
The digital landscape is fraught with ever-evolving threats that pose significant risks to small businesses. As cyberattacks become increasingly sophisticated, the importance of robust cybersecurity measures—including small business cyber insurance—cannot be overstated. This article delves into ten compelling reasons why cyber insurance is not just a safety net but an essential component of a small enterprise's risk management strategy.
How can small businesses effectively safeguard their operations and financial stability in the face of mounting cyber threats? The answers lie in understanding the critical role that tailored insurance coverage plays in enhancing resilience and protecting against potentially devastating losses.
Cyber Solutions Inc. offers a comprehensive suite of customized cybersecurity services tailored specifically for small enterprises. This includes risk assessments, threat detection, and incident response planning. These offerings empower companies to operate securely while simplifying IT management complexities. As we approach 2025, the evolution of cyber threats underscores the critical need for proactive cybersecurity measures. With increasing digital transformation, the demand for robust protection is undeniable.
Cyber insurance, such as data breach coverage, is an essential element of a small enterprise's risk management strategy. It delivers financial protection against the potentially devastating costs associated with data breaches, which can average $120,000 per incident. Experts emphasize that cyber insurance is essential, as without it, small enterprises are vulnerable to significant financial losses, with nearly 20% of those affected by a breach facing bankruptcy.
Successful implementations of managed IT and cybersecurity services demonstrate that small enterprises can markedly enhance their security posture. Organizations utilizing these services report fewer incidents and improved compliance with regulatory standards. Cybersecurity solutions not only address the specific challenges faced by small enterprises but also ensure they are prepared for the future, including AI-driven attacks and insider risks. By partnering with Cyber Solutions Inc., small enterprises can fortify their defenses and protect their operations against the ever-evolving landscape of cyber threats.

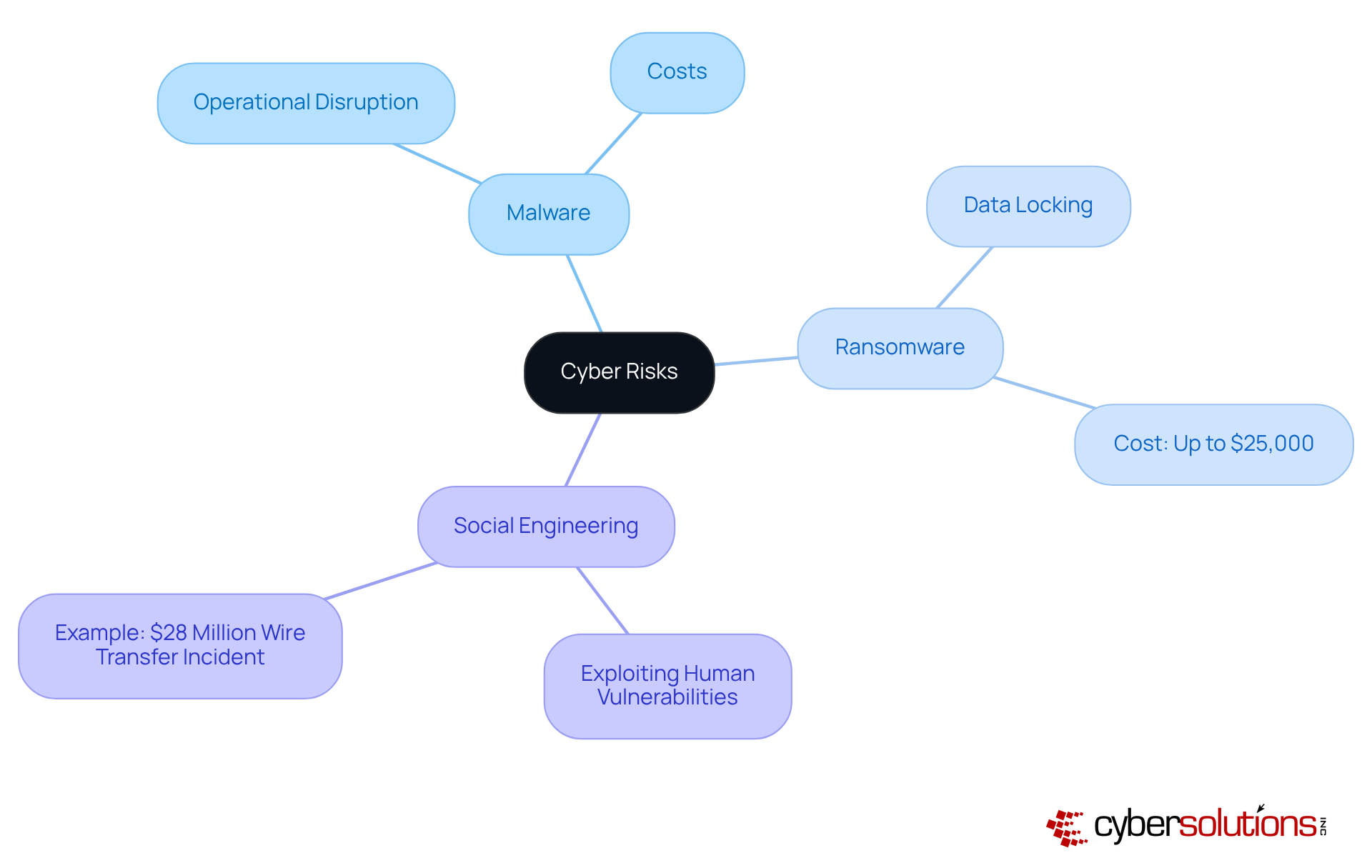
Small enterprises are increasingly becoming prime targets for cyber attacks involving malware, ransomware, and social engineering. Malware can severely disrupt operations, while ransomware can lock critical data, rendering it inaccessible until a ransom is paid. In fact, the typical cost of a ransomware incident on a small enterprise can reach up to $25,000, with significant financial implications.
Furthermore, social engineering attacks exploit human vulnerabilities, leading to unauthorized access to sensitive information. A notable example includes a recent incident where an employee in Hong Kong was deceived into approving a $28 million wire transfer through a fabricated video conference, showcasing the alarming sophistication of these tactics. Approximately 60% of small enterprises consider threats like phishing and ransomware as critical, emphasizing the necessity of cybersecurity measures to address these dangers.
As cyber threats evolve, understanding these risks is vital for small enterprises, highlighting the crucial role of cyber insurance as a safeguard against potential financial losses. To bolster defenses, implementing security measures such as firewalls is essential. This approach not only prevents unauthorized software from executing but also minimizes vulnerabilities, making it harder for attackers to exploit systems. Ongoing surveillance of application activity ensures prompt detection and prevention of threats, further safeguarding operational activities.
Cybersecurity professionals stress that alongside employee training and awareness programs, cyber insurance is a key strategy in mitigating risks and enhancing overall security posture.
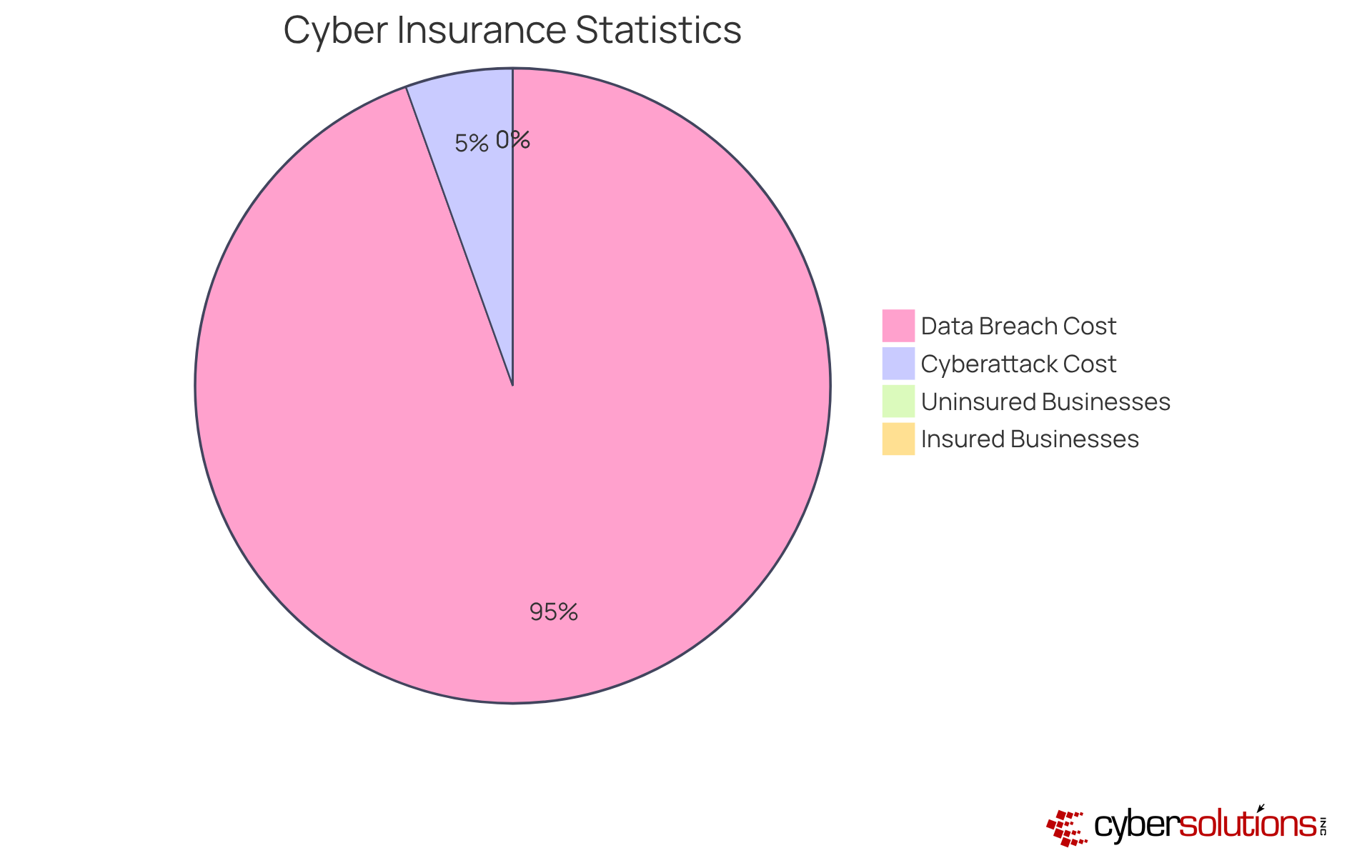
In today's digital landscape, cyber insurance is not merely an option for minor enterprises; it is a critical necessity. Cyber insurance serves as a vital resource, addressing the substantial costs associated with data breaches, including legal fees, notification expenses, and system recovery. With the average cost of a data breach projected to soar to $4.4 million by 2025, the financial impact can be staggering. Furthermore, the average total cost of a cyberattack on a small to medium-sized business (SMB) stands at $254,445, which emphasizes the necessity of cyber insurance to alleviate the financial strain that can jeopardize their very existence. By covering these expenses, cyber insurance empowers minor enterprises to recover swiftly from breaches, alleviating the risk of crippling financial burdens that threaten their operations.
Consider this: numerous minor enterprises have successfully navigated the aftermath of digital incidents with the support of cyber insurance. A striking case is that of a small healthcare provider that endured a ransomware attack, leading to significant operational disruptions. Thanks to their cyber insurance, they were able to finance legal consultations and system recovery, allowing them to resume normal operations without incurring crippling debt. It's imperative to note that 75% of SMBs indicate they could not sustain operations if faced with ransomware, underscoring the essential nature of having cyber insurance.
Financial analysts emphasize that investing in cyber insurance not only mitigates immediate recovery costs but also enhances long-term resilience. As 80% of minor enterprise leaders express intentions to increase their digital security budgets, incorporating cyber insurance into their risk management strategies is becoming increasingly crucial. Currently, a mere 17% of small enterprises have cyber insurance in place, revealing a significant gap in their preparedness. This proactive approach not only safeguards against financial losses but also bolsters customer confidence; indeed, 55% of consumers are less likely to engage with businesses that have experienced a data breach. Thus, cyber insurance transcends being a mere safety measure; it represents a strategic investment in the future stability and reputation of minor enterprises.
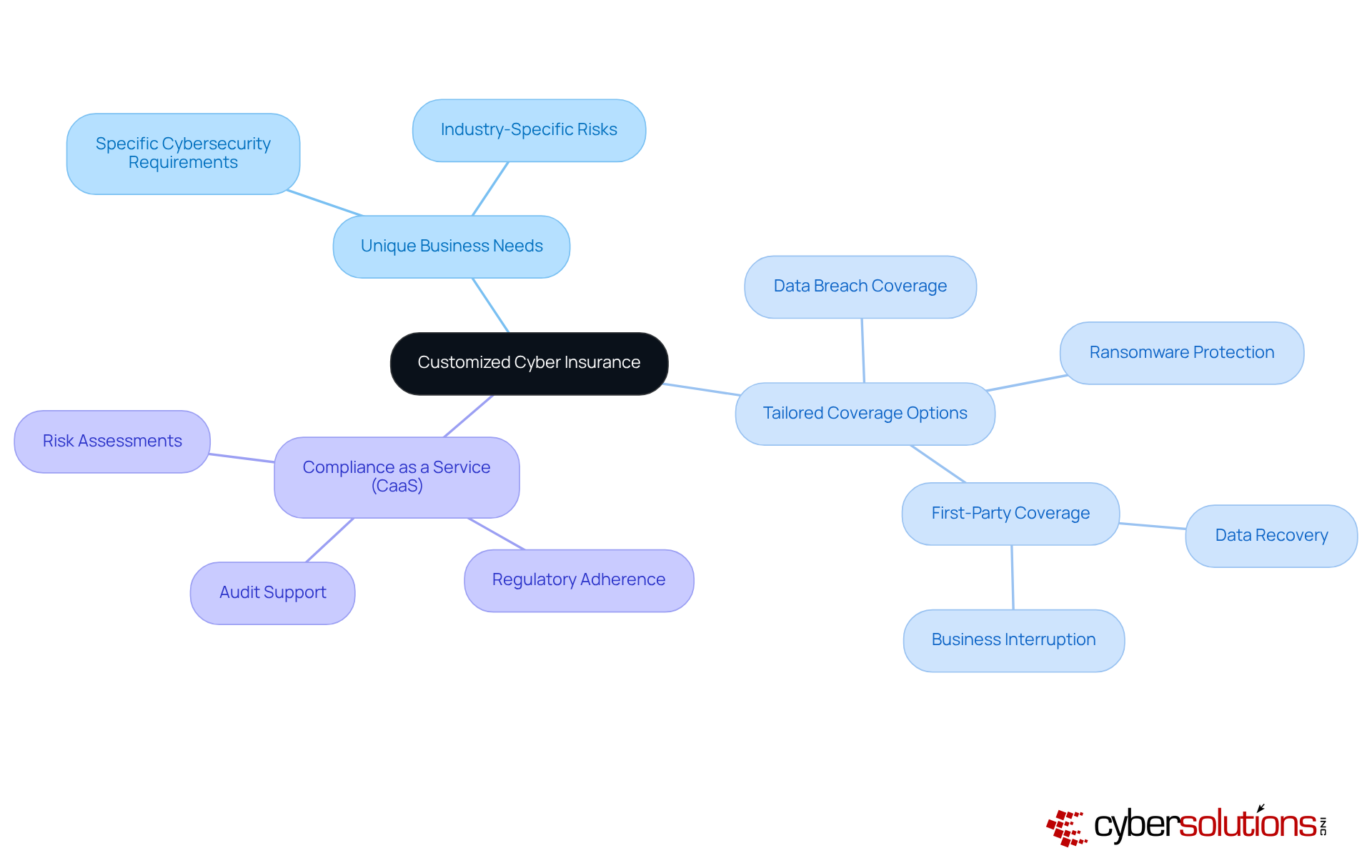
Every small enterprise possesses unique needs, and it is imperative that coverage reflects this reality. Tailoring coverage options, such as those that include liability or data breach protection, ensures that organizations are effectively shielded from the risks they face. Engaging with a knowledgeable provider can illuminate the most pertinent coverage options available.
Furthermore, integrating compliance solutions into your strategy can significantly enhance your coverage by ensuring that your organization adheres to legal standards. CaaS provides comprehensive solutions, including assessments and audit support, which are vital for SMBs operating in regulated environments.
By aligning your business operations with robust compliance solutions, you not only protect your assets but also strategically position your enterprise for growth and resilience amid evolving threats.
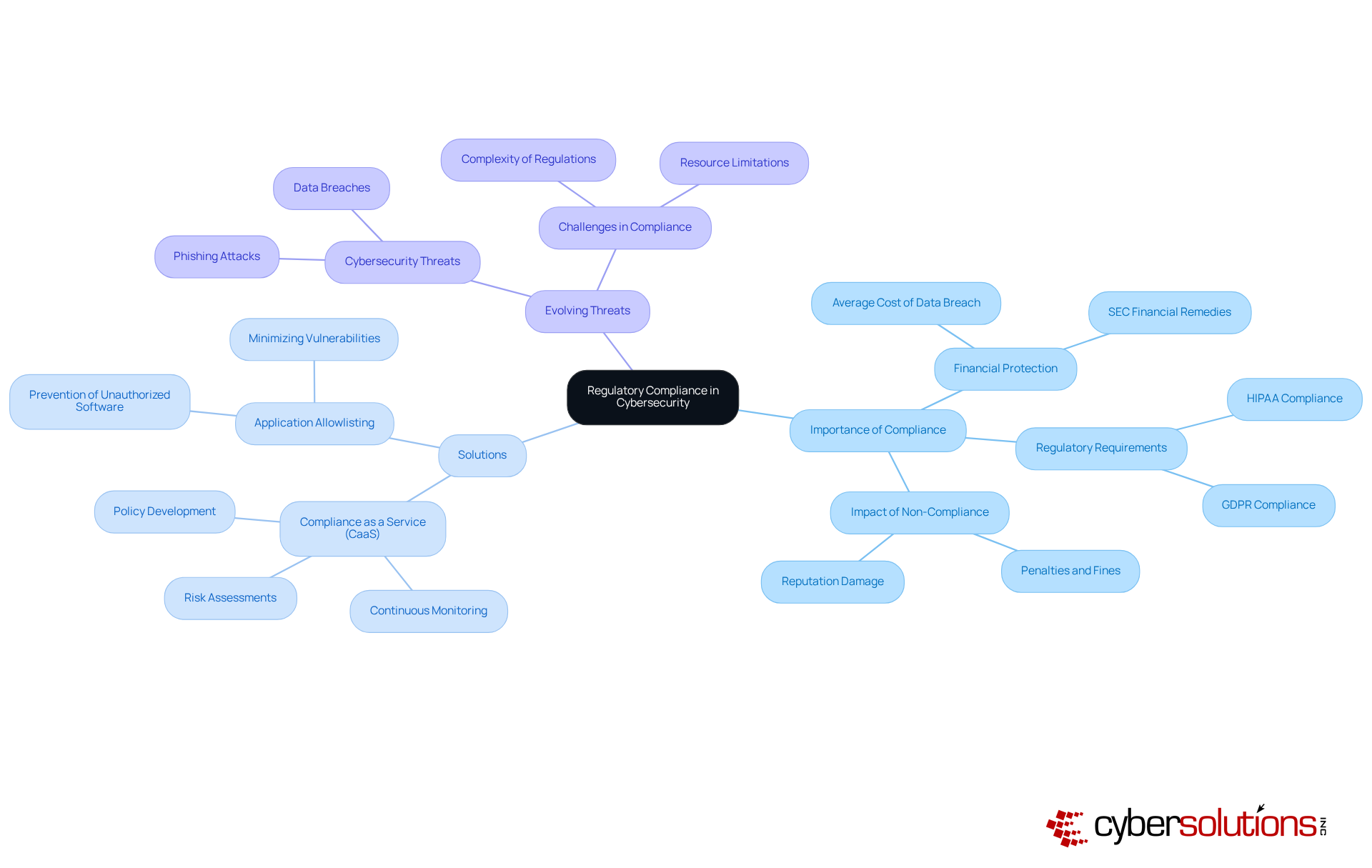
In today's digital landscape, cybersecurity measures are more critical than ever, particularly in industries like healthcare, where compliance with standards such as HIPAA is non-negotiable. For organizations navigating these stringent requirements, cyber insurance serves as an essential resource, safeguarding them against potential penalties and bolstering their compliance posture. By embedding cybersecurity solutions, businesses can leverage protection not merely as a safety net but as a proactive approach to maintaining regulatory adherence.
To streamline compliance efforts, integrating solutions like Compliance as a Service (CaaS) and application allowlisting is pivotal. CaaS provides continuous monitoring, comprehensive risk assessments, and expert guidance, ensuring that organizations remain vigilant in their compliance journey. Meanwhile, application allowlisting acts as a frontline defense, preventing unauthorized software from executing, thus minimizing vulnerabilities and ensuring adherence to rigorous data protection protocols.
As cybersecurity threats evolve, the imperative for healthcare organizations to maintain compliance becomes increasingly clear. The integration of these solutions not only addresses compliance challenges but also fortifies the overall security posture, enabling organizations to thrive in a complex regulatory environment.
In today's digital landscape, cyber insurance is not merely an option; it is a necessity for healthcare organizations. Cyber coverage offers benefits that extend far beyond simple financial protection. It provides access to incident response services, which are crucial for effectively managing the aftermath of a breach. This support not only facilitates swift recovery but also plays a vital role in public relations initiatives, assisting organizations in communicating after an incident. Maintaining trust with clients and stakeholders is essential for reputation management, and digital protection serves as a critical resource in this context.
Consider the recent case study of a healthcare provider, which underscores the importance of preparedness when confronting ransomware attacks. Having an incident response team on-site within a day can significantly contain threats and mitigate damage. Furthermore, adopting a layered approach—including endpoint isolation, malware removal, and user training—enables a faster and more comprehensive recovery. It is also important to recognize that 27% of organizations experienced exclusions that resulted in non-payout or partial payouts, highlighting the necessity of selecting the right coverage.
With only 10% of SMEs having embraced cyber insurance, a considerable gap in protection remains that small enterprises must address. C-suite executives should routinely assess their policies to ensure alignment with evolving security requirements. Are you prepared to safeguard your organization against the ever-growing threats in the digital realm?

In today's digital landscape, the significance of possessing cyber insurance cannot be overstated. In the aftermath of a digital attack, having access to critical resources—including forensic analysis, legal assistance, and public relations strategies—is crucial for effectively managing the fallout. A quick and efficient response is vital for minimizing damage and restoring operations. Companies with cyber insurance typically experience a notably reduced recovery duration, averaging approximately 20% shorter than those lacking coverage, as highlighted in various studies on the benefits of insurance. This rapid recovery is essential; experts like Timothy Shields emphasize that timely support can prevent long-term financial and reputational harm.
Moreover, small enterprises that have successfully navigated digital incidents often credit their insurance coverage for granting access to essential services, enabling effective recovery. For instance, numerous case studies demonstrate that organizations utilizing cyber insurance effectively regained financial losses and mitigated reputational damage. It is also imperative for companies to routinely revise their online protection plans to align with the evolving digital environment.
Overall, the assistance provided through cyber insurance is an invaluable asset in the face of online threats, encompassing first-party costs such as incident response and third-party claims like regulatory fines. As the digital landscape continues to shift, cyber insurance will be essential for safeguarding organizational integrity and resilience.
Choosing the right digital coverage supplier is crucial for small businesses, and several key factors should guide this decision. The insurer's reputation is paramount; businesses must seek insurers known for their reliability and customer satisfaction, as these elements significantly influence the quality of service during claims processing. In 2025, a substantial number of businesses reported dissatisfaction with their digital coverage providers, underscoring the need for thorough research before committing to a policy.
Coverage comprehensiveness is another vital consideration. Businesses should evaluate whether the available coverage options adequately address their specific risks, such as data breaches, ransomware attacks, and operational disruptions. For example, policies that encompass both first-party losses and third-party liabilities offer a more robust safety net.
The level of support provided by the insurer is equally important. Businesses should prioritize insurers that offer access to pre-breach and post-breach response services, which can be invaluable during a crisis. Professional assistance is essential for recovery, ensuring organizations can recover swiftly and effectively. Cyber Solutions exemplifies this approach by offering cybersecurity services, including threat detection and email security, which not only complement insurance coverage but also proactively mitigate risks associated with cyber threats.
Industry experts emphasize that businesses should select providers that understand their unique challenges. Robert Fitzgerald, CEO of Arcas Risk Management, advises, "Look for a provider that understands the SMB space," as this can result in more tailored solutions aligned with the specific risk profiles of smaller enterprises. Cyber Solutions demonstrates this understanding by providing customized managed IT and cybersecurity services specifically designed for medium enterprises, including compliance support to ensure adherence to industry standards.
Moreover, instances of businesses evaluating their coverage reveal that those who conducted thorough assessments of their needs and sought guidance from knowledgeable agents reported higher satisfaction with their coverage. This proactive approach not only enhances protection but also fosters a deeper understanding of the coverage landscape.
In summary, when selecting an insurance provider for digital security, small businesses should prioritize reputation, coverage options, and the level of support offered in relation to their specific needs. By doing so, they can ensure they are well-equipped to navigate the evolving landscape of digital threats, backed by comprehensive security solutions from providers like Cyber Solutions.

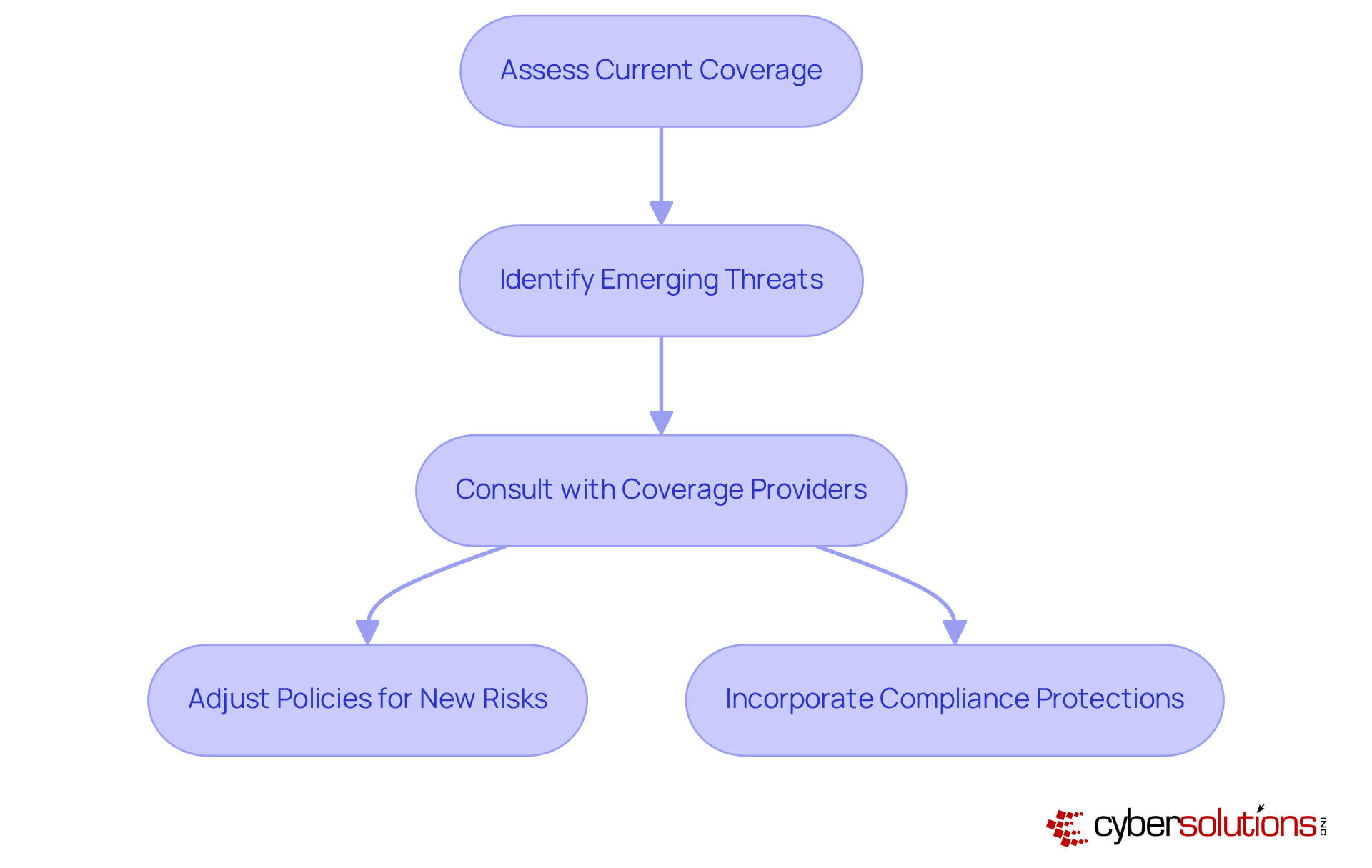
The digital threat landscape is in a state of constant flux, with new and sophisticated dangers emerging regularly. Small enterprises must stay alert and proactive in adjusting their policies to address these changing risks. Regular assessments of coverage are crucial, as they enable organizations to align their policies with the latest threats, such as AI-driven attacks and ransomware incidents, which have surged by 46% in recent years. Working together with cybersecurity experts can assist in guaranteeing that companies are sufficiently safeguarded against these risks.
In 2025, trends suggest that minor enterprises will increasingly require measures to protect against cyber threats, such as data breaches and the misuse of IoT devices. Analysts emphasize that it is crucial to include provisions for these new risks in insurance policies for maintaining resilience. For example, numerous minor enterprises are currently pursuing policies that address not only direct financial losses but also the expenses related to recovery efforts.
As the regulatory environment grows increasingly intricate, lesser enterprises must also take into account compliance requirements in their coverage plans. This includes comprehending their own vulnerabilities, as one in four SMBs currently lacks this knowledge, leading to potential blind spots in their preparedness. By adopting a proactive approach and frequently revising their online protection policies, minor enterprises can more effectively manage the obstacles presented by a progressively aggressive digital landscape.
Cyber insurance, such as coverage options, serves as a strategic resource that significantly enhances the resilience of minor enterprises. By safeguarding against financial losses, ensuring compliance with regulatory requirements, and providing access to expert resources, it empowers organizations to confidently navigate the complexities of the digital landscape.
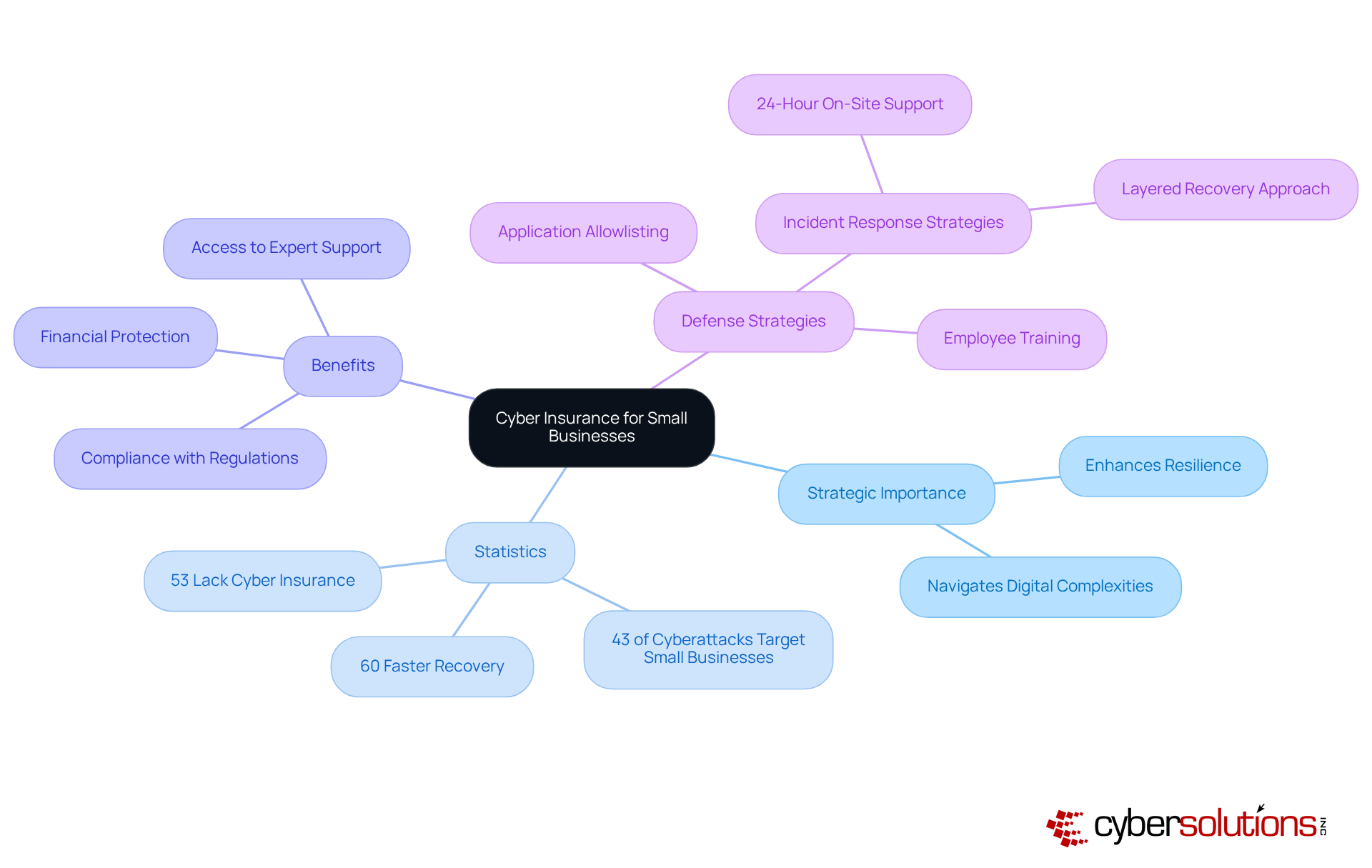
In 2025, statistics reveal that enterprises with cyber insurance experience a 60% faster recovery from cyber incidents compared to those without coverage. This swift recovery is often reinforced by effective incident response strategies, including:
Furthermore, with 43% of cyberattacks targeting minor enterprises and the average cost of a data breach reaching $2.98 million, the need for cyber insurance is clear.
Application allowlisting plays a critical role in this defense by proactively preventing malware and unauthorized software from executing, thereby reducing vulnerabilities and ensuring system integrity. This proactive investment transcends a mere safety net; it is an essential step toward securing the future of any small enterprise through comprehensive risk management.
As Paolo Dal Cin aptly states, having a comprehensive digital liability policy tailored to specific business needs provides the financial security necessary to concentrate on core operations. Additionally, with 53% of small businesses lacking cyber insurance, those that do invest in it demonstrate a commitment to security, potentially increasing stakeholder trust and enhancing overall reputation.
Cyber insurance has become an essential asset for small businesses navigating the complexities of today’s digital landscape. As cyber threats evolve and grow increasingly sophisticated, the need for robust protection cannot be overstated. Small business cyber insurance not only provides financial security against potential breaches but also enhances overall resilience, enabling organizations to recover swiftly from incidents while maintaining compliance with regulatory standards.
Critical insights reveal the pervasive risks that small enterprises face, including:
The staggering costs associated with data breaches further underscore the importance of cyber insurance as a strategic investment. With statistics indicating that a significant portion of small businesses remain uninsured, the urgency for tailored coverage becomes clear. Customized insurance solutions, combined with proactive measures like application allowlisting and incident response support, empower businesses to effectively mitigate risks and safeguard their operations.
In light of the evolving threat landscape and the increasing reliance on digital solutions, small enterprises must prioritize their cybersecurity strategies. Investing in cyber insurance is not merely about protection; it is a commitment to resilience, trust, and long-term success. By taking proactive steps to secure coverage that aligns with their unique needs, small businesses can confidently navigate the challenges of the digital age, ensuring they are well-prepared for whatever threats may arise.
What services does Cyber Solutions Inc. offer for small businesses?
Cyber Solutions Inc. offers a comprehensive suite of tailored cybersecurity services, including 24/7 help desk support, endpoint protection, and managed security services, designed to help small businesses operate securely and simplify IT management.
Why is small business cyber insurance important?
Small business cyber insurance is crucial as it provides financial protection against the high costs associated with data breaches, which can average $120,000 per incident. Without it, small enterprises face significant financial risks, with nearly 20% of those affected by a cyberattack potentially facing bankruptcy.
How do managed IT and cybersecurity services benefit small enterprises?
Managed IT and cybersecurity services can significantly enhance the security posture of small enterprises, leading to fewer incidents and improved compliance with regulatory standards. These services help businesses prepare for advanced threats, including AI-driven attacks and insider risks.
What are common cyber threats faced by small businesses?
Small businesses face various cyber threats, including malware, ransomware, and social engineering attacks. Ransomware incidents can cost up to $25,000, while significant data breaches can average around $4.88 million in losses.
What proactive measures can small businesses take to mitigate cyber risks?
Small businesses can implement proactive measures such as application allowlisting, which prevents unauthorized software from executing and minimizes vulnerabilities. Ongoing surveillance of application activity is also essential for prompt threat detection and prevention.
What financial implications do data breaches have for small businesses?
The average cost of a data breach is projected to reach $4.4 million by 2025, with the total cost of a cyberattack on a small to medium-sized business averaging $254,445. These significant financial burdens highlight the necessity of small business cyber insurance.
How does small business cyber insurance support recovery from cyber incidents?
Small business cyber insurance helps cover the costs associated with data breaches, such as legal fees and regulatory fines, allowing businesses to recover quickly without incurring crippling debt. This support is vital for sustaining operations post-incident.
What percentage of small businesses currently have cyber insurance?
Only 17% of small enterprises currently have small business cyber insurance in place, indicating a significant gap in preparedness against cyber threats.
How does having cyber insurance impact consumer confidence?
Having cyber insurance can bolster customer confidence, as 55% of consumers are less likely to engage with businesses that have experienced a data breach. This makes cyber insurance a strategic investment in a business's stability and reputation.