
In an era where digital threats evolve at lightning speed, the significance of cybersecurity alerts has never been more pronounced, particularly for C-suite leaders tasked with safeguarding their organizations. These alerts not only provide crucial insights into emerging risks but also empower executives to make informed decisions that can protect their assets and ensure compliance with industry standards.
However, with the sheer volume of potential threats and the complexity of modern cyber landscapes, how can leaders effectively navigate this critical information to bolster their defenses and mitigate risks? This question underscores the urgency of understanding the current cybersecurity landscape and its implications for organizational resilience.
In today's rapidly evolving digital landscape, the importance of cybersecurity cannot be overstated. Cyber Solutions Inc. offers a collection of meticulously crafted alerts to keep businesses informed of potential risks. These alerts are tailored to meet the specific requirements of various industries, enabling organizations to respond promptly to emerging threats. For instance, the recent report highlighted a staggering 150% increase in China-related activity, underscoring the necessity for proactive measures.
By leveraging advanced technologies and expert insights, Cyber Solutions empowers leaders to make informed decisions that safeguard their assets and reputation. The impact of these alerts extends beyond immediate risk awareness; they play a pivotal role in strategic planning. This enables leaders to allocate resources effectively and prioritize security initiatives. As the threat landscape continues to evolve, the significance of these alerts becomes increasingly critical, positioning them as an indispensable resource for any organization aiming to enhance security posture and operational resilience.
In today's digital landscape, the significance of cybersecurity cannot be overstated, particularly within the healthcare sector. The Cybersecurity and Infrastructure Security Agency (CISA) plays a vital role in safeguarding organizations by issuing advisories that detail newly discovered vulnerabilities and ongoing threats. C-suite leaders must recognize the importance of subscribing to these advisories to proactively mitigate potential risks. Entities that have successfully implemented cybersecurity measures, such as threat detection systems, have reported notable enhancements in their security posture, demonstrating the advisories' practical value in real-world scenarios.
CISA stands as the gold standard in cybersecurity, as it effectively prevents malware and unauthorized software from executing. This proactive approach significantly reduces risks and minimizes vulnerabilities. Furthermore, it aids organizations in meeting stringent compliance requirements, including:
while simultaneously bolstering their overall security framework. By restricting the applications permitted to operate, organizations can effectively thwart ransomware and other malicious software from infiltrating their systems. Elements such as centralized management and ongoing monitoring further enhance this strategy, enabling organizations to manage allowlists efficiently and identify unauthorized software attempts in real-time.
Staying informed on cybersecurity threats empowers executives to implement timely security measures that help safeguard sensitive data and uphold operational integrity. Recent advisories have highlighted critical vulnerabilities, acting as important alerts for organizations to prioritize their remediation efforts. How prepared is your organization to respond to these emerging threats?
Moreover, CISA underscores the importance of threat intelligence as a cornerstone of an effective cybersecurity strategy. By adhering to these advisories and executing proactive strategies like incident response planning, organizations can significantly diminish risks associated with cyberattacks. As CISA continues to update the KEV Catalog with new vulnerabilities, it is imperative for executives to remain vigilant and responsive to these updates, ensuring their organizations are well-equipped to navigate the evolving threat landscape.
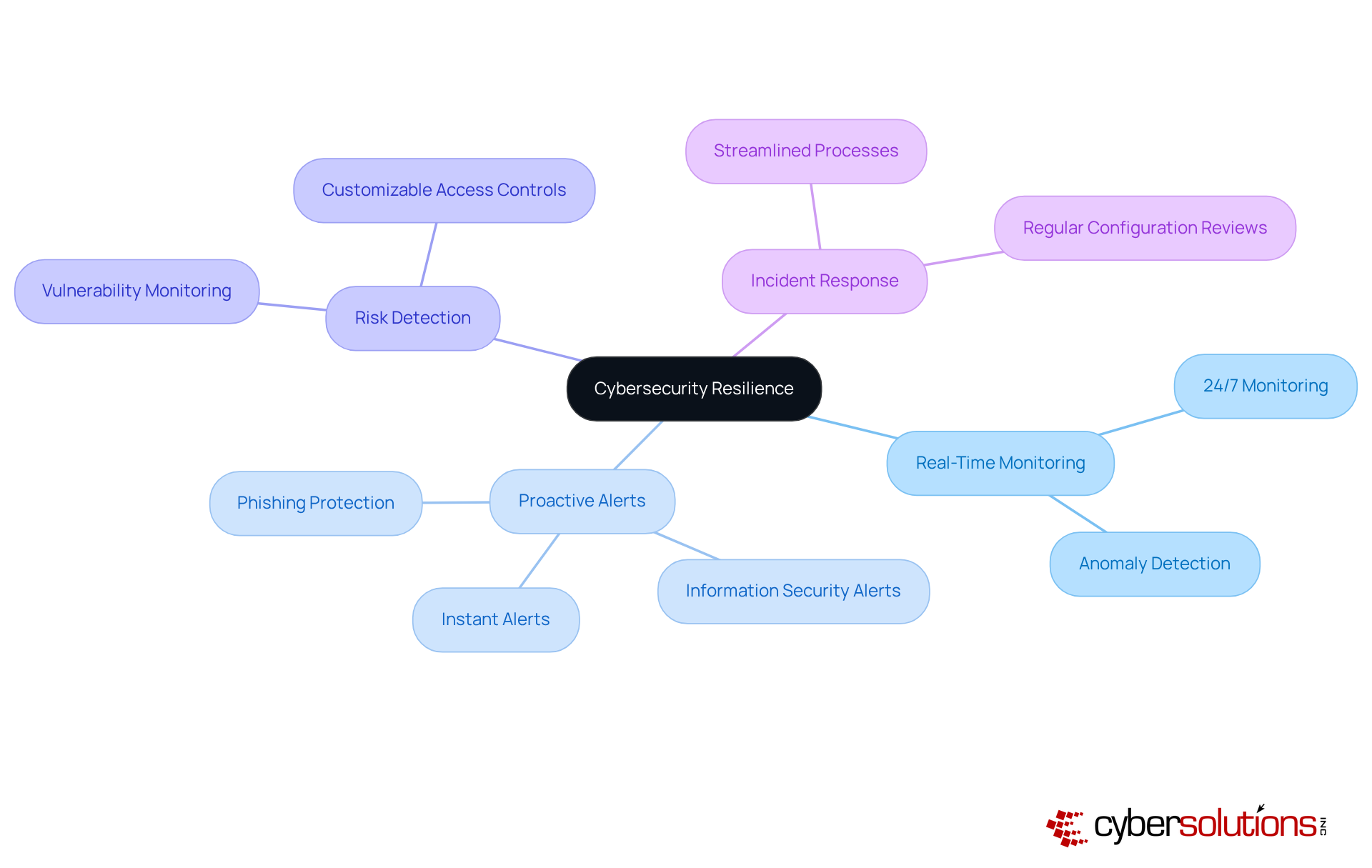
In today's digital landscape, cybersecurity is not just a necessity; it is a critical component of organizational resilience. Cyber Solutions' alert services empower organizations with real-time information regarding potential security incidents. By continuously monitoring for anomalies and vulnerabilities, we enable swift action to prevent downtime or breaches.
C-suite executives must prioritize the integration of Cyber Solutions' services. These services are meticulously designed to combat phishing, ransomware, and other malware attacks. With timely notifications, instant alerts, and actionable insights, leaders can significantly enhance their security posture and risk management. Our risk intelligence and customizable access controls ensure that only authorized users gain entry, adapting as your operations expand.
This proactive approach not only mitigates the risk of cyber threats but also aligns with current trends in cybersecurity management. Organizations increasingly recognize the value of vigilance and preparedness in safeguarding their operations. By leveraging Cyber Solutions' extensive monitoring services, executives can ensure their entities remain robust against evolving cyber challenges. This commitment ultimately fosters a culture of safety and compliance.
To maximize these benefits, C-suite leaders should regularly review and adjust their protective configurations to stay ahead of the threats.
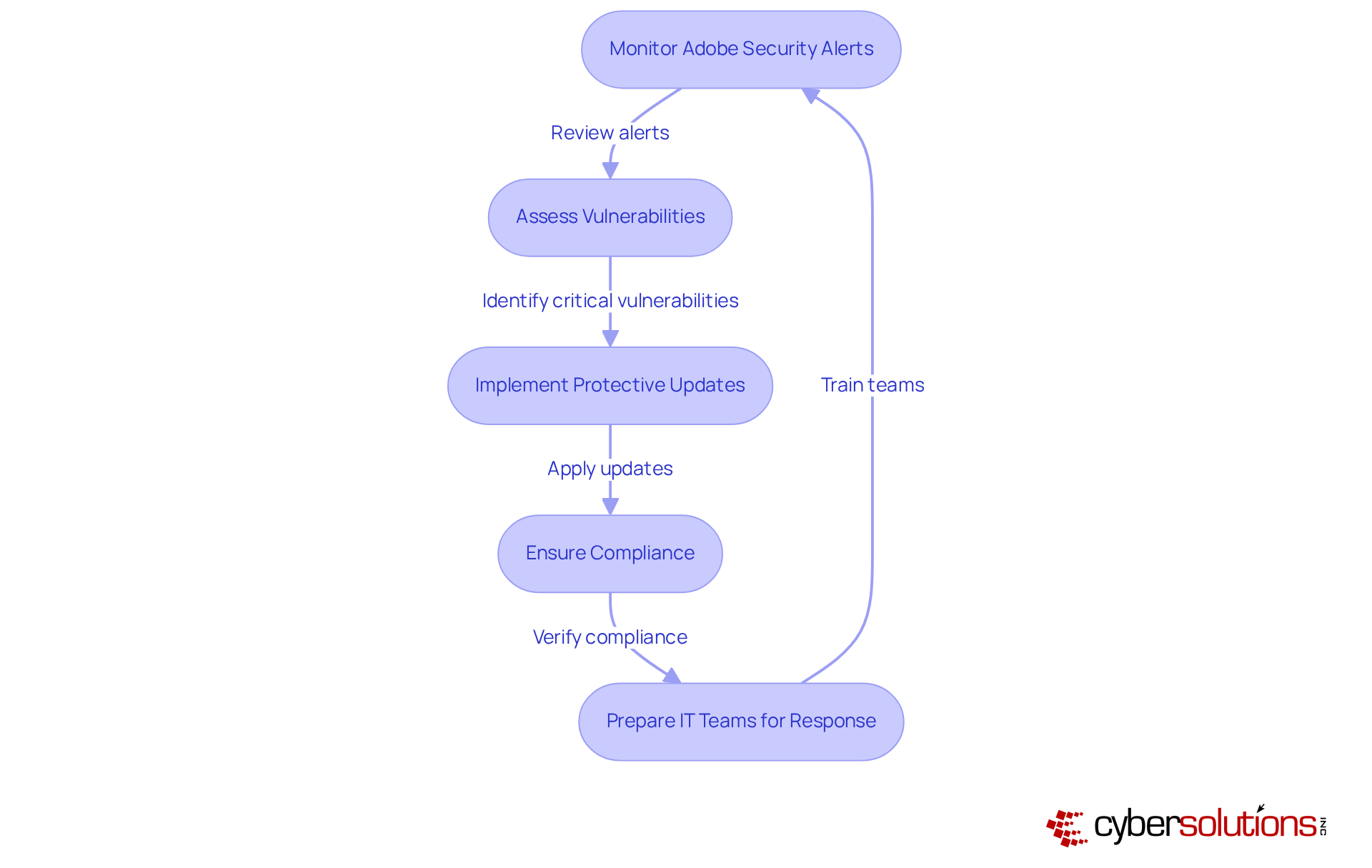
In today's digital landscape, the importance of cybersecurity cannot be overstated, particularly for organizations relying on technology. Adobe frequently issues warnings regarding vulnerabilities that pose significant risks, potentially impacting the operational integrity of these organizations. Recent updates have addressed vulnerabilities that could allow attackers to bypass security measures or execute arbitrary code. Therefore, organizations must prioritize monitoring these alerts to mitigate risks associated with potential exploits.
Organizations like Adobe Commerce exemplify effective responses to vulnerabilities, swiftly implementing measures to safeguard their creative assets and sensitive information. This is not merely a best practice; it is essential for maintaining the trust of clients and stakeholders. Expert insights emphasize the necessity for IT teams to be adequately prepared to respond promptly to Adobe's updates, reinforcing the need for vigilance in today’s threat landscape.
Such diligence not only protects against breaches but also ensures compliance, thereby strengthening the organization's overall defense posture. By adopting a proactive approach, organizations can effectively navigate the complexities of cybersecurity, ensuring resilience against evolving threats. The question remains: are your systems prepared to respond to the next alert?
that equips organizations with the necessary insights to navigate the evolving landscape of cybersecurity threats and vulnerabilities. This intelligence empowers leaders to proactively identify and mitigate potential risks, significantly bolstering their organization’s security posture. By routinely analyzing SecurityScorecard reports, executives can make informed decisions that align with their risk management strategies. This proactive approach is crucial, especially considering that 88% of cybersecurity professionals express concerns about data breaches, underscoring the urgent need for comprehensive security measures.
Moreover, the implementation of application allowlisting is vital for organizations aiming to strengthen their defenses. By permitting only pre-approved applications to operate, businesses can substantially diminish the risks associated with malware, ransomware, and unauthorized software execution. This practice not only ensures compliance but also minimizes vulnerabilities and reduces the attack surface, making it increasingly difficult for attackers to exploit systems. As Dan Streetman, CEO of Tanium, aptly stated, "Organizations can’t afford blind spots in their vendor ecosystem." This highlights the critical importance of a well-rounded security strategy.

In today's digital landscape, Hacker News stands as a vital platform for monitoring significant cybersecurity incidents. To engage with this resource, as it delivers timely updates on risks that could potentially impact their organizations. By thoroughly analyzing the nature and implications of these incidents, executives can bolster their preparedness and formulate effective strategies to mitigate potential damages.
Staying informed through Hacker News not only aids in understanding the evolving risk landscape but also empowers executives to implement measures that shield their organizations from emerging threats. To further strengthen their defenses, C-suite leaders are strongly advised to utilize alert services. These services provide instant alerts and real-time insights as needed, ensuring that suspicious activities are detected and addressed before they escalate into crises, thereby protecting businesses from ransomware, phishing, and other malware attacks.
Moreover, establishing access controls and tailored restrictions can significantly enhance security. By adopting these strategies, executives can create a robust defense mechanism that not only safeguards their entities but also fosters a culture of security awareness throughout their organizations.

UVA Information Security Alerts are vital for understanding the evolving landscape of threats, particularly phishing and pretexting attacks. Recent data reveals that social engineering attacks constituted 39% of initial access incidents in the first half of 2025, highlighting the urgent need for proactive measures. C-suite leaders must prioritize comprehensive training and awareness programs to effectively combat these threats. Organizations that cultivate a security-conscious culture can significantly reduce their risk of falling prey to social engineering tactics.
Successful programs have proven effective in mitigating risks. For example, organizations leveraging platforms like KnowBe4 have reported improved employee awareness. By equipping staff with the knowledge to recognize suspicious messages, organizations can establish a robust initial line of defense against cyber threats.
Furthermore, implementing regular training sessions that address the latest tactics, such as the ClickFix method—which experienced a staggering 1,450% increase in the first half of 2025—can further bolster organizational resilience. As attackers grow more sophisticated, it is essential for security teams to consistently update training resources to reflect current dangers and reinforce best practices related to cybersecurity.
In conclusion, investing in security training not only enhances a company's defenses but also fosters a culture of vigilance that is critical in today’s threat landscape. By prioritizing these initiatives, C-suite executives can significantly reduce their organizations' vulnerability to social engineering attacks and other social engineering schemes.
Ongoing alerts are vital for organizations aiming to ensure the swift resolution of vulnerabilities. C-suite leaders must prioritize the adoption of automated systems, which significantly streamline the patching process and reduce the risk of exploitation. By embracing these solutions, organizations can bolster their protective posture and mitigate the impact of cyber threats, particularly concerning critical infrastructure, which requires advanced protective protocols and procedures to safeguard sensitive federal data.
Recent trends illustrate that automation in patch management not only expedites processes but also nurtures a culture of security awareness. Organizations that have integrated automated patch management report a marked decrease in the time needed to address vulnerabilities, empowering them to respond promptly to emerging risks.
Furthermore, the emergence of sophisticated threats, such as those posed by the newly identified cybercrime group TA585, highlights the necessity of proactive measures. Cybercriminals often exploit inadequately protected systems, making it imperative for companies to implement automated systems that generate information security alerts and patch management to stay ahead of potential exploits. This proactive approach not only enhances protection but also aligns with regulatory requirements, which increasingly stress the importance of compliance to avert substantial penalties.
Incorporating frameworks like NIST CSF and CIS Controls can further fortify an organization's patch management strategy, ensuring that vulnerabilities are managed in near real-time. A recent case study revealed that a healthcare provider, by adopting a comprehensive patch management strategy, successfully recovered from a ransomware attack ahead of schedule while enhancing its protective measures. Additionally, with the global average cost of a data breach reaching $5.08 million, the financial implications of neglecting patch management cannot be overstated. The significance of having a structured response plan underscores that acting swiftly is essential to minimizing damage and maintaining eligibility for lucrative government contracts.
In conclusion, investing in patch management transcends a mere technical upgrade; it is a strategic imperative that enables organizations to sustain resilience against evolving threats while safeguarding their financial interests and ensuring compliance with stringent cybersecurity standards.

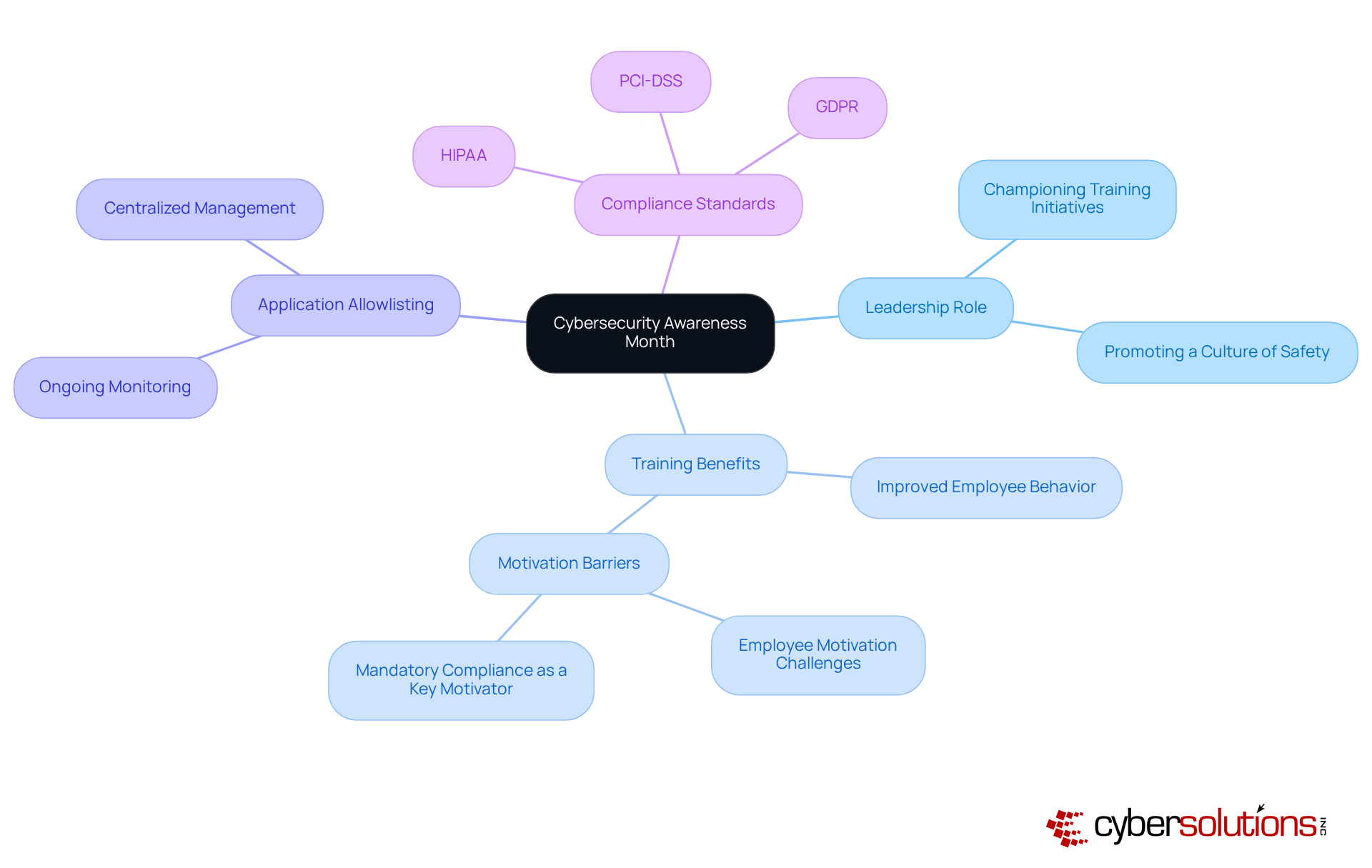
Cybersecurity Awareness Month serves as a critical reminder for organizations to bolster their protective culture. C-suite leaders must seize this opportunity to champion security awareness among employees. Research indicates that 96% of leaders believe enhanced organization-wide training can significantly reduce cyberattacks, underscoring the necessity of a comprehensive training program.
Fostering a culture of safety not only strengthens resilience against cyber threats but also ensures compliance with regulations. Effective training initiatives can lead to improvements in employee behavior, with 68% of IT managers identifying lack of awareness as a key barrier to implementing protective measures. By integrating real-life scenarios into training, organizations can better equip employees to recognize and respond to risks, ultimately embedding security practices into their daily routines.
Furthermore, promoting application allowlisting is vital for developing a vigilant workforce. Application allowlisting is a pivotal strategy in this regard, as it proactively blocks unauthorized software from executing, thereby mitigating the risk of malware and ransomware attacks. Essential features of application allowlisting include:
These features enhance control and policy enforcement. This strategy not only diminishes vulnerabilities but also aids organizations in meeting compliance standards such as HIPAA, PCI-DSS, and GDPR.
Public-private partnerships and collaborative efforts are essential in tackling the ever-evolving landscape of cybersecurity threats. As highlighted during Cybersecurity Awareness Month, organizations that prioritize security awareness and implement robust measures like training programs are better equipped to defend against potential breaches and to respond effectively to information security alerts, thereby upholding operational integrity. By making cybersecurity a collective responsibility, leaders can empower their teams to actively participate in safeguarding sensitive information and critical infrastructure.
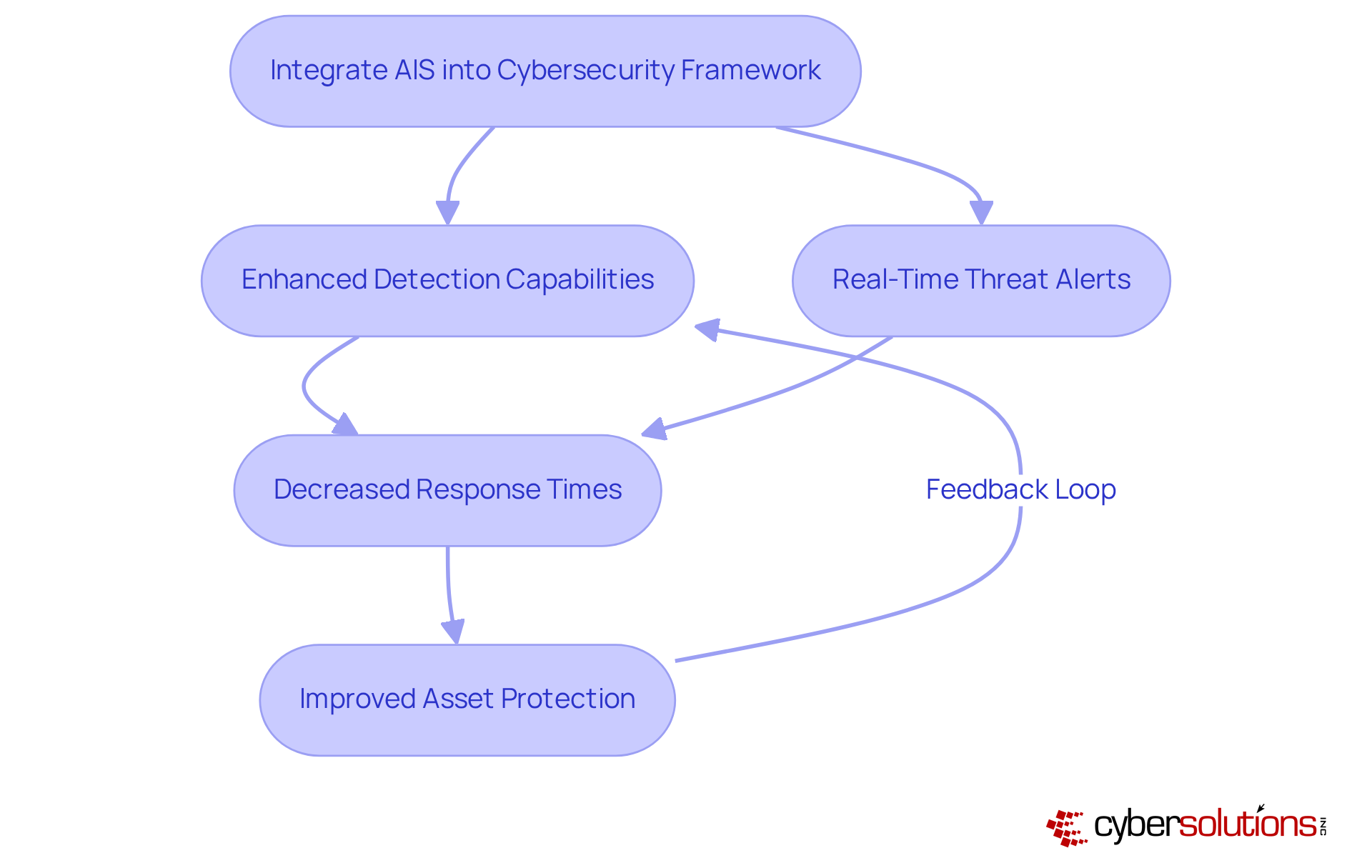
AIS serves as a pivotal resource, enabling entities to receive real-time information regarding threats. By integrating AIS into their cybersecurity frameworks, C-suite leaders can markedly enhance their detection capabilities. This strategic incorporation allows organizations to leverage data and insights, enabling swift reactions to emerging threats and enhancing asset protection.
The impact of real-time danger intelligence and threat indicators on response times is profound. Organizations that utilize AIS have reported a significant decrease in response times, facilitating the mitigation of potential breaches before they escalate. Notably, the Cybersecurity and Infrastructure Security Agency (CISA) has seen a remarkable increase in shared cyber risk indicators, soaring from approximately 1 million in 2023 to over 10 million in 2024, largely due to contributions from a private-sector partner. This increase underscores the critical value of collaborative information sharing in bolstering security measures.
Expert insights affirm that the integration of AIS into cybersecurity frameworks not only elevates risk detection but also fosters a proactive security culture. Organizations adopting AIS report improved efficiency and a more agile response to risks, ultimately leading to reduced operational disruptions and financial losses. As a result, the strategic implementation of AIS becomes indispensable for organizations striving to stay ahead of potential risks.
In today's cybersecurity landscape, the significance of timely information security alerts has never been more pronounced for C-suite leaders. These alerts are indispensable tools that empower executives to stay ahead of emerging threats, ensuring their organizations remain resilient and compliant in an increasingly complex digital environment. By prioritizing these alerts, leaders can make informed decisions that not only safeguard their assets but also enhance their overall security posture.
Throughout this article, we have highlighted critical insights, including:
These strategies collectively strengthen an organization's defenses.
As the cybersecurity landscape continues to evolve, the imperative for C-suite leaders is clear: proactive engagement with information security alerts is essential. By fostering a culture of security awareness and prioritizing the implementation of robust cybersecurity measures, organizations can significantly mitigate risks and protect their critical assets. Embracing these practices not only safeguards against potential breaches but also positions businesses for sustained success in an era where cyber threats are omnipresent.
What services does Cyber Solutions Inc. offer for cybersecurity?
Cyber Solutions Inc. provides a collection of cybersecurity alerts tailored to various industries, helping businesses stay informed about potential risks and respond promptly to emerging threats.
Why are cybersecurity alerts important for businesses?
Cybersecurity alerts are crucial as they enable organizations to be aware of immediate risks, shape strategic business decisions, allocate resources effectively, and enhance their security posture and operational resilience.
What recent trend was highlighted in the CrowdStrike report mentioned in the article?
The CrowdStrike report indicated a 150% increase in China-related cyber activity, emphasizing the need for timely cybersecurity alerts.
What role does the Cybersecurity and Infrastructure Security Agency (CISA) play in cybersecurity?
CISA issues advisories detailing newly discovered vulnerabilities and ongoing threats, helping organizations, particularly in the healthcare sector, to proactively mitigate potential risks.
What is application allowlisting and why is it important?
Application allowlisting is a cybersecurity strategy that prevents malware and unauthorized software from executing, significantly reducing vulnerabilities and helping organizations meet compliance requirements like HIPAA, PCI-DSS, and GDPR.
How can organizations benefit from CISA advisories?
Organizations can stay informed about critical vulnerabilities and implement timely remediation strategies, enhancing their protective measures against cyberattacks.
What is the significance of real-time monitoring and alerts in cybersecurity?
Real-time monitoring and alerts enable organizations to detect anomalies and potential security incidents swiftly, allowing for immediate action to prevent downtime or breaches.
How can C-suite executives enhance their organization's cybersecurity?
Executives should prioritize integrating proactive cybersecurity offerings, regularly review protective configurations, and stay updated on emerging threats to ensure robust security against evolving cyber challenges.