
In an era where cyber threats are increasingly sophisticated, the demand for secure infrastructure solutions is more critical than ever. These solutions not only safeguard sensitive data but also ensure compliance with stringent regulations, empowering organizations to navigate the complexities of modern cybersecurity.
However, as businesses invest in these technologies, a pressing question arises: what key features truly define an effective secure infrastructure? How can these features be leveraged to mitigate the risks inherent in today's digital landscape?
Understanding these elements is essential for organizations aiming to protect their assets and maintain trust in an ever-evolving threat environment.
In today's digital landscape, the importance of cybersecurity cannot be overstated, especially in healthcare. Secure infrastructure solutions encompass a comprehensive array of technologies, policies, and practices that are designed to protect a company's IT environment from ever-evolving cyber threats. This includes enhanced hardware, software, networks, and information centers specifically created to prevent unauthorized access, breaches, and other vulnerabilities.
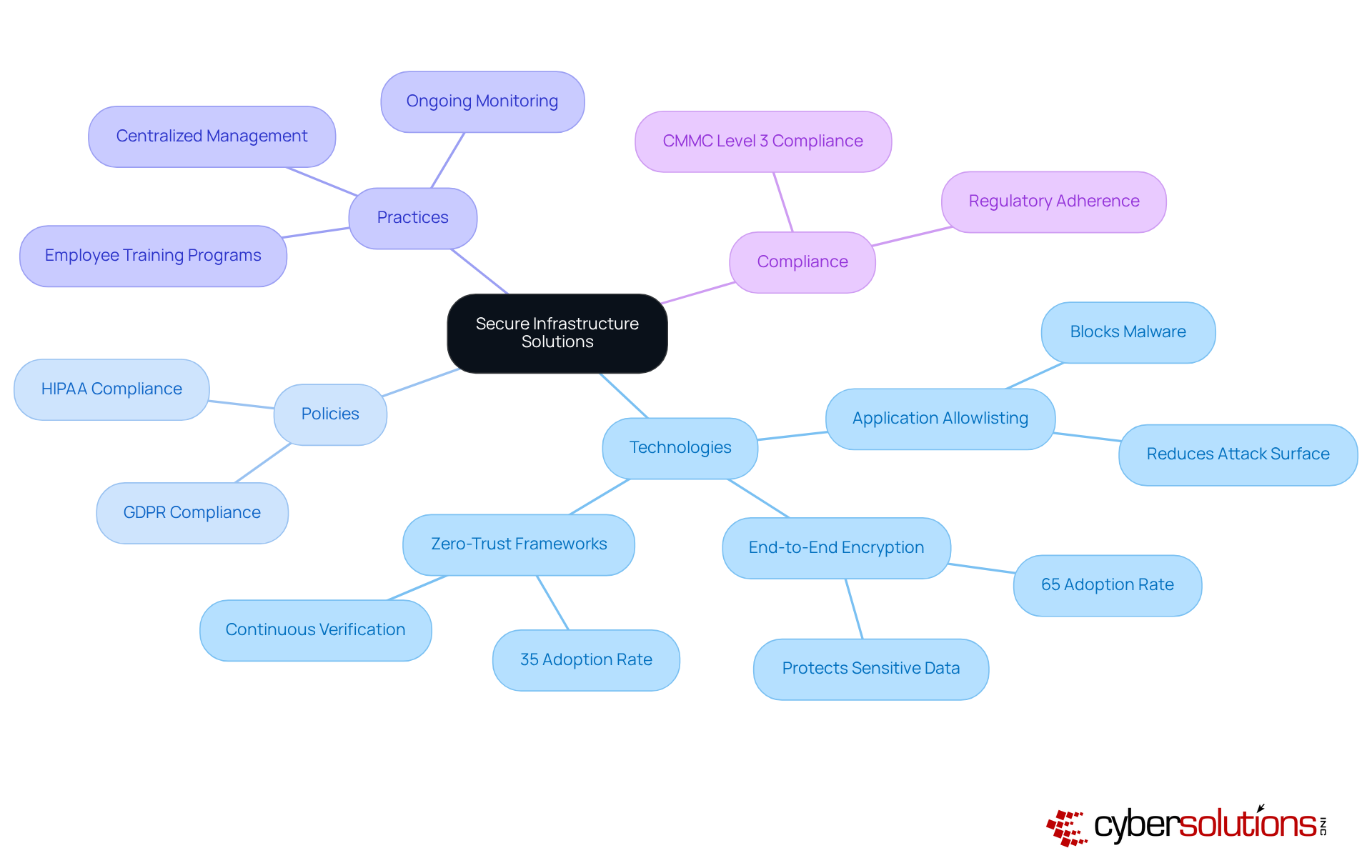
A critical component of this framework is antivirus software, which proactively blocks malware and unauthorized software from executing. By doing so, it effectively reduces the attack surface and minimizes vulnerabilities. This approach not only safeguards data but also ensures compliance with industry regulations such as PCI DSS and HIPAA. In fact, a significant 65% of entities have adopted secure infrastructure solutions to bolster data security, reflecting the growing recognition of secure systems as a vital element of a robust cybersecurity strategy.
As organizations increasingly embrace cloud computing, projected to reach 65% adoption by 2025, these solutions act as the backbone of operational safety in a rapidly changing digital environment. Real-world examples, such as the adoption of zero trust security by 35% of organizations, illustrate a shift towards continuous verification and granular access control, further underscoring the essential role of secure infrastructure solutions in mitigating cyber risks.
Moreover, security features, including centralized management and ongoing monitoring, enhance security by ensuring that only authorized applications can operate, thus preventing potential threats. Achieving compliance not only strengthens security but also secures federal contracts, demonstrating a commitment to protecting sensitive federal data.
Ultimately, these solutions empower businesses to operate with confidence, knowing they are protected from cyber threats.
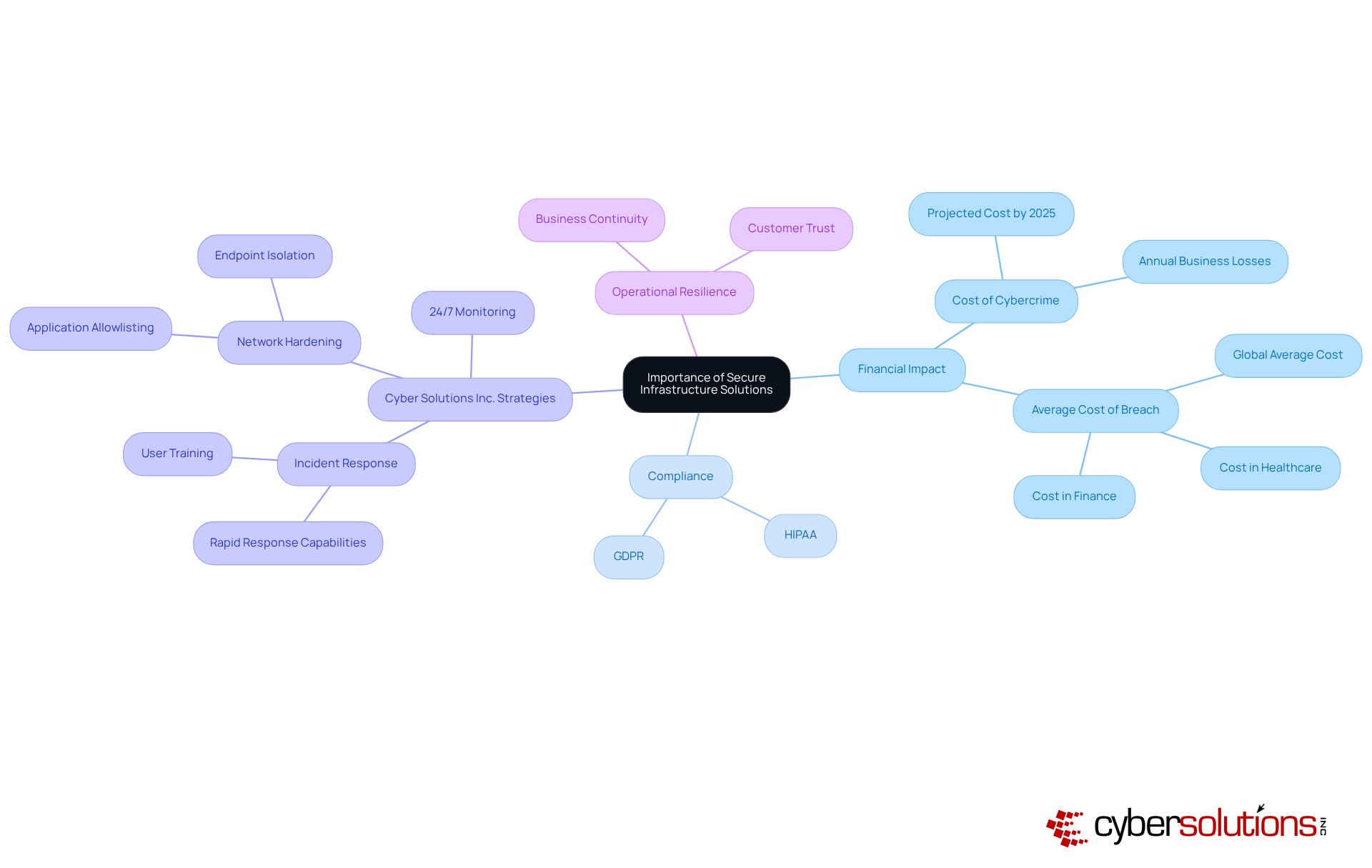
In the current digital landscape, the significance of secure infrastructure solutions cannot be overstated. With a staggering $10.5 trillion lost annually by 2025, organizations face unprecedented risks. Cybersecurity measures, with a 10% increase year-on-year, are vital for preventing these costly incidents, ensuring data integrity, and fostering customer trust. They also play a crucial role in compliance regulations, which impose strict data protection requirements. As remote work becomes increasingly prevalent, the demand for secure solutions to access corporate resources has intensified, making these solutions essential for operational resilience. Organizations that prioritize secure infrastructure not only protect their assets but also enhance their reputation and reliability in the eyes of customers and stakeholders.
Cyber Solutions Inc. employs a comprehensive cybersecurity strategy that features a layered approach to enhance recovery and client partnership. This strategy is exemplified by our rapid response team, ensuring that our incident response team can be on-site within 24 hours to effectively manage risks. By implementing endpoint isolation, malware removal, and user training, we facilitate a quicker and more thorough recovery from incidents, as evidenced by our case studies.
Moreover, our security measures, including application allowlisting, are crucial in preventing unauthorized software from executing. This approach minimizes the attack surface and assists organizations in meeting stringent compliance requirements. By permitting only approved applications to run, we significantly reduce vulnerabilities, making it more challenging for attackers to exploit systems.
In this evolving risk environment, Cyber Solutions Inc. remains committed to providing innovative solutions, ensuring proactive cybersecurity and risk prevention for our clients.
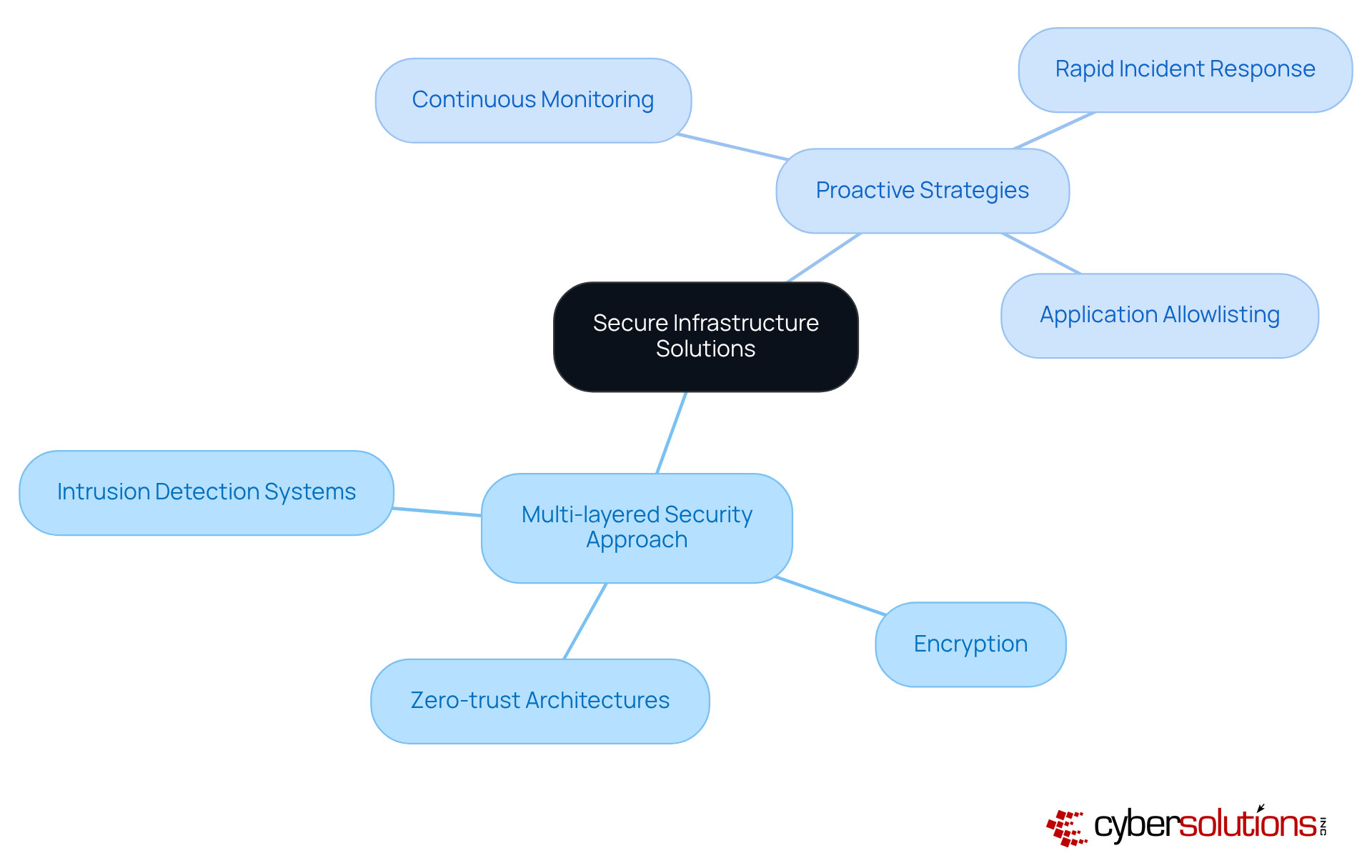
The escalating sophistication of cyber threats and the increasing reliance on digital technologies have made the development of secure infrastructure solutions more critical than ever. In the past, security measures primarily revolved around perimeter defenses like firewalls and antivirus software. However, as cyberattacks have evolved, organizations are now adopting a comprehensive security strategy that includes:
This shift highlights a growing recognition that security measures must be integrated into every facet of IT infrastructure, rather than treated as an afterthought.
Statistics reveal that approximately 4,000 cyberattacks occur daily, underscoring the urgent need for enhanced security protocols. In response, organizations are embracing proactive strategies that emphasize:
For example, healthcare companies, which faced an average of 1,500 data breaches in 2023, are increasingly implementing multi-layered security frameworks to safeguard sensitive patient data.
A vital aspect of this proactive approach is application whitelisting, which prevents unauthorized or malicious applications from executing, significantly reducing vulnerabilities. By allowing only pre-approved software to run, organizations not only bolster their security posture but also ensure compliance with regulatory standards. Features like centralized oversight and ongoing monitoring capabilities enhance the effectiveness of security measures, enabling organizations to swiftly detect and mitigate risks. This comprehensive strategy emphasizes the necessity of integrating security solutions into the overall security framework, reinforcing Cyber Solutions' commitment to delivering robust protection against evolving cyber threats.
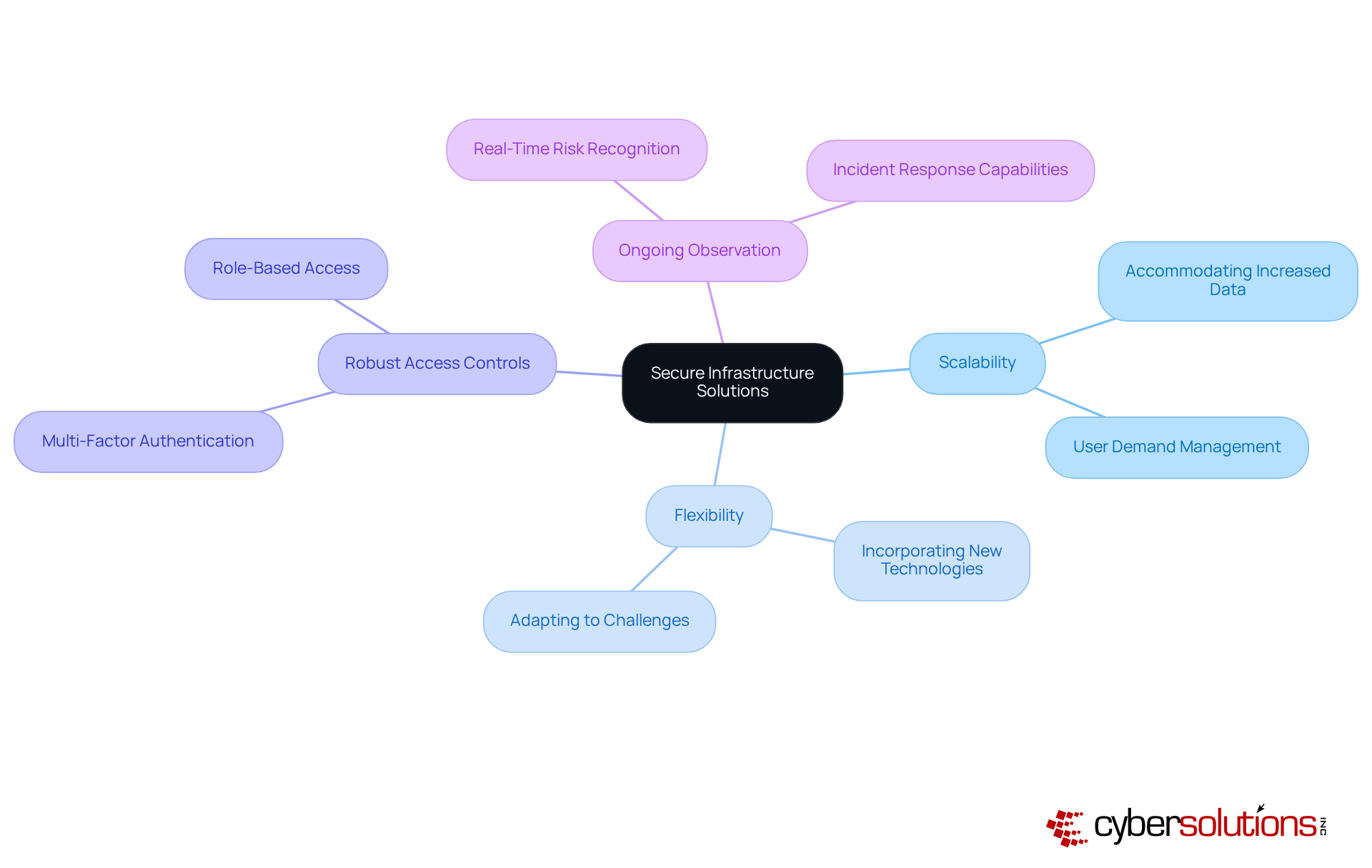
In today's digital landscape, the importance of secure infrastructure solutions cannot be overstated. The essential characteristics of secure infrastructure solutions are crucial for protecting organizations against ever-evolving threats.
Furthermore, ongoing observation and assessment are essential for recognizing and alleviating risks in real-time. This proactive approach ensures that questionable activities are identified and managed before they escalate, protecting both the organization and its patients. Together, these characteristics form a framework that can endure and react to threats effectively.
As healthcare CFOs navigate these challenges, it is a strategic imperative to implement secure infrastructure solutions.
Cybersecurity is not just a technical requirement; it’s a critical necessity for healthcare organizations today. As cyber threats continue to evolve, the stakes have never been higher. Organizations across various sectors have successfully implemented secure infrastructure solutions.
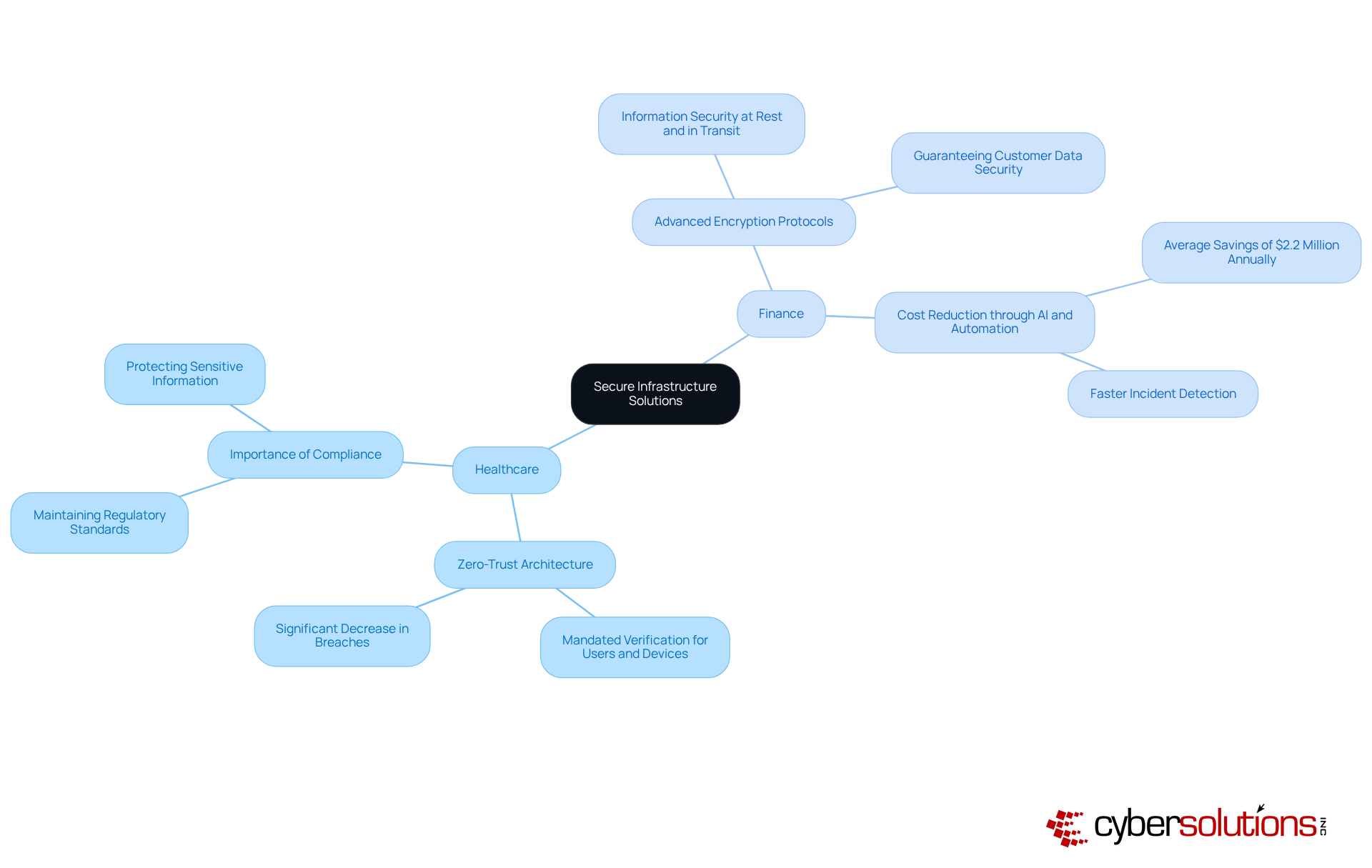
For instance, a healthcare provider implemented a multi-factor authentication system, mandating verification for every user and device accessing its network. This strategy resulted in a significant decrease in data breaches, underscoring the effectiveness of such frameworks in protecting sensitive information. In the financial sector, institutions have embraced encryption for information both at rest and in transit. This proactive measure guarantees that sensitive customer information remains secure, even in the event of a breach.
Statistics reveal that organizations utilizing secure infrastructure solutions experience a marked decrease in security incidents. This reinforces the necessity of these measures in maintaining data integrity. Furthermore, experts advocate for continuous monitoring as a critical component in healthcare cybersecurity, emphasizing its role in threat detection.
These case studies underscore the vital role of secure infrastructure solutions in safeguarding critical assets and enhancing overall security posture. As healthcare organizations navigate these challenges, the implementation of robust security measures is not just advisable; it is imperative.
In today's interconnected landscape, the importance of secure infrastructure solutions cannot be overstated. Cybersecurity is not just a technical enhancement; it’s a vital framework that shields organizations from the relentless onslaught of cyber threats. By integrating advanced technologies and practices, businesses can bolster their IT environments, ensuring sensitive data remains secure and compliant with industry regulations.
Consider the critical role of:
As cyber risks escalate, implementing these strategies can significantly reduce vulnerabilities and enhance operational resilience. For instance, various sectors, particularly healthcare, have successfully adopted these solutions to safeguard their assets and maintain compliance with stringent regulations.
The call to action is clear: organizations must prioritize the implementation of secure infrastructure solutions to navigate the complexities of modern cybersecurity effectively. By doing so, they not only protect their operations and customer trust but also position themselves as leaders in a landscape where cybersecurity is paramount. Embracing these solutions today will pave the way for a more secure digital future, making it imperative for all organizations to take proactive steps in enhancing their cybersecurity posture.
What are secure infrastructure solutions?
Secure infrastructure solutions are a comprehensive array of technologies, policies, and practices designed to protect a company's IT environment from cyber threats. They include enhanced hardware, software, networks, and information centers to prevent unauthorized access, breaches, and vulnerabilities.
Why is application allowlisting important in cybersecurity?
Application allowlisting is critical because it proactively blocks malware and unauthorized software from executing, reducing the attack surface and minimizing vulnerabilities. This approach safeguards sensitive information and ensures compliance with industry regulations such as GDPR and HIPAA.
What percentage of organizations have adopted end-to-end encryption?
Approximately 65% of entities have adopted end-to-end encryption to enhance data security, reflecting the growing importance of secure systems in cybersecurity strategies.
How are organizations adapting their cybersecurity strategies?
Organizations are increasingly embracing cutting-edge security technologies, with projections indicating a 65% adoption rate by 2025. This includes the adoption of zero-trust frameworks by 35% of organizations, which emphasizes continuous verification and granular access control.
What does achieving CMMC Level 3 compliance signify?
Achieving CMMC Level 3 compliance signifies strengthened cybersecurity practices and secures federal contracts, demonstrating a commitment to protecting sensitive federal data.
What are the financial implications of cybercrime for businesses?
Cybercrime is projected to cost businesses approximately $10.5 trillion annually by 2025, with the average cost of a data breach reaching around $4.88 million globally, reflecting a 10% increase year-on-year.
How do secure infrastructure solutions enhance customer trust?
By prioritizing secure infrastructure solutions, organizations protect their assets and ensure compliance with regulations, which enhances their reputation and reliability in the eyes of customers and stakeholders.
What strategies does Cyber Solutions Inc. implement for cybersecurity?
Cyber Solutions Inc. employs a layered cybersecurity strategy that includes rapid incident response, endpoint isolation, malware removal, user training, and proactive network hardening strategies such as application allowlisting.
What services does Cyber Solutions Inc. provide for proactive cybersecurity?
Cyber Solutions Inc. provides 24/7 network monitoring and alert services to ensure proactive cybersecurity and risk prevention for their clients.