
In an age where digital transformation is paramount, the role of customizable business software has emerged as a game-changer for organizations striving for efficiency and adaptability. This article delves into ten key features that executives should consider when selecting such software, highlighting benefits that extend beyond mere functionality.
However, with the rapid evolution of technology and increasing cybersecurity threats, how can businesses ensure they are making informed choices that align with their strategic goals?
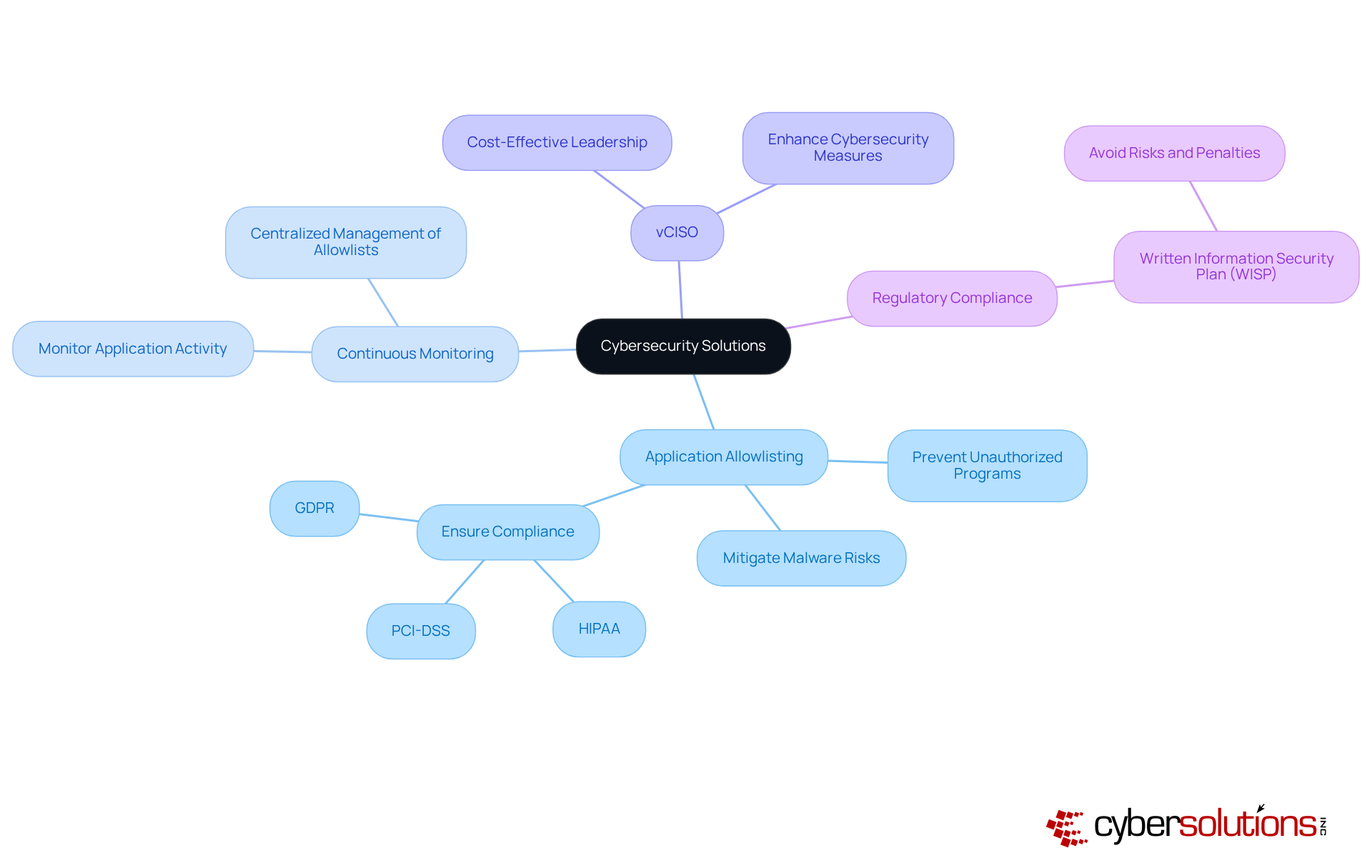
In today's digital landscape, the importance of cybersecurity cannot be overstated, particularly in critical sectors such as finance, healthcare, and legal. As organizations face an increasing number of cyber threats, the need for robust security measures has never been more pressing. Cyber Solutions Inc. specializes in providing tailored IT and cybersecurity solutions that meet the unique demands of these industries. A cornerstone of our strategy is proactive threat detection, a proactive measure designed to prevent unauthorized programs from executing. This approach significantly mitigates the risk of malware and ensures data integrity.
Our strategy not only includes continuous monitoring of application activity but also features centralized management of allowlists. This dual approach enhances security, allowing organizations to protect sensitive data effectively. By integrating these security measures into adaptable organizational applications, companies can safeguard themselves against substantial penalties associated with the absence of a written information security program (WISP).
Furthermore, the incorporation of a cybersecurity framework provides economical cybersecurity leadership, making it an essential consideration for executives focused on investing in solutions that align with their organizational goals. As we look ahead to 2025, the role of cybersecurity in commercial applications will serve as a foundational element for asset protection and compliance in an increasingly regulated environment. The time to act is now—ensuring that your organization is equipped with the necessary tools and strategies to navigate these challenges effectively.
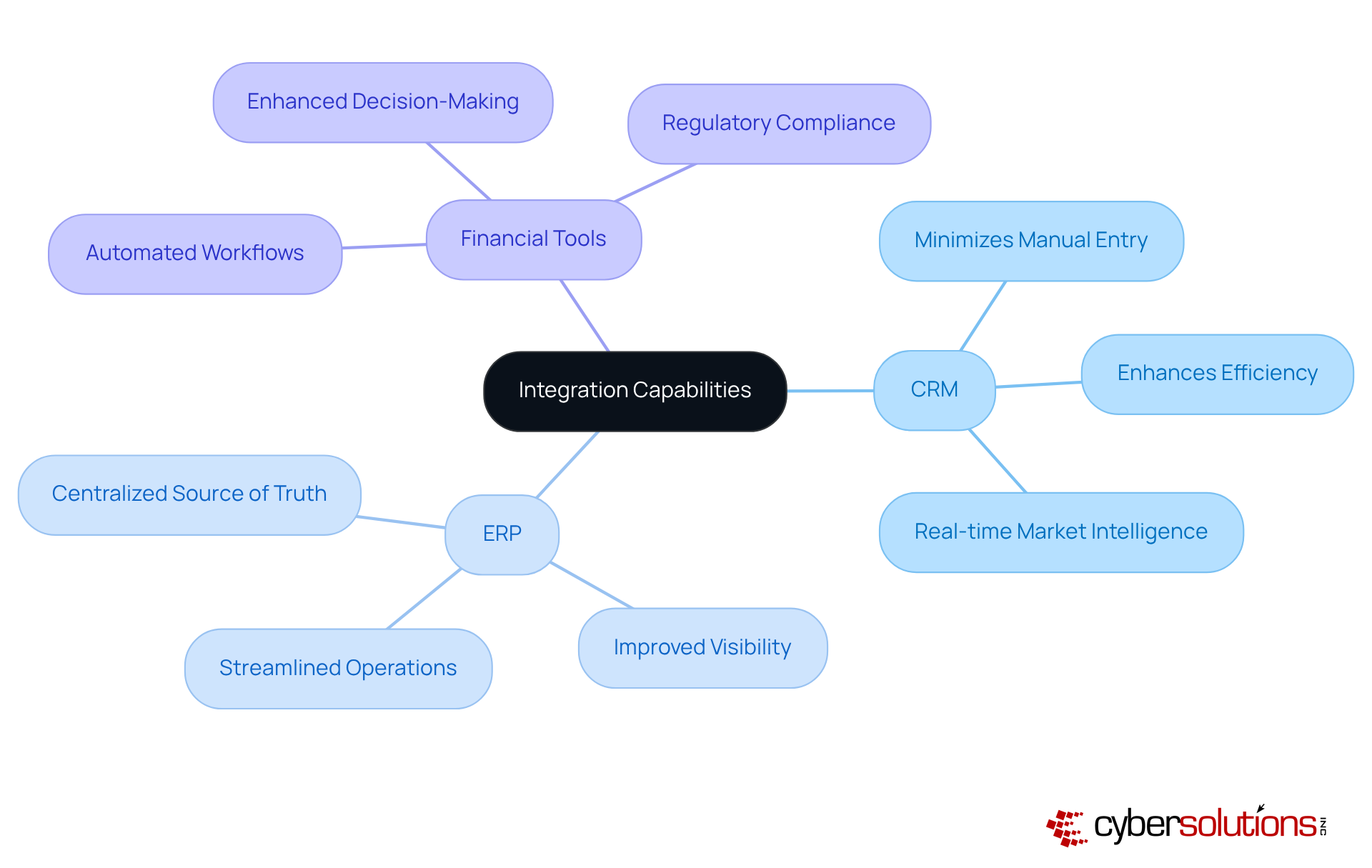
must provide robust integration solutions, including CRM, ERP, and financial tools. This capability is crucial as it guarantees that data flows seamlessly across platforms, thereby enhancing operational efficiency. By utilizing integration tools, organizations can establish a cohesive operational environment that not only improves productivity but also supports informed decision-making.
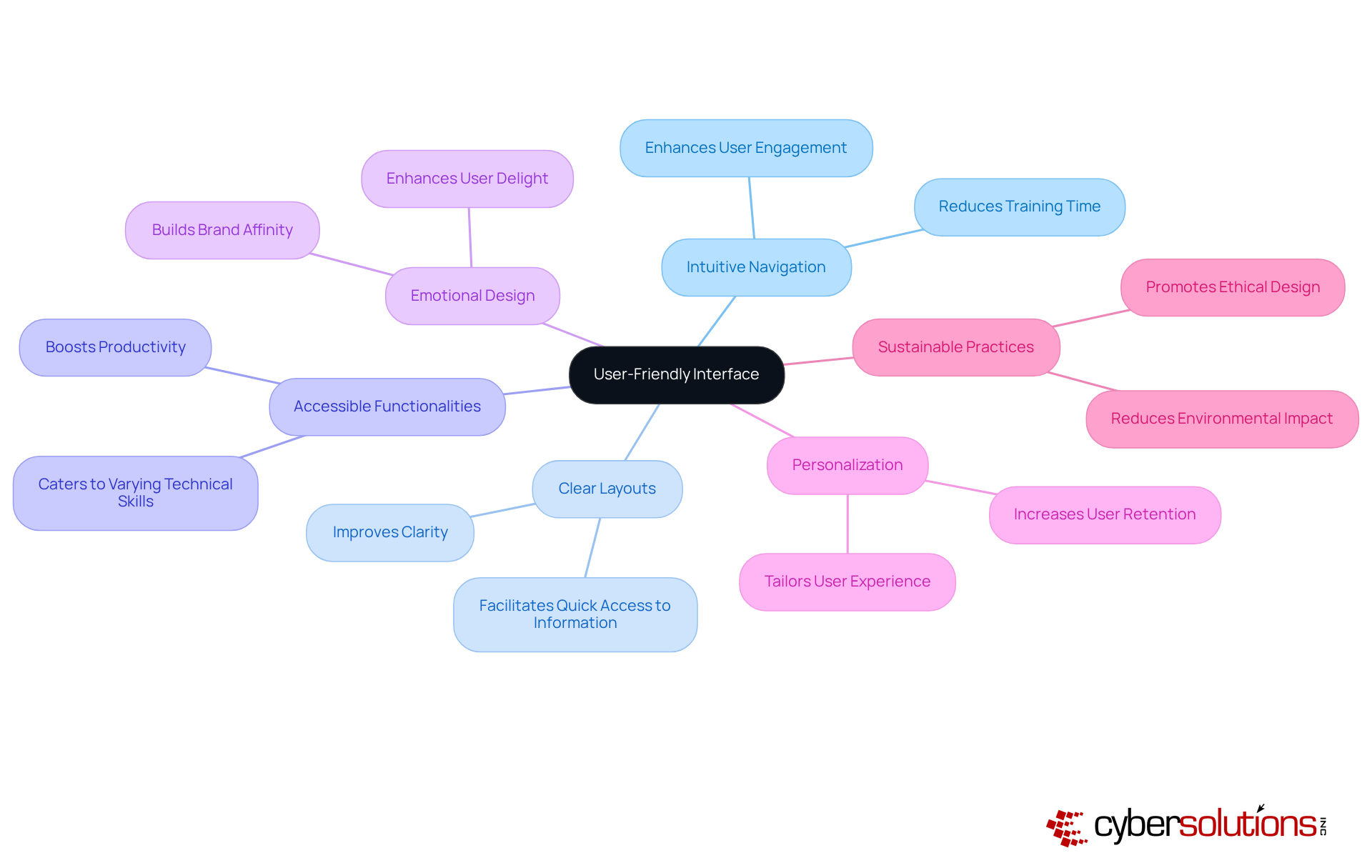
An accessible interface is not just beneficial; it is essential for productivity and driving engagement. Customizable business software must include:
By prioritizing user experience, organizations can significantly reduce training time and frustration, ensuring that employees harness the application to its fullest potential.
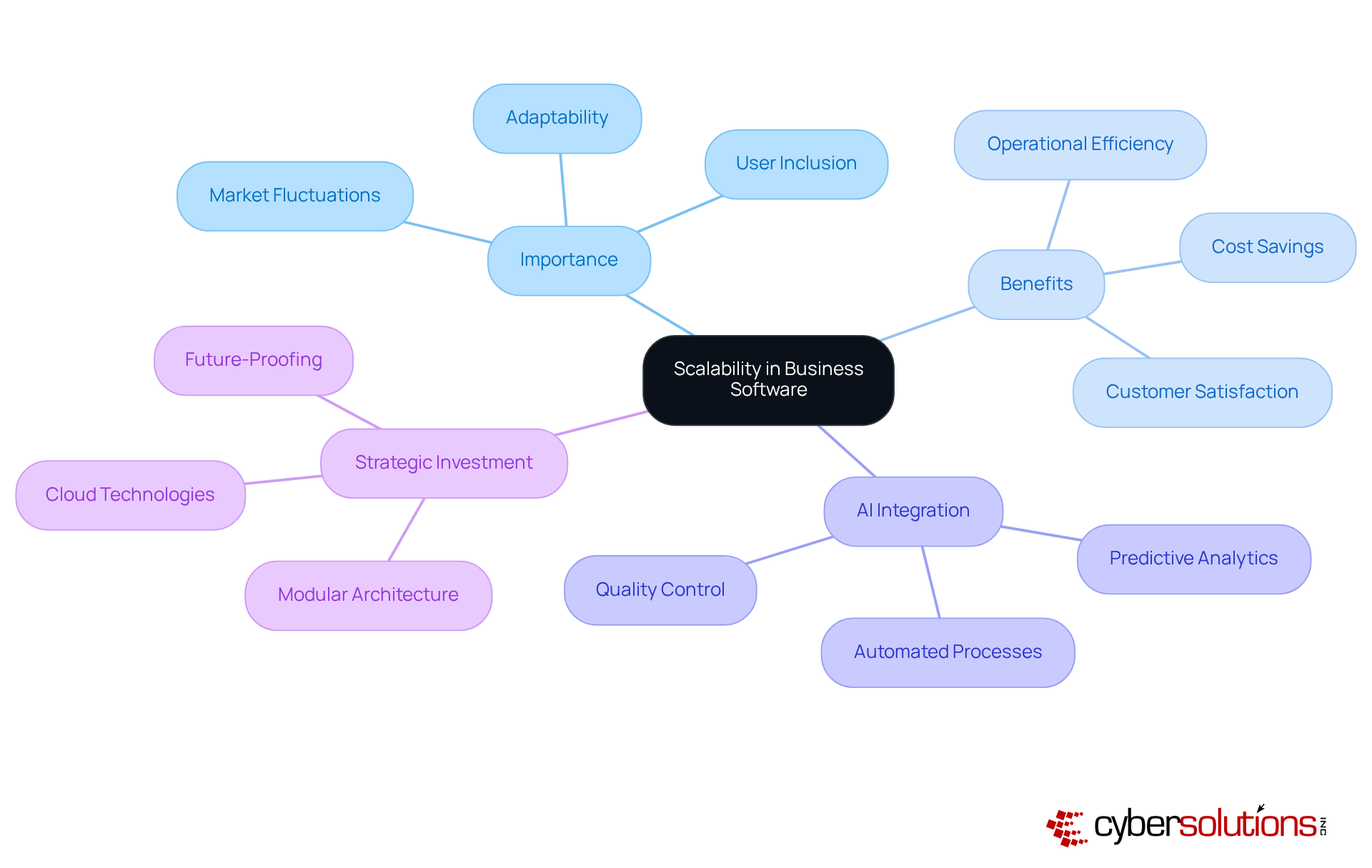
must prioritize scalability, a critical factor that enables organizations to grow operations effortlessly without the need for total system revamps. This capability allows for the seamless inclusion of new users, features, and integrations as organizations evolve. Scalable solutions empower companies to swiftly adapt to market fluctuations and customer demands, fostering growth and competitiveness.
As industry experts emphasize, scalable solutions are not merely a technical necessity; they are a strategic essential that enhances organizational adaptability and growth. Current trends underscore the incorporation of AI and machine learning into business processes, significantly improving predictive analytics and decision-making. For instance, producers employing customizable software have reported substantial enhancements in production rates and efficiency, illustrating how such solutions can drive company growth.
By investing in scalable technology, entities strategically position themselves to handle the challenges of expansion while ensuring optimal performance. This investment is not just a choice; it is a decisive step towards securing a competitive advantage in an ever-evolving market.
Integrating automated functions into adaptable business applications significantly simplifies processes and enhances operational efficiency. Automation effectively manages tasks such as data entry, reporting, and workflow management, alleviating the workload on employees and substantially reducing the risk of errors. By implementing automation, organizations can strategically reallocate resources, allowing teams to focus on higher-value activities that foster growth and innovation.
Current trends indicate that automation tools are enhancing user adoption and satisfaction. For instance, eighty-four percent of employees report enhanced job satisfaction because it enables them to concentrate on more significant work rather than trivial tasks. Furthermore, mechanization can yield considerable time savings; business leaders estimate that automation can save up to 30% of time spent on routine tasks. Notably, AI technologies can automate tasks that encompass 60-70% of employees' current workload, illustrating the potential impact of mechanization on workforce efficiency.
Real-world examples underscore the effectiveness of mechanization in enhancing efficiency. Organizations that have embraced automation have reported significant improvements in operational performance, with two-thirds of respondents in a McKinsey survey noting enhanced quality control and reduced operating costs. Additionally, Salesforce indicates that eighty-four percent of finance personnel assert they can make decisions more swiftly due to technological tools. Automation features in business software enhance data management and reporting, offering entities real-time insights that inform strategic decision-making.
As companies continue to adopt automated solutions, the rise of low-code/no-code platforms is empowering non-technical individuals to design and modify automated processes independently. This trend not only enhances collaboration and agility within teams but also drives innovation by facilitating quicker responses to market demands. However, it is crucial to acknowledge that challenges such as resistance to change and integration issues may arise during the implementation of automated solutions. Ultimately, the role of automation in adaptable enterprise applications is vital for companies seeking to enhance their operations and maintain a competitive edge.

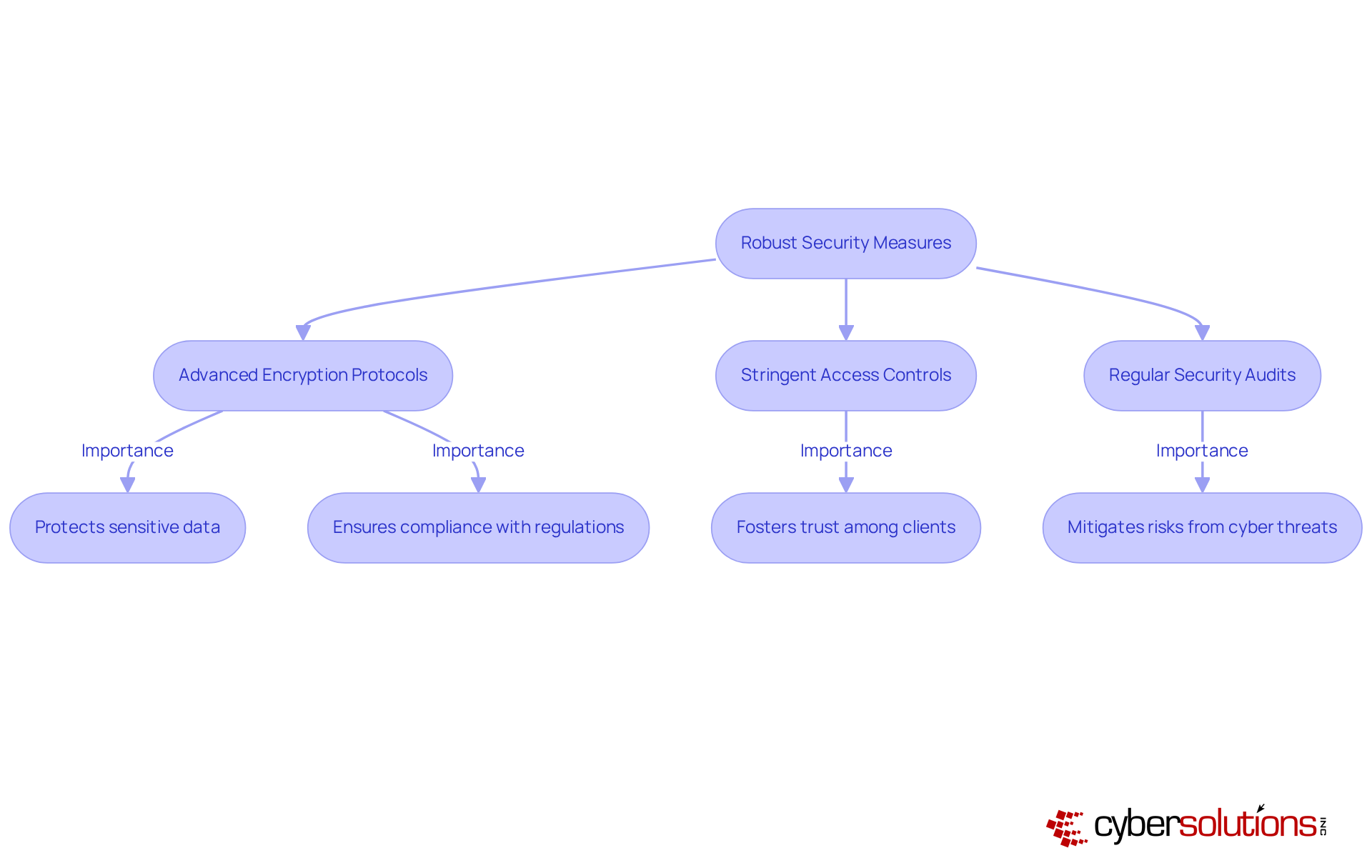
Customizable business software for enterprises must incorporate robust security measures to safeguard sensitive data and ensure compliance.
These measures not only protect against cyber threats but also foster trust among clients and stakeholders. As cyberattacks become increasingly sophisticated, organizations are urged to adopt a proactive security strategy.
By prioritizing these security protocols, organizations can effectively mitigate risks and enhance their overall operational resilience.
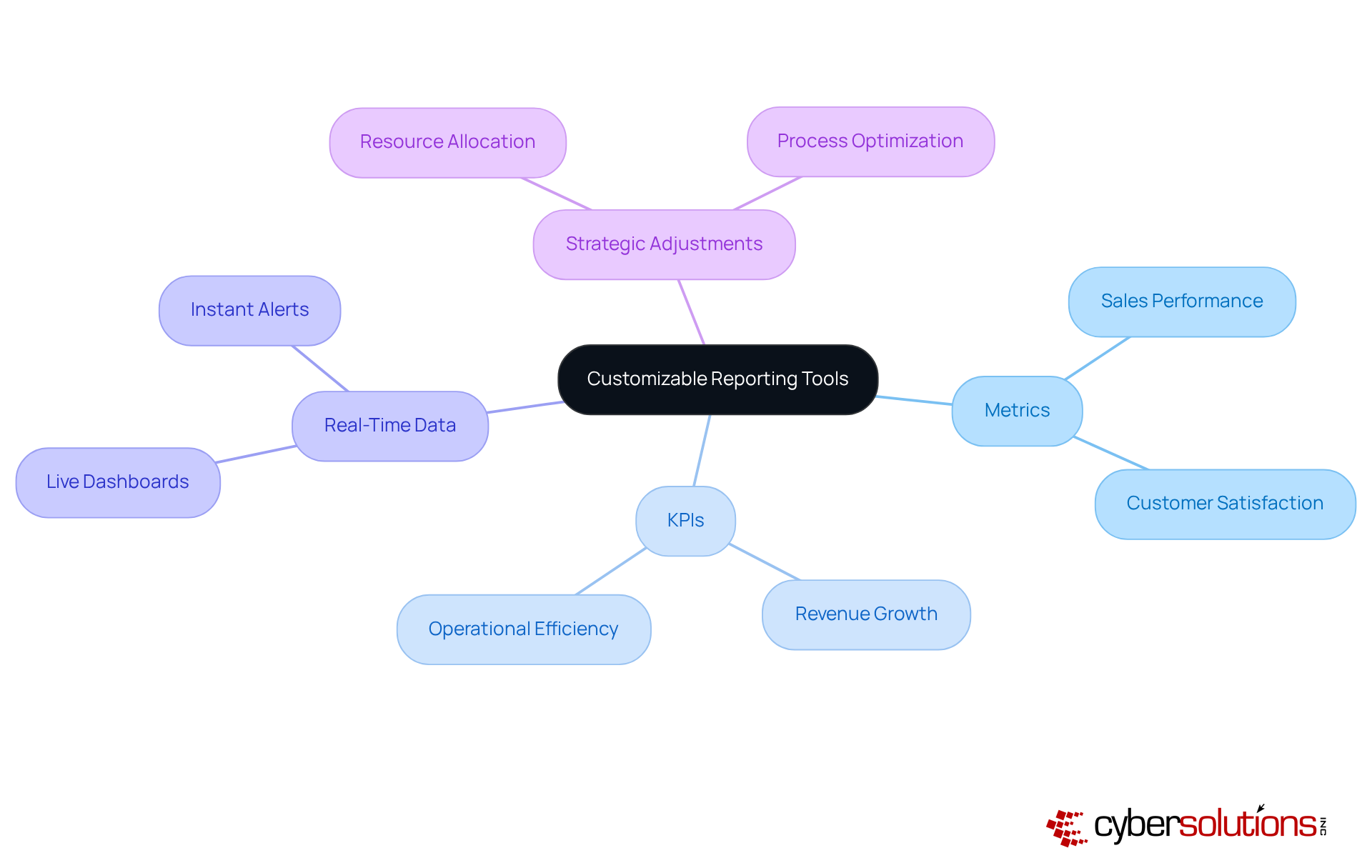
Customizable reporting tools are essential for gaining insights into organizational performance and making informed decisions. These tools empower users to utilize data to create reports that highlight specific metrics and KPIs pertinent to their operations. By providing analytics, organizations can identify trends, assess performance, and implement strategic adjustments to enhance overall effectiveness.
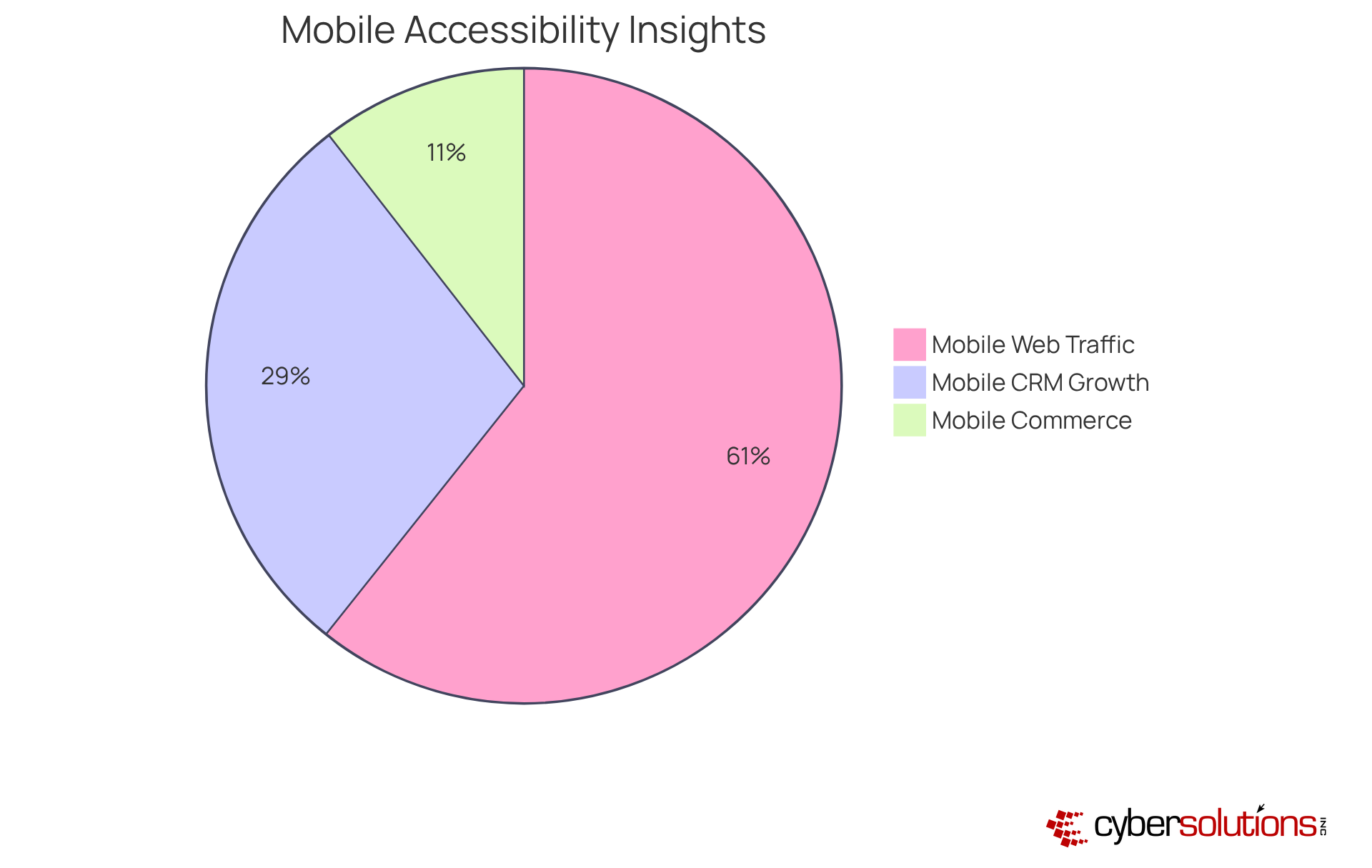
In today's landscape of remote work and mobile operations, the significance of mobile accessibility is undeniable. Mobile solutions must be prioritized, enabling employees to perform their tasks from virtually anywhere. This necessity includes intuitive mobile applications that provide access to essential functions and data on-the-go. By facilitating mobile access, organizations can significantly enhance productivity, ensuring that teams remain productive regardless of their location.
As mobile commerce is projected to account for 10.4% of all U.S. retail sales by 2025, the demand for mobile features is more critical than ever. Experts emphasize that incorporating mobile features not only simplifies processes but also fosters a culture of agility, allowing businesses to adapt swiftly to evolving market conditions. Companies utilizing mobile-friendly applications have reported enhanced collaboration and efficiency, showcasing the tangible advantages of investing in technology that supports remote work.
Moreover, with mobile devices representing 59.99% of web traffic in 2024, the focus on mobile optimization will continue to shape future operational practices. It is essential for organizations to prioritize these features in their development strategies. Furthermore, the worldwide mobile CRM market is projected to expand from $28.43 billion in 2024 to $58.07 billion by 2034, underscoring the growing significance of mobile solutions in corporate applications.
Effective customer support is a cornerstone of customizable business software, ensuring users have immediate access to assistance when needed. This support encompasses:
By delivering robust assistance, organizations can significantly enhance productivity, allowing employees to efficiently leverage the application to achieve their objectives.

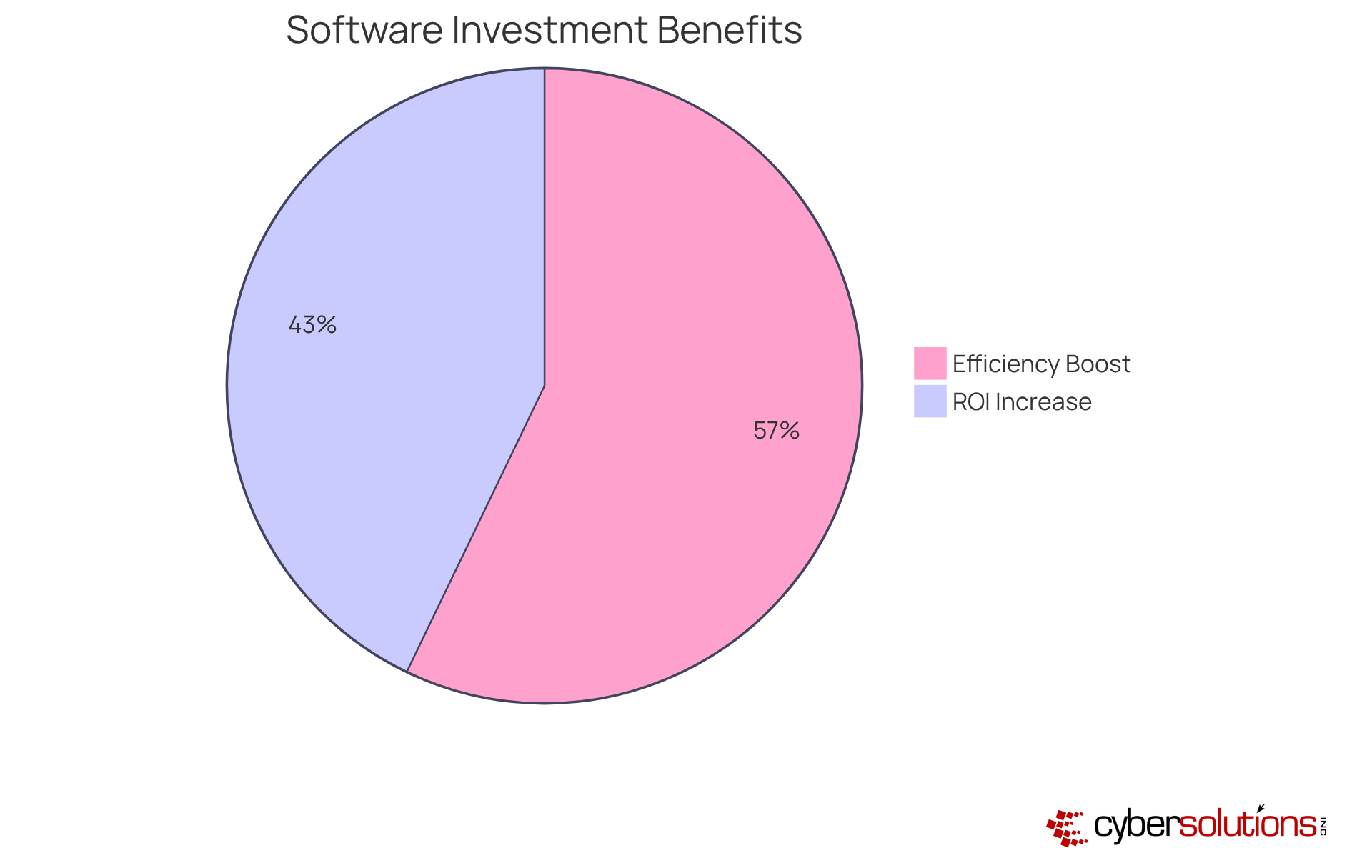
To assist organizations in maximizing their budget, executives must prioritize cost-effectiveness. This approach involves implementing pricing strategies, such as flat-rate pricing, which simplifies budgeting and eliminates unexpected IT expenses. By incorporating essential services like email licenses and software tools into one package, organizations can ensure predictable costs. This strategy not only reduces operational expenses through automation but also allows for scalability without incurring significant additional charges.
Moreover, companies that invest in customizable software can anticipate improved performance. For instance, they may experience:
By carefully evaluating the financial implications of software solutions, executives can make informed decisions that align with their goals and objectives. This proactive approach not only mitigates risks but also positions organizations to thrive in an increasingly competitive landscape.
Investing in customizable business software is not merely an option; it is an essential strategy for organizations striving to enhance operational efficiency, security, and adaptability in an ever-evolving market. By focusing on features such as robust integration capabilities, user-friendly interfaces, and comprehensive security measures, businesses can develop tailored solutions that effectively meet their unique needs while fostering long-term growth and sustainability.
Key features that executives must consider when selecting customizable software include:
Each of these elements significantly contributes to improving productivity, reducing operational costs, and ensuring compliance with industry regulations. Moreover, effective customer support and cost-effectiveness are critical components that maximize return on investment and enhance user satisfaction.
In summary, the significance of investing in customizable business software cannot be overstated. Organizations that embrace these tailored solutions position themselves strategically to navigate challenges, leverage opportunities, and maintain a competitive edge within their industries. As market trends continue to evolve, executives are urged to prioritize these features to secure their operational future and drive innovation within their teams.
Why is cybersecurity important for businesses today?
Cybersecurity is crucial for businesses, especially in sectors like finance, healthcare, and legal, due to the rising array of cybersecurity threats. Robust defenses are necessary to protect sensitive data and ensure compliance with regulations.
What specific cybersecurity solutions does Cyber Solutions Inc. offer?
Cyber Solutions Inc. provides tailored IT and cybersecurity solutions, focusing on application allowlisting to prevent unauthorized program execution, continuous monitoring of application activity, and centralized management of allowlists.
How does application allowlisting enhance cybersecurity?
Application allowlisting mitigates the risk of malware and ensures compliance with regulations such as HIPAA, PCI-DSS, and GDPR, thereby protecting sensitive data and reducing the risk of penalties for lacking a Written Information Security Plan (WISP).
What is the role of a virtual Chief Information Security Officer (vCISO)?
A vCISO offers economical cybersecurity leadership, helping organizations invest in solutions that align with their goals and navigate the increasingly regulated cybersecurity landscape.
What are the integration capabilities that customizable business software should have?
Customizable business software should provide robust integration features with existing systems like CRM, ERP, and financial tools to ensure seamless data flow, minimize manual entry, and reduce errors.
How do APIs contribute to operational efficiency in business software?
APIs and other integration tools help establish a cohesive operational environment, enhancing efficiency and supporting informed decision-making by allowing data to flow seamlessly across platforms.
Why is a user-friendly interface important in customizable business software?
An accessible interface enhances user experience and drives application adoption by providing intuitive navigation, clear layouts, and functionalities tailored to users with varying technical skills.
What benefits does prioritizing user experience in software design bring to organizations?
Prioritizing user experience can significantly reduce training time and boost overall productivity, ensuring that employees can effectively utilize the application to its fullest potential.