
In today’s world, where cyber threats are more prevalent than ever, businesses are confronted with the critical challenge of safeguarding their digital assets while demonstrating resilience against potential breaches. The right cybersecurity metrics can mean the difference between a swift recovery and a catastrophic failure. This article explores ten essential cybersecurity KPIs that empower organizations to bolster their defenses, optimize operational efficiency, and ensure compliance. But with a plethora of metrics available, how can companies discern which KPIs truly matter for their resilience?
As we navigate this complex landscape, it’s vital to recognize the unique challenges that organizations face. Cybersecurity isn’t just a technical issue; it’s a fundamental aspect of business strategy. By understanding the implications of these threats, companies can better prepare themselves to respond effectively.
Ultimately, the right metrics can guide organizations in making informed decisions, enhancing their overall security posture. Let’s delve into these key performance indicators and discover how they can transform your approach to cybersecurity.
Cyber Solutions Inc. underscores the vital role of thorough security metrics in bolstering business resilience. In today’s landscape, where cyber threats are increasingly sophisticated, these metrics are not just about evaluating security measures; they’re essential for aligning with financial strategies to showcase value. By focusing on key performance indicators, organizations can effectively navigate the complexities of cybersecurity and compliance, ensuring robust protection against evolving threats while optimizing resource allocation.
Consider metrics like Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR). Tracking these can significantly enhance a company's risk mitigation capabilities. A shorter MTTD means quicker detection of potential threats, leading to faster responses and recovery. This ultimately reduces downtime and associated costs. Organizations that efficiently monitor these metrics often experience a marked improvement in their security posture and a decrease in the financial impacts of cyber incidents.
Moreover, with the right tools, implementing training programs centered around these metrics can elevate employee awareness and minimize vulnerabilities. Cyber Solutions Inc. provides comprehensive training, risk assessments, and proactive monitoring services that empower employees and fortify defenses. Real-world examples reveal that organizations not only enhance their defenses but also achieve improved operational efficiency, resulting in a more favorable ROI.
In our current digital environment, the importance of monitoring cybersecurity metrics cannot be overstated. These metrics lay the groundwork for informed decision-making, enabling organizations to allocate resources effectively and maintain compliance with regulatory standards. By leveraging insights from Cyber Solutions' Cybersecurity as a Service (CaaS), businesses can ensure resilience against ever-evolving cyber threats while preparing for audits and meeting stringent compliance requirements. A recent case study illustrated how Cyber Solutions' layered approach to cybersecurity led to a significant reduction in response times and an enhanced overall safety stance for a client, showcasing the effectiveness of their strategies.

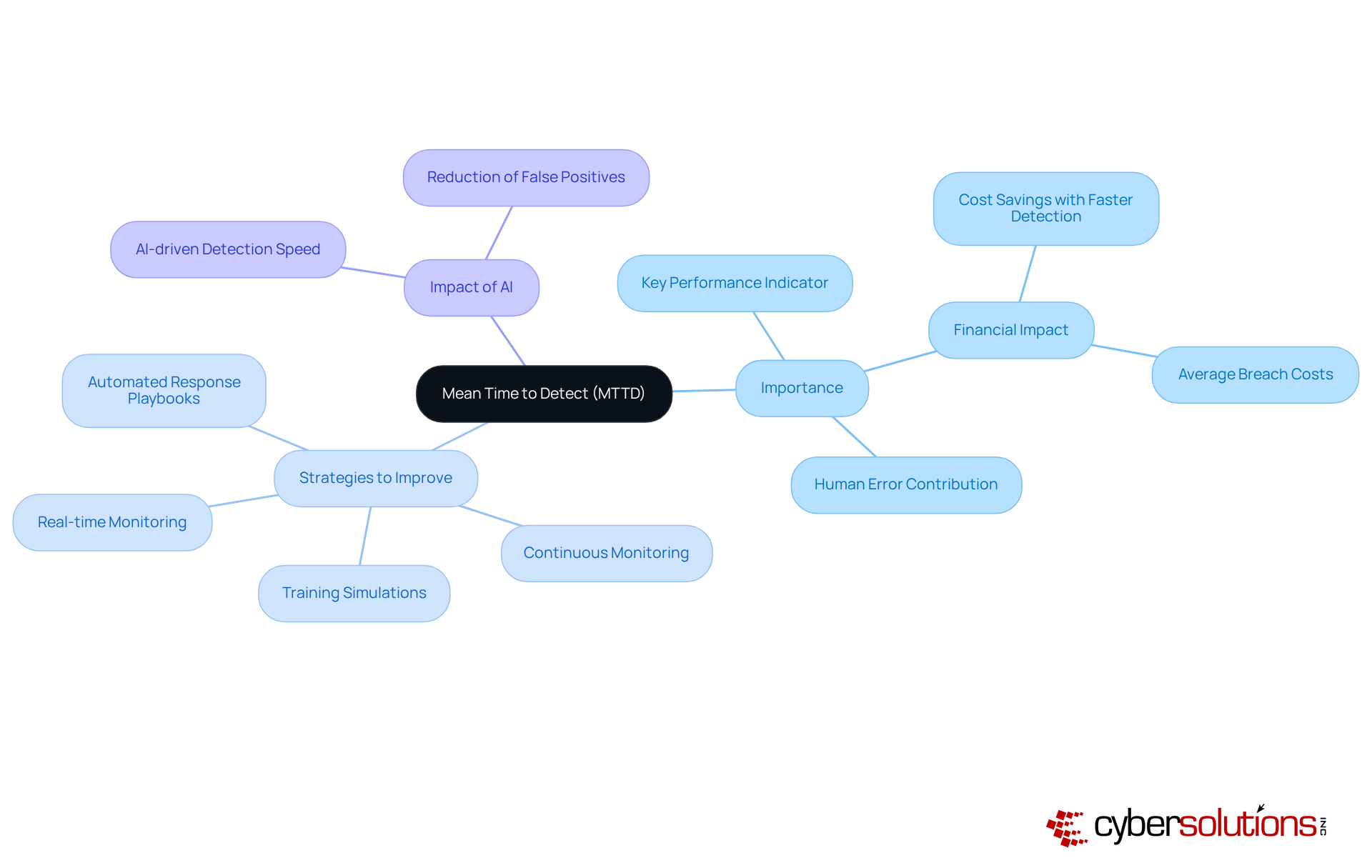
Mean Time to Detect (MTTD) serves as a crucial cyber security KPI that reflects the average time taken to identify a security event after it occurs. In today’s rapidly evolving cybersecurity landscape, organizations must implement measures to mitigate the potential repercussions of breaches. Advanced tools, particularly those powered by artificial intelligence, can significantly enhance MTTD. For instance, organizations utilizing AI-driven detection systems recognize breaches an average of 80 days faster than those relying on manual methods, resulting in savings of nearly $2 million per event.
To improve MTTD, businesses should adopt best practices such as:
Notably, 88% of employees participate in security awareness training, underscoring the importance of training in enhancing MTTD.
Moreover, organizations must address the challenge of false positives, which can divert attention from genuine threats and increase MTTD. These strategies not only streamline detection processes but also foster a culture of continuous improvement in incident management, which is essential for establishing effective security protocols. As the cybersecurity environment evolves, entities must invest in robust detection capabilities, such as those provided by Cyber Solutions, to ensure swift identification of threats. This investment is vital for maintaining operational integrity and resilience against cyber events.
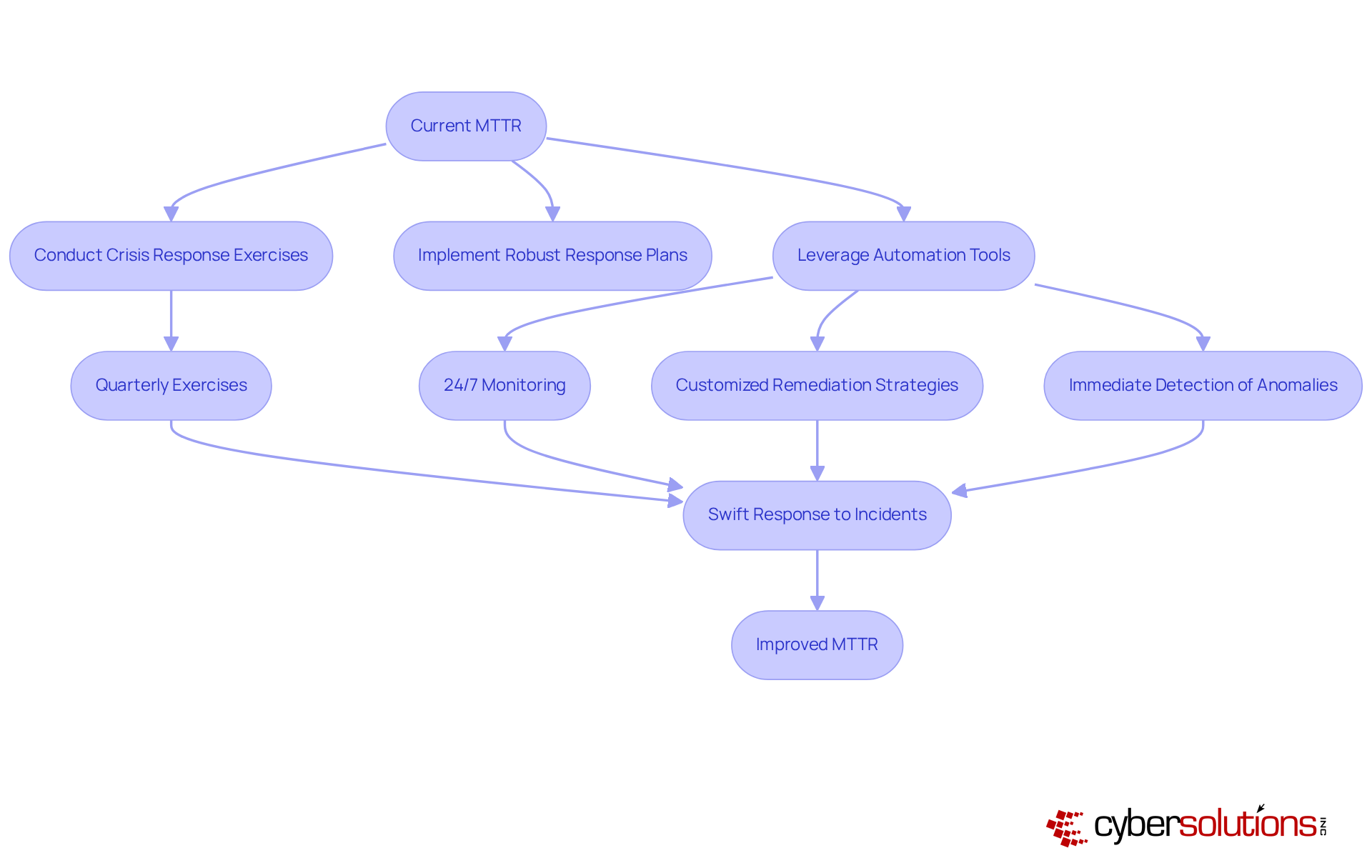
In today's digital landscape, the Mean Time to Respond (MTTR) is a critical metric for organizations that aim to effectively manage security incidents. Reducing MTTR is not just a goal; it’s an essential strategy for minimizing the impact of security breaches and downtime. How can organizations achieve this? By implementing and leveraging automation tools that facilitate faster remediation processes.
Consider this: firms that invest in security training every three months can react to security events 35% quicker, significantly lowering their MTTR. This statistic underscores the importance of timely incident response, as indicated by the data. Cyber Solutions enhances this process through monitoring and alerts, ensuring immediate detection of anomalies and potential vulnerabilities. This proactive approach not only aids in quick situation containment but also guarantees the establishment of customized remediation strategies, addressing risks and preparing comprehensive documentation for audits.
By prioritizing a swift response to incidents - whether through on-site assistance or a multi-tiered recovery strategy - Cyber Solutions empowers organizations to mitigate damage and maintain business continuity effectively. In a world where every second counts, the ability to respond rapidly can make all the difference.
In today's digital landscape, the importance of cybersecurity cannot be overstated, especially in healthcare. Mean Time to Contain (MTTC) is a critical metric that measures the duration required to restrict the spread of a security incident. A lower MTTC signifies a more effective containment strategy, which is essential for minimizing damage and loss.
Organizations must prioritize improving their MTTC by investing in detection and response technologies. For instance, Cyber Solutions offers advanced solutions, ensuring that suspicious activities are detected and neutralized before they escalate into significant threats. Furthermore, having a swift response team on-site can dramatically enhance containment efforts. Case studies reveal that prompt action often leads to quicker recovery from incidents, underscoring the need for readiness.
Conducting thorough assessments allows organizations to identify vulnerabilities and strengthen their response strategies. This proactive approach not only enhances MTTC but also improves security posture and fortifies overall resilience. By addressing these challenges head-on, healthcare organizations can better protect themselves against the ever-evolving landscape of cyber threats.

The rate of reported breaches serves as a crucial metric that indicates a company's cybersecurity posture. In today's landscape, where threats are ever-evolving, organizations must analyze incident occurrence trends to pinpoint vulnerabilities. Did you know that nearly 88% of data breaches in 2025 were linked to human error? This statistic underscores the urgent need for improved training.
Consistent reporting of breaches not only aids in identifying weaknesses but also plays a vital role in achieving compliance. With the average cost nearing $4.44 million in 2025, prioritizing event reporting is essential for mitigating financial risks and enhancing overall security measures. Moreover, organizations that actively engage in incident reporting demonstrate greater resilience. For instance, those conducting regular tabletop exercises reported improved clarity in roles and decision-making during critical incidents.
This proactive approach not only fortifies defenses but also fosters a culture of security awareness—an essential element for navigating the complexities of today's threat environment. As a result, it is imperative for organizations to take decisive action, ensuring they are not just reactive but strategically prepared to face potential threats head-on.

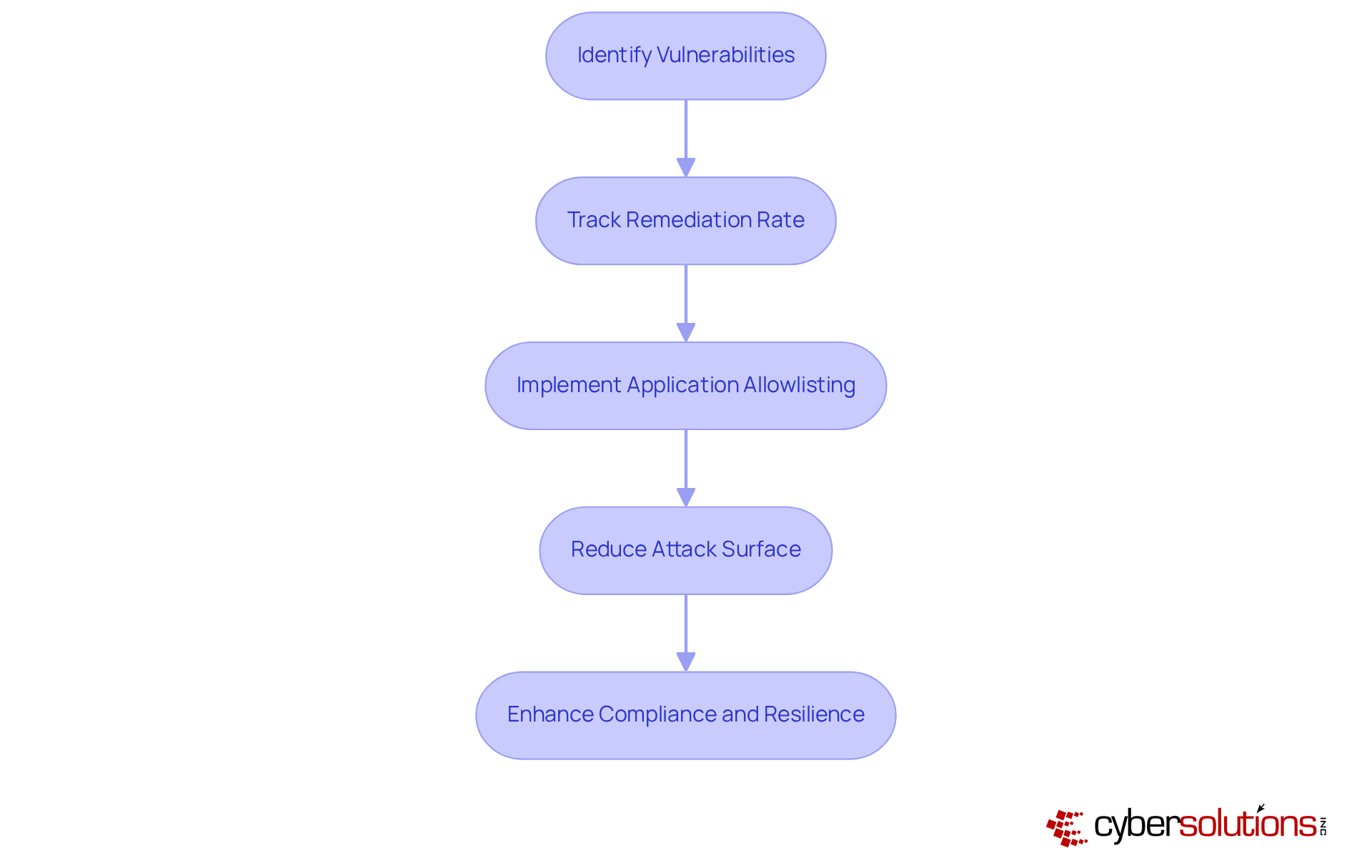
In today's digital landscape, the importance of cybersecurity in healthcare cannot be overstated. The vulnerability remediation rate, which tracks the percentage of identified vulnerabilities successfully addressed within a specified timeframe, serves as a crucial metric for organizations. A high remediation rate is an important indicator that reflects a company's commitment to maintaining a secure environment and minimizes potential attack vectors that could jeopardize sensitive data.
Healthcare organizations face unique challenges in cybersecurity, making it imperative to prioritize remediation programs that enable prompt remediation of identified risks, which should be measured through key performance indicators. Implementing endpoint protection emerges as a critical component of this strategy. By proactively preventing unauthorized software from executing, organizations can significantly reduce their attack surface and minimize vulnerabilities.
This approach not only mitigates risks associated with malware and ransomware but also ensures compliance with regulations such as HIPAA. Have you considered how integrating security awareness training into your cybersecurity framework could enhance your efforts? By doing so, entities can bolster their overall resilience against evolving threats, ensuring a safer environment for both patients and providers.
The phishing click rate is a vital metric, showcasing the percentage of employees who interact with phishing links during simulated attacks. A high click rate signals an urgent need for improvement. Organizations that regularly conduct training can significantly elevate security awareness; for instance, a comprehensive training program led to a remarkable 60% reduction in errors during simulated phishing attacks. One company, after implementing ongoing phishing training, reported a decrease in click rates from 15% to just 6% regarding the submission of personal information during tests.
The significance of these simulations cannot be overstated. They not only educate employees on how to recognize and report phishing attempts but also cultivate a culture of vigilance. Firms that have adopted regular training sessions have witnessed a notable decline in click rates, with some achieving an impressive 80% reduction in risky behaviors after a year of continuous training. This proactive approach empowers employees to become defenders against cyber threats, transforming them from potential victims into vigilant protectors of their organization’s digital assets.
Given the evolving threat landscape, where 82.6% of phishing emails now employ AI-generated content, organizations must prioritize employee training. By doing so, they can effectively lower their overall phishing susceptibility and bolster their security posture, ensuring that employees are well-prepared to identify and respond to phishing threats.

The completion rate is a crucial metric that reflects the percentage of employees who have successfully completed mandatory training. High completion rates signify a strong commitment to cultivating a robust culture of security awareness. Regular training not only equips employees with essential skills to identify potential threats but also empowers them to act as the first line of defense against cyberattacks.
Recent trends reveal that organizations prioritizing role-specific content and adaptive training methods experience notable improvements in engagement and effectiveness. For example, companies implementing consistent, behavior-based training have reported an impressive 86% reduction in security incidents over the course of a year. At Cyber Solutions, measures were taken to eliminate potential attack vectors and refresh protective configurations, alongside prompt training for staff on recognizing suspicious emails and maintaining proper online safety practices.
Moreover, fostering a culture of awareness involves recognizing employees for their proactive actions, which can enhance participation rates and overall attentiveness. As a result, integrating protective practices into daily workflows becomes essential. This ensures that employees are not only trained but are vigilant.

Cybersecurity is not just a technical issue; it’s a critical business imperative, especially in healthcare. The cost metric serves as a vital indicator of the average financial impact of security breaches on organizations. This metric includes both direct costs, like remediation efforts, and indirect costs, such as reputational damage and potential loss of business. Recent findings reveal that the average cost has soared to an astonishing $10.22 million, highlighting the escalating financial risks. Alarmingly, nearly half of the organizations that faced a breach reported significant losses as a direct consequence of these incidents.
By meticulously analyzing the cost data, companies can uncover valuable insights into the financial ramifications of their cybersecurity posture, which serves as an important decision-making tool. This understanding empowers them to make informed decisions about future investments in security measures related to risk management. For instance, organizations utilizing AI-driven protective systems have experienced an average cost reduction of $1.76 million per breach, underscoring the potential of technology to mitigate financial risks.
The complexity of data storage environments, particularly in sectors like healthcare, further exacerbates financial losses and extends containment times. Organizations that effectively map and categorize their data assets can enhance their protection frameworks, ultimately reducing the financial fallout from potential breaches. As cyber threats continue to evolve, grasping the financial implications of security events becomes essential for organizations aiming to achieve their business objectives while maintaining resilience and operational efficiency.
Investing in tailored IT services from Cyber Solutions, including features like proactive monitoring and incident response planning, not only safeguards your business but also boosts operational efficiency, maximizing ROI. With a flat-rate pricing structure, companies can streamline budgeting and eliminate unexpected IT costs, ensuring they are prepared for any situation. Moreover, Cyber Solutions' rapid incident response strategies, featuring 24/7 on-site support and a layered recovery approach, are crucial for minimizing damage and ensuring continuity of operations, particularly in healthcare where patient safety and data integrity are paramount.

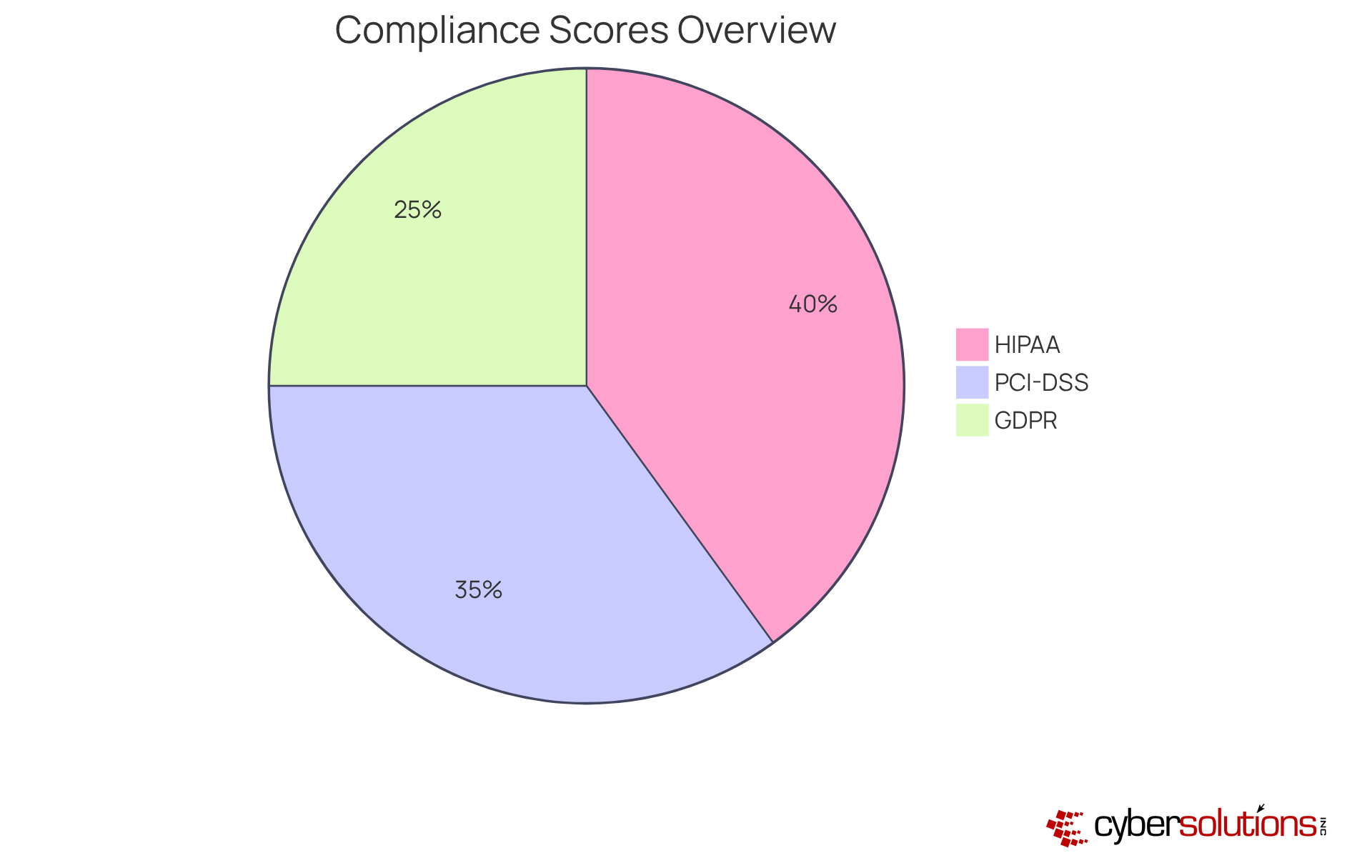
In today's digital landscape, the compliance score is crucial for assessing a company's adherence to regulations. A high compliance score is not just about avoiding legal penalties; it’s about protecting sensitive data from breaches. Did you know that 87% of entities report security incidents? Regular evaluations of compliance status are vital to prevent such risks.
To maintain compliance, organizations must implement and adapt to evolving regulations. This proactive approach not only enhances security posture but also builds trust with stakeholders. In fact, 90% of executives believe that compliance is essential for business success. By establishing a robust compliance framework, organizations can effectively mitigate risks associated with security threats and enhance their resilience as part of their overall cybersecurity strategy.
In today's digital landscape, the importance of tracking essential KPIs in cybersecurity cannot be overstated. These metrics are foundational tools that empower organizations to bolster their defenses against an ever-evolving threat landscape. By concentrating on key indicators such as:
businesses can not only protect their digital assets but also align their cybersecurity strategies with broader financial objectives, ensuring a solid return on investment.
The insights presented underscore the critical role of proactive monitoring and employee training in mitigating risks associated with cyber incidents. With a staggering percentage of breaches stemming from human error, it’s clear that fostering a culture of awareness and preparedness is paramount. Organizations that prioritize these metrics often see improved operational efficiency, reduced incident costs, and enhanced compliance with regulatory standards, ultimately leading to a stronger security posture.
As the digital landscape continues to evolve, embracing comprehensive cybersecurity metrics is essential for any organization aiming for long-term resilience. By investing in tailored cybersecurity solutions and fostering a proactive approach to training and incident management, businesses can not only safeguard their assets but also cultivate a culture of security that empowers every employee to act as a guardian of their organization. The time to act is now; prioritize these essential KPIs to fortify defenses and ensure a more secure future.
What is the importance of cybersecurity metrics for businesses?
Cybersecurity metrics are essential for bolstering business resilience by evaluating security measures and aligning them with financial strategies to showcase return on investment (ROI). They help organizations navigate cybersecurity complexities and ensure robust protection against evolving threats.
What are some key cybersecurity metrics mentioned in the article?
Key cybersecurity metrics include Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR). These metrics enhance risk mitigation capabilities by enabling quicker detection and response to potential threats.
How does a shorter Mean Time to Detect (MTTD) benefit an organization?
A shorter MTTD leads to quicker detection of potential threats, resulting in faster responses and recovery. This ultimately reduces downtime and associated costs, improving the organization's overall security posture.
What role does human error play in cybersecurity incidents?
Human error is responsible for 90% of cyber incidents, highlighting the need for training programs that focus on cybersecurity metrics to elevate employee awareness and minimize vulnerabilities.
How does Cyber Solutions Inc. support organizations in enhancing their cybersecurity?
Cyber Solutions Inc. provides comprehensive training, 24/7 IT support, and proactive monitoring services to empower employees and fortify defenses against cyber threats.
What is the significance of monitoring cybersecurity KPIs?
Monitoring cybersecurity KPIs is crucial for informed decision-making, effective resource allocation, and maintaining compliance with regulatory standards. It lays the groundwork for organizations to prepare for audits and meet stringent compliance requirements.
How can organizations improve their Mean Time to Detect (MTTD)?
Organizations can improve MTTD by implementing real-time monitoring solutions, conducting regular training simulations, utilizing automated response playbooks, and addressing the challenge of false positives.
What is the Mean Time to Respond (MTTR) and why is it important?
MTTR is a critical cybersecurity KPI that measures the average time taken to respond to a security incident. Reducing MTTR is vital for minimizing the impact of breaches and swiftly restoring normal operations.
What strategies can organizations use to reduce their MTTR?
Organizations can reduce MTTR by implementing robust response plans, leveraging automation tools, conducting crisis response exercises regularly, and ensuring 24/7 network monitoring and alerts.
How does Cyber Solutions enhance incident response for organizations?
Cyber Solutions enhances incident response through 24/7 network monitoring, immediate detection of anomalies, customized remediation strategies, and comprehensive documentation for audits, ensuring effective damage mitigation and business continuity.