
In today's world, where data breaches and cyber threats are alarmingly prevalent, organizations are confronted with the critical challenge of protecting their vital information. This article explores essential best practices for Managed Service Providers (MSPs) to bolster their backup and recovery strategies. By doing so, they not only safeguard data but also ensure compliance with rigorous regulatory standards. Yet, many organizations still lack effective disaster management plans. This raises a pivotal question: how can businesses adeptly navigate the complexities of backup and recovery to mitigate risks and maintain operational continuity?
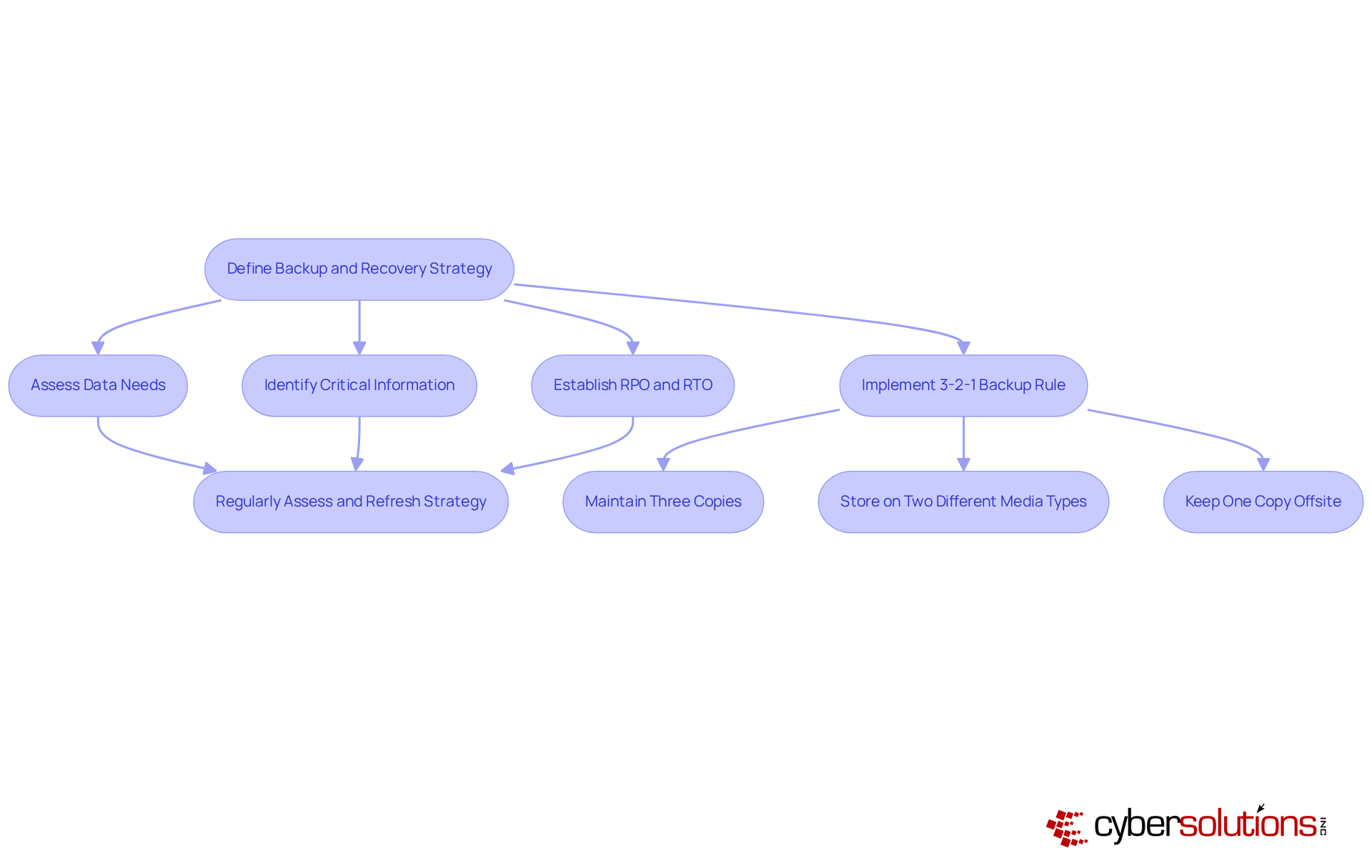
A well-defined plan for preservation and restoration is crucial for organizations. In today’s landscape, where data breaches are rampant, organizations must assess their data needs and identify critical information that requires regular backups. Establishing clear restoration objectives, such as recovery time objectives, is essential. As noted by Infrascale, "RPO and RTO sit at the center of every conversation. They specify how much information a business can afford to lose and how quickly it must recover online."
To ensure effective backup processes, implement the following best practices:
This approach not only bolsters data security but also ensures business continuity. Regularly assessing and refreshing your strategy is vital to adapt to evolving business requirements and technological advancements. Statistics reveal that only 24% of organizations possess advanced disaster management plans, underscoring the importance of continuous testing and real-world performance to guarantee effective restoration planning.
Moreover, businesses that experience regular downtime face costs that are 16 times greater than those with fewer disruptions, highlighting the financial impact of inadequate backup solutions. By prioritizing these best practices, organizations can significantly improve their backup and recovery success.
Compliance with regulatory frameworks like HIPAA, PCI-DSS, and GDPR is not just essential; it’s a critical mandate for organizations across various sectors. In today’s landscape, where cybersecurity threats loom large, aligning with managed service provider backup and recovery practices is paramount. Start by pinpointing the specific requirements relevant to your industry.
Implementing encryption for data, both at rest and in transit, is crucial. Additionally, maintaining detailed logs of recovery activities is vital for facilitating compliance during audits. Regular compliance assessments and audits are necessary to proactively identify and address gaps in your processes. This approach not only protects your organization from legal repercussions but also enhances your reputation with clients and stakeholders.
Consider this: two to five times in the past three years. This statistic underscores the importance of compliance. As one compliance officer noted, compliance is not merely a best practice; it’s a crucial necessity for operational integrity and trust.
Moreover, with 85% of organizations indicating that over the last three years, the need for robust managed service provider backup and recovery strategies has become more pressing than ever. The report in 2024 further emphasizes the financial risks associated with non-compliance.
Cyber Solutions offers businesses comprehensive solutions to meet these regulatory requirements. This includes thorough reporting, audit preparation, and continuous monitoring. As Lucia Giles aptly stated, 'If your organization isn’t compliant, the consequences could be devastating.'

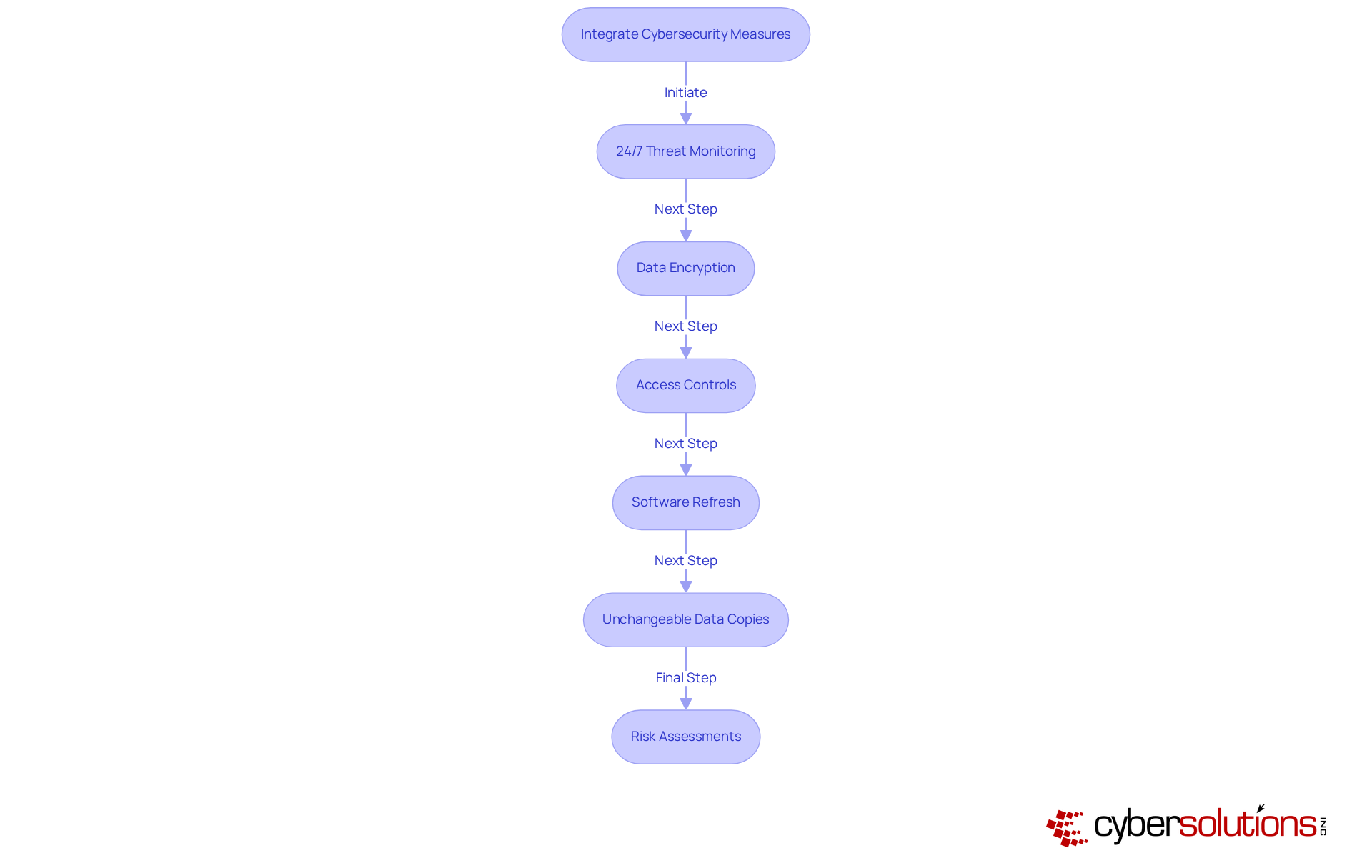
In today's digital landscape, the importance of robust cybersecurity in healthcare cannot be overstated. With the rise of cyber threats, healthcare organizations face unique challenges that demand immediate attention. Cyber Solutions stands ready to protect your stored information by incorporating cybersecurity measures into your backup solutions.
Our system detects and halts suspicious activities before they escalate, safeguarding your business from potential threats. By employing encryption, you can ensure that your data remains secure both in storage and during transmission. Additionally, establishing access controls limits who can access sensitive information, further enhancing your security posture.
It's crucial to consistently refresh your security protocols to guard against vulnerabilities and ensure your systems are equipped with the latest security patches. Consider utilizing unchangeable copies of your data, which cannot be modified or removed, as a safeguard against data loss.
Moreover, conducting thorough security assessments will help pinpoint and address possible vulnerabilities in your infrastructure. This proactive approach not only ensures adherence to regulations but also fortifies your organization against evolving threats. Are you ready to take the necessary steps to protect your healthcare data?
Ongoing supervision of support systems is vital for maintaining their reliability and effectiveness. Implementing monitoring tools can swiftly alert your IT team to any failures or irregularities in the backup process. Regular testing of recovery systems through restore drills is essential to confirm that systems are functioning correctly and accurately. Establishing a schedule for these tests ensures ongoing effectiveness.
Recording the outcomes of these drills not only aids in improvement but also bolsters organizational resilience. This proactive strategy fosters confidence in your backup solutions, aligning with current trends where 91% of managed service providers (MSPs) recognize the need for robust backup strategies. Moreover, with 43% of MSPs citing data security as their primary concern, the implementation of comprehensive backup solutions can significantly improve MSP backup and recovery by reducing risks associated with data loss and downtime.
A comprehensive approach to Managed Service Provider (MSP) backup and recovery is not just important; it’s essential for safeguarding critical data in today’s complex digital landscape. Organizations that establish a well-defined strategy, complete with clear recovery objectives, are better equipped to prepare for potential data loss and ensure swift restoration processes. By emphasizing best practices like the 3-2-1 backup rule and conducting regular assessments, businesses can enhance their data security while aligning with compliance mandates that protect against legal repercussions.
Key components vital for successful MSP backup and recovery strategies include:
Each of these practices plays a crucial role in fortifying an organization’s resilience against data breaches and operational disruptions. The result? Significant cost savings and enhanced trust with stakeholders.
In summary, organizations must prioritize the development and continuous improvement of their backup and recovery strategies. By investing in these best practices, businesses can protect their data and position themselves for success in a landscape fraught with challenges. Taking proactive steps now will ensure preparedness for future threats, making robust MSP backup and recovery solutions not just a necessity but a strategic advantage in today’s data-driven world.
Why is a backup and recovery strategy important for organizations?
A well-defined backup and recovery strategy is crucial for effective information protection, especially in a landscape where data breaches are common. It helps organizations assess their data needs and identify critical information that requires regular backup and recovery.
What are Recovery Point Objectives (RPO) and Recovery Time Objectives (RTO)?
RPO and RTO are key metrics in disaster recovery planning. RPO specifies how much information a business can afford to lose, while RTO indicates how quickly the business must recover its data online.
What is the 3-2-1 backup rule?
The 3-2-1 backup rule involves maintaining three copies of your information, storing them on two different media types, and keeping one copy offsite. This approach enhances data security and ensures compliance with industry regulations.
Why is it important to regularly assess and refresh a backup and recovery strategy?
Regular assessment and refreshing of the strategy is vital to adapt to evolving business requirements and technological advancements, ensuring that the backup and recovery plan remains effective.
What statistics highlight the importance of having a disaster management plan?
Only 24% of organizations possess advanced disaster management plans, indicating a significant gap in preparedness. Additionally, businesses that experience regular downtime face costs that are 16 times greater than those with fewer disruptions.
How can organizations enhance their resilience against information loss?
By prioritizing best practices in backup and recovery, such as defining clear restoration objectives and implementing the 3-2-1 backup rule, organizations can significantly enhance their resilience against information loss.