Introduction
Achieving compliance with the Cybersecurity Maturity Model Certification (CMMC) is no longer merely a regulatory checkbox for defense contractors; it has become a crucial element in protecting sensitive information within an increasingly complex cyber landscape. In today’s environment, where cyber threats are ever-evolving, organizations must recognize that CMMC compliance is essential not just for regulatory adherence but for safeguarding their operations and reputations.
This guide provides a step-by-step approach to navigating the intricacies of CMMC, empowering organizations to bolster their cybersecurity posture while ensuring eligibility for critical Department of Defense contracts. As the deadline for full compliance approaches, organizations face pressing questions:
- How can they effectively prepare?
- What strategies can they implement to adapt to the evolving requirements of this essential framework?
By understanding the current landscape of cybersecurity threats and their implications, organizations can take proactive steps to enhance their defenses. The time to act is now-let’s explore how to navigate these challenges effectively.
Understand the Cybersecurity Maturity Model Certification (CMMC)
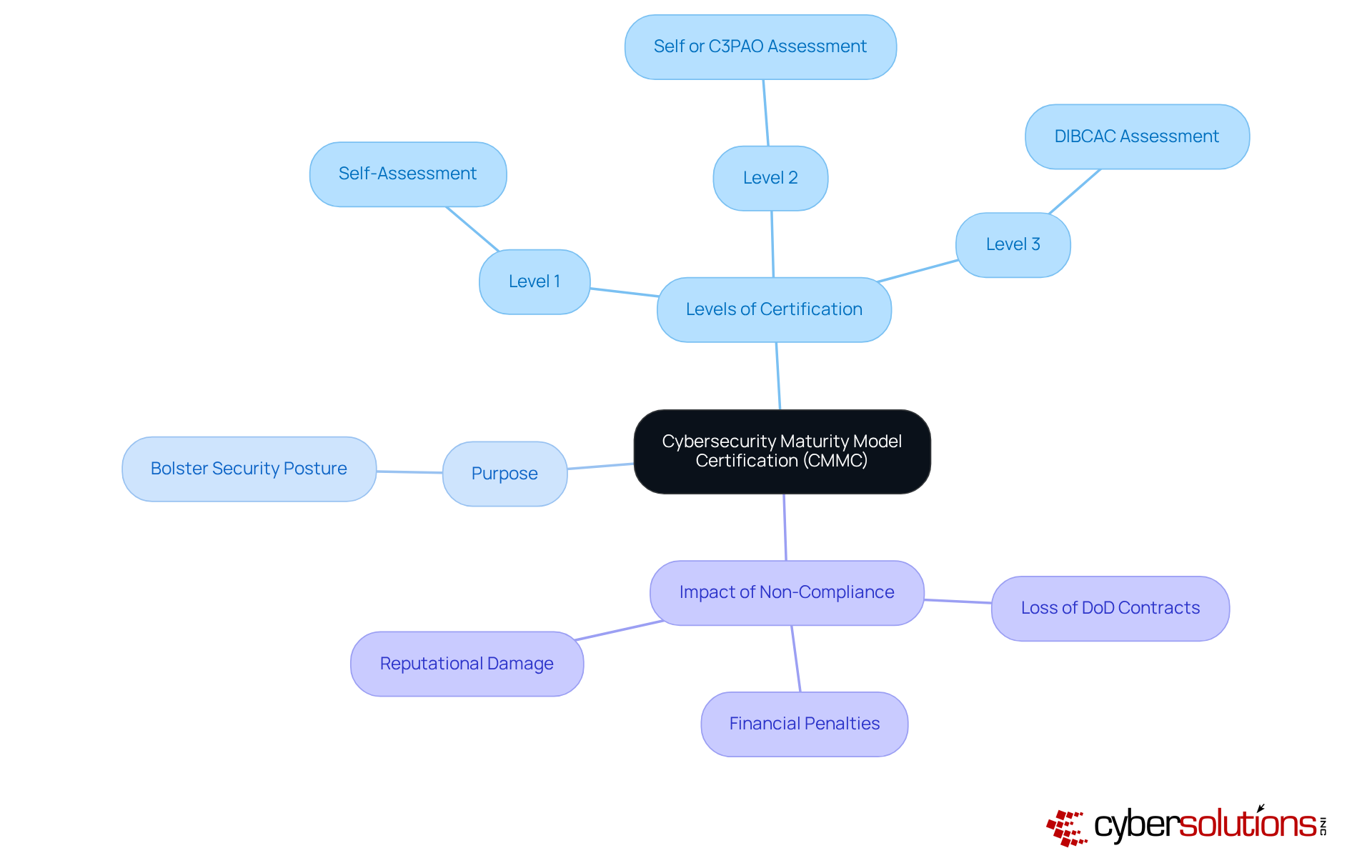
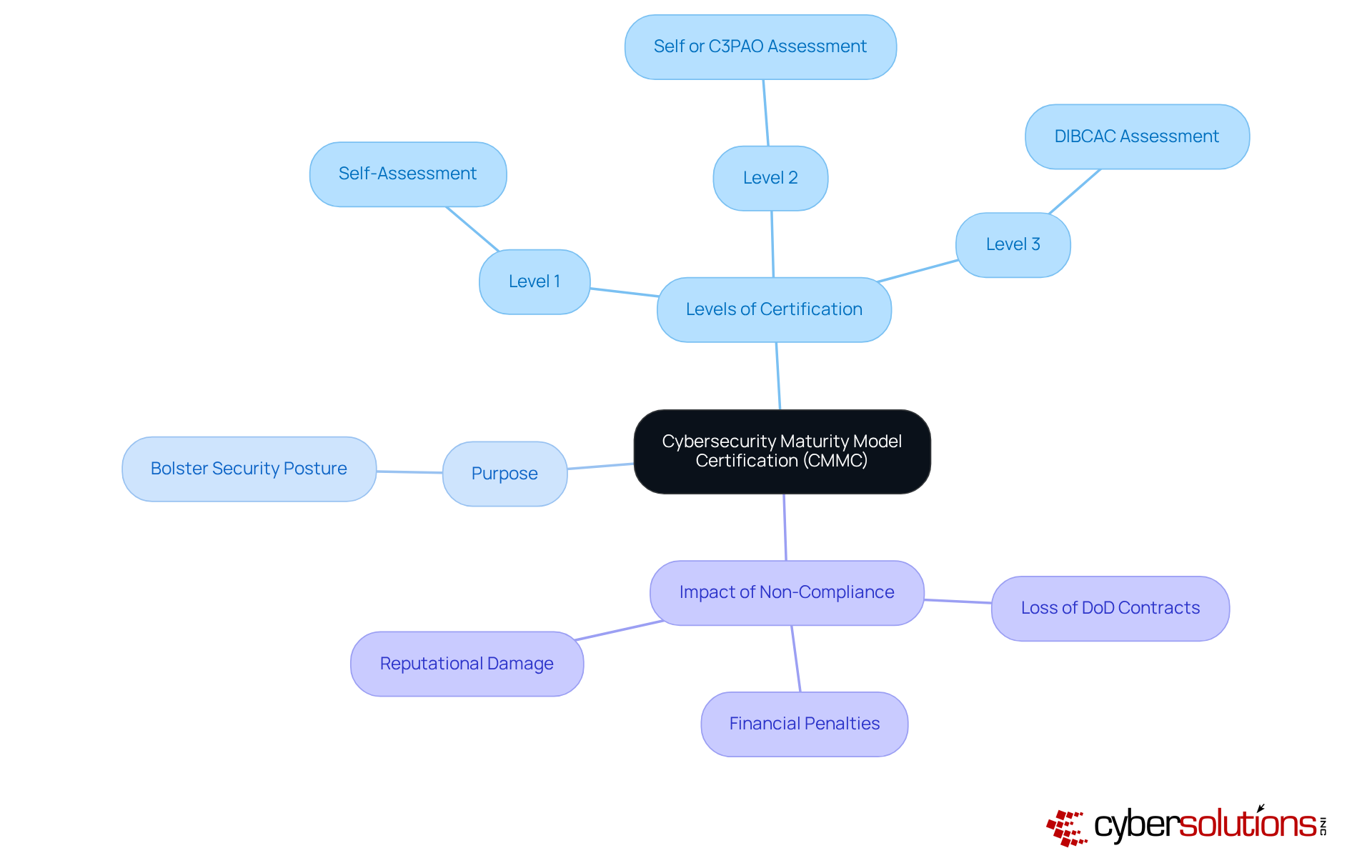
The Cybersecurity Maturity Model Certification (CMMC) stands as a crucial framework established by the U.S. Department of Defense (DoD) to ensure that contractors effectively safeguard sensitive information. This framework integrates various standards, providing a systematic approach to assess a company's cybersecurity posture.
Key Components of CMMC:
- Levels of Certification: The framework includes multiple levels, each defined by distinct practices and processes. Understanding these levels is crucial for developing the appropriate strategy for your organization.
- Purpose: The primary aim of the CMMC is to bolster the security posture of entities within the defense industrial base (DIB) by mandating the adoption of best practices.
- Consequences: Non-compliance with the certification can result in severe repercussions, such as the loss of DoD contracts, financial penalties, and damage to reputation. Therefore, comprehending the intricacies of cybersecurity maturity model compliance is vital for protecting your organization against the ever-evolving landscape of cyber threats.
As the deadline approaches, staying informed about updates and regulatory requirements is imperative for defense contractors. The certification process, set to be fully operational by November 10, 2028, underscores the need for proactive measures to ensure compliance and mitigate risks associated with cybersecurity failures. Experts in the field assert that adhering to the framework not only secures sensitive information but also enhances overall operational integrity, making it a fundamental aspect of modern defense contracting.
Explore CMMC Levels and Requirements
, each with distinct requirements that organizations must meet to ensure compliance. Understanding these levels is crucial for any organization aiming to achieve cybersecurity maturity and compliance.
Level 1: Basic Safeguarding
- Focus: Protecting Federal Contract Information (FCI).
- Requirements: Organizations must implement 15 foundational security practices, including access control and user identification, to establish a basic level of safeguarding. This initial step is vital for laying the groundwork for more advanced security measures.
- Focus: Protecting Controlled Unclassified Information (CUI).
- Requirements: This level necessitates adherence to 110 practices aligned with NIST SP 800-171, which encompass risk assessments, incident response plans, and other critical security measures to enhance protection. Notably, automation can significantly reduce the typical duration for obtaining compliance from 6-12+ months, simplifying the regulatory process. Additionally, applying application allowlisting at this level is essential, as it proactively stops unauthorized software from running, thus decreasing vulnerabilities and assisting entities in meeting regulatory requirements.
- Focus: Organizations managing the most sensitive information.
- Requirements: Involves the implementation of advanced security practices and processes, including continuous monitoring and incident response to safeguard against sophisticated threats. Application allowlisting plays a crucial role here as well, ensuring that only approved applications can run, which is essential for protecting sensitive data and maintaining regulatory standards.
Grasping these levels enables entities to assess their current posture and determine the essential actions to achieve compliance. It's crucial to note that noncompliance with the specified standards at Level 2 increases exposure to the risk of data breaches, underscoring the importance of adhering to these regulations. As companies prepare for the forthcoming 2026 standards for contractors, being aware of these levels and their implications is vital for upholding regulations and safeguarding sensitive information.

Prepare for CMMC Compliance: Actionable Steps
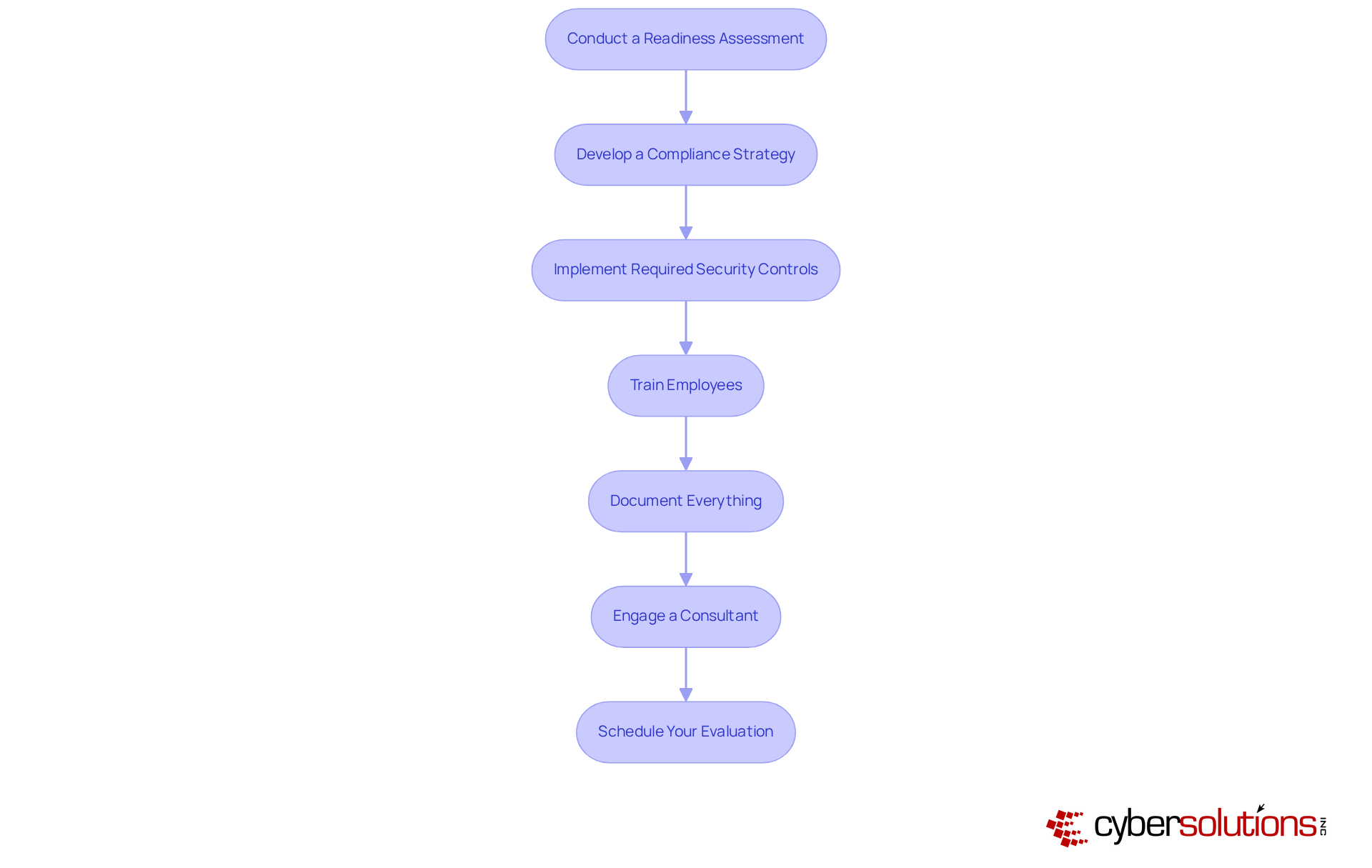
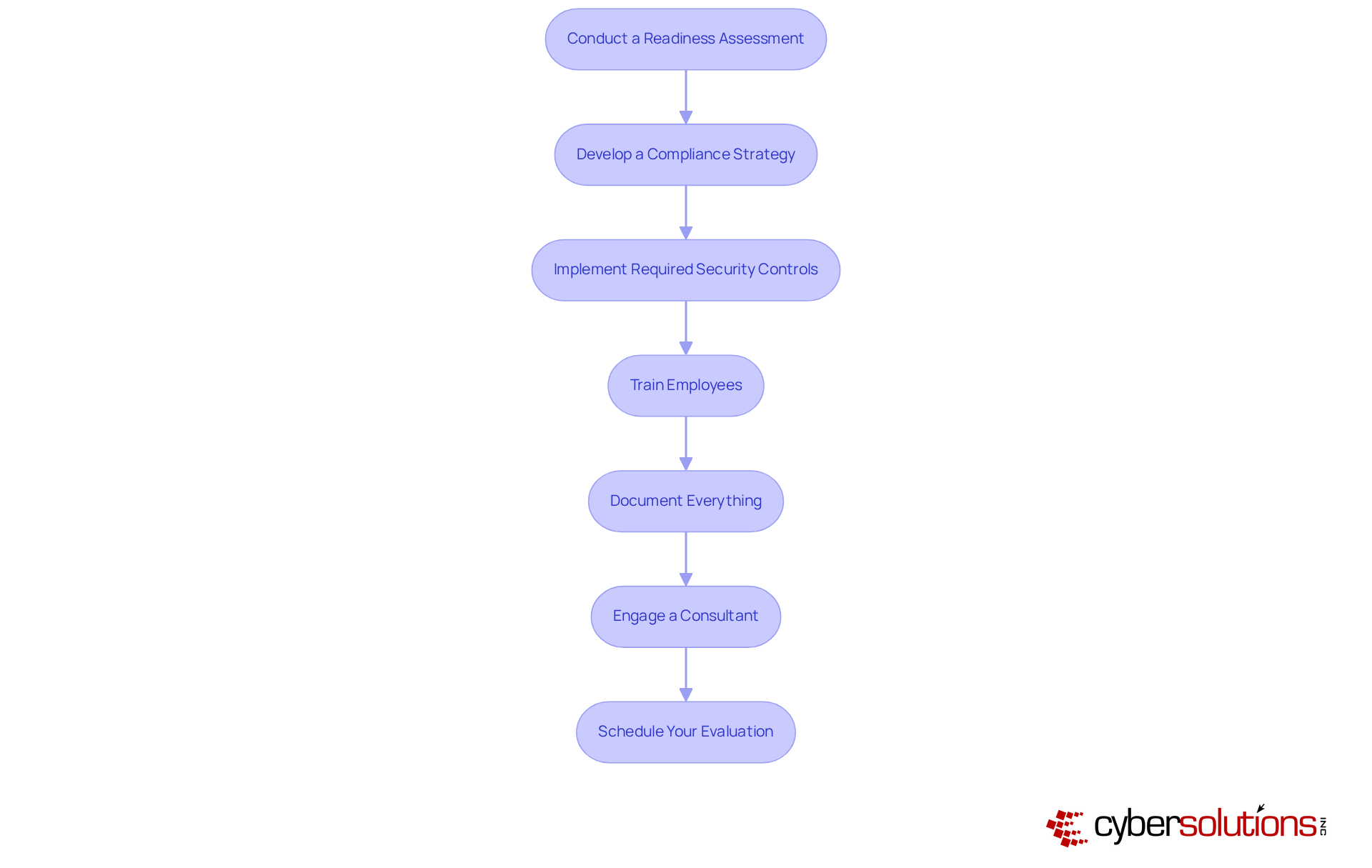
To effectively prepare for CMMC compliance, organizations must take decisive action. Compliance is not just a regulatory requirement; it’s a critical component of operational integrity. Here are the essential steps to ensure your organization meets CMMC requirements:
- Assess Current Practices: Begin by evaluating your current cybersecurity practices against CMMC requirements to pinpoint any gaps. This initial assessment is crucial, as the Department of Defense estimates that 152 to 440 labor hours are needed for achieving compliance during a Level 2 self-assessment.
- Create a Comprehensive Plan: Create a comprehensive plan that outlines the necessary steps to achieve conformity, including specific timelines and designated responsibilities. This plan should be adaptable to changes in your organization, such as technology shifts or new data flows, while ensuring compliance.
- Implement Security Measures: Based on the gaps identified, implement essential security measures, including access controls, encryption, and security protocols. Automation and AI can significantly streamline this process, potentially compressing the timeline for achieving compliance.
- Train Employees: Ensure that all employees are well-informed about their roles in maintaining cybersecurity and adherence to regulations. Regular training sessions can enhance awareness and readiness for compliance throughout the organization.
- Maintain Documentation: Maintain thorough documentation of all processes, policies, and training efforts. This documentation is essential for showcasing compliance during evaluations and can help reduce risks linked to audits.
- Hire a Specialist: Consider hiring a specialist with knowledge in cybersecurity maturity model certification to guide your organization through the process. Their insights can be invaluable in navigating the complexities of CMMC requirements.
- Schedule Your Evaluation: Once you feel your organization is compliant, arrange a formal assessment with a certified assessor. This step is critical to validate your compliance and ensure your readiness for contract eligibility with the Department of Defense.
By following these steps, organizations can significantly enhance their information security posture and ensure they are well-prepared for the upcoming regulatory deadline in March 2026.
Maintain Compliance: Continuous Assessment and Improvement
In today's rapidly evolving digital landscape, maintaining CMMC compliance is not just a regulatory requirement; it's a critical necessity for safeguarding sensitive information. As we approach 2026, the urgency for readiness preparations intensifies. Organizations must adopt a proactive approach that encompasses several key strategies to ensure they meet the evolving demands of cybersecurity.
- Regular Self-Assessments: Conduct assessments to evaluate the effectiveness of your security practices. This process is essential for identifying vulnerabilities and ensuring that your entity achieves compliance with the necessary standards. Cybersecurity experts emphasize that routine self-assessments are crucial for maintaining a robust security posture and adapting to evolving threats.
- Continuous Monitoring: Implement systems that provide real-time detection and response capabilities for security incidents. Current trends suggest that entities are progressively utilizing automated monitoring tools to improve their security frameworks, enabling rapid response to potential breaches.
- Update Policies and Procedures: Regularly review and revise your policies to reflect changes in technology and regulatory requirements. This ensures that your organization remains compliant with the latest standards and best practices.
- Employee Training: Provide ongoing training for employees to keep them informed about the latest cybersecurity threats and best practices. A well-informed workforce is a critical line of defense against cyber threats, and continuous education fosters a culture of security awareness.
- Engage in Audits: Arrange regular audits with outside evaluators to confirm your adherence status. These audits not only verify alignment with regulations but also provide valuable insights for enhancement, assisting entities in achieving and staying ahead of regulatory requirements.
- Document Changes: Keep detailed records of all modifications made to your security practices and policies. This documentation is essential for showing adherence during evaluations and ensuring that your organization can effectively respond to any inquiries regarding its cybersecurity posture.
Furthermore, implementing security measures can significantly enhance your cybersecurity posture by preventing unauthorized software from executing, thereby reducing vulnerabilities and ensuring compliance with stringent data protection protocols. By prioritizing these strategies, organizations can not only meet but also fortify their defenses against the ever-present threat of cyber attacks.

Conclusion
Achieving compliance with the Cybersecurity Maturity Model Certification (CMMC) is not just a regulatory requirement; it’s a crucial step for organizations involved in defense contracting to protect sensitive information from escalating cyber threats. Understanding the framework's levels and requirements enables organizations to craft effective strategies that not only meet compliance standards but also bolster their overall cybersecurity posture.
Key components of CMMC include:
- Distinct certification levels
- The necessity for comprehensive readiness assessments
- The importance of continuous monitoring and improvement
Organizations must take actionable steps to prepare for compliance, focusing on:
- Thorough documentation
- Employee training
- Proactive engagement with cybersecurity experts
These elements collectively form a robust foundation for achieving and maintaining CMMC compliance.
The significance of CMMC compliance goes beyond mere regulatory adherence; it embodies a commitment to safeguarding sensitive data and ensuring operational integrity within the defense industrial base. As the 2026 deadline approaches, organizations must prioritize their compliance efforts and recognize the long-term benefits of a strong cybersecurity framework. By taking decisive action now, entities can secure their contracts and fortify their defenses against the ever-evolving landscape of cyber threats.
Frequently Asked Questions
What is the Cybersecurity Maturity Model Certification (CMMC)?
The CMMC is a framework established by the U.S. Department of Defense (DoD) to ensure that contractors effectively safeguard sensitive information by integrating various cybersecurity standards and best practices.
What are the key components of the CMMC?
The key components of the CMMC include levels of certification, the purpose of enhancing security within the defense industrial base (DIB), and the impact of non-compliance.
How many levels of certification are included in the CMMC?
The CMMC includes multiple levels of certification, each defined by distinct practices and processes that organizations must understand to develop a compliance strategy.
What is the primary purpose of the CMMC?
The primary purpose of the CMMC is to bolster the security posture of entities within the defense industrial base (DIB) by mandating the adoption of robust cybersecurity practices.
What are the consequences of non-compliance with the CMMC?
Non-compliance can lead to severe repercussions, including the loss of DoD contracts, financial penalties, and damage to an organization’s reputation.
When is the CMMC set to be fully operational?
The CMMC is set to be fully operational by November 10, 2028.
Why is it important for defense contractors to stay informed about the CMMC?
It is important for defense contractors to stay informed about updates and regulatory requirements to ensure compliance and mitigate risks associated with cybersecurity failures.
How does adhering to the CMMC benefit organizations?
Adhering to the CMMC not only secures sensitive information but also enhances overall operational integrity, making it a fundamental aspect of modern defense contracting.
List of Sources
- Understand the Cybersecurity Maturity Model Certification (CMMC)
- hklaw.com (https://hklaw.com/en/insights/publications/2025/09/cmmc-goes-live-new-cybersecurity-requirements)
- cybersheath.com (https://cybersheath.com/resources/blog/state-of-the-dib-report-2025-only-1-of-contractors-are-ready-for-cmmc)
- Department of Defense Publishes Final Rule to Implement Cybersecurity Maturity Model Certification 2.0 in Solicitations and Contracts - ConsensusDocs (https://consensusdocs.org/news/department-of-defense-publishes-final-rule-to-impl)
- Department of Defense Finalizes Cybersecurity Maturity Model Certification Rule: Heightened False Claims Act Exposure for Cybersecurity Missteps - O'Melveny (https://omm.com/insights/alerts-publications/department-of-defense-finalizes-cybersecurity-maturity-model-certification-rule-heightened-false-claims-act-exposure-for-cybersecurity-missteps)
- A Quiet Policy Shift Just Redefined Entire Federal Cybersecurity Landscape (https://forbes.com/sites/emilsayegh/2026/02/07/a-quiet-policy-shift-just-redefined-entire-federal-cybersecurity-landscape)
- Explore CMMC Levels and Requirements
- cmmc.com (https://cmmc.com/newsroom/cmmc-enforcement-day-one-few-companies-ready)
- Preparing for CMMC: Navigating DoD’s New Cybersecurity Rules | Insights | Dickinson Wright (https://dickinson-wright.com/news-alerts/client-alert-dorn-preparing-for-cmmc)
- CMMC Changes Cybersecurity Requirements for Defense Contractors - AGC News (https://news.agc.org/advocacy/cmmc-changes-cybersecurity-requirements-for-defense-contractors)
- What You Need to Know Heading Into 2026 | Fortra (https://fortra.com/blog/cmmc-compliance-what-you-need-know-heading-2026)
- Prepare for CMMC Compliance: Actionable Steps
- Report finds large gap in CMMC readiness among defense industrial base (https://defensescoop.com/2025/01/28/redspin-report-cmmc-readiness-gap-2025-defense-industrial-base)
- cmmc.com (https://cmmc.com/newsroom/cmmc-enforcement-day-one-few-companies-ready)
- What You Need to Know Heading Into 2026 | Fortra (https://fortra.com/blog/cmmc-compliance-what-you-need-know-heading-2026)
- Preparing for CMMC: Navigating DoD’s New Cybersecurity Rules | Insights | Dickinson Wright (https://dickinson-wright.com/news-alerts/client-alert-dorn-preparing-for-cmmc)
- Planning Your 2026 CMMC Compliance Roadmap (https://cybersheath.com/resources/blog/planning-your-2026-cmmc-compliance-roadmap)
- Maintain Compliance: Continuous Assessment and Improvement
- CMMC Compliance in 2026: How Did We Get Here and What’s Coming Next (https://112cyber.com/blog/cmmc-compliance-in-2026)
- CMMC 2.0 Level 2 Simplified: Steps, Controls List & Checklist (https://strikegraph.com/blog/cmmc-2-level-2-requirements)
- CMMC Certification vs. Self-Assessment What You Need to Know (https://agileit.com/news/cmmc-certification-vs-self-assessment-what-you-need-to-know)
- CMMC Compliance Support: 5 Tips for Maintaining Your CMMC Compliance Status (https://isidefense.com/blog/cmmc-compliance-support-5-tips-for-maintaining-your-cmmc-compliance-status)
- nationaldefensemagazine.org (https://nationaldefensemagazine.org/articles/2024/10/1/few-companies-ready-for-cmmc-compliance-study-finds)