
In today's world, the stakes are higher than ever when it comes to cybersecurity in healthcare. Organizations are grappling with increasingly sophisticated cyber threats, making the protection of sensitive data a top priority. For CFOs and decision-makers, navigating the complex landscape of cybersecurity pricing models is not just a financial exercise; it’s a strategic imperative. Each model presents unique advantages and challenges that can profoundly influence budget allocations and the overall effectiveness of security measures.
How can healthcare organizations pinpoint the most suitable pricing structure? It’s crucial to find a model that not only addresses immediate security needs but also aligns with long-term strategic goals in an ever-evolving digital environment. The implications of choosing the wrong model can be significant, potentially exposing organizations to greater risks and financial strain.
To effectively tackle these challenges, Cyber Solutions offers tailored approaches that consider both the current threat landscape and the specific needs of healthcare organizations. By leveraging data-driven insights and proven strategies, organizations can enhance their security posture while managing costs effectively. The right pricing model can empower healthcare providers to safeguard sensitive information without compromising their financial stability.
In today's digital landscape, the importance of cybersecurity cannot be overstated, especially for healthcare organizations facing unique challenges. Understanding the various models for cybersecurity services is crucial for making informed investment decisions that protect sensitive data and critical infrastructure.
Typically, organizations allocate 7-12% of their IT budget to digital security, leading to expenditures determined by their specific requirements. For instance, small enterprises often spend between $5,000 and $50,000 annually on cybersecurity, influenced by their size and industry requirements. Understanding pricing models not only aids in budgeting but also ensures that organizations can effectively safeguard their assets against the rising tide of cyber threats.
In today's digital landscape, the significance of robust cybersecurity cannot be overstated, especially for healthcare organizations. As cyber threats continue to evolve, CFOs face unique challenges that demand an investment in security measures. Understanding various pricing models is crucial for organizations to navigate these complexities effectively.
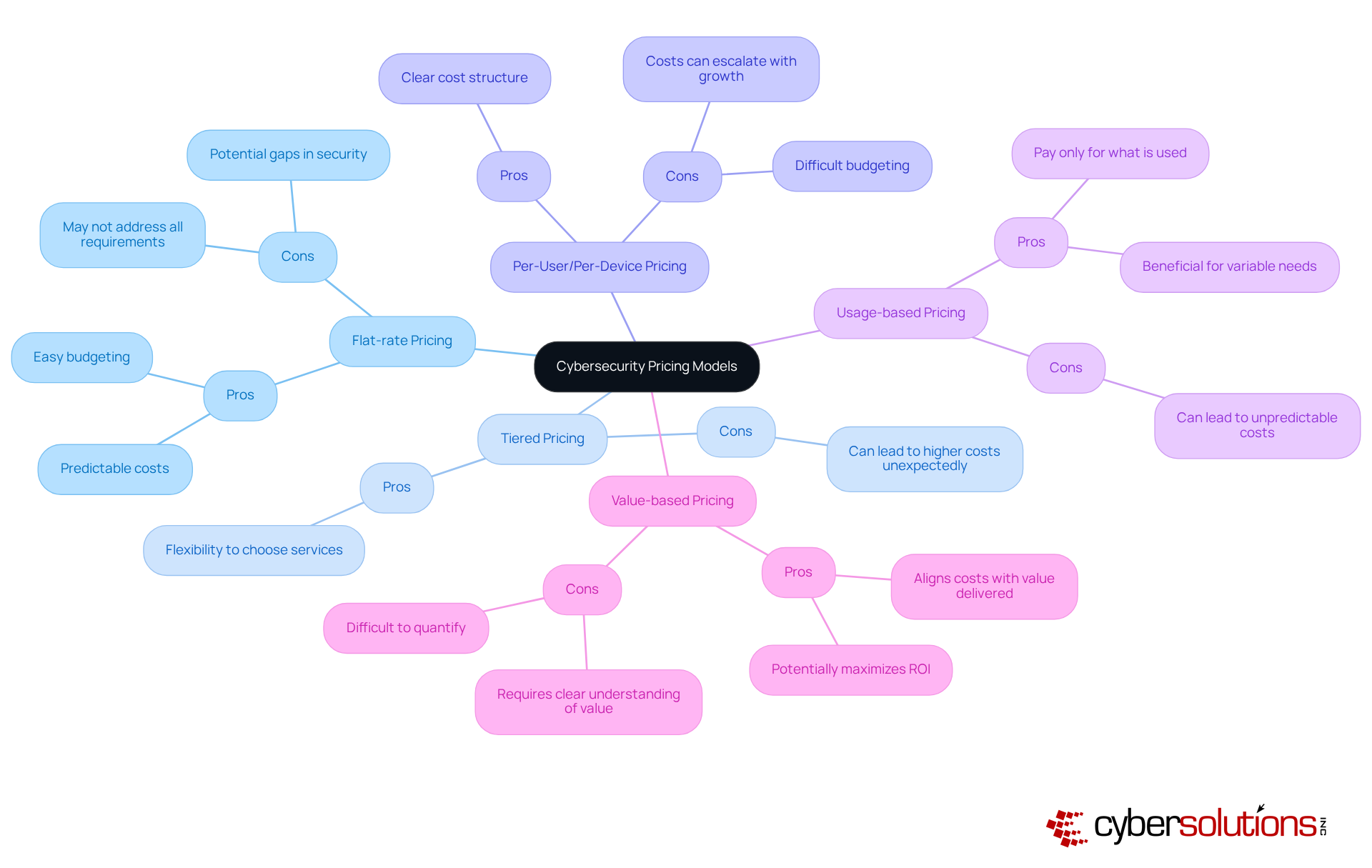
This model is particularly beneficial for small to medium-sized businesses that seek predictable costs. It simplifies budgeting, yet it may not address all specific requirements, potentially leading to gaps in coverage. A flexible option, this model allows entities to select a tier that aligns with their security needs. However, businesses may incur higher costs if they unexpectedly need to upgrade to a more comprehensive tier. In 2025, the adoption of subscription-based models has surged, with many organizations recognizing its adaptability to changing security demands. For example, a medium enterprise that initially chose a lower tier might find itself requiring advanced features, such as proactive monitoring and incident response, as cyber threats escalate, resulting in unplanned expenses. It's essential to acknowledge the financial pressures that can arise from tiered pricing, particularly when considering scalability, as entities may frequently need to enhance their service levels. This approach is advantageous for organizations with a clear understanding of their user base. However, as the entity expands, costs can escalate quickly. Statistics show that average pricing for managed IT services ranges from $30 to $100 per device per month, which can accumulate rapidly for larger teams. Ideal for businesses with fluctuating needs, this model allows payment only for what is used. However, without careful monitoring, it can lead to unpredictable expenses, making robust tracking mechanisms essential. This approach aligns costs with the value delivered, making it suitable for organizations that can quantify the ROI of their security investments. It requires a clear understanding of the value proposition, which can be challenging for some businesses.
Each pricing structure, such as pay-as-you-go, has its advantages and disadvantages, making it vital for companies to evaluate their specific situations and strategic objectives before selecting a pricing framework. By understanding the implications of different models and investing in solutions that enhance efficiency and minimize downtime, like those offered by Cyber Solutions, organizations can manage their security investments more effectively and ensure they are adequately protected against emerging threats.

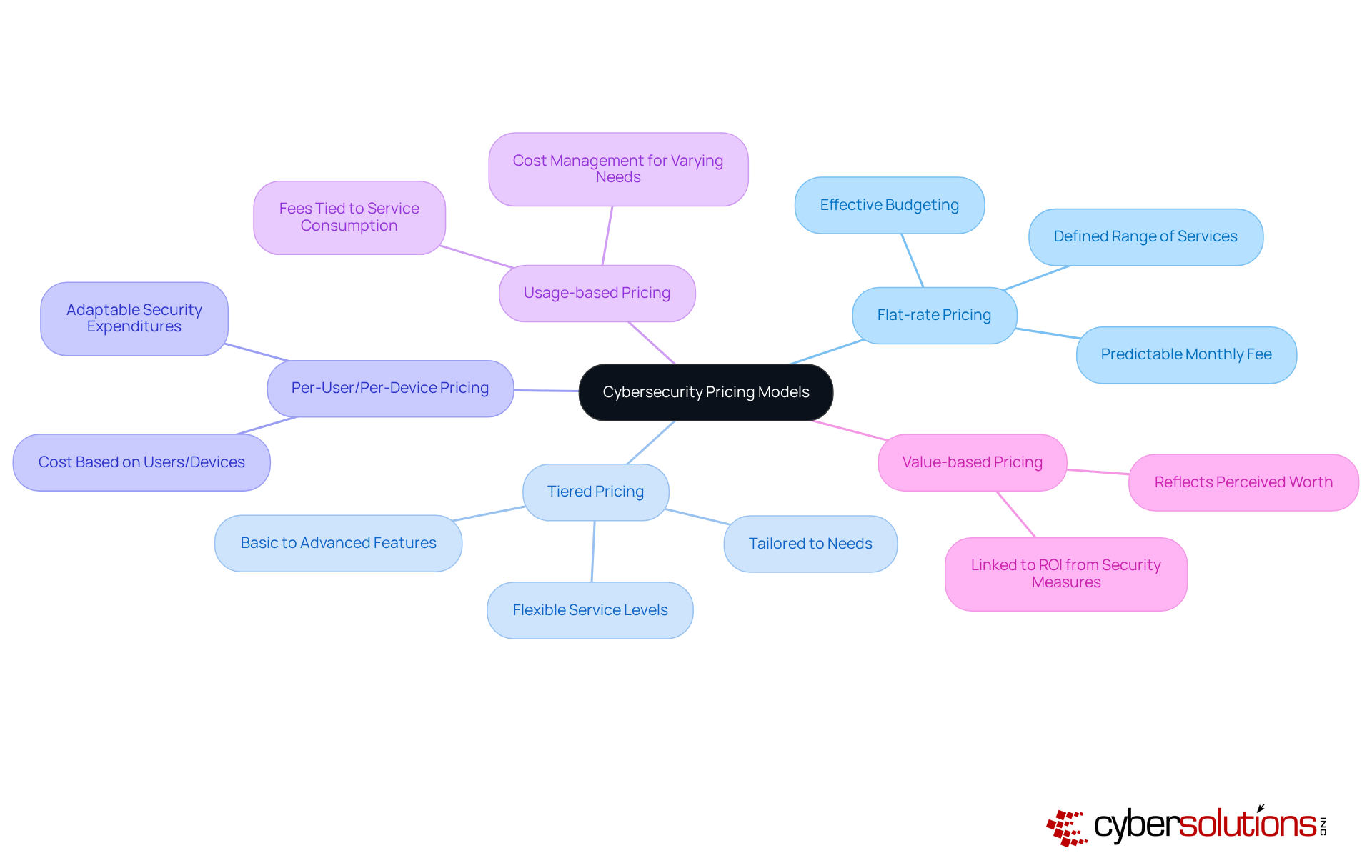
In today's rapidly evolving digital landscape, cybersecurity has become a critical concern for organizations. Understanding the various available pricing models is essential for CFOs to make informed decisions that align with their business goals. Here’s a breakdown of the key pricing models:
Flat-rate Pricing:
Tiered Pricing:
Per-User/Per-Device Pricing:
Usage-based Pricing:
Value-based Pricing:
By comprehending these advantages and disadvantages, organizations can effectively align their investments in cybersecurity with their strategic objectives. This understanding not only aids in budgeting but also ensures that the chosen cybersecurity measures adequately protect against the unique threats faced in the healthcare sector.
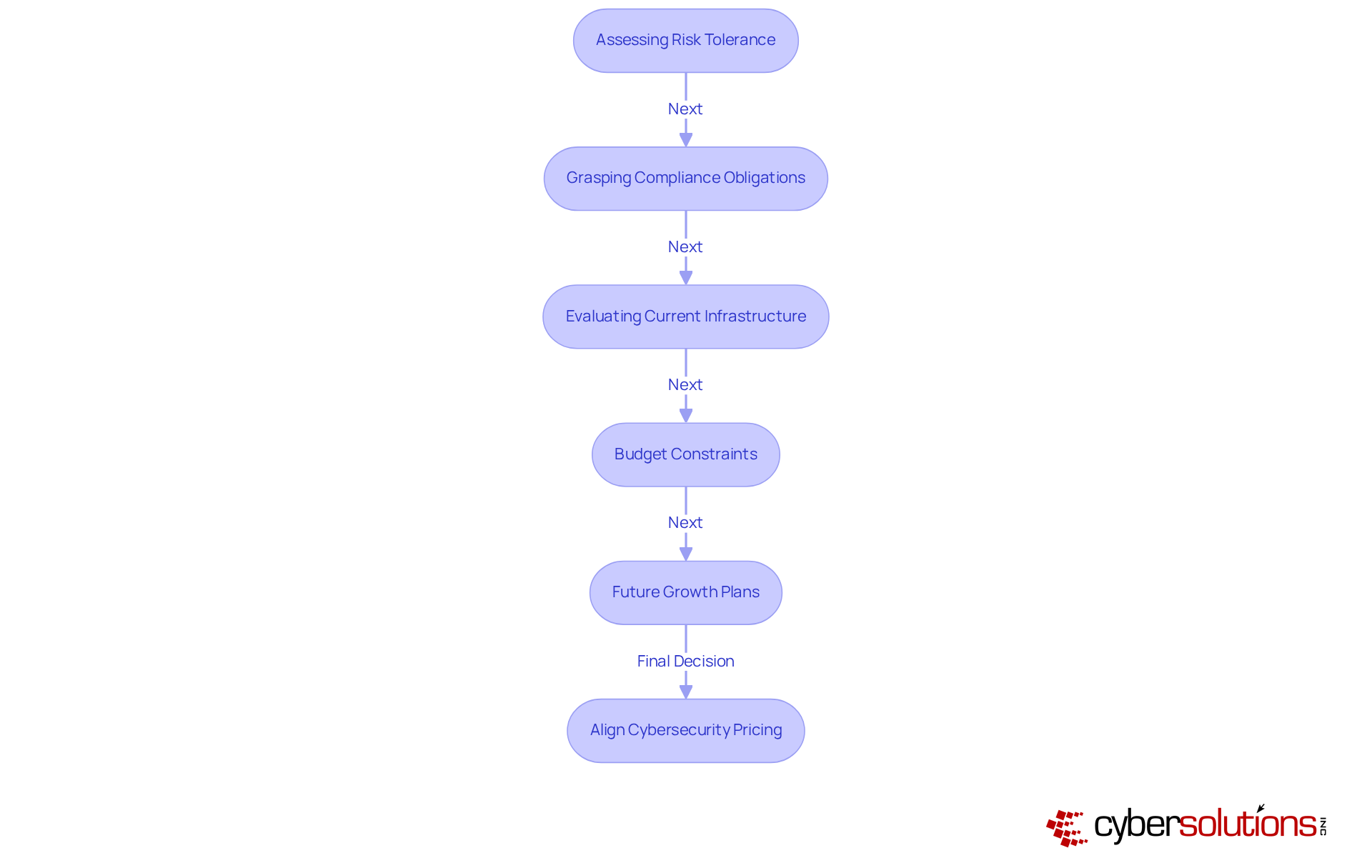
Aligning cyber security pricing with organizational needs is not just a strategic choice; it’s a necessity in today’s digital landscape. Organizations face a myriad of threats that can jeopardize their operations and reputation. Understanding how to effectively align cyber security pricing with these needs is crucial for decision-makers.
By carefully considering these factors, organizations can select a pricing model that not only meets their current needs but also supports their long-term objectives, ensuring resilience against evolving cyber threats.
Understanding the complexities of cybersecurity pricing models is crucial for organizations aiming to safeguard their assets in a rapidly evolving digital landscape. As threats become more sophisticated, decision-makers must evaluate various pricing structures - flat-rate, tiered, per-user/per-device, usage-based, and value-based - to tailor their investments effectively. This strategic alignment not only addresses current needs but also positions organizations for future growth.
Each pricing model presents unique advantages and challenges.
The importance of selecting the right cybersecurity pricing model cannot be overstated. Organizations must carefully assess their risk tolerance, compliance obligations, existing infrastructure, budget constraints, and future growth plans to make informed decisions. By aligning cybersecurity investments with strategic objectives, businesses can bolster their resilience against evolving threats and ensure robust protection for sensitive data. A thoughtful approach to cybersecurity pricing not only safeguards assets but also positions organizations for sustained success in a digital-first world.
Why is understanding cybersecurity pricing models important for organizations, especially in healthcare?
Understanding cybersecurity pricing models is crucial for making informed investment decisions that protect sensitive data and maintain compliance, particularly for healthcare organizations facing unique challenges.
What is flat-rate pricing in cybersecurity?
Flat-rate pricing offers a predictable monthly fee that encompasses a defined range of services, allowing organizations to budget effectively and avoid unexpected costs.
How does tiered pricing work in cybersecurity services?
Tiered pricing provides flexibility by enabling organizations to select from multiple service levels tailored to their specific needs and budgets, ranging from basic protections to advanced features like incident response and compliance support.
What is per-user/per-device pricing?
Per-user/per-device pricing calculates costs based on the number of users or devices being secured, making it beneficial for organizations with fluctuating personnel levels.
What is usage-based pricing in cybersecurity?
Usage-based pricing ties fees to actual service consumption, making it suitable for organizations with varying security needs and helping manage costs effectively.
What does value-based pricing reflect in cybersecurity services?
Value-based pricing reflects the perceived worth of the service to the client and is often linked to the potential return on investment from enhanced security measures.
How much of their IT budget do organizations typically allocate to cybersecurity?
Organizations typically allocate 7-12% of their IT budget to digital security, leading to significant annual expenses determined by cybersecurity pricing.
What are the typical annual cybersecurity expenses for small enterprises?
Small enterprises often spend between $5,000 and $50,000 annually on cybersecurity, influenced by their size and industry requirements.