
In a world where digital threats loom larger than ever, small businesses find themselves increasingly vulnerable to cyberattacks that could cripple their operations. With a staggering 75% of these enterprises having faced at least one online attack in the past year, the urgency for robust cyber insurance has never been more pressing.
This article delves into ten compelling reasons why investing in cyber insurance is essential for small businesses in 2025, illuminating the protective measures that can safeguard their financial stability and operational continuity.
As the landscape of cyber threats evolves, the question remains: how can small businesses ensure they are adequately prepared to confront these challenges head-on?
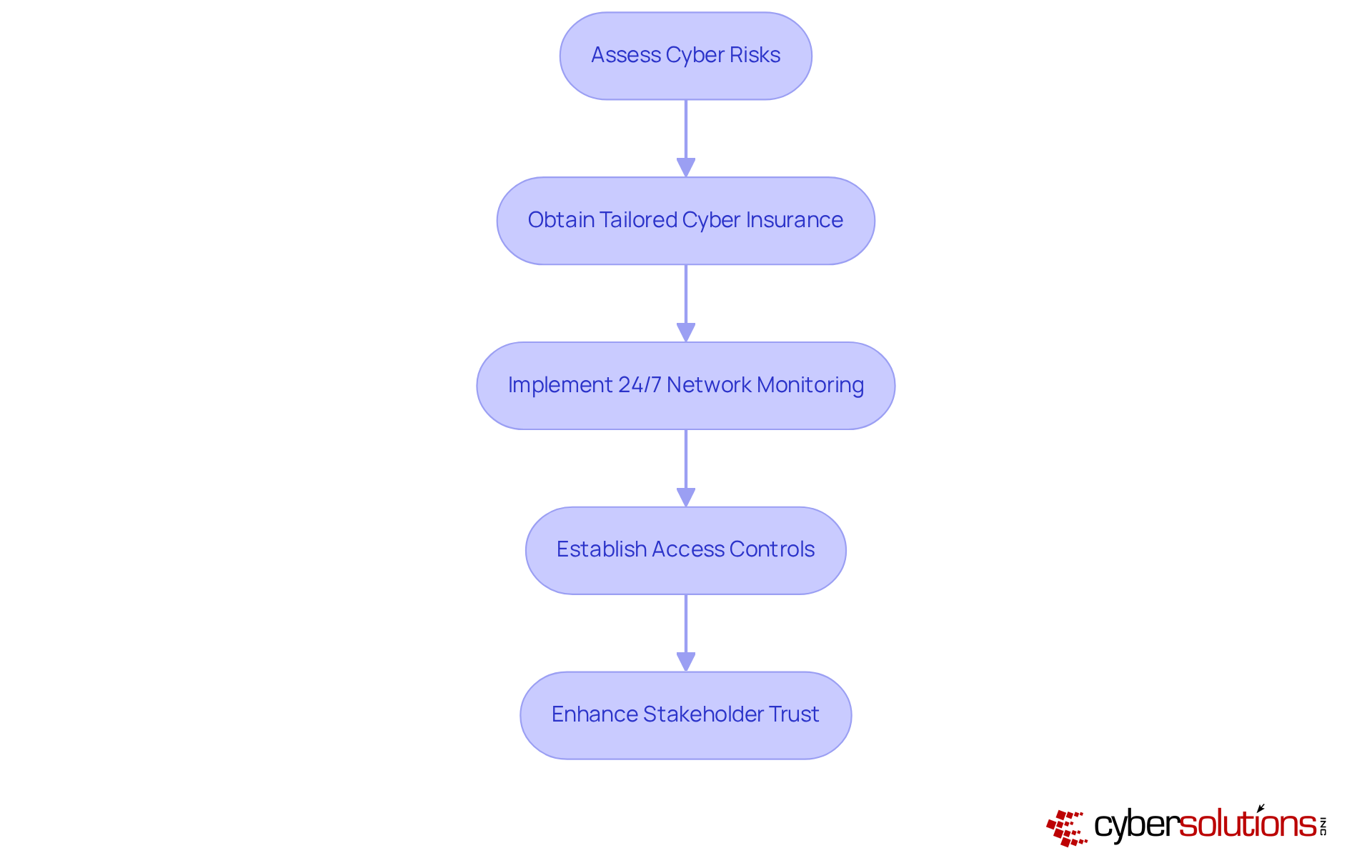
In today’s digital landscape, cyber insurance is not just an option; it’s a necessity. Cyber Solutions Inc. provides a specifically designed solution to address the unique challenges faced by small businesses. By meticulously assessing these risks, Cyber Solutions ensures that clients receive protection that not only shields against digital threats but also aligns seamlessly with their financial strategies. This customized approach is crucial, especially considering that 75% of minor enterprises underestimate their vulnerability to cyberattacks, with many indicating they could not sustain operations if impacted by ransomware. Moreover, the average recovery cost from such attacks can soar to $120,000, underscoring the importance of having adequate coverage.
To enhance this protective framework, Cyber Solutions delivers robust monitoring services. This continuous monitoring identifies anomalies and potential vulnerabilities, providing immediate alerts and real-time insights that empower swift action to avert downtime or breaches. Such measures are essential in defending against ransomware, phishing, and other malware threats, ensuring that suspicious activities are detected and neutralized before they escalate into significant risks. Additionally, the services encompass access controls and tailored restrictions, guaranteeing that only authorized personnel can access sensitive information.
Experts assert that cyber insurance is indispensable, as it enables businesses to manage risks without overspending on unnecessary coverage. By investing in cyber insurance, these enterprises can bolster their resilience against online dangers, minimize downtime, and expedite recovery following an incident. This strategic investment not only protects assets but also enhances stakeholder trust, illustrating a commitment to protecting essential information in an increasingly digital environment.
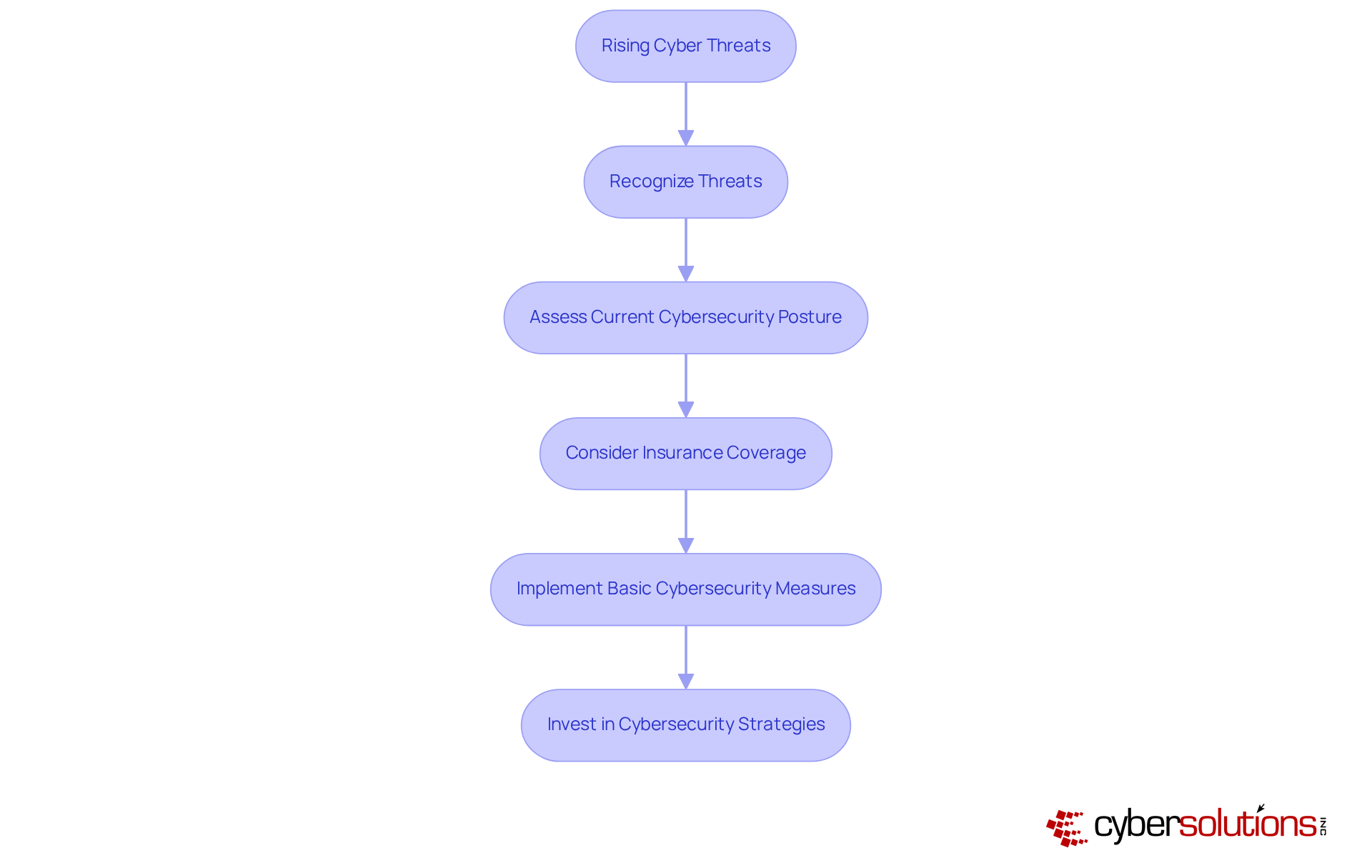
In 2025, minor enterprises face a troubling rise in cyber threats, including ransomware, phishing, and data breaches. The complexity of these threats has intensified, highlighting the urgent necessity for cyber insurance. Data indicates that 75% of minor enterprises experienced at least one online attack in the previous year, with ransomware incidents averaging $35,000 in costs each. Furthermore, nearly 60% of minor enterprises that suffer a significant cyberattack cease operations within six months, underscoring the severe impact of such incidents.
Real-world examples underscore this urgency:
Experts emphasize that cyber insurance is not merely a safety net but a crucial component of a risk management strategy. With the average cost of a cyberattack for small enterprises reaching $120,000 in 2025, having coverage can provide financial protection and peace of mind. Additionally, many insurers now require companies to implement basic security measures to qualify for coverage, further promoting proactive security practices.
A recent case involving a healthcare provider demonstrates the effectiveness of a layered cybersecurity approach, which includes rapid response and specialized expertise. By acting swiftly and having an incident response team on-site, the provider not only contained the threat but also improved its security measures, resulting in a significant reduction in potential future breaches. This example highlights the importance of cyber insurance as part of a broader strategy to safeguard operations and ensure long-term sustainability, particularly in the face of emerging threats. To mitigate risks, minor enterprises should regularly assess their cybersecurity posture and consider acquiring comprehensive digital protection to shield against potential financial setbacks.
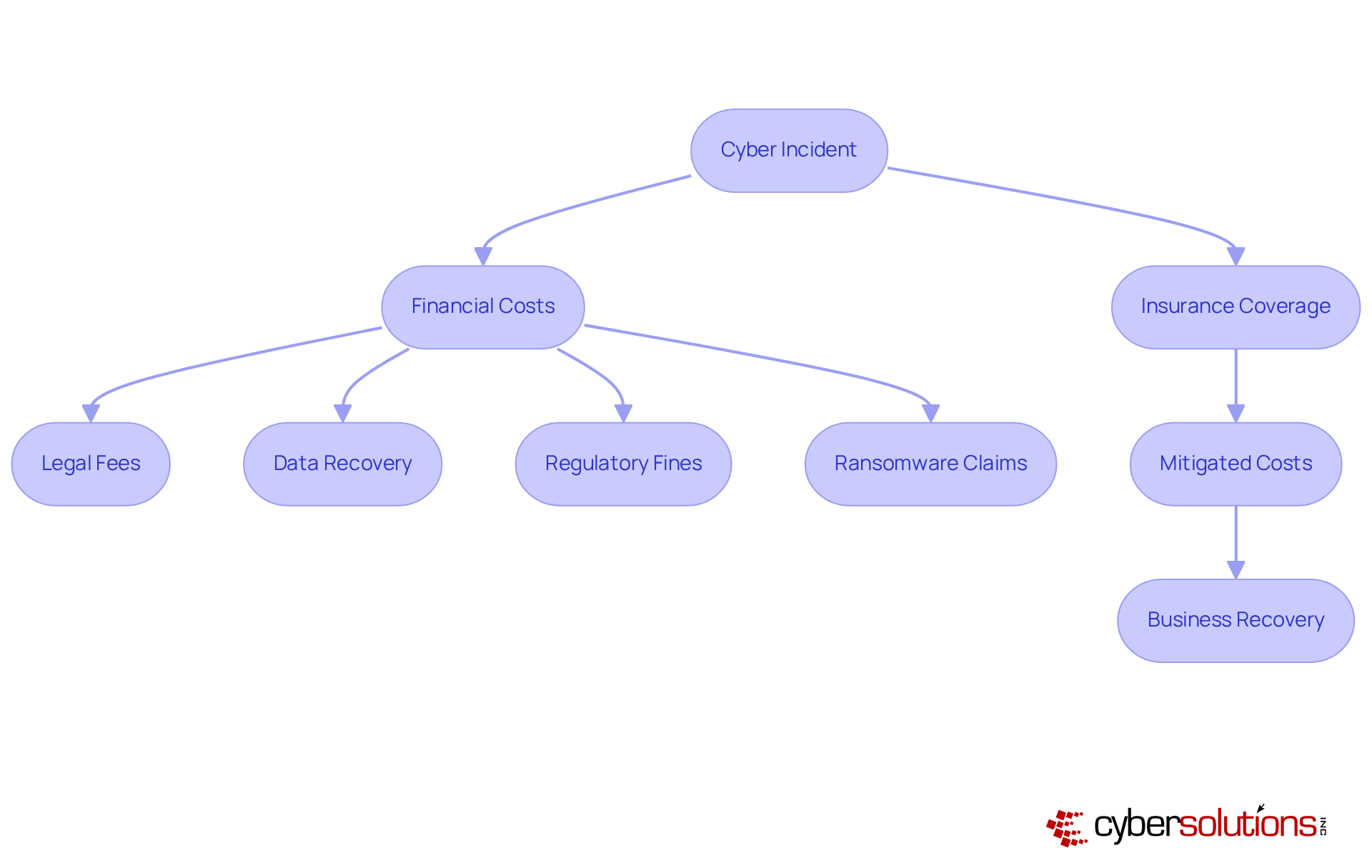
Cyber insurance is an essential investment, especially as the frequency and severity of cyberattacks continue to escalate. The average cost of a data breach for small businesses can soar to approximately $120,000, encompassing expenses such as legal fees, data recovery, and potential regulatory fines. Without adequate coverage, these costs can threaten the very existence of a small enterprise.
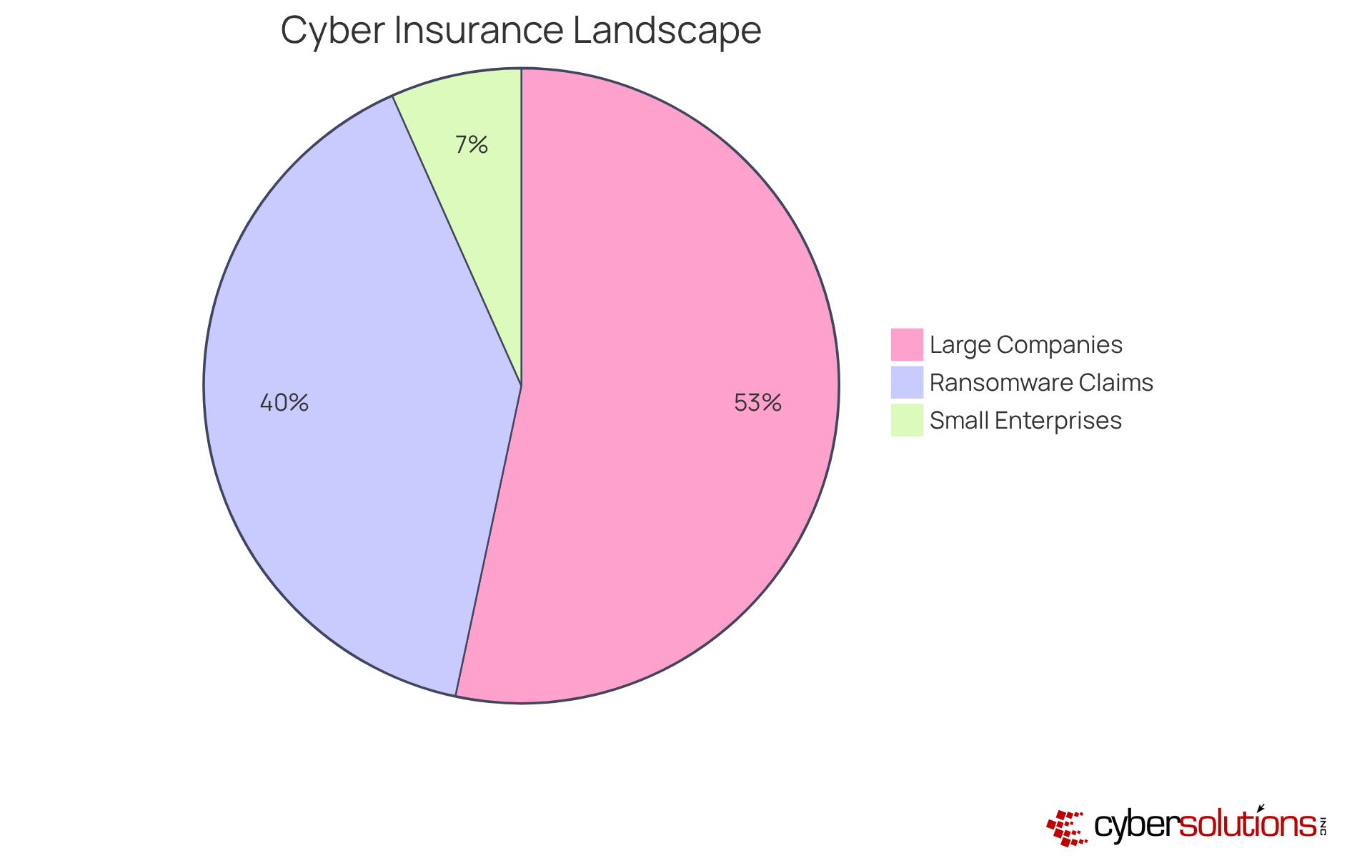
In the first half of 2025, ransomware attacks represented 60% of the value of major claims, underscoring the substantial financial impact. Cyber insurance mitigates these risks by covering a range of costs associated with cyberattacks and ransomware incidents, allowing businesses to recover swiftly and maintain operations. For instance, companies that have implemented cyber insurance policies have reported successful recoveries from incidents, showcasing the effectiveness of these policies in preserving their financial health.
Moreover, as digital threats continue to evolve, the necessity for cyber insurance becomes increasingly evident. A recent study revealed that claims related to data exfiltration were more than twice as costly as those without, emphasizing the need for businesses to reassess their coverage needs. Financial experts assert that cyber insurance is not merely a precaution; it is a strategic decision aimed at ensuring long-term viability in an unpredictable digital landscape. By securing appropriate coverage, small enterprises can protect themselves from the potentially devastating financial repercussions of cyber incidents, ensuring their resilience during challenging times.
In today's digital landscape, the importance of robust cybersecurity cannot be overstated, especially for healthcare organizations. As they navigate unique challenges such as data breaches, the need for tailored cyber coverage becomes paramount. Factors like industry, size, and existing cybersecurity measures play a critical role in determining the appropriate coverage. For example, while healthcare entities grapple with specific compliance risks, financial institutions must contend with SEC regulations.
Cyber Solutions Inc. stands out by collaborating closely with clients to assess their specific needs. This partnership enables the creation of customized policies that provide optimal protection without incurring unnecessary costs. Such a tailored approach not only ensures adequate coverage against prevalent threats like ransomware and phishing attacks but also underscores the vital need for proactive risk management. Continuous monitoring is essential; it allows for the detection and mitigation of suspicious activities before they escalate into significant threats, thereby protecting the organization.
As of 2024, a striking 87% of executives believe their companies are inadequately protected, underscoring the urgent need for comprehensive cyber insurance. Moreover, it is crucial for businesses to evaluate their coverage options to avoid the pitfalls of being underinsured. By concentrating on tailored solutions, organizations can effectively manage the complexities of digital protection, safeguarding their operations and bolstering overall resilience. CFOs are strongly urged to evaluate their current cyber coverage policies and consult with Cyber Solutions Inc. for customized solutions that specifically address their requirements.

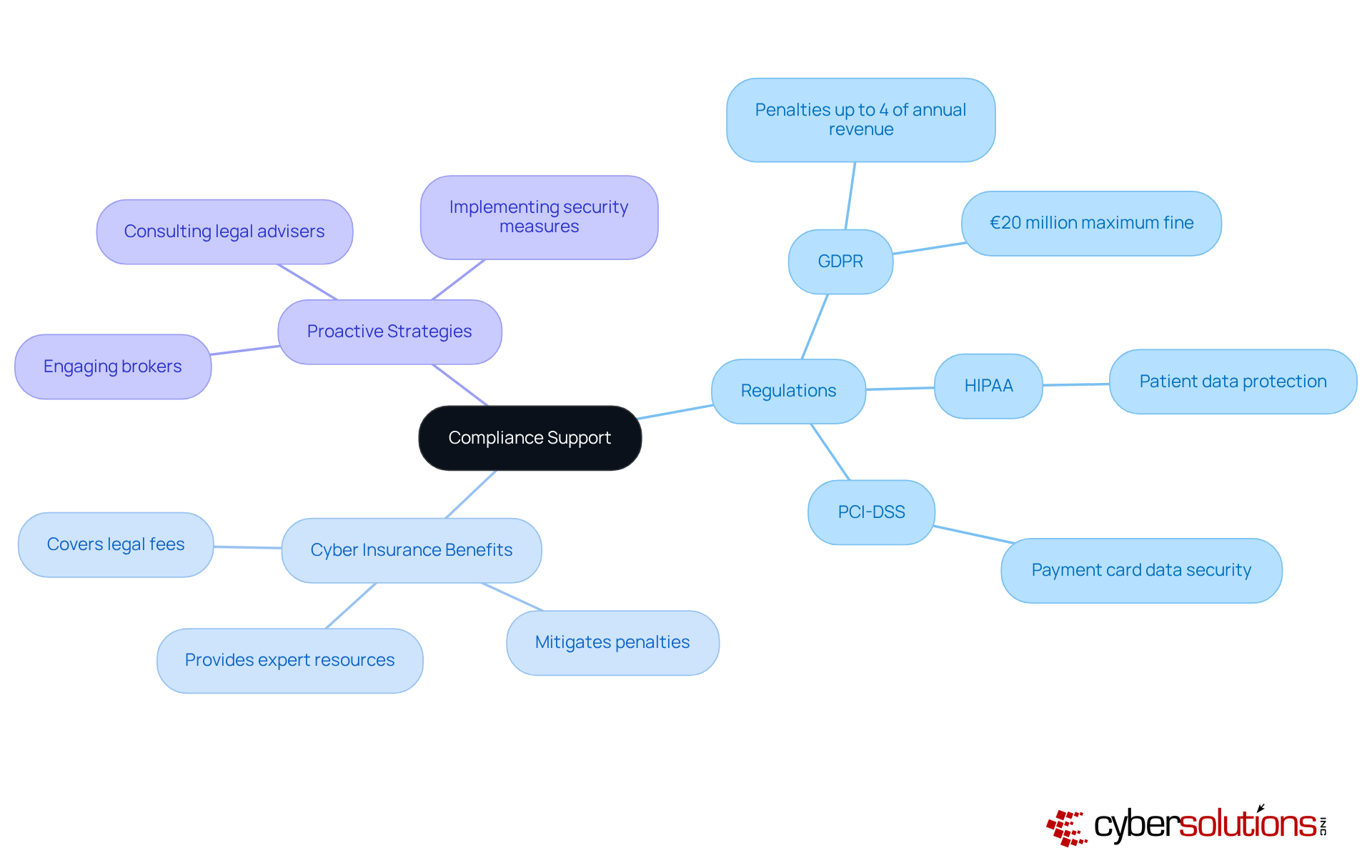
In today's highly regulated landscape, the importance of adhering to regulations such as GDPR, HIPAA, and PCI DSS cannot be overstated for businesses. Cyber insurance plays a vital role in assisting organizations with compliance, covering liabilities stemming from non-compliance. Did you know that violations can lead to penalties of up to 4% of annual global revenue or €20 million? This stark reality underscores the necessity of cyber insurance as a crucial safeguard.
Furthermore, numerous insurers provide valuable resources and expert advice to help organizations implement best practices, thereby ensuring compliance and minimizing risk exposure.
Legal experts stress that engaging with brokers and legal advisers is critical for policyholders to fully understand their coverage and effectively manage risks. This proactive approach not only mitigates risks but also builds resilience in the face of evolving regulatory demands.
As the landscape of cybersecurity threats continues to evolve, organizations must remain vigilant and equipped to tackle these challenges head-on.
Cyber insurance coverage is paramount in reinforcing trust in data security. When clients observe that a business has proactively implemented extensive measures to safeguard their data, it fosters a sense of safety and confidence. This trust is critical; research indicates that companies with robust cyber insurance are perceived as more reliable, leading to increased customer loyalty and an enhanced reputation.
Notably, 62% of companies with cyber insurance report improved customer retention, providing a competitive advantage in today's market. Branding specialists assert that the visibility of cyber insurance not only mitigates risks but also serves as evidence of a company's dedication to safeguarding sensitive information.
A recent case exemplifies this principle; their swift response and multi-layered approach not only contained a ransomware threat but also strengthened their security measures, resulting in a 30% increase in customer satisfaction ratings following the incident. This proactive strategy not only alleviated immediate threats but also bolstered their reputation as a trustworthy entity in the healthcare sector.
Businesses can significantly enhance their brand reputation, positioning themselves as dependable allies in an increasingly digital landscape.

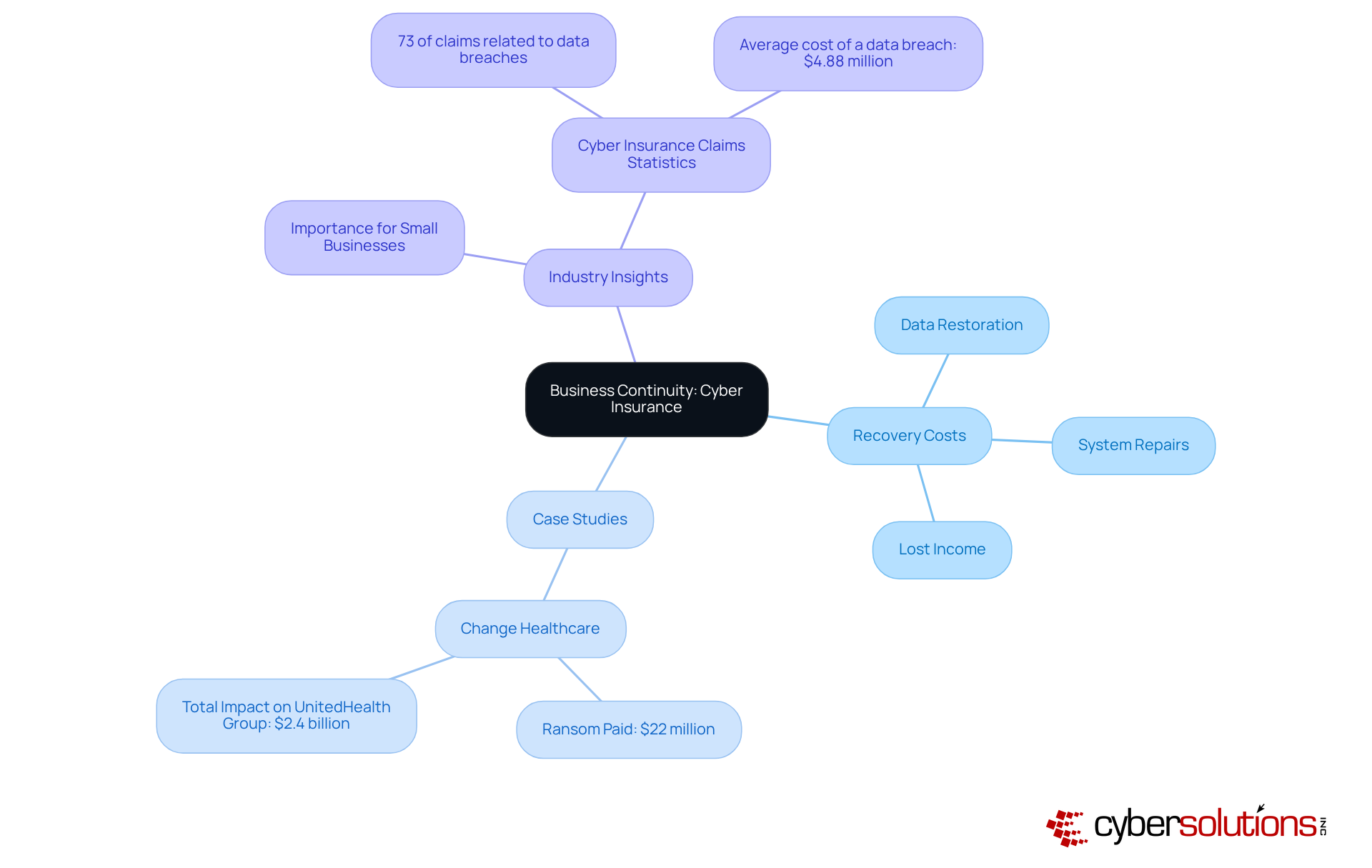
Digital coverage is vital for operational continuity, enabling organizations to swiftly recover from online incidents. In the wake of a cyber attack, this coverage addresses various risks, including:
For instance, companies facing ransomware attacks often rely on their cyber insurance policies to mitigate losses, with recovery expenses averaging over $2.5 million per incident. Such financial support not only sustains operations but also minimizes disruptions, fostering resilience.
Moreover, entities like Change Healthcare exemplify the effectiveness of cyber insurance in managing the fallout from significant breaches. In a notable case, Change Healthcare paid a ransom of $22 million, resulting in a total impact of approximately $2.4 billion on UnitedHealth Group. This underlines the importance of preparedness in navigating crises.
Industry specialists emphasize that having cyber insurance is increasingly recognized as a necessity associated with online threats. This growing awareness underscores the importance of integrating risk management strategies into business operations, ensuring organizations are well-equipped to confront the challenges posed by contemporary online threats.
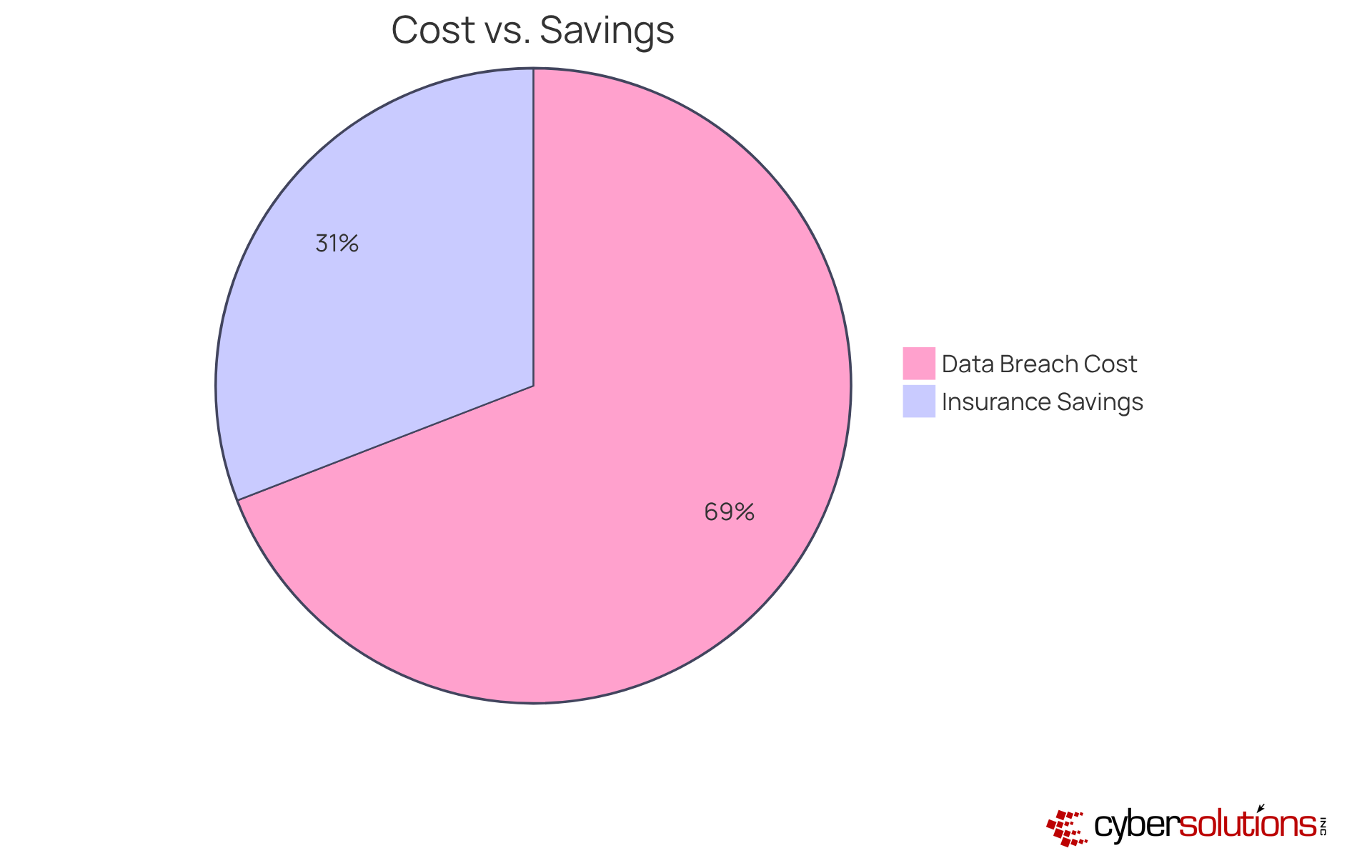
Investing in cyber insurance is a strategic financial choice, providing significant cost-effectiveness. While premiums may initially appear as an extra expense, the potential savings can be staggering. For example, the average cost of a data breach globally is approximately $3.86 million, whereas, in the U.S., it reached $8.64 million in 2020. This stark contrast underscores the necessity of having coverage in place to mitigate substantial losses and ensure access to financial resources.
Moreover, cyber insurance not only shields against immediate financial impacts but also promotes long-term stability. By covering costs related to data recovery, legal fees, and customer notifications, businesses can avert crippling expenses that threaten their operations. Financial analysts emphasize that businesses demonstrating proactive measures through enhanced cybersecurity may reduce their coverage expenses, thereby increasing their return on investment. As Lauren Winchester notes, "Anticipation, as the key to effective risk management, is essential."
In the long run, the financial advantages of investing in online security coverage can be substantial. With proper planning, as highlighted by AmTrust, having a robust coverage plan can be the difference between recovery and closure. As the digital protection market is projected to expand to $22.5 billion by 2025, it is clear that companies are recognizing the critical role of cyber insurance in their strategies. Thus, the need for small businesses positions it as an essential investment for small enterprises navigating the complexities of today's online landscape.
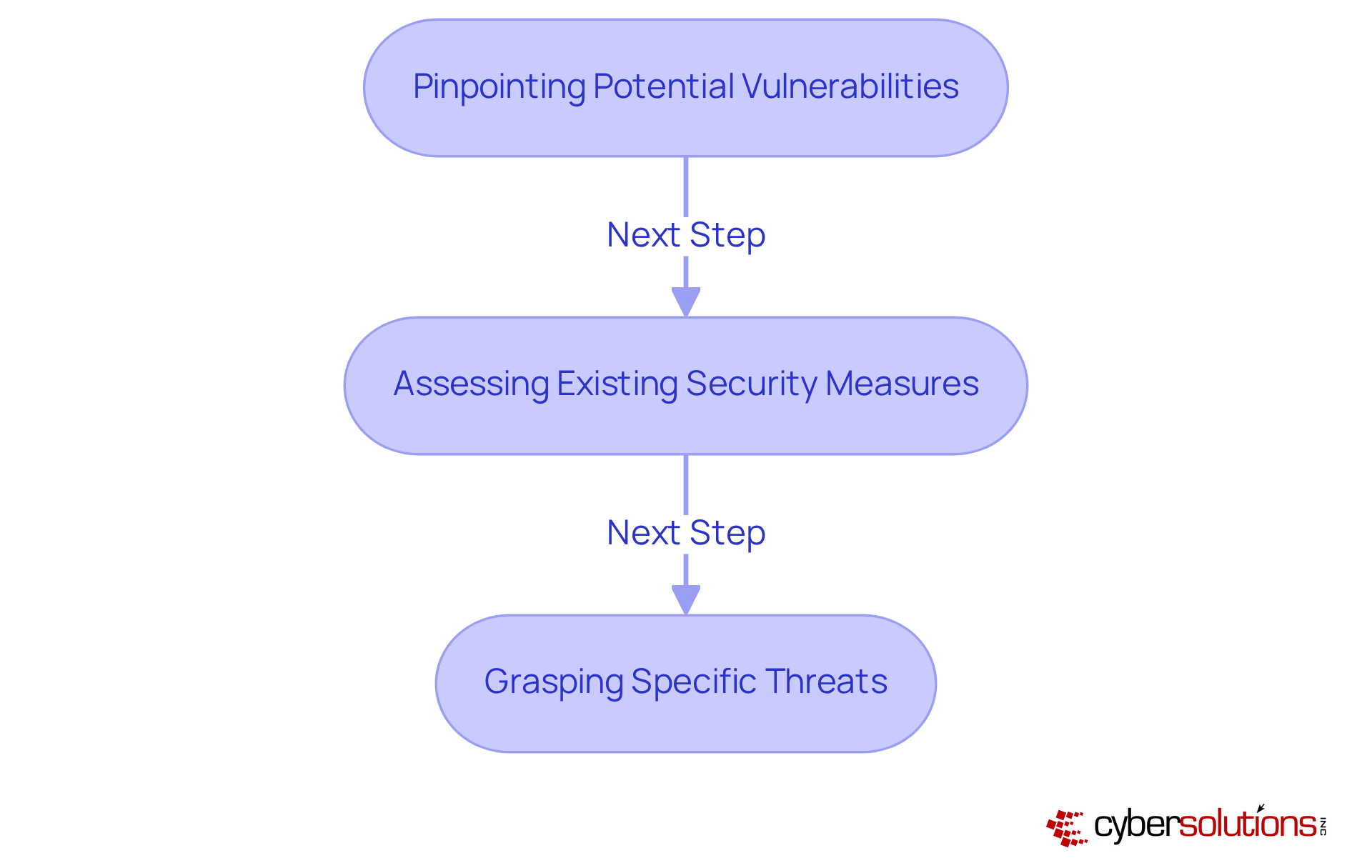
For minor enterprises striving to secure appropriate coverage, risk assessment is imperative. This critical process involves:
With a staggering 41% of minor enterprises experiencing a cyber incident, securing insurance is not just beneficial; it is essential for survival. A thorough understanding of the risk environment empowers organizations to make informed decisions regarding coverage options, ensuring robust protection against digital threats.
Moreover, statistics reveal that only 14% of small enterprises can effectively mitigate cyber risks, highlighting the urgency of considering insurance solutions. For example, Efficient Services Escrow Group faced a devastating loss of $1.5 million due to insufficient cybersecurity measures, illustrating the financial impact of cyber threats. Cybersecurity experts assert that risk assessment is crucial for determining coverage requirements in small businesses, as it enables organizations to tailor their protections to address specific threats.
At Cyber Solutions, we assist you in developing a comprehensive risk management strategy while integrating multifactor authentication (MFA) and other security measures that can significantly diminish vulnerabilities and enhance protection. As specialists emphasize, MFA is no longer a mere option; it has become a fundamental necessity for every small and medium-sized enterprise. By prioritizing risk evaluations, minor enterprises can strengthen their defenses and ensure they are adequately protected against the evolving landscape of digital threats.
As we approach 2025, the landscape of digital risk coverage is poised for change. Heightened digital threats and increasing regulatory pressures are compelling insurers to implement more stringent coverage requirements. This shift is underscored by the fact that:
Furthermore, advancements in technology are facilitating the development of more sophisticated coverage products aimed at addressing cyber threats, which constituted 60% of large claims in the first half of 2025. Notably, ransomware was implicated in 88% of data breaches at small and medium-sized enterprises, underscoring the unique risks these organizations face and the need for comprehensive coverage.
To effectively counter these threats, continuous monitoring is essential, ensuring that suspicious activities are identified and mitigated before escalating into significant threats. Small enterprises must remain vigilant and informed about trends in cybersecurity to ensure they are adequately prepared and can capitalize on new opportunities in the evolving insurance market. This includes comprehending how regulatory frameworks influence coverage and recognizing the necessity of compliance measures, which are increasingly mandated by insurers.
To bolster their cybersecurity posture, small enterprises should implement proactive measures, including risk assessments and employee training.
By adapting to these changes and executing these strategies, small businesses can enhance their resilience and effectively secure their operations through cyber insurance.
In the rapidly evolving digital landscape of 2025, cyber insurance emerges as an indispensable resource for small businesses. As organizations face increasing cyber threats, including ransomware and data breaches, the necessity of tailored cyber coverage cannot be overstated. Investing in comprehensive cyber insurance not only safeguards vital data but also fortifies businesses against significant financial losses, ensuring operational continuity and enhancing stakeholder trust.
Key insights highlight the alarming statistics surrounding cyber incidents:
This underscores the importance of customized policies that align with specific business needs, proactive monitoring, and compliance with regulatory frameworks. Real-world examples illustrate the devastating consequences of inadequate coverage, reinforcing that cyber insurance is not merely a safety net but a crucial component of a robust risk management strategy.
Ultimately, the call to action is clear: small businesses must prioritize cyber insurance as a strategic investment to navigate the complexities of digital threats. By taking proactive measures, conducting thorough risk assessments, and collaborating with specialized providers like Cyber Solutions Inc., organizations can enhance their resilience, protect their operations, and secure a sustainable future in an increasingly perilous digital environment.
Why is cyber insurance necessary for small businesses?
Cyber insurance is essential for small businesses as it provides protection against digital threats, which have become increasingly prevalent. Many small enterprises underestimate their vulnerability to cyberattacks, and without insurance, they risk significant financial losses that could threaten their operations.
What types of cyber threats are small businesses facing in 2025?
In 2025, small businesses are facing a rise in various digital threats, including ransomware, phishing, and data breaches. These threats have intensified in complexity, making cyber insurance a crucial component of risk management.
What are the average costs associated with cyberattacks for small businesses?
The average recovery cost from a cyberattack for small businesses can reach approximately $120,000. This includes expenses related to legal fees, data recovery, and potential regulatory fines.
How does Cyber Solutions Inc. support small businesses with cyber insurance?
Cyber Solutions Inc. provides a comprehensive suite of tailored cyber insurance options, robust 24/7 network monitoring, and alert services to identify vulnerabilities and potential threats. Their customized approach ensures that clients receive protection that aligns with their financial strategies.
What are the consequences of not having cyber insurance for small businesses?
Without cyber insurance, small businesses face severe financial repercussions, including the risk of ceasing operations after a significant cyberattack. Nearly 60% of small enterprises that experience a major attack may close within six months.
What proactive measures do insurers require for cyber coverage?
Many insurers now require small businesses to implement basic cybersecurity measures to qualify for coverage, promoting proactive security practices that help mitigate risks.
Can cyber insurance help with recovery from cyber incidents?
Yes, cyber insurance can help small businesses recover swiftly from incidents by covering costs associated with data breaches and ransomware attacks, thereby maintaining operational continuity.
What is the importance of a layered cybersecurity approach?
A layered cybersecurity approach, which includes rapid incident response and specialized expertise, is crucial in effectively managing threats. It can significantly reduce the likelihood of future breaches and improve overall security measures.
How can small businesses assess their cybersecurity needs?
Small businesses should regularly evaluate their cybersecurity posture and consider acquiring comprehensive digital protection to shield against potential financial setbacks from cyber incidents.