
In today’s tech-driven landscape, the importance of IT managed services contracts is paramount. These agreements are not just formalities; they represent strategic partnerships that delineate the scope of IT support, cybersecurity measures, and operational responsibilities between businesses and managed service providers. As organizations grapple with the complexities of modern cybersecurity threats and compliance demands, a pressing question emerges: how can C-suite leaders ensure that these contracts not only safeguard their assets but also propel business growth?
Understanding the nuances of IT managed services contracts is crucial for executives aiming to bolster their operational resilience and gain a competitive edge. By recognizing the strategic value of these agreements, leaders can navigate the intricate web of cybersecurity challenges effectively, ensuring that their organizations are not only protected but also positioned for success.
An IT managed services contract is not just an agreement; it’s a crucial partnership between a business and a managed services provider that delineates specific IT offerings, responsibilities, and terms of engagement. In today’s landscape, where technology is rapidly evolving, an IT managed services contract becomes essential. They typically encompass a variety of services, including network management, data backup, cloud services, and cybersecurity.
A key component of cybersecurity in these agreements is threat detection. This proactive measure prevents malware and unauthorized software from executing, significantly bolstering the organization’s security posture. By establishing a legal framework, the agreement ensures that both parties are aligned on their responsibilities and performance expectations, which is vital for operational efficiency and accountability in IT management.
With a substantial number of companies now leveraging managed services, the focus is on enhancing IT operations while ensuring security and compliance. Effective agreements often include critical elements such as:
These components work together to streamline collaboration between the business and the managed services provider.
Incorporating comprehensive cybersecurity solutions, like application allowlisting, is not just beneficial; it’s essential for organizations aiming to meet stringent compliance requirements and safeguard against emerging threats. Cyber Solutions stands ready to address these challenges, ensuring that your organization remains resilient in the face of adversity.

In the current digital landscape, IT managed services are essential for organizations grappling with complex IT challenges and escalating costs. By outsourcing IT functions, businesses can leverage specialized expertise and cutting-edge technologies without the burden of in-house management. This strategic decision allows companies to focus on their core competencies while ensuring their IT infrastructure remains robust, secure, and compliant with industry regulations.
Cyber Solutions provides a comprehensive suite of features, including cloud services, proactive monitoring, and other critical components for maintaining IT systems and security. The benefits of outsourcing IT solutions are numerous. Organizations can realize significant savings by minimizing fixed salary expenses and overhead linked to maintaining an internal IT team. For instance, the typical monthly cost for basic managed IT support can range from $1,500 for 10 users to $100,000 for 500 users, offering scalable solutions tailored to organizational needs. Furthermore, outsourcing enables businesses to adjust their support levels dynamically, enhancing operational efficiency during peak demand while reducing costs during quieter times.
Current trends indicate a shift towards cybersecurity-as-a-service, driven by the increasing complexity and frequency of cyber threats. With 88% of ransomware victims being organizations with fewer than 1,000 employees, the urgency for cybersecurity measures has never been greater. Managed service providers are now incorporating AI and machine learning for predictive analytics and proactive security strategies, ensuring organizations can respond swiftly to potential threats.
Numerous examples exist of companies benefiting from managed IT services. Organizations that have transitioned to these controlled solutions report improved operational resilience, reduced downtime, and enhanced security postures. For example, businesses utilizing outsourced support have seen a decrease in productivity interruption hours, which can significantly impact their financial performance.
Expert insights reveal that an IT managed services contract, when well-structured, not only provides predictability in expenses and performance levels but also fosters a culture of accountability and continuous improvement. As companies face ongoing regulatory pressures and the need for innovation, investing in managed IT solutions is no longer just a cost-saving measure; it has become a strategic enabler for growth and competitive advantage.

Key components of IT managed services contract are crucial for ensuring robust cybersecurity in healthcare.
These elements are essential for creating a comprehensive agreement and ensuring that the IT managed services contract aligns with the entity's strategic objectives.

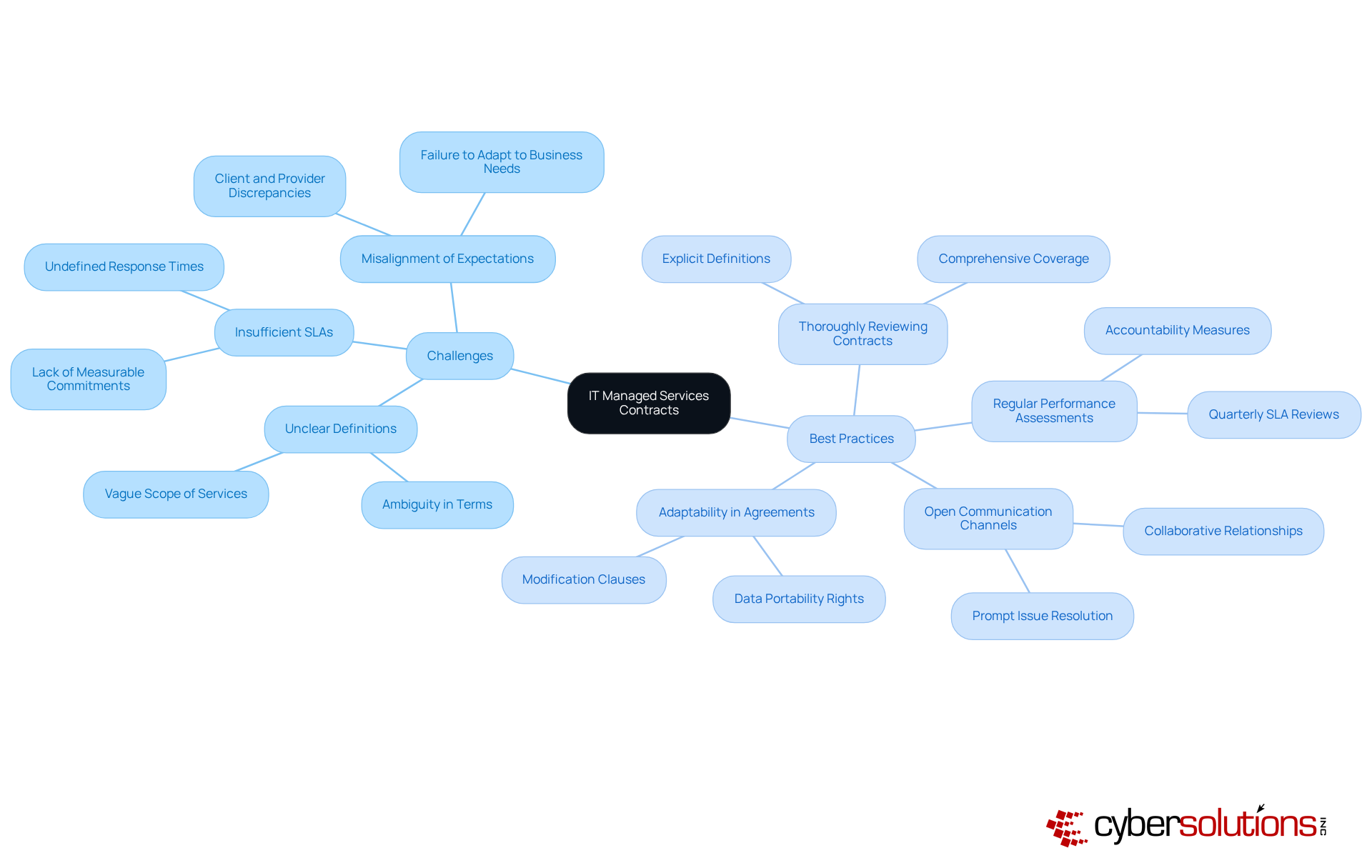
Difficulties in IT outsourcing agreements often stem from unclear definitions, insufficient service level agreements, and misalignment of expectations between clients and outsourcing providers. Addressing these challenges is crucial for organizations aiming to optimize their IT performance. Here are some best practices:
By implementing these best practices, organizations can significantly enhance their IT operations, which leads to improved IT performance and reduced operational risks. It's important to recognize that IT projects often exceed budget forecasts by an average of 27%, with some reaching up to 200%. This underscores the critical need for effective management and oversight.
In conclusion, IT managed services contracts are not just agreements; they are essential partnerships that lay the groundwork for effective collaboration between businesses and managed service providers. These contracts establish a clear framework for responsibilities and cybersecurity measures, serving as strategic tools that enhance operational efficiency and mitigate risks. As organizations face an increasingly complex digital landscape, the significance of these agreements is paramount.
Key components such as service level agreements, detailed scopes of services, and well-defined termination clauses are vital for fostering accountability. They ensure that both parties share aligned expectations. Furthermore, integrating robust cybersecurity measures, like application allowlisting, is crucial for safeguarding sensitive data and adhering to regulatory standards. By adopting these contracts, organizations can streamline their IT operations while positioning themselves for sustainable growth and a competitive edge.
The ever-evolving nature of cybersecurity threats, coupled with the trend towards outsourcing IT functions, highlights the necessity for well-structured managed services agreements. Executives must prioritize the development and management of these contracts to effectively navigate challenges and leverage best practices. By doing so, organizations can transform potential risks into opportunities for innovation and resilience, ensuring they remain leaders in their industries.
What is an IT managed services contract?
An IT managed services contract is a partnership between a business and a managed service provider (MSP) that outlines specific IT services, responsibilities, and terms of engagement.
Why are IT managed services contracts important?
They are essential in today’s environment due to the evolving cybersecurity threats, helping organizations enhance IT operations while mitigating risks associated with cybersecurity and compliance.
What types of services are typically included in an IT managed services contract?
Services often include network management, cybersecurity measures, data backup, and technical assistance.
What is application allowlisting and why is it important?
Application allowlisting is a cybersecurity measure that prevents malware and unauthorized software from executing, significantly enhancing an organization’s security posture.
What are some critical elements included in effective IT managed services contracts?
Effective contracts often include service level agreements (SLAs), detailed outlines of contributions, and clear termination clauses.
How do these elements contribute to the partnership between a business and an MSP?
These components streamline collaboration, ensure both parties are aligned on responsibilities, and enhance operational efficiency and accountability in IT management.
What role does Cyber Solutions play in relation to IT managed services contracts?
Cyber Solutions addresses challenges related to cybersecurity and compliance, helping organizations remain resilient against emerging threats.