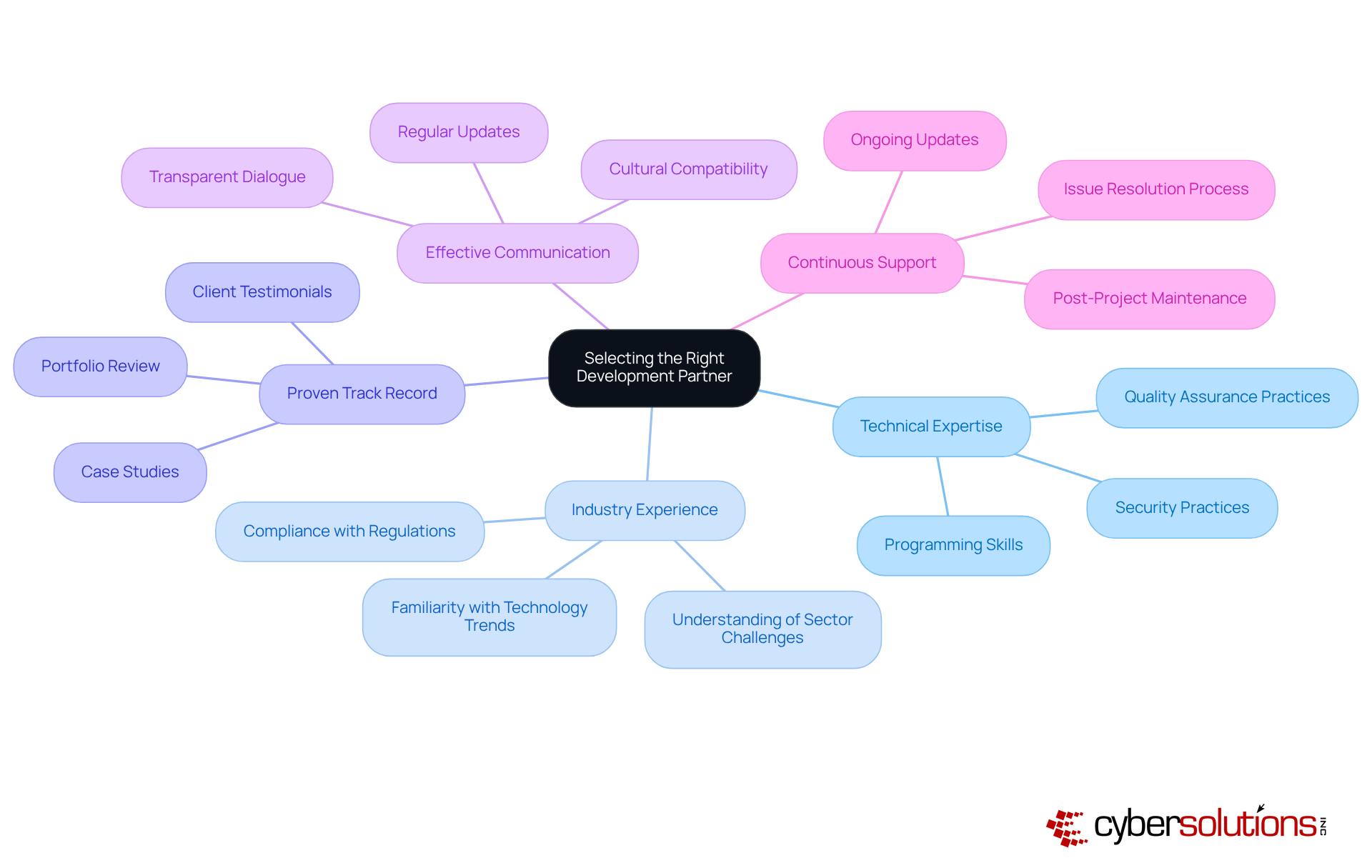
Selecting the right development partner for custom software is paramount for organizational success. Key factors to consider include:
These factors are essential for ensuring alignment with your business objectives. As Stoyan Mitov, CEO of Dreamix, emphasizes, the right partner can navigate IT complexities and optimize expenses, delivering high-quality results that enhance productivity.
Moreover, industry knowledge cannot be overlooked; partners with a profound understanding of your sector can anticipate challenges and propose effective solutions, ensuring efficiency and alignment with strategic goals. It is critical to recognize that poor communication accounts for 60% of project failures, highlighting the necessity for clear and consistent dialogue throughout the partnership.
Additionally, ongoing support is vital for long-term success, as it helps address any issues that may arise and ensures the system remains up-to-date. Successful collaborations often lead to significant improvements in project outcomes, underscoring the importance of careful selection in the development process. To reinforce your decision, consider establishing regular check-ins with your partner to maintain alignment and cultivate a productive relationship.
Investing in custom software is not merely a response to immediate organizational needs; it is a strategic move that equips entities to tackle future challenges. These solutions are meticulously crafted with specific features, enabling organizations to swiftly adjust to shifting market dynamics and technological innovations. Such adaptability is vital for sustaining competitiveness and effectively addressing customer expectations.
Consider this:
As organizations navigate an increasingly volatile landscape, the capacity to integrate emerging technologies and respond adeptly to market fluctuations becomes essential. Thus, custom software emerges as a crucial element of strategies aimed at future-proofing, ensuring that businesses remain resilient and poised for growth.
Investing in custom business software is no longer a luxury; it is an absolute necessity for C-suite leaders who aim to navigate the complexities of today’s digital landscape. Tailored solutions not only address unique operational challenges but also provide a competitive advantage by enhancing efficiency, security, and adaptability. As organizations face increasing demands for personalized applications, the shift towards custom software development becomes imperative to effectively meet specific business needs.
Throughout this article, key points have been underscored, including the critical role of custom software in:
Recognizing the signs that indicate the need for custom solutions—such as inefficiencies and poor integration—has been emphasized. Moreover, the advantages of custom software over off-the-shelf solutions, particularly regarding scalability and compliance, reinforce the argument for tailored approaches in business operations.
Ultimately, as organizations strive to future-proof their operations, the adoption of custom business software emerges as a strategic move that not only addresses current challenges but also prepares businesses for future growth. By investing in tailored solutions, C-suite leaders can ensure their organizations remain resilient and responsive to evolving market demands. The time to act is now; embracing custom software is essential for fostering innovation, enhancing productivity, and securing a sustainable competitive edge in an ever-changing business environment.
What is the primary focus of Cyber Solutions Inc.?
Cyber Solutions Inc. focuses on developing custom business software tailored to the unique needs of organizations, particularly in the healthcare sector, to enhance operational efficiency and bolster security measures.
How does Cyber Solutions Inc. ensure compliance with industry regulations?
Cyber Solutions ensures compliance with industry regulations such as HIPAA, PCI-DSS, and GDPR by creating bespoke applications that streamline workflows, optimize data management, and integrate security features like application allowlisting.
What is application allowlisting and why is it important?
Application allowlisting is a security measure that prevents unauthorized applications from executing, safeguarding sensitive data and reinforcing compliance with critical regulations.
What is the trend regarding custom software development by 2025?
By 2025, it is forecasted that up to 70% of new enterprise programs will be developed using Low Code/No Code platforms, indicating a growing demand for personalized applications.
How does custom software improve operational efficiency?
Custom software automates repetitive manual tasks, such as data entry and reporting, freeing up employee time for strategic initiatives, boosting productivity, and reducing the risk of human error.
What advanced security features can be integrated into custom software?
Advanced security features for custom software can include robust encryption protocols, stringent access controls, regular security audits, and application allowlisting to address unique vulnerabilities.
What is the significance of integrating security into the software development lifecycle?
Integrating security into the development lifecycle is essential for mitigating the risk of data breaches and ensuring compliance with regulatory standards, as security should be a continuous focus rather than a final checklist item.
What is Compliance as a Service (CaaS)?
Compliance as a Service (CaaS) offers businesses comprehensive solutions to meet regulatory requirements, including assessments, policy development, audit preparation, and continuous monitoring.
Why is it essential for organizations to invest in custom business software solutions?
Investing in custom business software solutions is essential for organizations to enhance operations, adapt to market changes, maintain a competitive edge, and effectively protect sensitive information in a complex digital environment.