
Data storage disaster recovery has become a crucial priority for C-suite leaders, particularly in a landscape riddled with cyber threats and data breaches. Organizations that invest in strong recovery strategies not only safeguard their essential information but also bolster their operational resilience, significantly minimizing downtime and financial losses. Yet, as the threat landscape continues to evolve, how can executives guarantee that their disaster recovery plans stay effective and relevant? This article explores key strategies that empower leaders to tackle these challenges head-on and strengthen their organizations against potential disruptions.
Data storage is not just a technical necessity; it’s a strategic imperative for C-suite leaders. In an era marked by rampant information breaches and cyber threats, understanding the vital role of contingency planning can mean the difference between seamless and catastrophic failure. A well-structured disaster recovery plan not only safeguards critical information but also facilitates business continuity, minimizing downtime and financial losses.
Recent studies reveal that organizations investing in disaster recovery solutions can reduce restoration time by as much as 50%, significantly bolstering their resilience against unforeseen disruptions. Furthermore, achieving compliance with regulations enhances emergency response strategies by ensuring the implementation of advanced security protocols that protect sensitive federal information. The importance of data protection and GDPR underscores the need for effective strategies to avoid hefty fines and reputational damage.
As organizations navigate an increasingly complex threat landscape, prioritizing data storage disaster recovery is not merely prudent; it is essential for safeguarding operational integrity and financial stability. Are you prepared to face the challenges of today’s cybersecurity environment? The time to act is now.

Creating a detailed recovery strategy (DRP) is not just important; it’s essential for C-suite executives. In today’s landscape, a complete risk evaluation is the first step to recognizing potential threats. Cyberattacks, natural disasters, and hardware failures are just a few examples of risks that can severely disrupt operations. With 29% of breaches involving third-party attacks, as reported in 2026, the need for a robust recovery plan has never been clearer.
Once risks are identified, conducting a business impact analysis (BIA) becomes crucial. This analysis evaluates how disasters can affect business operations and helps establish clear objectives for restoration, specifically recovery time objective (RTO) and recovery point objective (RPO). These metrics guide the restoration process, ensuring that critical systems are back online within acceptable timeframes and that data loss is minimized. Moreover, defining roles and responsibilities within the team is vital; this clarity ensures that every member understands their unique contributions to the restoration effort.
Integrating Cyber Solutions' advanced technologies like threat detection and email security can significantly enhance your organization’s crisis management capabilities. Continuous monitoring allows for the detection and prevention of suspicious activities before they escalate into serious threats. This proactive approach provides real-time insights, enabling swift action to avert downtime or breaches. Additionally, utilizing cloud-based solutions for data storage can further bolster recovery capabilities, offering scalability and flexibility that lead to faster recovery times and reduced impact from disruptions.
A well-documented DRP should also include provisions for at least one backup copy stored off-site, safeguarding against physical disasters. Regular reviews and updates are essential to reflect technological advancements and changes in business operations, ensuring the plan remains effective and relevant. By prioritizing these strategies, C-suite leaders can not only protect their organizations against data integrity threats but also enhance overall resilience.
Integrating cutting-edge technology into emergency response plans is not just beneficial; it’s essential for organizations that prioritize data security to swiftly recover from information loss events. C-suite executives must prioritize the establishment of data backup systems that ensure business continuity by consistently generating copies of vital information. This ensures that data remains current and easily accessible for restoration. Moreover, employing cloud storage solutions is essential for effective recovery as it provides resources that are readily available during emergencies, significantly enhancing information integrity.
Emerging technologies like artificial intelligence and machine learning are game-changers in this arena. They can predict potential data loss scenarios and automate recovery processes, effectively reducing downtime. For instance, organizations that have implemented advanced recovery systems have reported a remarkable 30% reduction in restoration time. This statistic underscores the tangible advantages of leveraging technology in crisis management.
It’s crucial to recognize the risks of data loss, such as lost productivity and supply chain interruptions. Monitoring tools are vital in maintaining system performance and uptime, ensuring that operations function effectively. Adopting the 3-2-1 backup strategy - keeping three copies of data, using two different media types, storing one copy offsite, and ensuring one immutable copy - can further enhance data security. As we look ahead to 2026, the effectiveness of these automated solutions will be pivotal in minimizing operational disruptions and enhancing overall business resilience.

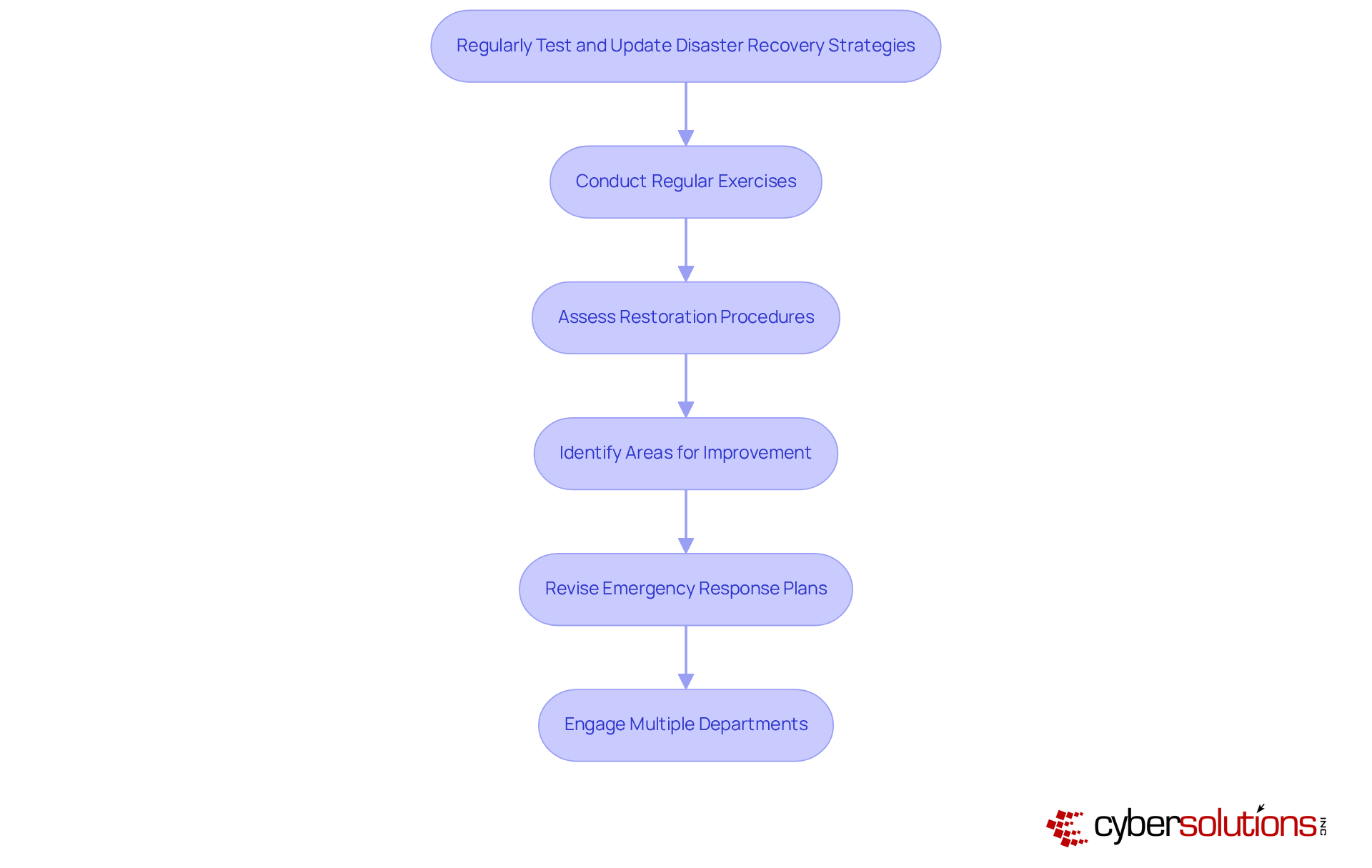
To ensure the efficiency of disaster recovery, C-suite executives must prioritize testing. Regular exercises that mimic various emergency situations are crucial for organizations to assess their restoration procedures and identify areas for improvement. Performing these tests at least bi-annually is recommended, as this frequency helps maintain team readiness and ensures that all personnel are familiar with their roles during a crisis.
As technology and business practices evolve, it’s essential to revise disaster recovery plans accordingly. This includes integrating new tools, procedures, and regulatory requirements. Testing plays a vital role in recovery by reinstating access to IT systems, data, and applications following a disruption. Organizations that regularly test and update their data storage can achieve a remarkable 40% improvement, underscoring the critical importance of this practice in maintaining operational continuity.
Collaboration is not just beneficial; it’s essential. Incidents affecting businesses often impact multiple functions simultaneously, enhancing coordination and clarifying escalation paths. By fostering collaboration across departments, organizations can better prepare for emergencies and ensure a swift, effective response.
Data storage disaster recovery is not just a technical issue; it’s a strategic imperative for C-suite leaders. In an era where data crises can threaten the very foundation of a business, the ability to manage these challenges effectively is crucial. Protecting vital information ensures business continuity and shields organizations from the potentially devastating impacts of data loss. Therefore, the proactive implementation of comprehensive disaster recovery plans (DRPs) is essential, enabling businesses to respond swiftly and efficiently to unexpected disruptions.
Key insights reveal the necessity of developing a thorough DRP that includes:
Regular testing and updates are vital, as these practices enhance team readiness and operational resilience. By leveraging modern technologies like artificial intelligence and cloud solutions, organizations can significantly reduce restoration times and bolster their overall crisis management capabilities.
The message for C-suite leaders is clear: investing in robust data storage disaster recovery strategies is not merely a safeguard against data loss; it’s a pathway to ensuring long-term business viability and resilience. As the threat landscape evolves, embracing these best practices empowers organizations to navigate challenges effectively, fostering a culture of preparedness that is essential for success in today’s dynamic environment.
Why is data storage disaster recovery important for organizations?
Data storage disaster recovery is crucial for organizations as it is a strategic imperative that safeguards critical information, facilitates rapid recovery, and minimizes downtime and financial losses during crises such as information breaches and cyberattacks.
How can a well-structured emergency response strategy benefit an organization?
A well-structured emergency response strategy can significantly reduce restoration time by up to 50%, enhancing organizational resilience against unforeseen disruptions and ensuring business continuity.
What role does CMMC Level 3 compliance play in emergency response strategies?
Achieving CMMC Level 3 compliance enhances emergency response strategies by ensuring the implementation of advanced security protocols that protect sensitive federal information.
What regulations emphasize the need for effective information restoration plans?
Regulations such as HIPAA and GDPR emphasize the need for effective information restoration plans to avoid hefty fines and reputational damage.
Why is prioritizing crisis management essential for organizations today?
Prioritizing crisis management is essential for organizations as it safeguards operational integrity and financial stability in an increasingly complex threat landscape, particularly in the current cybersecurity environment.