
In today's digital landscape, small businesses are facing an alarming surge in cyber threats, particularly ransomware attacks that can devastate operations and compromise sensitive data. The stakes have never been higher; statistics show that countless organizations have fallen victim to endpoint breaches, underscoring the urgent need for robust protection strategies.
This article explores ten essential tactics that small enterprises can implement to strengthen their defenses against ransomware. It emphasizes not only the necessity of proactive measures but also the critical vulnerabilities that many organizations still overlook.
How ready is your business to tackle these ever-evolving threats?
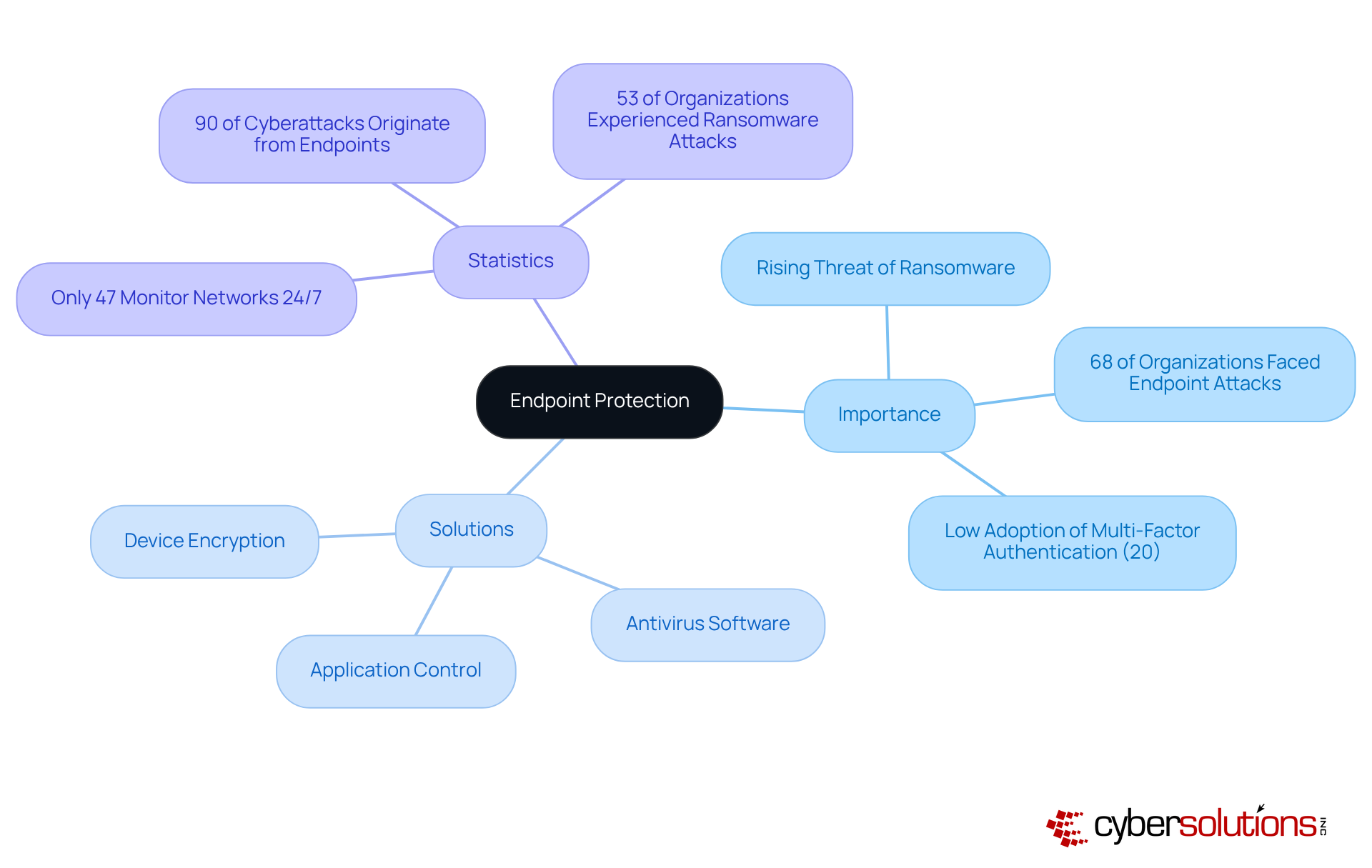
Endpoint protection is not just important; it's essential for small enterprises aiming to defend against the threat of ransomware. Did you know that 60% of small businesses that experience a cyber attack go out of business within six months? This alarming statistic underscores the necessity of implementing robust security measures.
Cyber Solutions Inc. stands ready to provide advanced cybersecurity solutions tailored specifically for small businesses. Our offerings include:
All designed to meet your unique needs. These solutions enable early identification and response to threats, before breaches can occur. Regular updates and continuous monitoring are crucial to maintaining the effectiveness of your defenses against ever-evolving threats.
Currently, only 30% of small businesses have a formal cybersecurity plan in place, highlighting a significant gap in security measures. By prioritizing cybersecurity training, organizations can dramatically reduce their vulnerability to malicious software. This proactive approach not only ensures business continuity but also protects your bottom line. Don't wait for an attack to happen - take action now to secure your business's future.
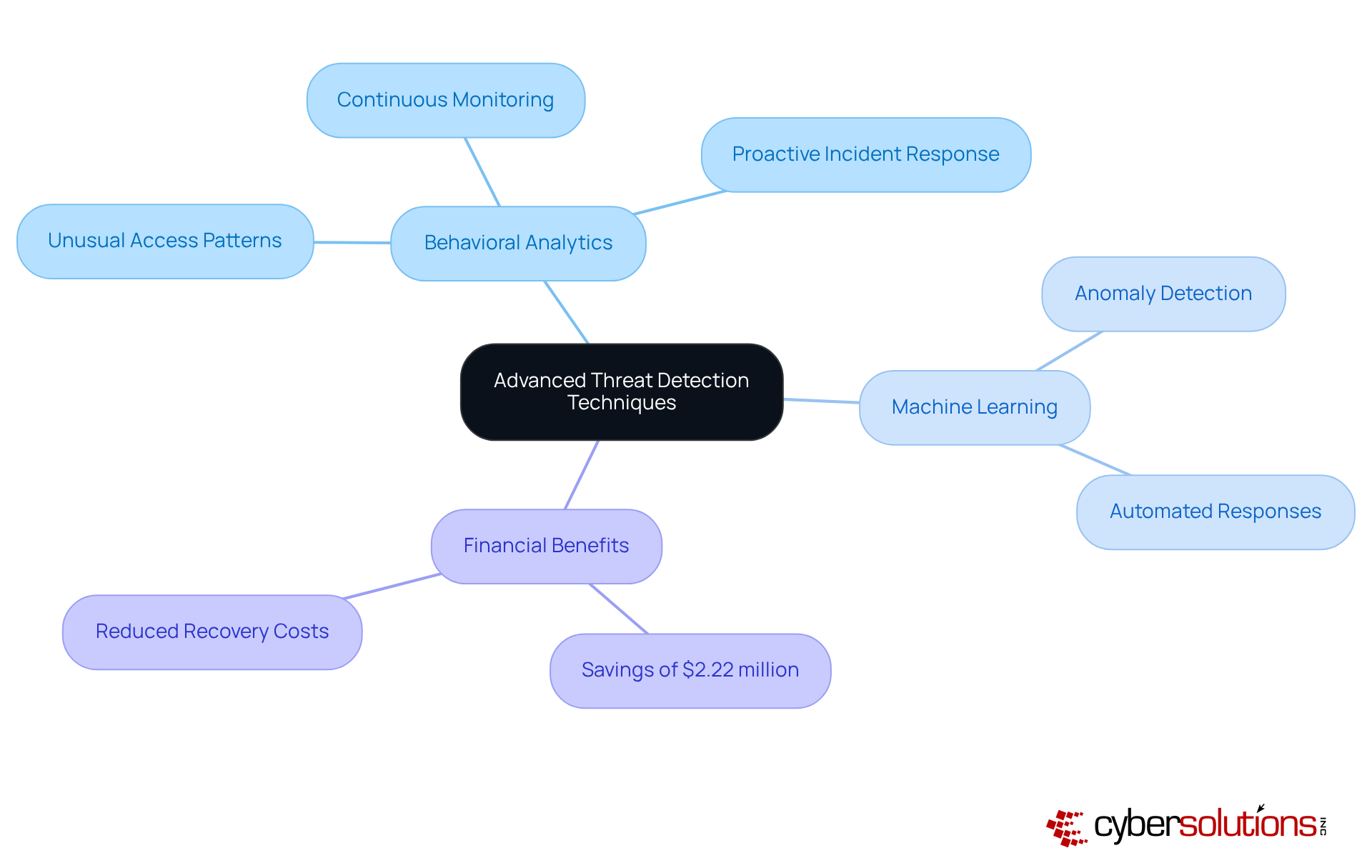
In today's digital landscape, the importance of cybersecurity cannot be overstated, especially in the healthcare sector. With the rise of cyber threats, small enterprises must adopt advanced technologies, such as artificial intelligence and machine learning, to bolster their defenses against such attacks. These technologies enable organizations to continuously monitor network traffic and user behavior, swiftly identifying anomalies that may signal an impending attack.
For example, threat detection systems can flag unusual access patterns, like accessing sensitive financial data at odd hours, as highly suspicious. This proactive strategy not only enhances the ability to respond to potential risks from small business ransomware but also significantly reduces damage and recovery costs. In fact, recent findings reveal that organizations leveraging AI and automation in their security measures have saved an average of $2.22 million in breach costs. This underscores the importance of adopting advanced threat detection techniques.
As cybersecurity evolves, incorporating advanced technologies into security protocols is becoming essential for early detection and effective response. This approach empowers organizations to stay ahead of potential risks. Case studies further support this, demonstrating how quick response and a structured strategy can improve cybersecurity, particularly in industries like healthcare. Here, prompt action and specialized knowledge are crucial in mitigating the effects of cyberattacks.
In conclusion, the integration of advanced threat detection is not just a technical upgrade; it's a vital step toward enhancing security and ensuring the resilience of healthcare organizations against the ever-growing threat of cybercrime.
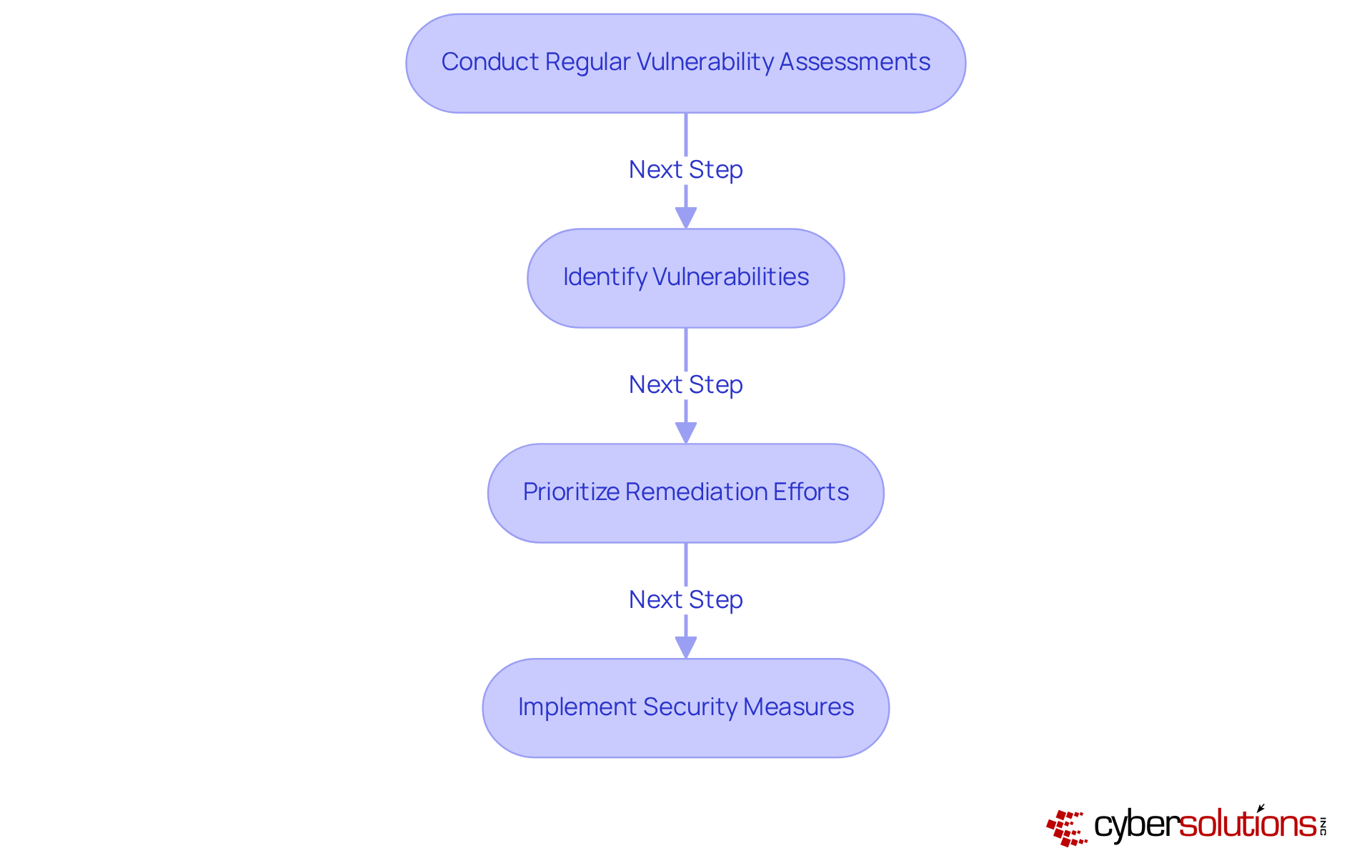
Routine assessments are crucial for small enterprises aiming to identify vulnerabilities that could be exploited by attackers. Did you know that over 86% of small and medium-sized enterprises have conducted a vulnerability assessment? Yet, many still struggle with effectively managing vulnerabilities. Cyber Solutions Inc. offers comprehensive services tailored to evaluate the security posture. By systematically identifying vulnerabilities and prioritizing remediation efforts, organizations can significantly reduce their risk of attacks.
Cybersecurity professionals stress that without regular assessments, organizations remain vulnerable to potential breaches, which can lead to devastating financial and reputational damage. Real-world examples demonstrate that organizations not only enhance their security stance but also build trust with clients by showcasing their commitment to data protection. As the landscape of cyber threats evolves, adopting a proactive approach is essential for safeguarding sensitive information.
In conclusion, conducting regular assessments is not just a precaution; it's a strategic move that can safeguard your organization against the ever-changing threats in the cyber landscape.
A successful incident response plan is essential for small enterprises to effectively combat ransomware. Cyber Solutions Inc. specializes in assisting organizations in developing strategies during a crisis. This involves:
Regular testing and updates to the plan are vital; however, many businesses lack preparedness, leaving a staggering 86% vulnerable to potential breaches.
By proactively preparing and consistently enhancing their incident response plans, small businesses can significantly mitigate the impact of cyber attacks. It's time for these organizations to take action and safeguard their operations against the ever-evolving landscape of cyber threats.
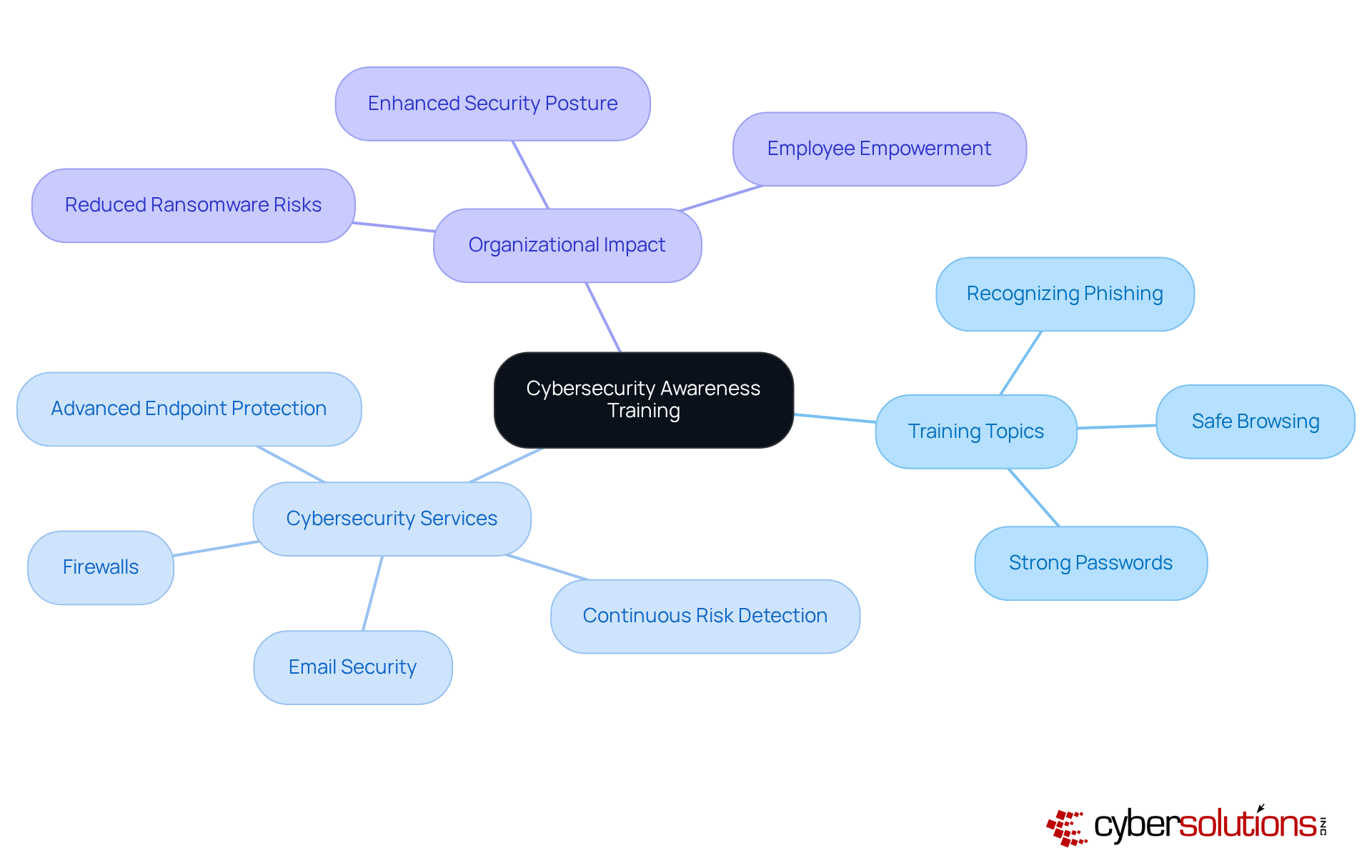
In today's digital landscape, training employees on cybersecurity awareness stands as one of the most effective strategies to thwart cyber threats. Cyber Solutions Inc. offers tailored training programs designed to equip staff with the skills to recognize phishing attempts, practice safe browsing, and understand the importance of cybersecurity.
But training is just the beginning. Cyber Solutions also provides a comprehensive training program, including:
By fostering a culture of security and empowering employees with the knowledge to identify potential threats, organizations can transform their workforce into a formidable first line of defense against cyber risks.
Moreover, with advanced monitoring tools, Cyber Solutions ensures that any suspicious activities are swiftly detected and addressed, significantly enhancing the overall security posture of the organization. In an era where cyber threats are ever-evolving, can your organization afford to overlook the importance of cybersecurity training?
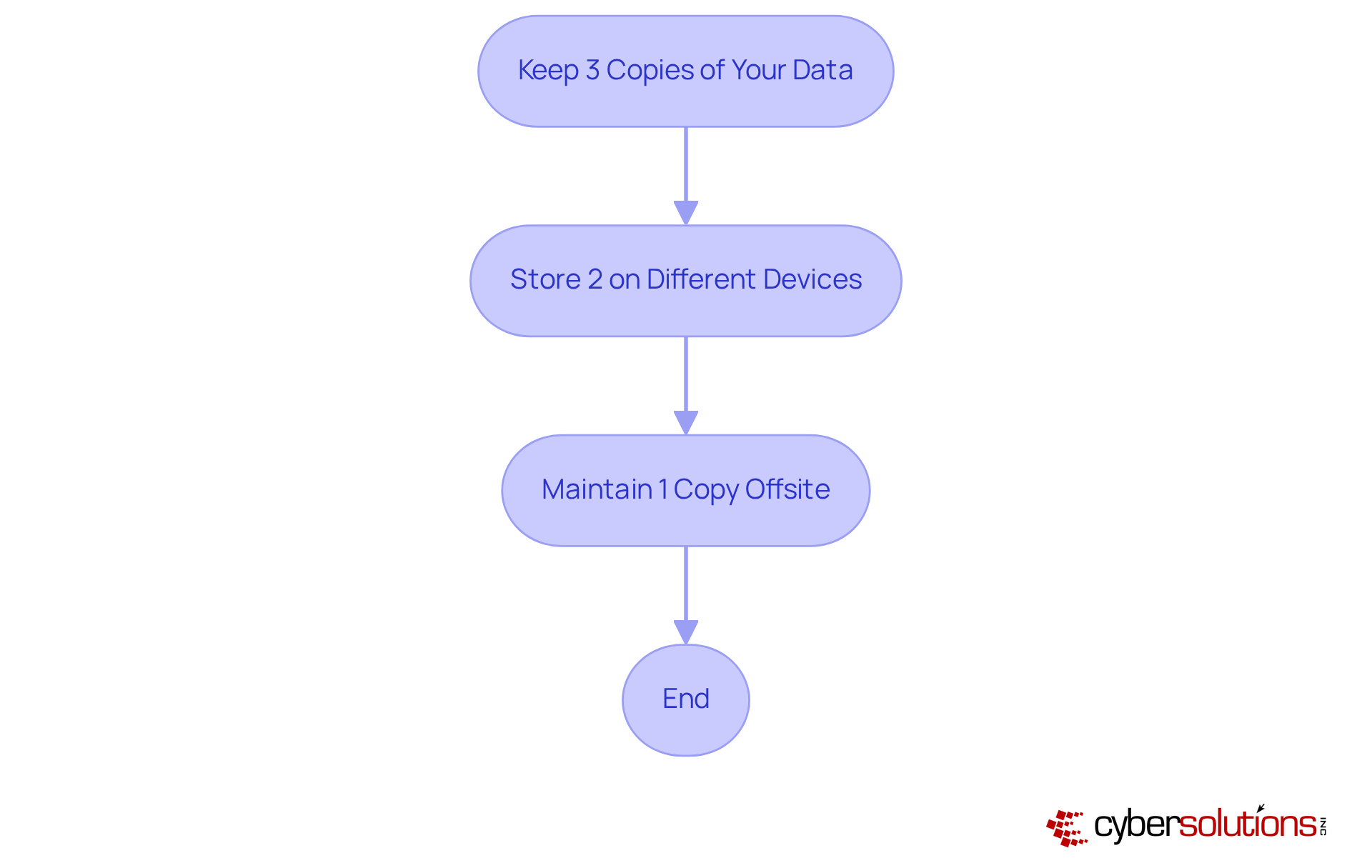
Establishing regular protocols is crucial for minor enterprises aiming to recover swiftly from ransomware attacks. The 3-2-1 strategy stands out as a highly recommended approach:
This method not only protects against data loss but also facilitates recovery, significantly minimizing downtime during an attack.
Despite its effectiveness, research reveals that many organizations are not implementing this strategy, exposing a significant gap in preparedness. Experts warn that overlooking regular backups can lead to disaster, as many organizations find their backup data inaccessible only after a breach occurs.
Real-world applications of the 3-2-1 strategy demonstrate its resilience. For instance, organizations across local disks, cloud services, and physical media reported improved recovery times. A recent case involving Cyber Solutions showcased their rapid response, restoring 4,500 endpoints for a healthcare provider, underscoring how the 3-2-1 strategy was pivotal in their recovery process.
By adopting this proactive approach, minor enterprises can fortify their defenses against the escalating threat of ransomware. Are you prepared to safeguard your organization? The time to act is now.
In today's digital landscape, ensuring adherence to cybersecurity regulations is not just important - it's essential for small enterprises to avoid breaches, protect sensitive information, and avoid legal penalties. Cyber Solutions Inc. stands out by simplifying this process through its compliance offerings. These services encompass:
By implementing necessary policies and conducting regular assessments, organizations can effectively align their cybersecurity practices with regulatory requirements. This alignment not only enhances their overall security posture but also significantly reduces the risk of attacks from small business ransomware. Have you considered how a robust compliance strategy could safeguard your organization?
Moreover, our CaaS solutions provide vital support for audit preparation, ensuring that organizations are well-equipped to meet and mitigate potential penalties. With Cyber Solutions Inc. at your side, you can navigate compliance with confidence, knowing that your compliance needs are in expert hands.

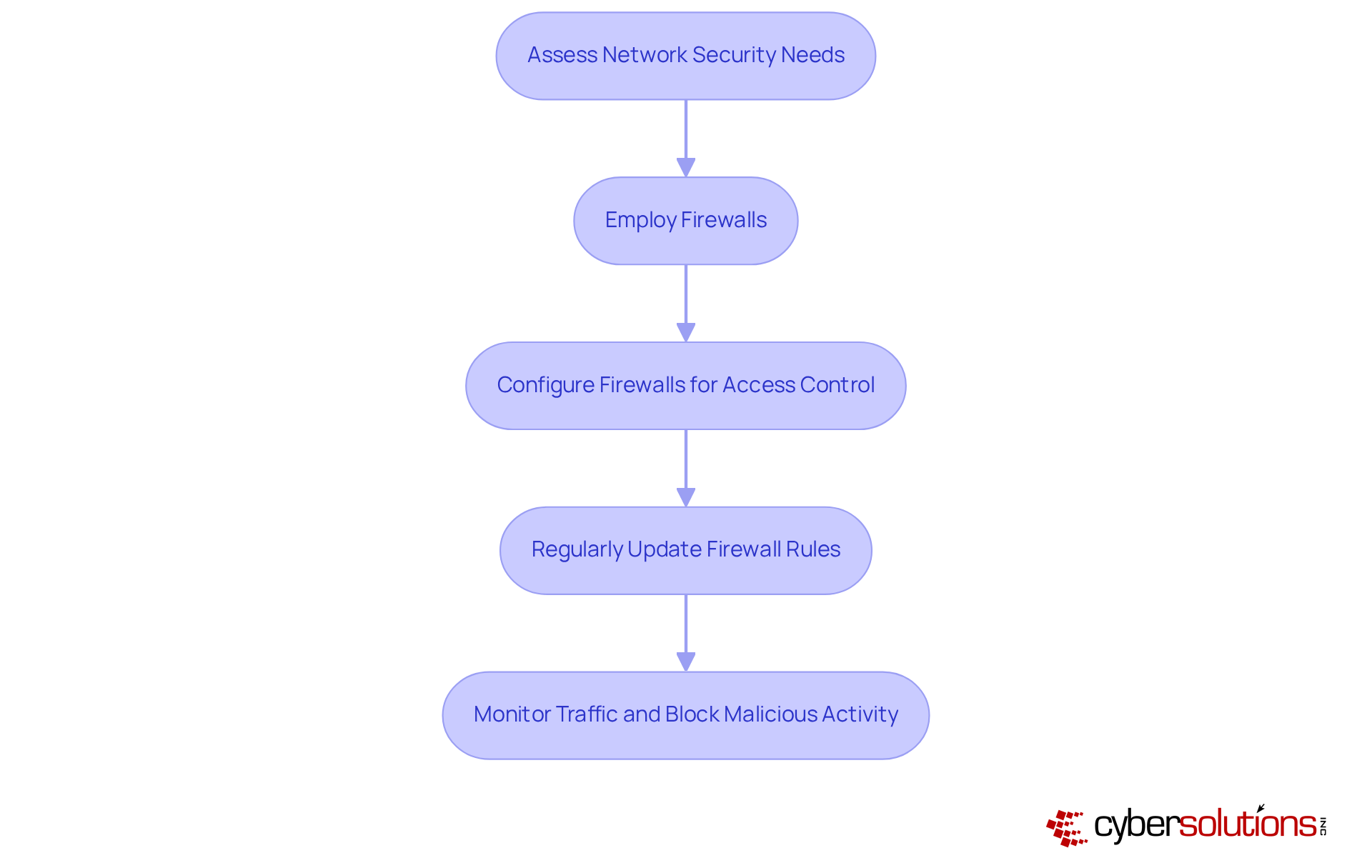
In today's digital landscape, safeguarding enterprise networks is more critical than ever. Cybersecurity threats are rampant, and organizations must take proactive measures. Employing firewalls is essential for defending minor enterprise networks against unauthorized access and potential malware attacks.
Cyber Solutions offers solutions that not only monitor but also filter incoming and outgoing traffic, effectively blocking malicious activity. By configuring firewalls to enforce strict policies and regularly updating firewall rules, organizations can significantly reduce their risk of cyber incidents. This not only protects assets but also fosters trust among clients and stakeholders.
Consider the implications: without proper firewall protection, organizations expose themselves to significant vulnerabilities. Cyber Solutions stands ready to address these challenges, ensuring that your network remains secure against evolving threats. Don't leave your cybersecurity to chance—take action today to fortify your defenses.
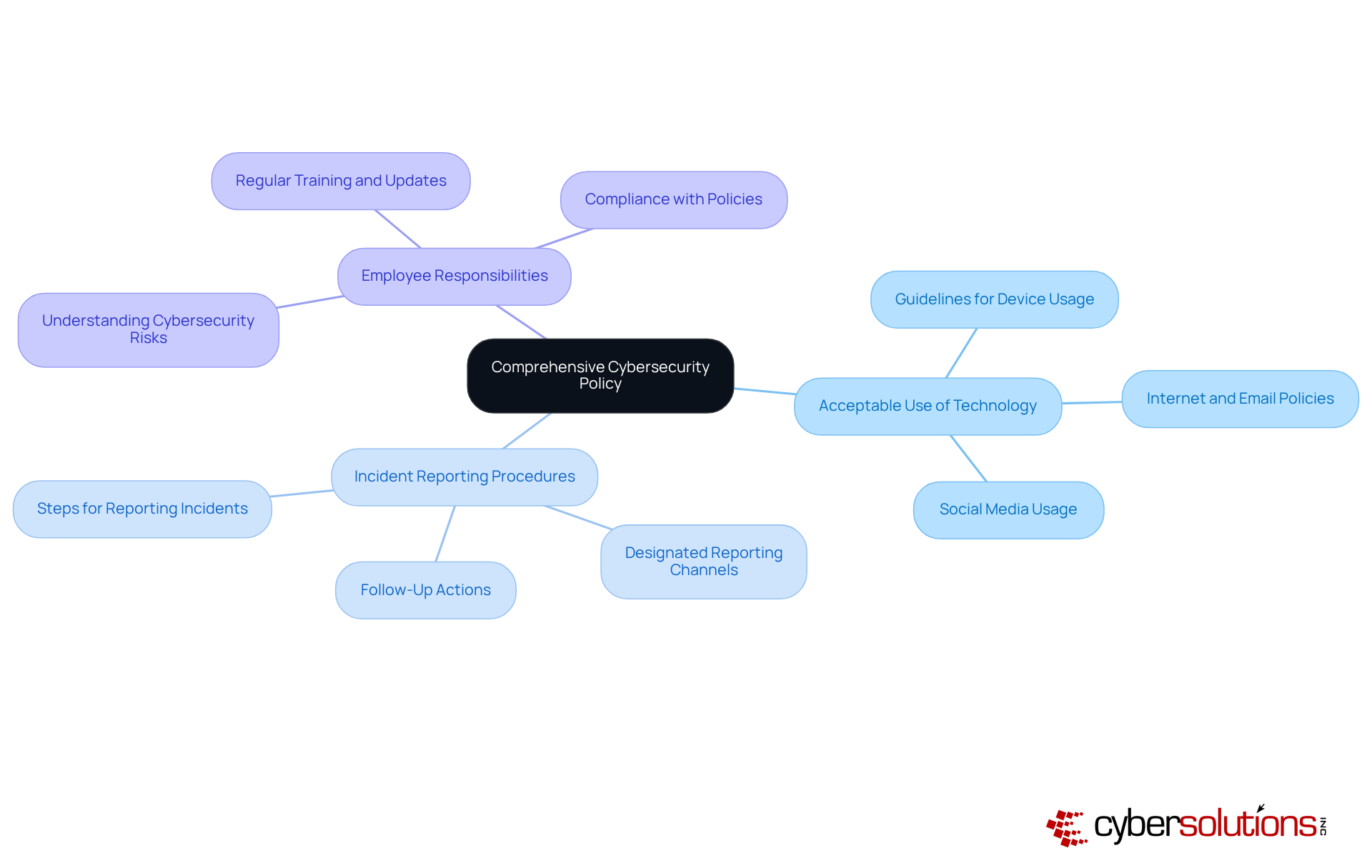
Establishing a robust cybersecurity policy is essential for small businesses to protect against threats by setting clear guidelines and expectations for their staff. In an era where cyber threats are increasingly sophisticated, Cyber Solutions Inc. specializes in developing tailored strategies that specifically address unique risks and compliance requirements.
Such a policy should encompass:
This ensures that every team member understands their role in maintaining security. Research indicates that organizations with well-defined policies are significantly better equipped to mitigate risks. For instance, 76% of small enterprises that increased their cybersecurity investments reported heightened concerns over threats, underscoring the urgent need for strong policies.
Real-world examples further illustrate that organizations implementing comprehensive policies have effectively reduced their vulnerability to ransomware. This highlights the critical importance of cybersecurity measures in today’s digital landscape. By partnering with Cyber Solutions Inc., small enterprises can fortify their defenses against attacks and navigate the complexities of cybersecurity with confidence.
In today's digital landscape, cybersecurity is not just an option for small enterprises; it's a necessity. Collaborating with a managed security service provider like Cyber Solutions Inc. can significantly enhance your organization's security posture. With extensive services that include threat analysis, risk detection, and incident response, Cyber Solutions ensures that your business is well-equipped to face evolving cyber threats.
Consider the unique challenges that small enterprises face in cybersecurity. Cyber Solutions offers solutions such as:
These services are designed to protect organizations against the increasing risks of ransomware and other cyber threats. By leveraging the expertise of Cyber Solutions, businesses can access tools and resources that might otherwise be beyond their budget.
Why risk your organization's security when you can partner with experts who understand the cybersecurity landscape? With Cyber Solutions, you gain not only robust protection but also peace of mind, knowing that your cybersecurity needs are in capable hands. Don't wait for a breach to occur; take action now to secure your enterprise's future.
In today's digital landscape, the escalating threat of ransomware demands that small businesses prioritize comprehensive cybersecurity strategies. Protecting sensitive data and maintaining operational integrity is not just advisable; it's essential. By implementing effective measures - such as endpoint protection, advanced threat detection, and regular vulnerability assessments - businesses can significantly reduce their risk of falling victim to cyberattacks. The proactive steps outlined here serve as a crucial roadmap for small enterprises aiming to bolster their defenses against the ever-evolving landscape of cyber threats.
Key strategies include:
Each of these elements is vital in creating a resilient cybersecurity posture that safeguards valuable information and fosters trust with clients and stakeholders. Moreover, leveraging partnerships with managed security service providers can enhance the security capabilities of small businesses, granting access to advanced technologies and expertise that may otherwise be out of reach.
Ultimately, the responsibility of protecting an organization from ransomware lies with its leadership. By taking decisive action today - whether through investing in cybersecurity training, implementing regular data backups, or establishing comprehensive cybersecurity policies - small businesses can mitigate risks and secure their future. The time to act is now; the safety and success of your organization depend on it.
Why is endpoint protection essential for small enterprises?
Endpoint protection is essential for small enterprises to defend against the rising tide of ransomware attacks. Statistics show that 68% of organizations have faced endpoint attacks that compromised their data, highlighting the need for robust protection measures.
What solutions does Cyber Solutions Inc. offer for endpoint protection?
Cyber Solutions Inc. offers advanced endpoint protection solutions tailored for small businesses, including antivirus software, application control, and device encryption. These solutions help in early identification and response to threats, safeguarding sensitive data.
What is the importance of regular updates and monitoring in endpoint protection?
Regular updates and continuous monitoring are crucial to maintaining the effectiveness of endpoint protection against ever-evolving threats, ensuring that organizations can respond promptly to new vulnerabilities.
What percentage of small enterprises have adopted multi-factor authentication?
Currently, only 20% of small enterprises have adopted multi-factor authentication, indicating a significant gap in security measures.
How can advanced threat detection techniques benefit small enterprises?
Advanced threat detection techniques, such as behavioral analytics and machine learning, help small enterprises continuously monitor network traffic and user behavior, swiftly identifying anomalies that may signal an impending attack.
What financial benefits can organizations see from leveraging AI and automation in security measures?
Organizations that leverage AI and automation in their security measures have saved an average of $2.22 million in breach costs, highlighting the financial benefits of adopting such technologies.
Why are routine vulnerability assessments important for small enterprises?
Routine vulnerability assessments are crucial for proactively identifying and addressing security flaws that could be exploited by ransomware. They help organizations reduce their risk of attacks and manage vulnerabilities effectively.
What percentage of small and medium-sized enterprises have conducted a cybersecurity risk assessment?
Over 86% of small and medium-sized enterprises have conducted a cybersecurity risk assessment, although many still struggle with effectively managing vulnerabilities.
How do regular vulnerability evaluations enhance an organization's security stance?
Regular vulnerability evaluations enhance an organization's security stance by systematically identifying vulnerabilities and prioritizing remediation efforts, which can significantly reduce the risk of ransomware attacks.
What is the strategic importance of investing in routine vulnerability assessments?
Investing in routine vulnerability assessments is a strategic move that safeguards organizations against the changing threats in the cyber landscape and builds trust with clients by demonstrating a commitment to data protection.