Introduction
In today's digital landscape, local IT solutions are not just beneficial; they are essential for organizational success. As businesses strive to enhance operational efficiency and align their IT strategies with overarching goals, the importance of robust cybersecurity and compliance cannot be overstated. Yet, many organizations find themselves grappling with the complexities of IT integration.
How can they effectively assess their unique needs and implement tailored solutions that resonate with their specific challenges? Exploring this question opens the door to not only meeting current demands but also preparing for future growth.
Assess Organizational Needs for Tailored IT Solutions
To effectively execute IT solutions, organizations must start with a comprehensive assessment of their specific needs. This foundational process involves assessing the current IT infrastructure, identifying pain points, and understanding the unique operational needs of the business to develop tailored strategies. Here are the key steps to consider:
- Conducting interviews: Engaging with various departments is essential for gathering insights on their IT challenges and expectations. By interviewing 6-8 stakeholders, organizations can align on objectives and uncover any misconceptions that may hinder progress.
- Performing gap analysis: This critical step compares current capabilities against desired outcomes, helping to pinpoint areas for improvement. Organizations that prioritize this analysis experience 2.5 times higher transformation success rates, underscoring the importance of this analysis. Notably, 64% of entities cite data quality as their primary data integrity challenge, highlighting the necessity of addressing this issue during evaluations.
- Utilizing assessment tools: Leveraging tools and frameworks can effectively quantify needs and prioritize IT initiatives. Organizations with strong integration in transformation initiatives achieve 10.3 times the returns compared to those with poor integration, emphasizing the value of structured assessments.
- Creating a report: Crafting a comprehensive report that outlines the assessment results serves as a guide for selecting suitable IT options. This documentation is crucial for ensuring that the implemented IT strategies are not only effective but also aligned with the organization’s strategic goals.
By thoroughly evaluating organizational requirements, companies can enhance their operational efficiency and ensure that their IT approaches effectively address both current challenges and future growth.

Select IT Solutions that Align with Business Goals and Compliance
Choosing IT solutions that align with organizational objectives and compliance is crucial for entities looking to enhance performance and mitigate risks. In today’s landscape, where 54% of enterprises struggle to meet challenges in hybrid and multi-cloud environments, this process involves several key steps:
By strategically selecting IT solutions that align with both business objectives and compliance standards, companies can optimize their investments while minimizing potential risks associated with non-compliance.

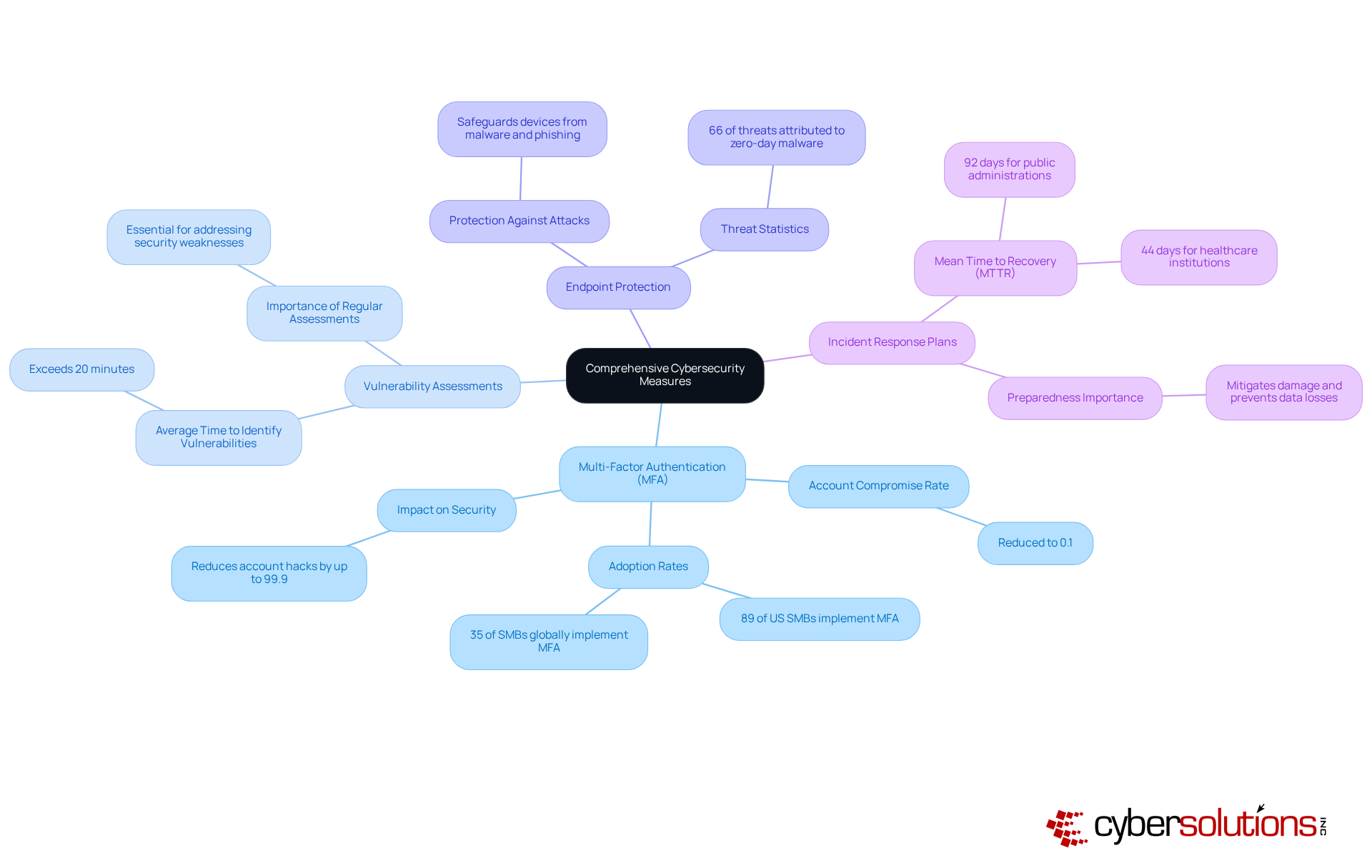
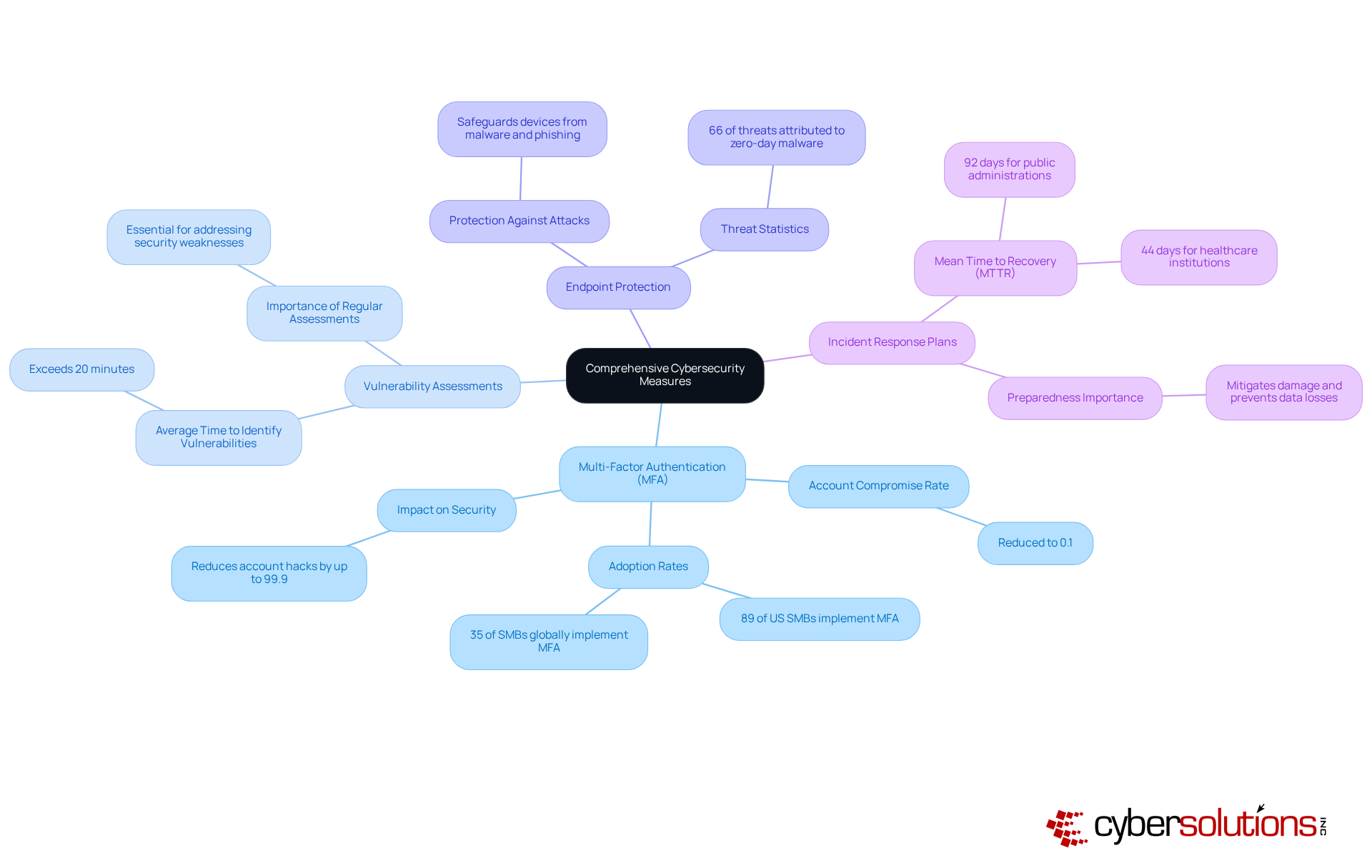
Integrate Comprehensive Cybersecurity Measures into IT Solutions
In today's digital landscape, the security of IT solutions is paramount, especially in healthcare. Companies must integrate comprehensive cybersecurity measures from the outset to safeguard sensitive information and maintain trust. Here are key practices that can fortify your defenses:
- MFA significantly enhances access security by requiring multiple forms of verification for users. This approach minimizes the risk of unauthorized access. Reports indicate that entities implementing MFA have reduced their account compromise rates to as low as 0.1%. Isn't it time your organization took this crucial step?
- Regular assessments are essential for identifying and addressing potential vulnerabilities in the IT infrastructure. With the average time surpassing 20 minutes, proactive assessments can significantly improve a company's security posture. How prepared is your organization to tackle these vulnerabilities?
- Deploying robust endpoint protection solutions safeguards devices connected to the network from various threats, including malware and phishing attacks. Given that 66% of all threats in recent quarters have been attributed to zero-day malware, effective endpoint protection is crucial. Are your endpoints adequately protected?
- Developing and regularly updating incident response plans ensures that entities can effectively respond to security incidents. The mean time to recovery (MTTR) for public administrations was reported at 92 days in 2022, highlighting the need for preparedness to mitigate damage and prevent data losses. Is your organization ready to respond swiftly?
By integrating these practices, companies can create a robust defense against cyber threats while ensuring compliance with industry regulations. As cybersecurity experts emphasize, the evolution of threats necessitates continuous improvement in security practices, making MFA a critical component of any comprehensive cybersecurity strategy. Don't wait for a breach to take action-strengthen your defenses today.
Provide Ongoing Support and Training for Effective IT Adoption
To enhance the effectiveness of adopted IT solutions, organizations must prioritize training for their employees. This commitment not only boosts productivity but also fosters a culture of learning and adaptability. Here are several key strategies to consider:
- Establish a training program: Create a structured curriculum that comprehensively covers the use of new technologies and best practices. This can be implemented within just a few months.
- Provide educational opportunities: Encourage employees to pursue further education and certifications relevant to their roles. Research shows that organizations investing in training experience faster adoption rates and improved data quality, ultimately enhancing overall performance.
- Create Support Channels: Implement resources to assist employees with challenges as they arise. The Uptime Institute highlights that ongoing support is crucial. By proactively addressing these challenges, organizations can significantly reduce the likelihood of costly disruptions.
- Collect Feedback: Regularly solicit input from users to identify areas for improvement and adjust training programs accordingly. Organizations that align educational initiatives with measurable business challenges can justify budget requests based on anticipated enhancements in performance metrics. Notably, effective training programs underscore the retention advantages of effective skill development.
By investing in ongoing support and training, organizations can ensure that employees are well-equipped to leverage local IT solutions effectively. This leads to improved productivity and reduced operational disruptions.

Conclusion
A successful implementation of local IT solutions is crucial for organizations aiming to thrive in today's competitive landscape. It hinges on a tailored approach that aligns with unique needs and objectives. By conducting thorough assessments, selecting appropriate solutions, integrating robust cybersecurity measures, and providing ongoing support and training, businesses can significantly enhance their operational efficiency and resilience against emerging challenges.
Key strategies include:
- Engaging stakeholders to identify specific pain points
- Selecting IT solutions that meet business goals while complying with regulatory standards
- Recognizing the critical role of cybersecurity in safeguarding sensitive information
Investing in continuous support and training not only fosters a culture of adaptability but also ensures that employees are equipped to leverage new technologies effectively.
Ultimately, adopting these best practices streamlines IT solutions implementation and positions organizations for long-term success. As the digital landscape evolves, prioritizing tailored IT strategies and fostering a culture of learning will be essential for businesses aiming to thrive. Embracing these principles today can lead to a more secure, efficient, and innovative future.
Frequently Asked Questions
What is the first step in executing local IT solutions for organizations?
The first step is to conduct a comprehensive assessment of the organization's specific needs, which includes evaluating the current IT infrastructure, identifying pain points, and understanding unique operational needs.
Why are stakeholder interviews important in the assessment process?
Stakeholder interviews are essential for gathering insights on IT challenges and expectations from various departments. Engaging with 6-8 stakeholders helps align objectives and uncover any misconceptions that may hinder progress.
What is a gap analysis and why is it important?
A gap analysis compares current IT capabilities against desired outcomes to identify areas for improvement. It is important because organizations that prioritize data quality experience significantly higher transformation success rates, and many cite data quality as a primary challenge.
How do assessment tools contribute to the evaluation of IT needs?
Assessment tools and frameworks help quantify needs and prioritize IT initiatives. Organizations with strong integration in transformation initiatives achieve much higher returns, demonstrating the value of structured assessments.
What should organizations do with the findings from their assessments?
Organizations should document the findings in a comprehensive report that outlines the assessment results. This documentation serves as a guide for selecting suitable IT options and ensures that implemented strategies align with the organization's strategic goals.
How can a thorough evaluation of organizational requirements benefit a company?
A thorough evaluation can enhance operational efficiency and ensure that IT approaches effectively address current challenges and support future growth.
List of Sources
- Assess Organizational Needs for Tailored IT Solutions
- Data Transformation Challenge Statistics — 50 Statistics Every Technology Leader Should Know in 2026 (https://integrate.io/blog/data-transformation-challenge-statistics)
- Quotes from Interviewing Users by Steve Portigal (https://shanegryzko.wordpress.com/2017/09/08/quotes-from-interviewing-users-by-steve-portigal)
- Select IT Solutions that Align with Business Goals and Compliance
- jumpcloud.com (https://jumpcloud.com/blog/it-compliance-statistics)
- 12 CIO Priorities for 2026 - TenHats (https://tenhats.com/cio-priorities)
- 110 security and compliance statistics for tech leaders to know in 2025 (https://vanta.com/resources/compliance-statistics)
- Strategic Alignment: Turning IT into a Business Advantage in 2026 | New Resources Consulting (https://newresources.com/strategic-alignment-turning-it-into-a-business-advantage-in-2026)
- 130+ Compliance Statistics & Trends to Know for 2026 (https://secureframe.com/blog/compliance-statistics)
- Integrate Comprehensive Cybersecurity Measures into IT Solutions
- Industry News 2025 Will MFA Redefine Cyberdefense in the 21st Century (https://isaca.org/resources/news-and-trends/industry-news/2025/will-mfa-redefine-cyberdefense-in-the-21st-century)
- 35 Cyber Security Vulnerability Statistics, Facts In 2026 (https://getastra.com/blog/security-audit/cyber-security-vulnerability-statistics)
- 2025 Multi-Factor Authentication (MFA) Statistics & Trends to Know (https://jumpcloud.com/blog/multi-factor-authentication-statistics)
- Multi-Factor Authentication (MFA) Statistics You Need To Know In 2025 | Dental Technologies (https://njda.org/news-information/news-archive/2025/11/25/multi-factor-authentication-(mfa)-statistics-you-need-to-know-in-2025---dental-technologies)
- Key Cyber Security Statistics for 2026 (https://sentinelone.com/cybersecurity-101/cybersecurity/cyber-security-statistics)
- Provide Ongoing Support and Training for Effective IT Adoption
- What Strategic IT Planning Looks Like in 2026 and Beyond (https://ntiva.com/blog/what-strategic-it-planning-looks-like-in-2026-and-beyond)
- Essential Employee Training Statistics for 2026 | Levelup LMS (https://leveluplms.com/key-employee-training-statistics-data-driven-trends-for-2026)
- The ROI of IT Training: What the Data Says (https://cbtnuggets.com/blog/training/training-strategy/roi-of-it-training)
- Employee training statistics show learning is moving beyond L&D - Coassemble (https://coassemble.com/blog/employee-training-statistics)
- How Training Impacts ERP Adoption Metrics - AorBorC Technologies | Zoho Certified Solution Providers (https://aorborc.com/how-training-impacts-erp-adoption-metrics)