
In today’s interconnected landscape, C-suite leaders face unprecedented demands to ensure seamless IT operations. The rise of 24/7 managed IT services offers a significant opportunity for executives to boost productivity, reduce risks, and streamline their operations. Yet, with the complexities of modern technology and the constant threat of cyber incidents looming large, how can leaders confidently navigate these challenges while keeping their eyes on strategic growth?
This article delves into the numerous benefits of round-the-clock IT support, illustrating how it can enhance operational efficiency and protect organizational success.
In today's fast-paced business environment, having IT support is not just an option—it's a necessity. Cyber Solutions ensures that IT issues are resolved swiftly, minimizing disruptions and allowing businesses to concentrate on growth rather than operational difficulties. With expert assistance consistently accessible, organizations can significantly improve productivity and efficiency.
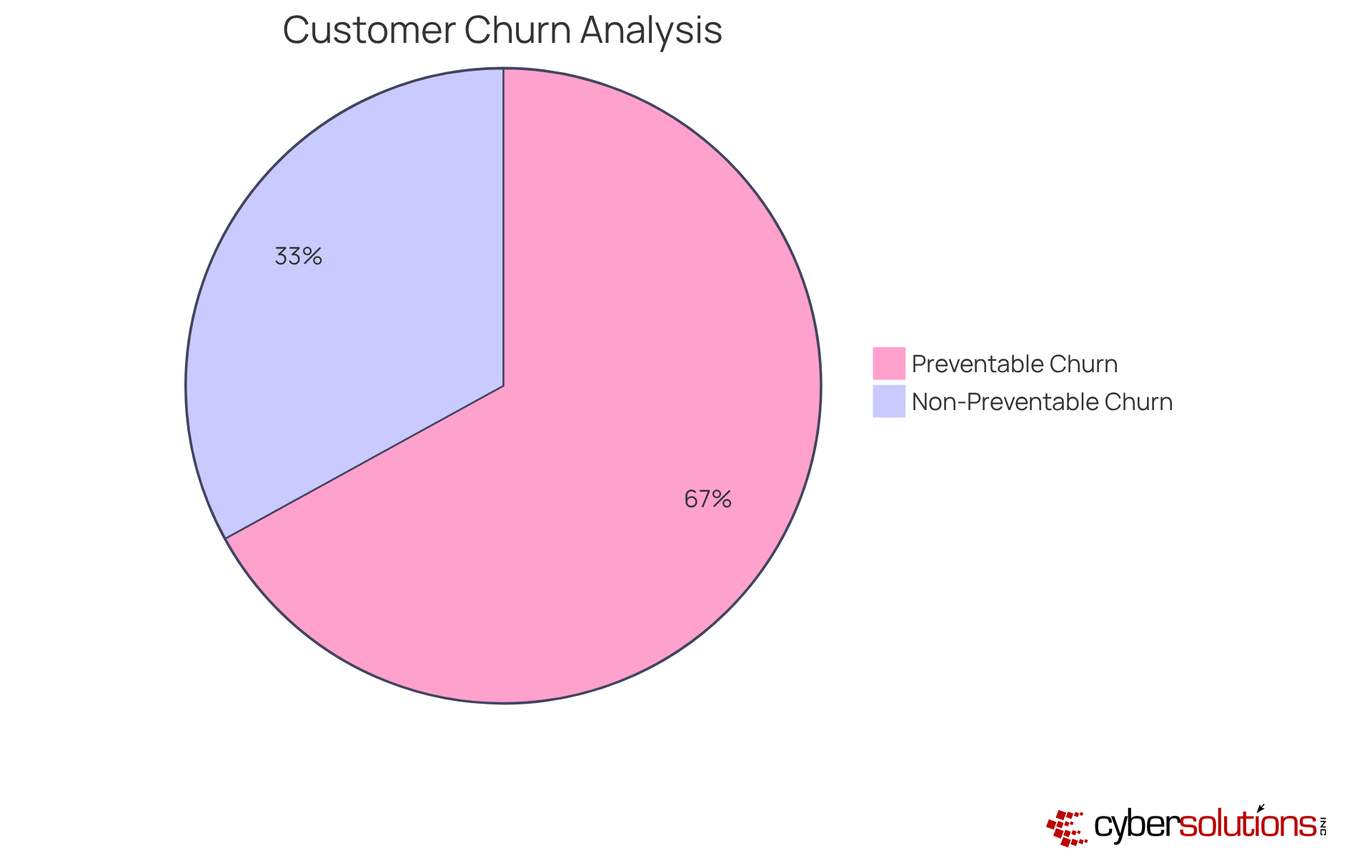
Consider this: companies that adopt managed IT services report a decrease in downtime-related losses, which can average nearly $9,000 per minute for large enterprises. Furthermore, did you know that 67% of customer churn is preventable if issues are resolved during the first contact? This statistic underscores the critical importance of quick resolution in maintaining customer satisfaction.
With a dedicated team on standby, businesses can confidently operate. This not only ensures seamless operations but also fosters sustained growth. By leveraging Cyber Solutions' 24/7 managed IT services, organizations can concentrate on what truly matters—driving innovation and achieving their strategic goals.
In today’s rapidly evolving digital landscape, proactive monitoring is not just an option; it’s a necessity for safeguarding your organization’s IT infrastructure. Cyber Solutions offers continuous assessment of system performance, enabling early detection of anomalies. This proactive approach allows for swift action to mitigate risks, ensuring that your systems remain robust and secure.
C-Suite leaders stand to gain significantly from this solution, as it directly promotes operational efficiency. Organizations that implement continuous system health monitoring report a staggering:
These statistics underscore the effectiveness of proactive strategies in today’s threat landscape.
Moreover, businesses utilizing managed IT services experience:
This translates to increased productivity. By fostering a culture of continuous improvement, organizations can anticipate and address potential issues before they escalate. Isn’t it time to safeguard your operations and maintain customer trust? With Cyber Solutions, you can take the necessary steps to enhance your IT infrastructure and ensure its resilience against cyber threats.
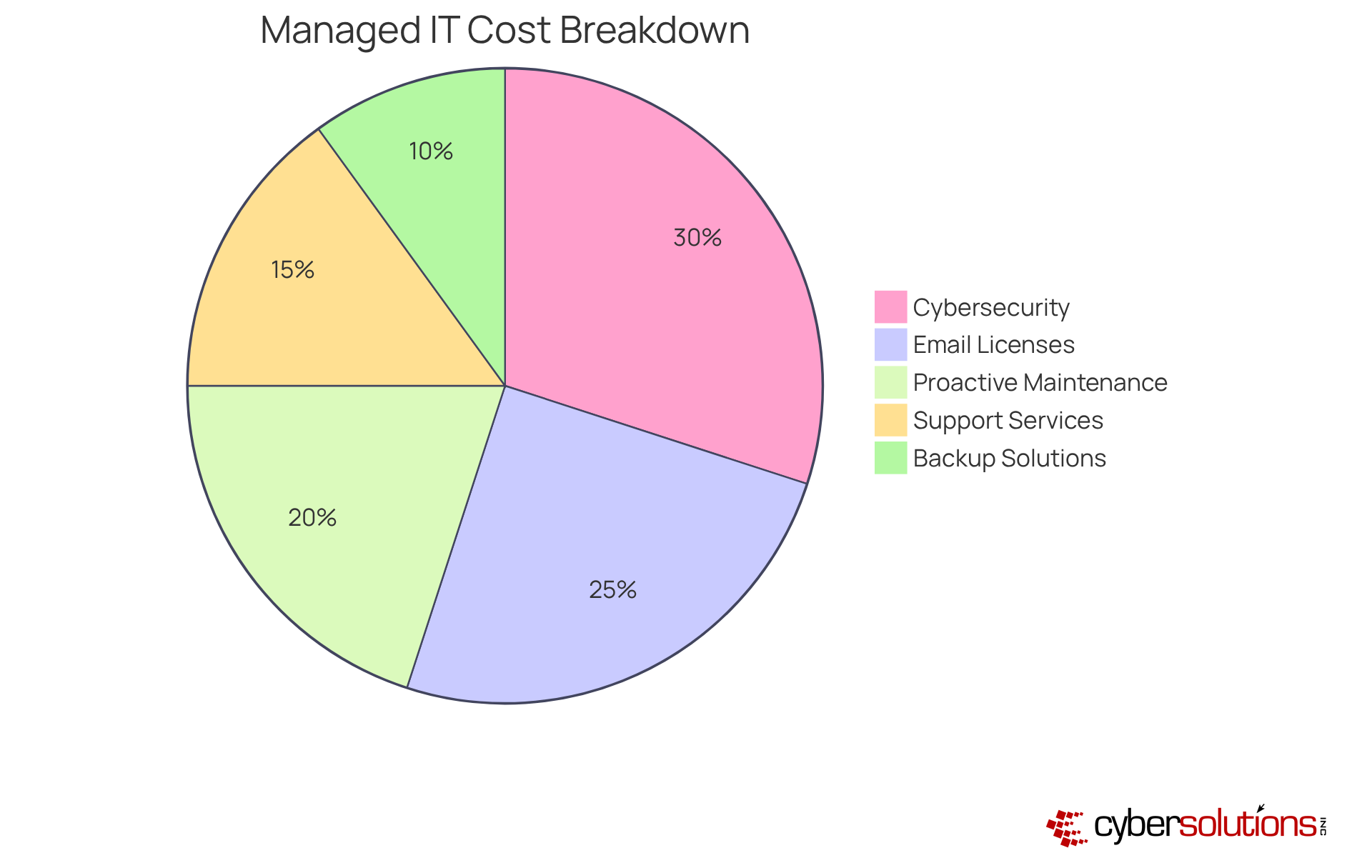
One of the key benefits of using managed IT services is the predictable costs. This flat-rate approach not only simplifies budgeting for IT expenses but also ensures that organizations eliminate unexpected costs and surprises. By knowing their expenses, organizations can allocate resources more efficiently, ensuring wise investments in their technology while upholding high standards of quality and security.
Typically, organizations spend between $100 to $250 per user each month for managed IT services. This comprehensive pricing encompasses everything from email licenses to cybersecurity measures, offering peace of mind in one cohesive package. With such clarity in costs, organizations can plan confidently that their IT needs are being effectively met through managed services.
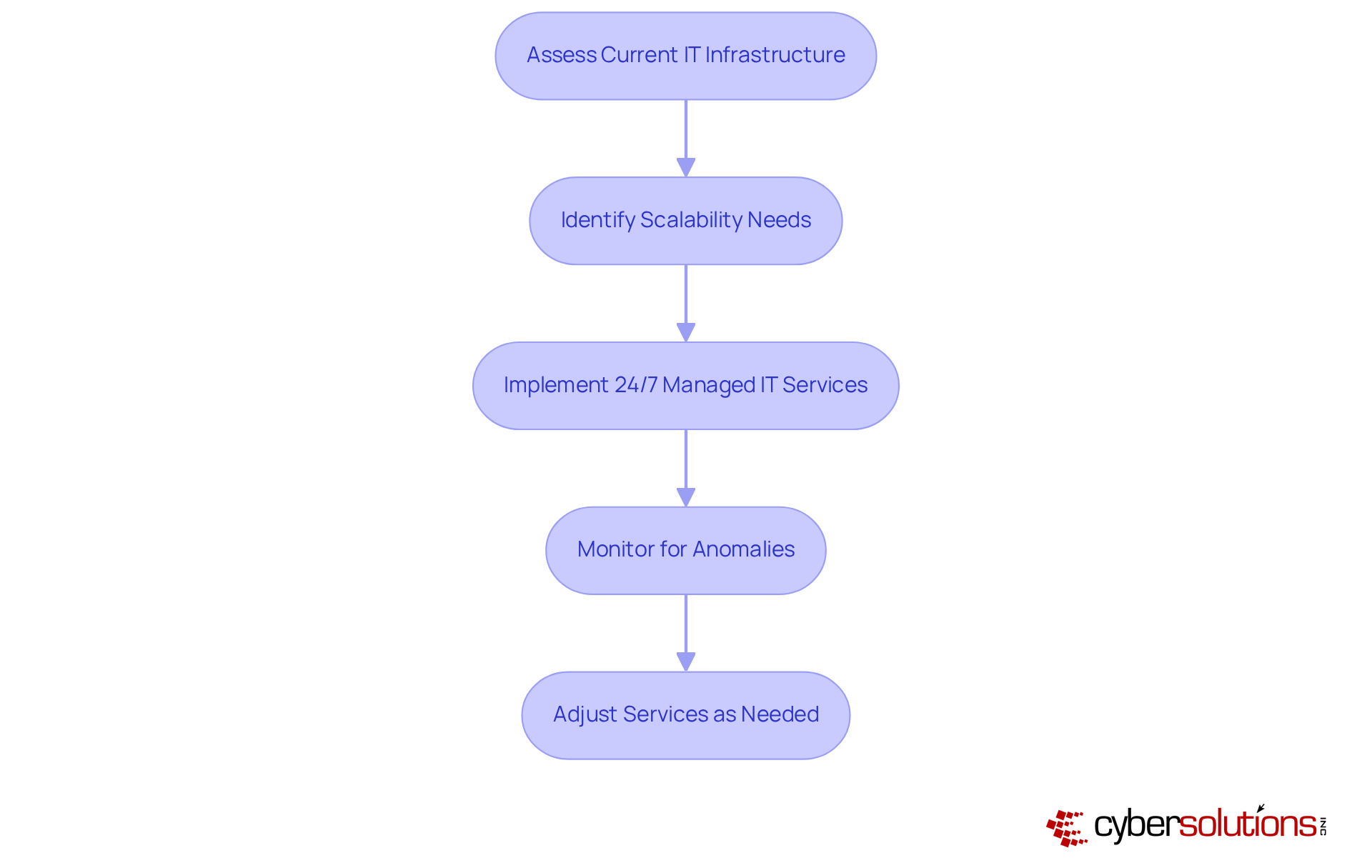
IT services are essential for creating a strategy that evolves alongside your business. As organizations grow, their IT requirements change, and Cyber Solutions ensures that its services can be tailored to meet these dynamic needs. This adaptability allows C-suite leaders to focus on growth, confident that their infrastructure is secure without major overhauls or disruptions.
With proactive monitoring, Cyber Solutions proactively identifies anomalies and potential vulnerabilities through detection and alert systems, enabling swift actions to mitigate risks. Features such as automated backups, patch management, and support not only enhance operational efficiency but also maximize ROI. The USD 449.79 billion market by 2028 underscores the critical role of scalable IT infrastructure in supporting business growth.
Investing in scalable infrastructure is vital for scalability to ensure readiness for future expansion. Are you prepared to meet the challenges of tomorrow? Assessing your IT capabilities today can pave the way for sustained success.
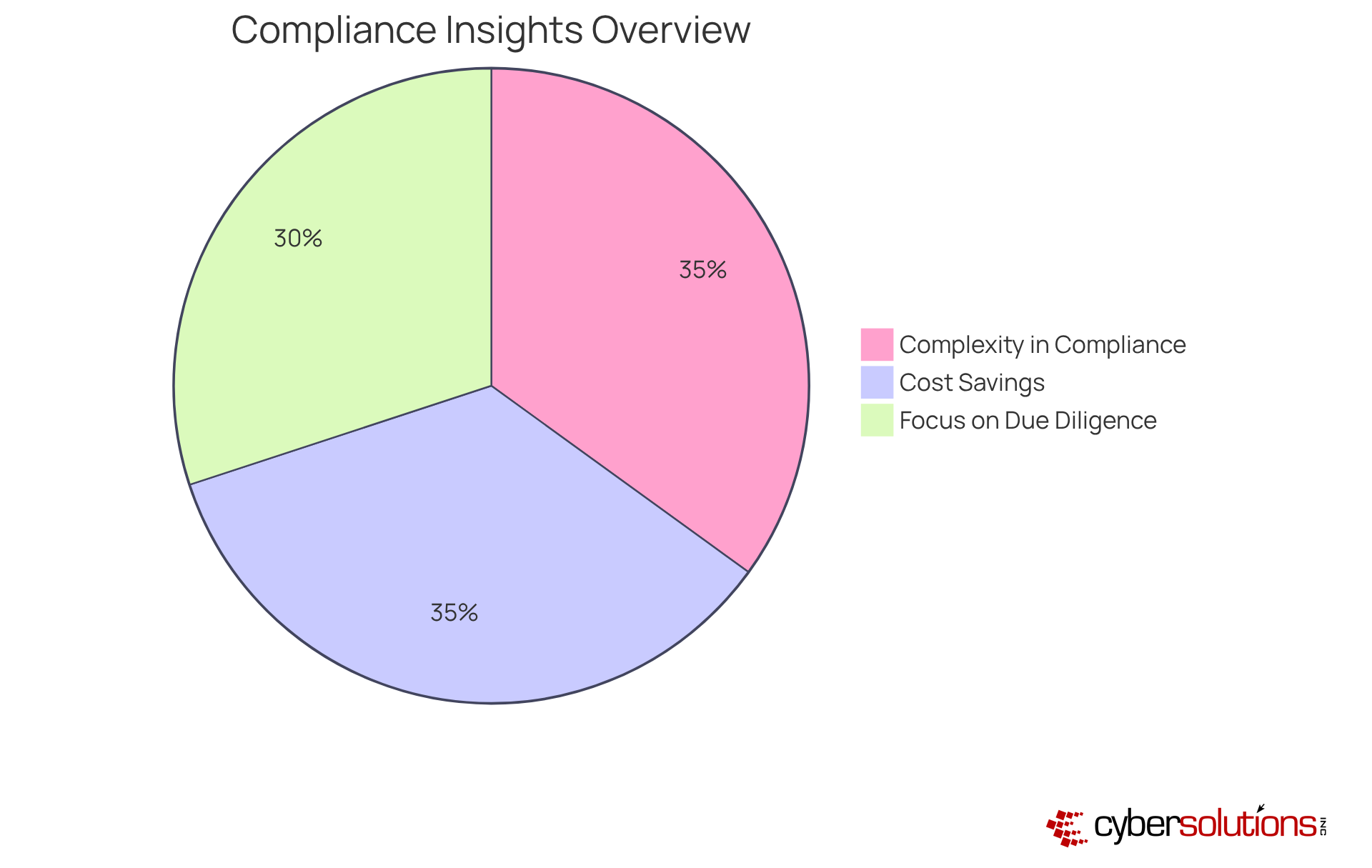
In today’s rapidly evolving regulatory landscape, compliance is not just a necessity; it’s a strategic advantage. Cyber Solutions provides essential compliance assistance that empowers organizations to navigate complex frameworks like HIPAA, compliance regulations, and GDPR with confidence. Our solutions deliver comprehensive support, encompassing assessments, policy development, monitoring, and audit preparation. This ensures that businesses, organizations, and stakeholders bolster their market reputation.
Consider this:
As businesses increasingly depend on third-party partners for compliance-related tasks, maintaining robust oversight is paramount. By leveraging our expertise, organizations can enhance their compliance posture, ensuring they are well-prepared to meet evolving regulatory demands while safeguarding their operations. Are you ready to take action?
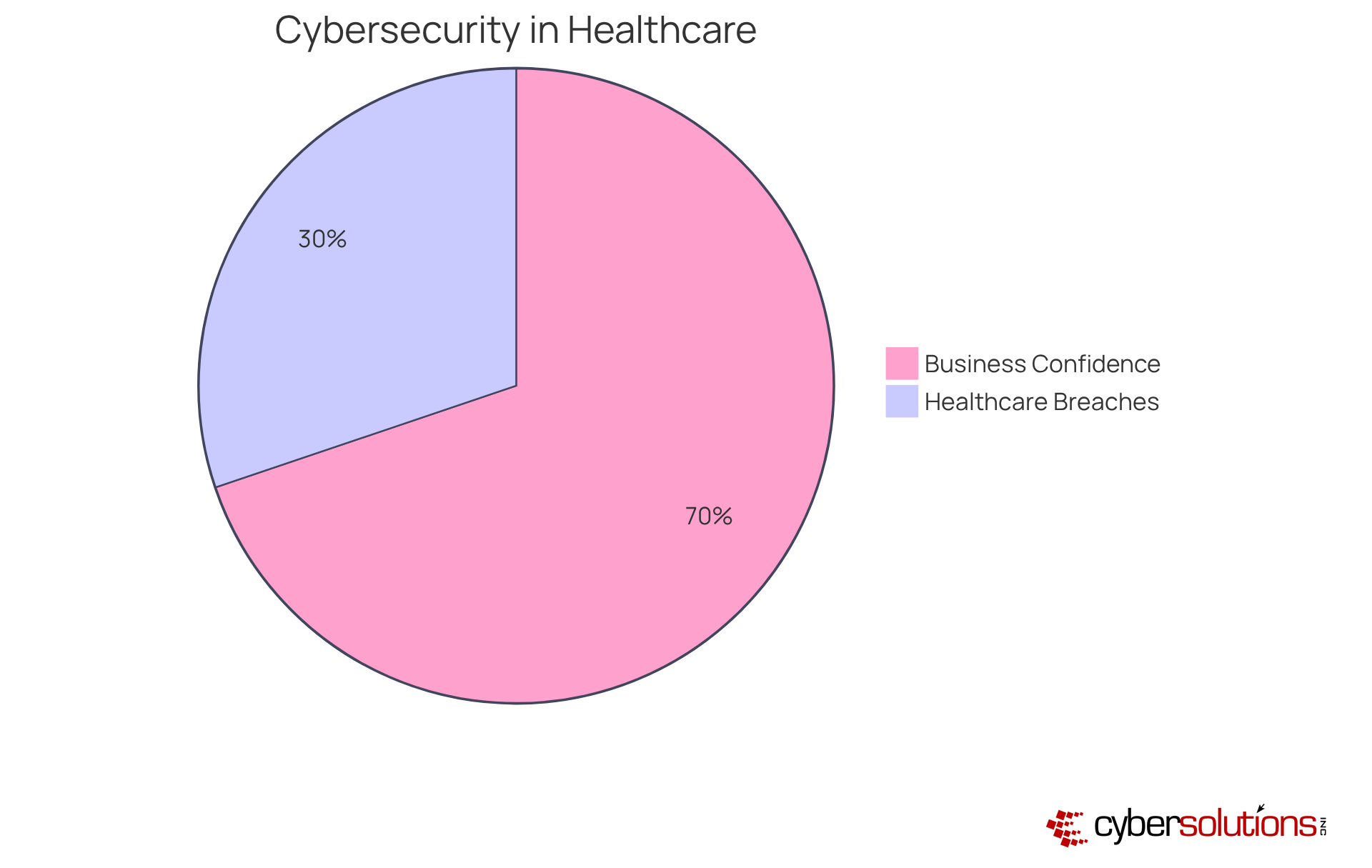
In today's digital age, the importance of cybersecurity cannot be overstated. With the healthcare industry facing a staggering number of breaches between 2015 and 2022, the need for effective cybersecurity solutions has never been more critical. Cyber Solutions employs a robust suite of enhanced cybersecurity measures designed to protect businesses from the ever-evolving landscape of digital threats. These measures include:
All aimed at fortifying sensitive information against potential breaches.
C-suite executives can operate with confidence, knowing their essential systems are safeguarded amid rising cyber risks. Organizations that have implemented cybersecurity strategies report significant reductions in incidents, with many experiencing enhanced operational resilience. But how can CFOs navigate this complex digital environment? Cybersecurity professionals emphasize the importance of proactive measures, revealing that continuous monitoring is essential.
This assurance is vital for leaders who must manage the risks associated with a breach, which has reached an alarming level. By investing in advanced cybersecurity solutions, organizations not only protect their sensitive information but also strengthen their overall security posture. This investment ultimately leads to improved business performance and increased stakeholder confidence. In a world where digital threats are ever-present, can you afford to take chances with your cybersecurity?
Continuous IT management is not just a necessity; it’s a cornerstone of business operations. Leaders can rest assured knowing their IT environment is under constant surveillance and support. The help desk services are crucial for swiftly addressing issues, minimizing disruptions, and preserving productivity. Organizations that implement managed IT services can significantly reduce the risk of downtime, which can cost companies upwards of $300,000 per hour. For instance, a prominent auto finance provider effectively utilized managed IT services to uphold essential systems and guarantee business continuity, showcasing the tangible benefits of proactive IT management.
Executives often express that the peace of mind provided by continuous IT monitoring allows them to focus on strategic initiatives rather than operational concerns. As one executive noted, "A stable and always available system helps you build trust and ensures a consistent user experience." This sentiment resonates across various industries, particularly in sectors like e-commerce, healthcare, and finance, where managed IT services are vital to avoid lost revenue and critical service failures.
Moreover, managed IT services not only address immediate issues but also identify vulnerabilities before they escalate, further enhancing operational stability. With 45% of breaches arising from hacking, the need for cybersecurity has never been greater. Ongoing IT management empowers organizations to navigate the complexities of the digital landscape confidently, ensuring resilience in the face of evolving threats.
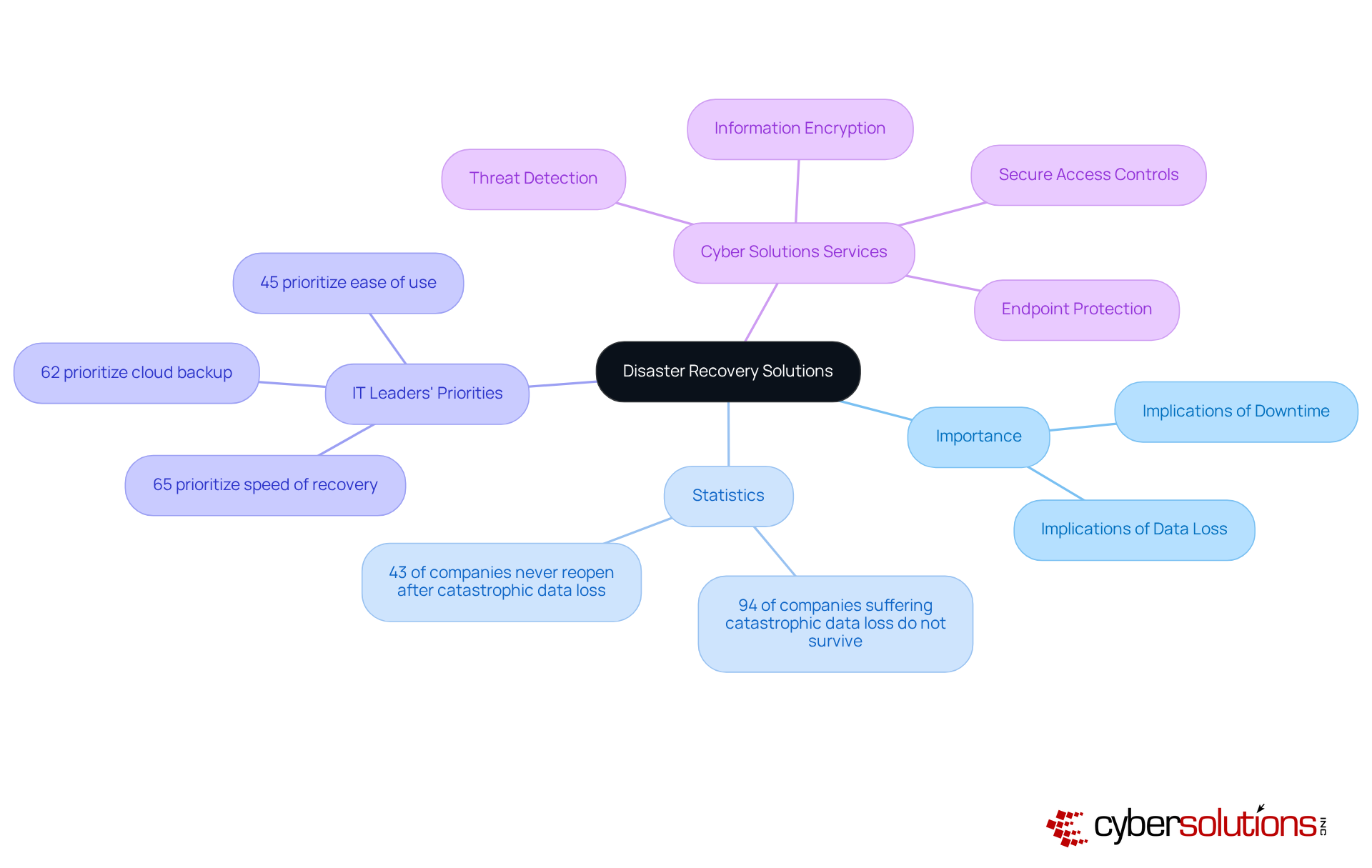
In today’s digital landscape, the importance of robust disaster recovery solutions in healthcare cannot be overstated. Cyber Solutions offers services that significantly reduce downtime and information loss during incidents, ensuring that organizations can swiftly recover from disruptions. This well-organized framework empowers businesses to protect essential information and maintain operational integrity, which is crucial in an industry where the implications of downtime are profound. Did you know that 94% of companies experiencing catastrophic data loss do not survive? Alarmingly, 43% never reopen their doors. This stark reality highlights the need for effective recovery plans.
IT leaders recognize the critical nature of minimizing downtime, with 65% prioritizing speed of recovery when selecting disaster recovery systems. Effective disaster recovery as a service (DRaaS) solutions enable organizations to recover applications quickly, significantly reducing the threat posed by ransomware and other cyber incidents. Take the healthcare sector, for example, where data breaches can have severe consequences. This alarming statistic underscores the pressing need for enhanced disaster recovery and business continuity strategies.
Moreover, organizations that align their recovery objectives with revenue-critical systems can allocate resources more effectively, ensuring preparedness for unexpected disruptions. Cyber Solutions' customized IT services cater to the unique security and compliance needs of sectors such as healthcare, finance, manufacturing, and government. Our offerings include:
As the global market for DRaaS is projected to expand significantly, investing in these solutions is not just a safeguard against loss; it’s a strategic move aimed at bolstering overall business resilience. By prioritizing disaster recovery and cybersecurity, organizations can effectively shield their organizations from the devastating impacts of downtime and data breaches.
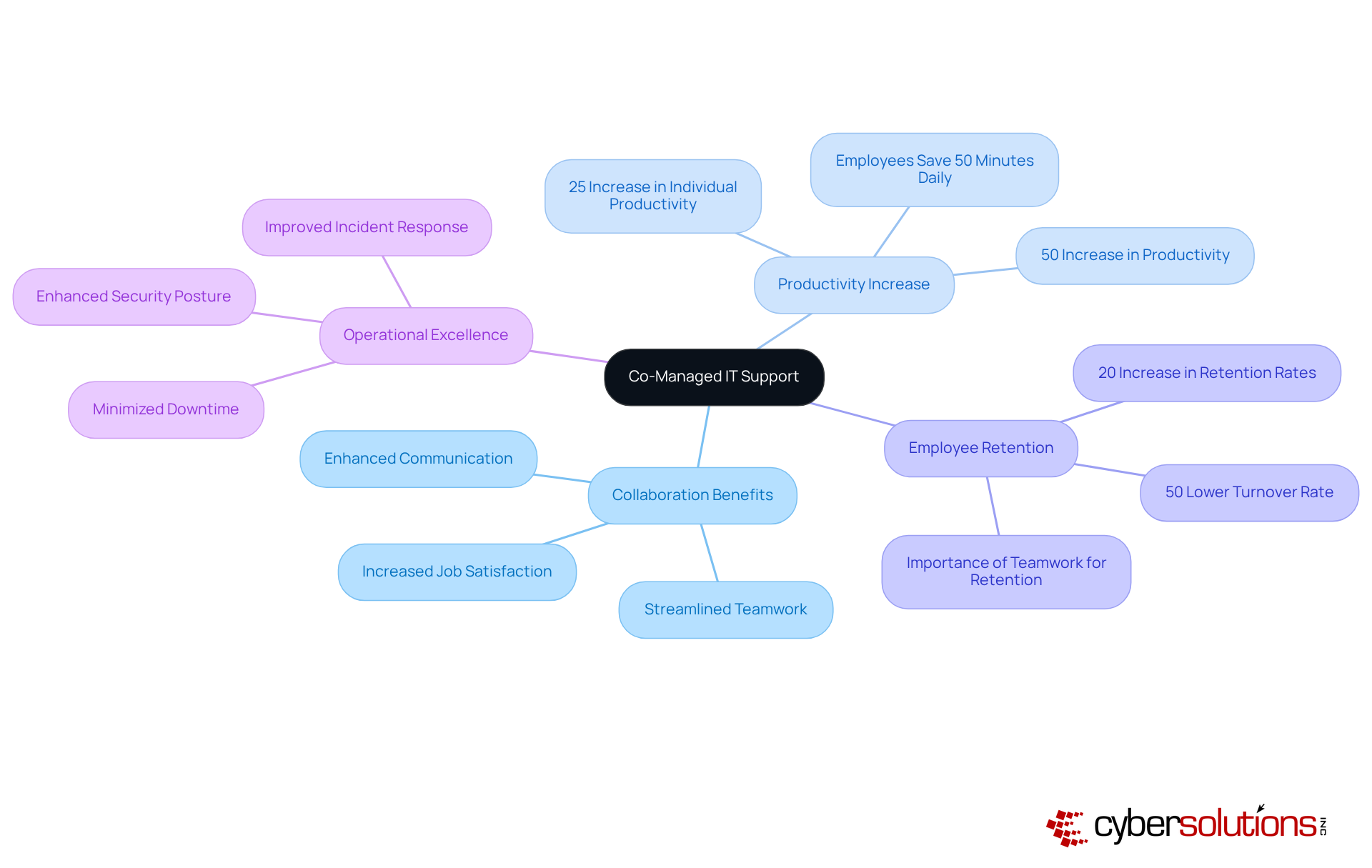
Co-Managed IT Support fosters a collaborative atmosphere between companies and their internal IT teams, significantly enhancing productivity. This empowers organizations to optimize existing resources while leveraging additional expertise and support. By integrating managed services, organizations can ensure that their IT operations run seamlessly and effectively, minimizing downtime and improving response times to incidents.
Consider this: improved efficiency. This boost stems from streamlined communication and teamwork, as highlighted by McKinsey's research, which shows that employees save an average of 50 minutes each day thanks to effective collaboration. Furthermore, entities that prioritize cooperation between internal teams and managed service providers experience a competitive advantage, a finding supported by Deloitte's study on the benefits of fostering collaboration.
As CIOs increasingly recognize the value of external partnerships, they find that collaboration with IT providers not only strengthens security but also drives innovation and operational excellence. However, it’s crucial to acknowledge that poor communication can obstruct collaboration, leading to workplace failures. Cyber Solutions exemplifies this approach by utilizing co-managed services, allowing organizations to focus on strategic initiatives while routine tasks are effectively managed, ultimately resulting in a more resilient IT infrastructure.
In today’s digital landscape, cybersecurity is not just a necessity; it’s a critical component of business operations, especially in healthcare. The implementation of managed IT services plays a pivotal role in optimizing IT processes, across the organization while ensuring security. By automating routine tasks and streamlining workflows, Cyber Solutions empowers C-suite leaders to shift their focus from mundane IT management to strategic initiatives that drive growth.
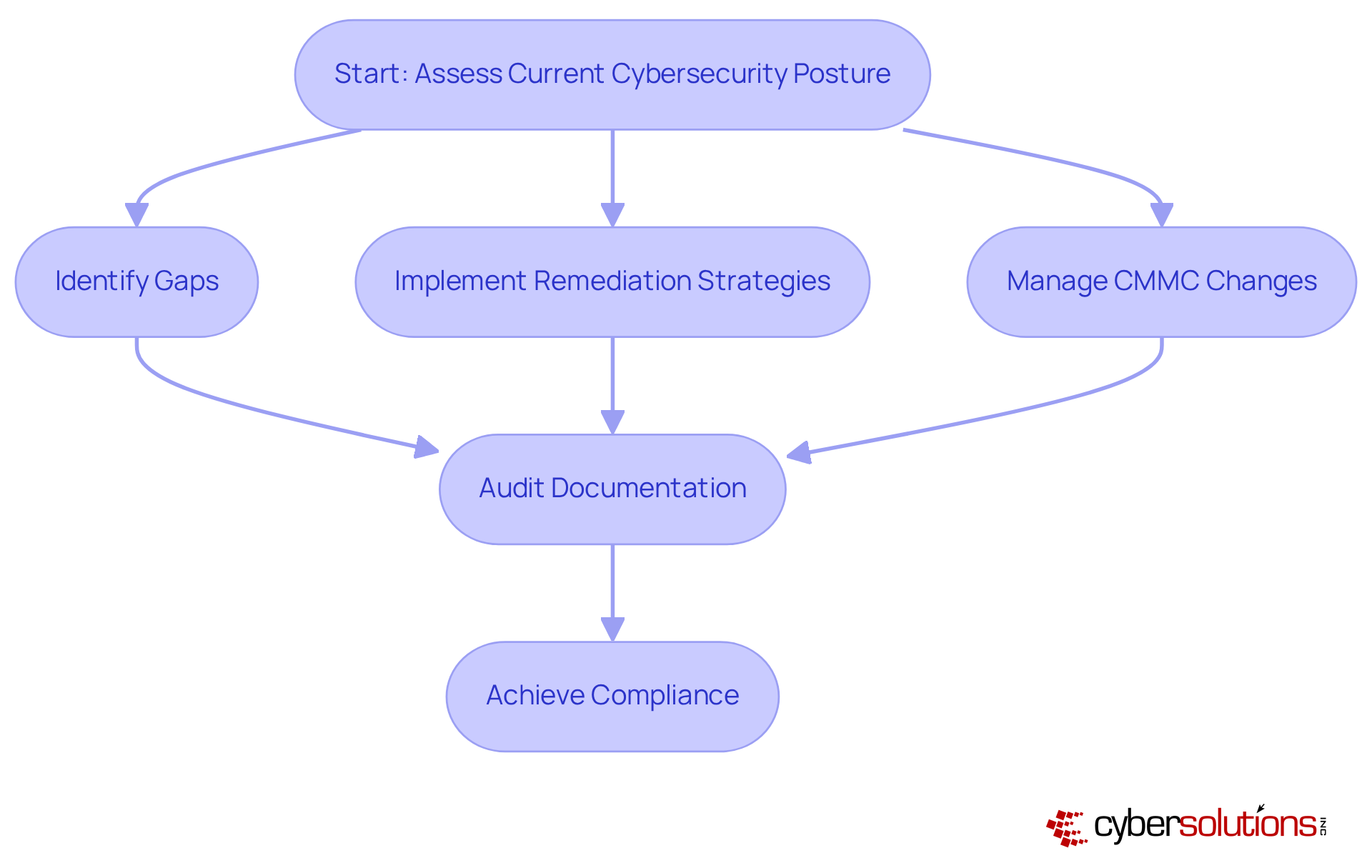
Our proven process for cybersecurity begins with a thorough assessment of your current cybersecurity posture, pinpointing gaps and offering tailored remediation strategies. Continuous management of CMMC changes is vital, ensuring your organization remains compliant with evolving standards. Moreover, we underscore the significance of meticulous documentation during audits, which is crucial for demonstrating compliance effectively.
This approach not only improves efficiency but also enhances security. Organizations leveraging managed IT services gain a competitive edge, enabling them to respond swiftly to incidents with expert guidance and support. Are you ready to elevate your cybersecurity strategy and safeguard your organization’s future?
The importance of 24/7 managed IT services for C-suite leaders is paramount. These services provide a comprehensive solution that not only boosts operational efficiency but also allows executives to concentrate on strategic initiatives instead of wrestling with IT issues. With continuous support and proactive monitoring, organizations can sustain a robust IT infrastructure that evolves with their needs.
Key benefits include:
Each of these elements is vital for safeguarding operations, minimizing downtime, and fostering resilience within organizations. The statistics presented underscore the tangible advantages of implementing 24/7 managed IT services, reinforcing the value of investing in such solutions.
As businesses navigate an increasingly complex digital landscape, the call to action is clear: prioritize the adoption of 24/7 managed IT services to enhance operational integrity and drive innovation. By doing so, organizations not only protect their assets but also position themselves for sustainable growth and success in a competitive environment. Embracing these services is not merely a strategic move; it is an essential step toward ensuring long-term stability and prosperity.
Why is 24/7 managed IT help desk support necessary for businesses today?
24/7 managed IT help desk support is necessary to swiftly resolve IT issues, minimize disruptions, and allow executives to focus on strategic initiatives rather than operational difficulties.
What are the benefits of immediate IT assistance for organizations?
Immediate IT assistance enhances productivity, mitigates costly downtime, and helps maintain customer satisfaction and loyalty, as 67% of customer churn is preventable if issues are resolved during the first contact.
How does proactive monitoring contribute to system health and security?
Proactive monitoring enables continuous assessment of system performance and security, allowing for early detection of anomalies and swift action to mitigate risks, ensuring robust and secure systems.
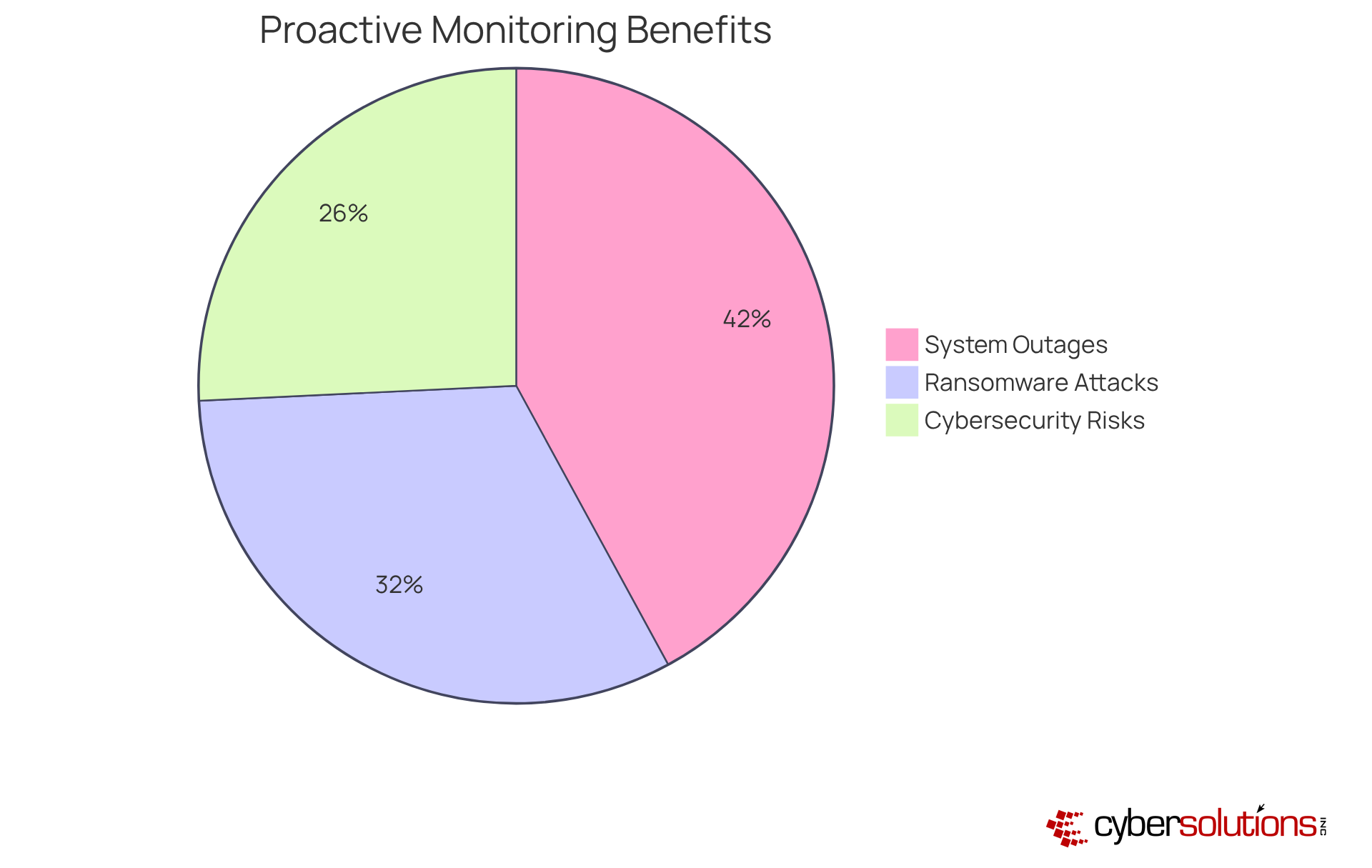
What statistics highlight the effectiveness of proactive monitoring?
Organizations that implement proactive monitoring report a 60% decrease in cybersecurity risks, a 75% reduction in ransomware attacks, and 98% fewer system outages.
How does 24/7 managed IT services help with budgeting for organizations?
24/7 managed IT services offer a predictable monthly pricing model, simplifying budgeting and eliminating unexpected IT expenses, which allows organizations to allocate resources more efficiently.
What is the typical cost range for managed IT support for small to medium-sized enterprises?
Small to medium-sized enterprises typically spend between $100 to $250 per user each month for managed IT support, which includes services like email licenses and advanced cybersecurity.