
Understanding the myriad ways cybercriminals infiltrate organizations is not just important; it is essential for safeguarding sensitive information, especially in sectors like healthcare where the stakes are exceptionally high. In this context, every C-suite leader must recognize the urgent need to fortify their cybersecurity strategies against evolving threats. This article delves into ten essential attack vectors that leaders must comprehend to effectively protect their organizations.
By exploring these definitions, executives can identify vulnerabilities within their systems and implement robust defenses. Yet, as the landscape of cyber threats continues to evolve, the pressing question remains: how can leaders ensure they stay ahead of these sophisticated attacks while maintaining operational integrity?
In today’s rapidly evolving digital landscape, the importance of cybersecurity cannot be overstated, especially within the healthcare sector. Cyber Solutions Inc. provides a comprehensive suite of services. Among these, the incident response team stands out as a critical component, offering prompt assistance during incidents to significantly reduce potential damage and enhance recovery. Furthermore, the incorporation of threat assessments, email safeguards, firewalls, and managed defense services strengthens defenses against cyber risks, ensuring that organizations remain resilient in the face of threats.
Utilizing threat intelligence, Cyber Solutions empowers entities to proactively defend against breaches, safeguarding sensitive data while ensuring compliance. This holistic approach not only fortifies protection but also enhances operational efficiency, allowing businesses to concentrate on their core functions without the complexities of IT management. As organizations navigate the shifting landscape of cyber threats, the adoption of cybersecurity frameworks is increasingly recognized as a strategic investment, aligning protective measures with corporate objectives and bolstering overall resilience.
It is essential to understand that cybersecurity is not a one-time endeavor but an ongoing process that requires continuous oversight and adaptation to emerging challenges. This perspective underscores the importance of viewing cybersecurity as a collective responsibility across the organization, fostering a culture that enhances defensive capabilities and ensures that all team members remain vigilant against potential threats. Moreover, our managed services present a cost-effective alternative to maintaining an in-house team, enabling organizations to allocate resources more efficiently while achieving robust protection.

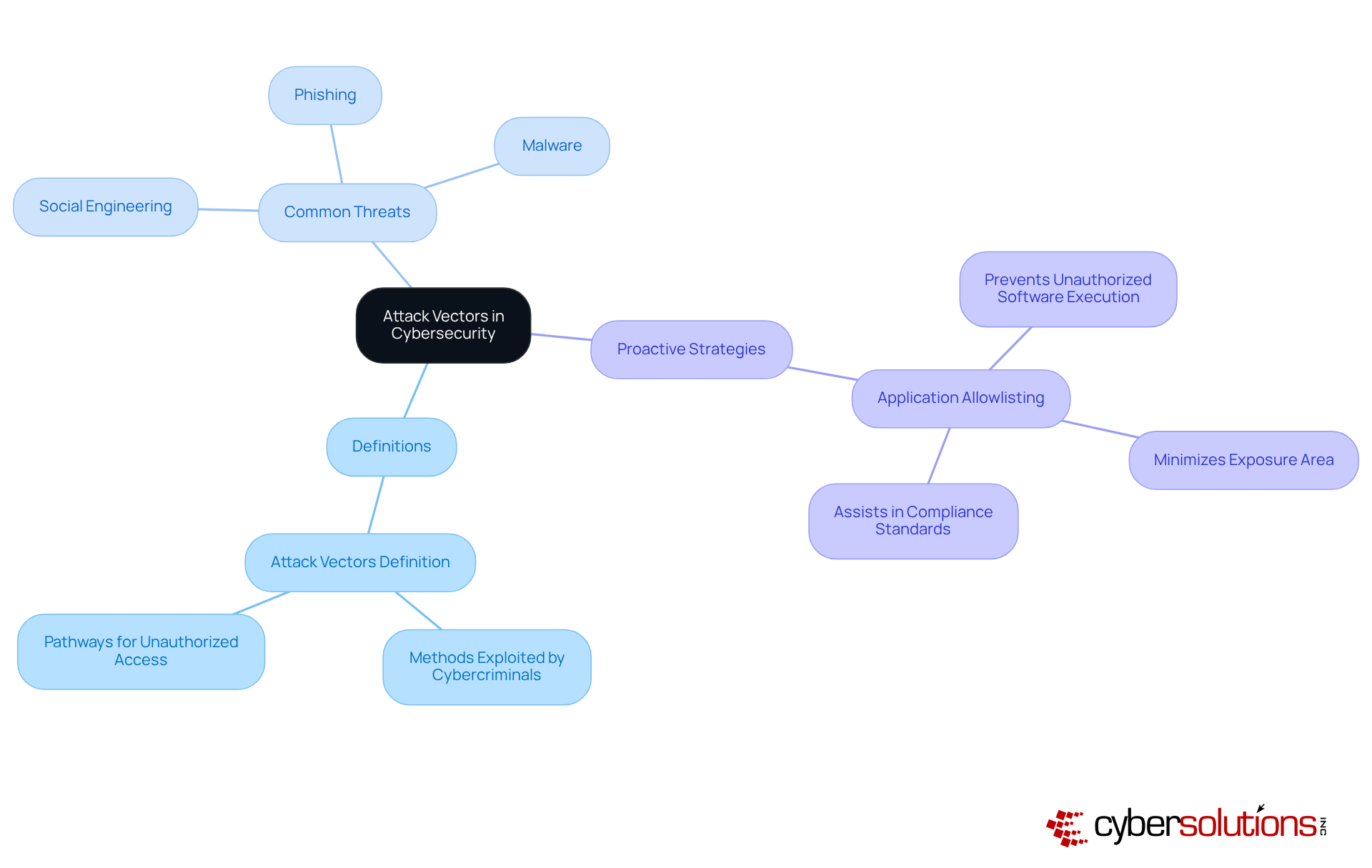
Understanding the concept is crucial in the realm of cybersecurity, particularly for organizations aiming to protect their systems and networks. The term refers to the methods or pathways that cybercriminals exploit to gain unauthorized access. By grasping these vectors, business leaders can identify vulnerabilities within their infrastructure, reinforcing their security posture.
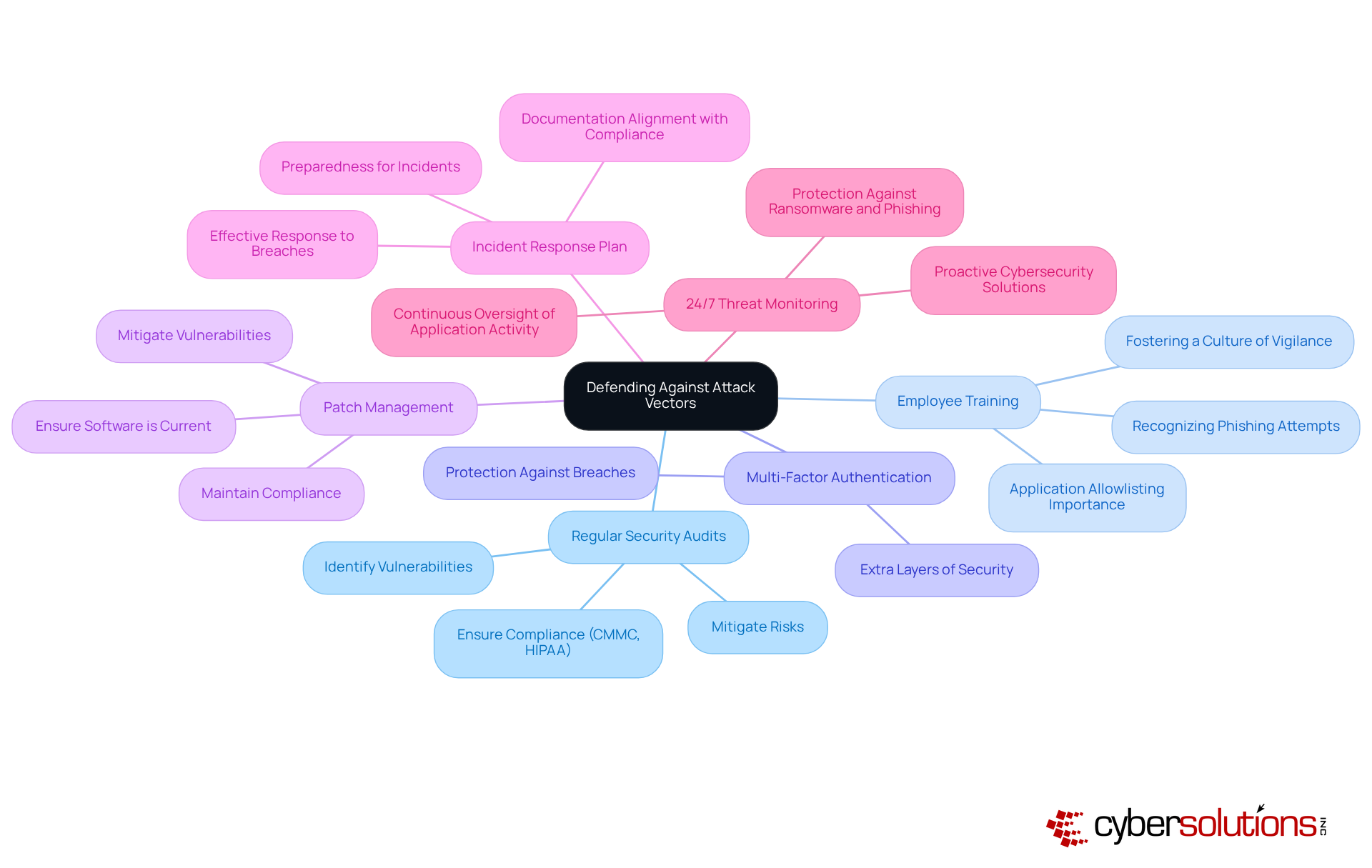
The section encompasses common threats such as phishing, malware, and social engineering, each presenting unique challenges. Recognizing these threats empowers organizations to implement security measures, such as employee training. This proactive measure not only prevents unauthorized software from executing but also minimizes the exposure area, thereby enhancing overall security. Furthermore, it assists in meeting compliance requirements, ensuring that only authorized applications operate within the network.
Incorporating proactive strategies like threat assessments enables organizations to allocate resources efficiently, significantly reducing risks associated with these threat vectors. By staying ahead of potential threats, businesses can safeguard their operations and maintain the trust of their stakeholders.
In today's digital landscape, the importance of cybersecurity cannot be overstated. Organizations face a myriad of threats that threaten their operational integrity and the confidentiality of sensitive information.
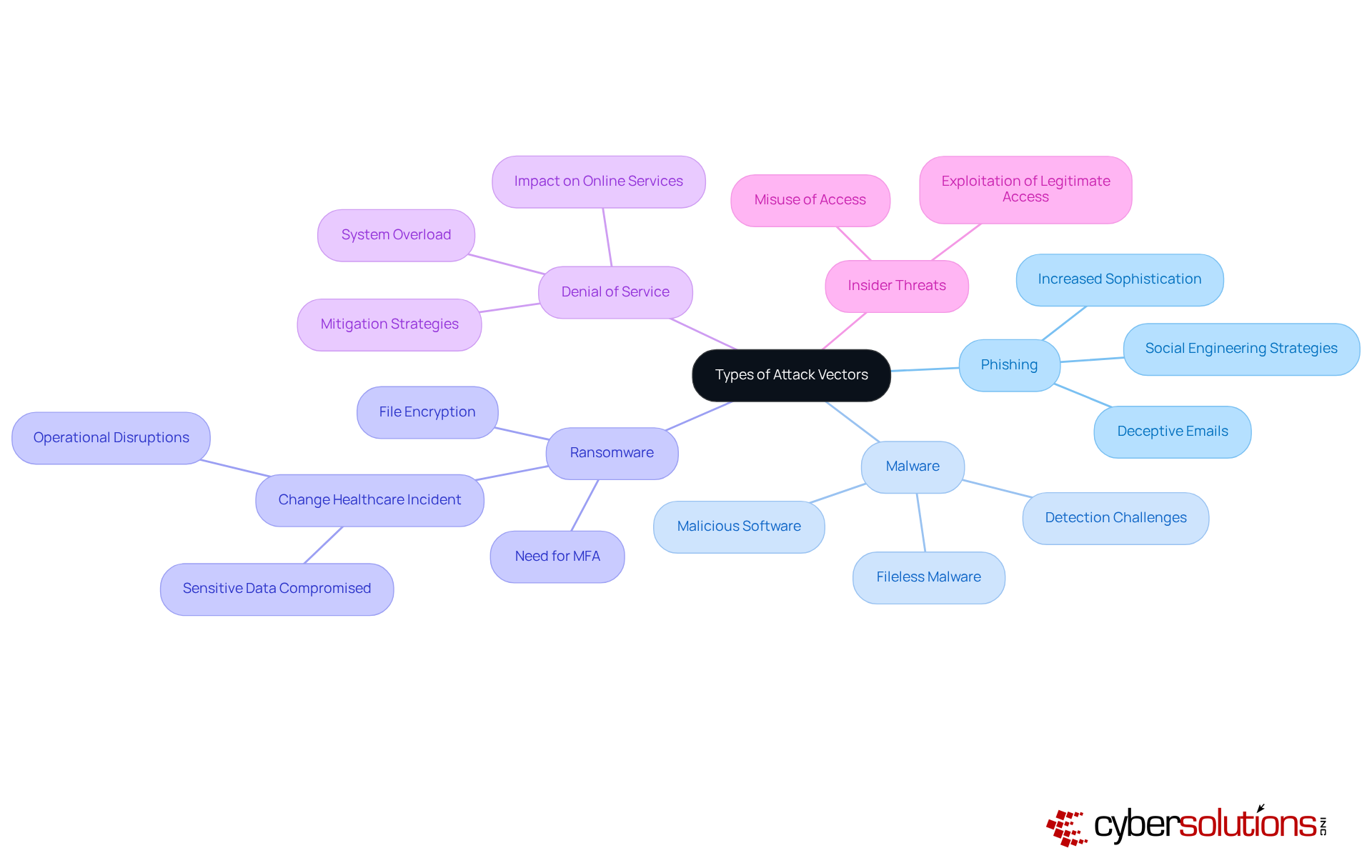
Understanding the types of attack vectors is crucial for organizations to effectively tailor their protective strategies. Experts emphasize that a multi-layered approach, the implementation of security awareness training, and application allowlisting—can significantly reduce the risk of successful intrusions. Application allowlisting, in particular, serves as a gold standard in cybersecurity by preventing unauthorized software from executing, thereby enhancing overall protection and ensuring compliance with regulations.
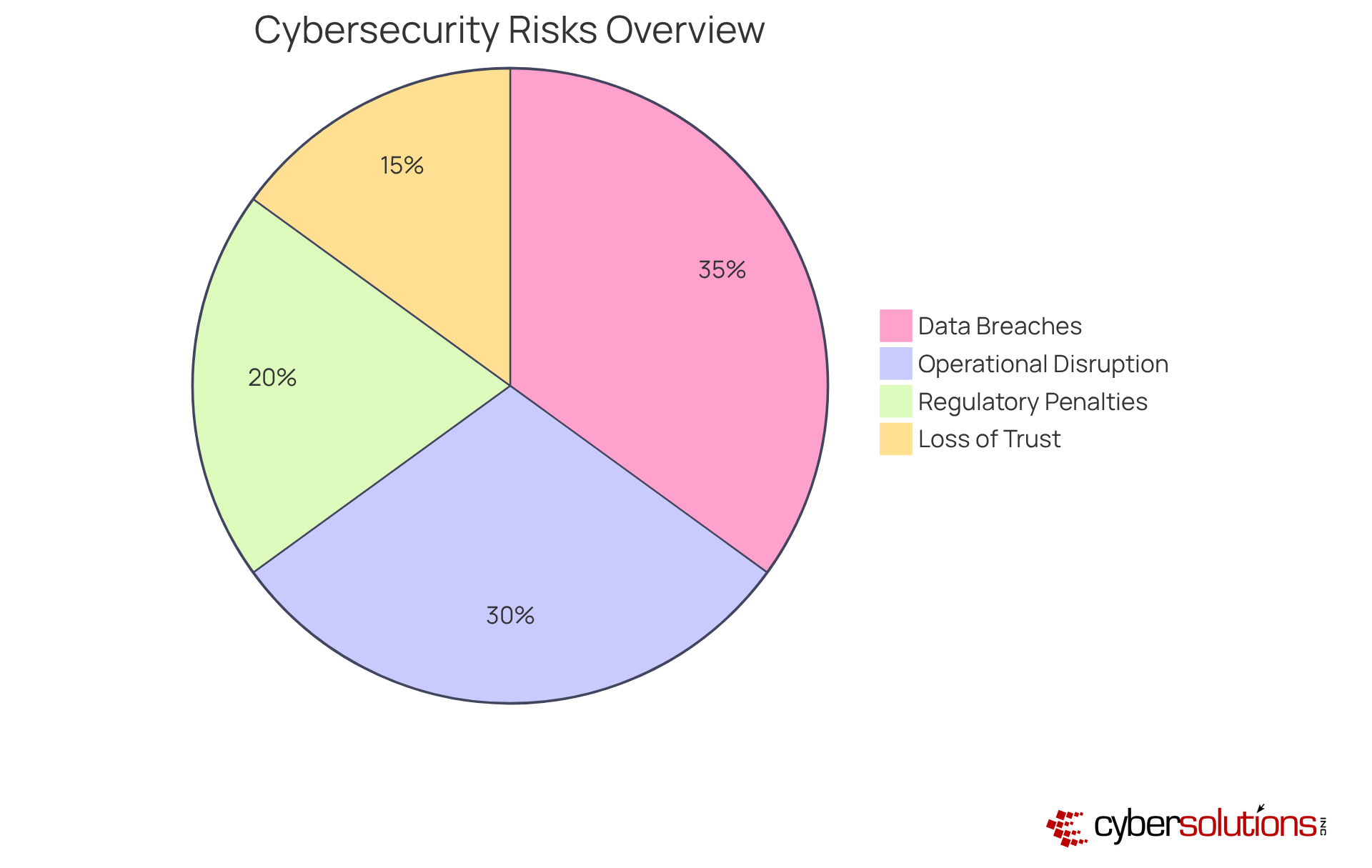
The attack vectors definition highlights the profound impact they have on system security, underscoring the critical need for investment in healthcare. Consider the following significant risks:
Understanding these risks is essential for C-suite leaders, particularly CFOs, to advocate for enhanced security measures. The current landscape of cybersecurity threats demands immediate attention and action.
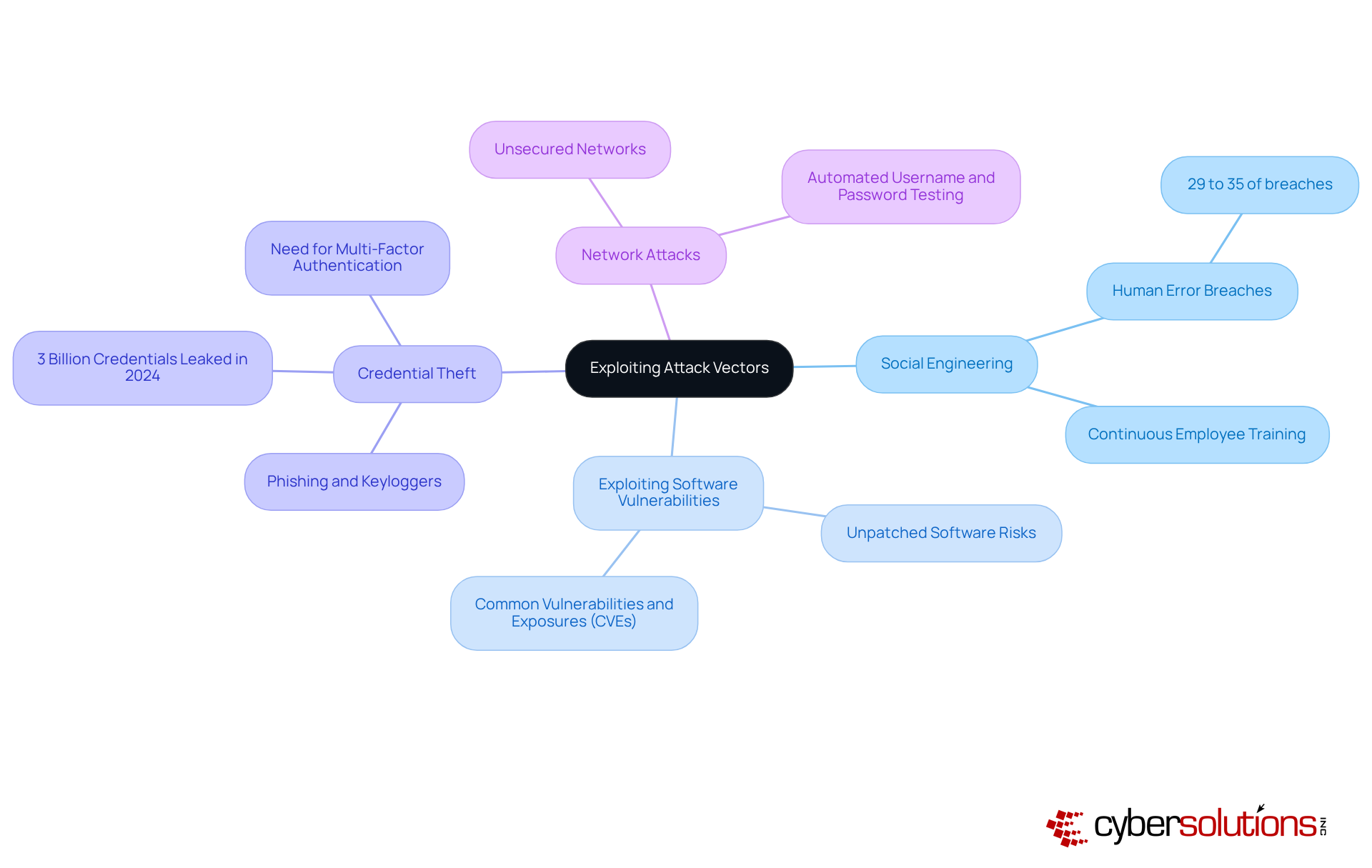
Cybercriminals are increasingly exploiting vulnerabilities through a variety of sophisticated methods that demand urgent attention from organizations, particularly in the healthcare sector. Understanding these tactics is vital for establishing security protocols that can protect sensitive data.
By comprehensively understanding the attack vectors, organizations can implement more robust protective measures to thwart potential breaches. This proactive approach not only safeguards sensitive data but also maintains compliance in an increasingly regulated environment.
In the realm of cybersecurity, understanding the attack vectors is paramount to protecting systems. Attack vectors can be classified into two primary categories: passive and active.
Understanding the differences between passive and active attack vectors is essential for organizations striving to enhance their security posture. For instance, organizations can establish strong monitoring systems to identify unusual network activity suggesting passive intrusions, while also utilizing firewalls to combat active dangers.
As such, a proactive method for recognizing and addressing these threat vectors is crucial for protecting sensitive information and ensuring operational integrity. Organizations that effectively defend against attack vectors not only safeguard their data but also strengthen their overall security framework, ensuring resilience and fostering trust with stakeholders.

In today's digital landscape, the significance of robust cybersecurity measures cannot be overstated, especially within the healthcare sector. Organizations must adopt best practices to defend against an array of attack vectors that threaten sensitive information and operational integrity.
By adopting these best practices, organizations can significantly lower the risk of successful intrusions while ensuring compliance with regulatory standards. The proactive implementation of these strategies not only enhances security but also instills confidence among stakeholders in the organization's commitment to cybersecurity.
Utilizing threat intelligence is crucial for companies seeking to strengthen their security against evolving intrusion methods. As we approach 2025, the landscape of cybersecurity is marked by a notable increase in threats and AI-driven initiatives. Statistics reveal that over 60% of entities reported encountering attacks in the past year, underscoring the importance of staying informed.
To effectively monitor threats, organizations should:
Organizations such as Whitehorse City Council exemplify efficient oversight through their security operations center (SOC), which operates continuously to identify and address risks in real-time. This ongoing vigilance has significantly bolstered their security stance, highlighting the importance of dedicated resources in tackling cyber challenges.
Industry leaders emphasize the necessity of understanding the attack vectors definition within the changing risk landscape. As one specialist noted, "It is crucial to watch for emerging threats; to achieve success, we must first comprehend the changing risk environment." By prioritizing security measures, entities can protect their assets while ensuring compliance, ultimately fostering a more secure digital environment.
Compliance is vital for mitigating risks associated with the attack vectors definition. Organizations must:
By emphasizing adherence, entities not only lower the risk of penalties but also enhance their protections against cyber threats. As regulatory bodies continue to enforce stringent measures, the importance of compliance cannot be overstated.
C-suite executives must cultivate a strategic understanding of the attack vectors to effectively safeguard their enterprises. In today’s rapidly evolving cybersecurity landscape, understanding the threats is not merely an option but a necessity. In fact, a staggering 84% of organizations in 2025 reported a rise in cyber incidents compared to just three years prior, illustrating the critical importance of staying informed about vulnerabilities and sophisticated phishing schemes.
Engaging with cybersecurity experts is paramount to grasping the risks. With executives facing cyber threats at a rate 12 times higher than that of regular employees, the insights gained from professionals can significantly fortify a company's defenses. This collaboration not only enhances understanding of vulnerabilities but also empowers leaders by providing them with the knowledge to make informed decisions regarding their security posture.
Moreover, understanding the implications of attack vectors is essential for integrating cybersecurity into the overall business strategy. Organizations that view cybersecurity as a strategic investment rather than a mere cost center are better positioned to effectively understand the risks and mitigate threats. For instance, 75% of Chief Information Security Officers (CISOs) attribute a reduction in incidents to increased investment in artificial intelligence, underscoring the necessity of incorporating advanced technologies.
By fostering a culture of awareness and proactive engagement, C-suite leaders can better shield their organizations from the ever-evolving landscape of cyber threats.
Understanding the intricacies of attack vectors is vital for C-suite leaders aiming to safeguard their organizations against the ever-evolving landscape of cyber threats. This article has highlighted the critical definitions and implications of various attack vectors, emphasizing their role as pathways exploited by cybercriminals to gain unauthorized access. By grasping these concepts, executives can better identify vulnerabilities within their systems and implement effective strategies to bolster their cybersecurity posture.
Key insights discussed include:
In conclusion, fostering a culture of security awareness and proactive engagement among C-suite leaders is essential in navigating the complexities of cybersecurity. By prioritizing a strategic approach to understanding attack vectors, organizations can not only protect sensitive information but also build trust with stakeholders. The time to act is now; investing in robust cybersecurity measures is not merely a defensive strategy but a fundamental aspect of ensuring long-term business resilience and success.
What services does Cyber Solutions Inc. provide to enhance cybersecurity?
Cyber Solutions Inc. offers a comprehensive suite of cybersecurity services that include 24/7 help desk support, endpoint protection, email safeguards, firewalls, and managed defense services to mitigate various attack vectors.
Why is 24/7 help desk support important in cybersecurity?
The 24/7 help desk support is crucial as it provides prompt assistance during incidents, helping to significantly reduce potential damage and enhance overall business protection.
What are attack vectors in the context of cybersecurity?
Attack vectors refer to the methods or pathways that cybercriminals exploit to gain unauthorized access to systems and networks.
What are some common types of attack vectors?
Common attack vectors include phishing, malware, ransomware, denial of service (DoS) attacks, and insider threats.
How can organizations protect against phishing attacks?
Organizations can protect against phishing attacks by implementing employee training programs that raise awareness about deceptive emails and by utilizing targeted defenses.
What is malware and how does it affect organizations?
Malware is malicious software that disrupts, damages, or gains unauthorized access to systems. Its impact can include operational disruptions and data breaches.
What is ransomware and what are its potential consequences?
Ransomware is a type of malware that encrypts files and demands payment for decryption. Its consequences can include significant operational disruptions and financial losses, as seen in the Change Healthcare incident.
What strategies can organizations employ to mitigate the risk of ransomware?
Organizations can adopt multi-factor authentication (MFA) and develop swift incident response strategies to effectively manage ransomware incidents.
What is the significance of application allowlisting in cybersecurity?
Application allowlisting is a proactive strategy that prevents unauthorized software from executing, thus minimizing exposure to threats and ensuring compliance with regulations.
Why is cybersecurity considered an ongoing process?
Cybersecurity is an ongoing process because it requires continuous oversight and adaptation to emerging challenges, emphasizing the need for a collective responsibility across the organization.
How do managed IT services benefit organizations?
Managed IT services provide a cost-effective alternative to maintaining an in-house team, enabling organizations to allocate resources more efficiently while achieving robust protection against cyber threats.