
Outsourcing IT support services has become a strategic necessity for organizations looking to enhance operational efficiency and drive growth. By leveraging external expertise, companies can significantly reduce costs, improve productivity, and strengthen their cybersecurity posture. This shift allows internal teams to focus on core business functions, ultimately fostering innovation and agility.
However, the decision to outsource is not without its challenges. Leaders must navigate potential pitfalls to maximize the benefits of outsourced support. How can they ensure that their organizations thrive in this rapidly evolving digital landscape? This article delves into the ten strategic advantages of outsourcing IT support services, offering insights that empower organizations to make informed decisions.
In an era where cybersecurity threats are increasingly sophisticated, understanding the implications for your organization is crucial. By addressing these challenges head-on, organizations can position themselves for success and resilience in the face of adversity.
from Cyber Solutions Inc. empowers organizations to use managed services for routine IT tasks, allowing internal teams to focus on essential operations. This extensive support include:
These services together enhance efficiency and significantly reduce costs. Companies that utilize outsourced support report a decrease in operational expenses by 20-30% and an increase in productivity by 15-25%. By leveraging external expertise, firms can optimize operations, ensuring that resources are allocated efficiently and effectively.
This strategic approach fosters a more agile organization, positioning companies to respond swiftly to market demands. In a landscape where competition is fierce, the ability to adapt is crucial. Outsourced support not only drives growth and innovation but also prepares organizations for the future. Are you ready to enhance efficiency and secure your organization's future?

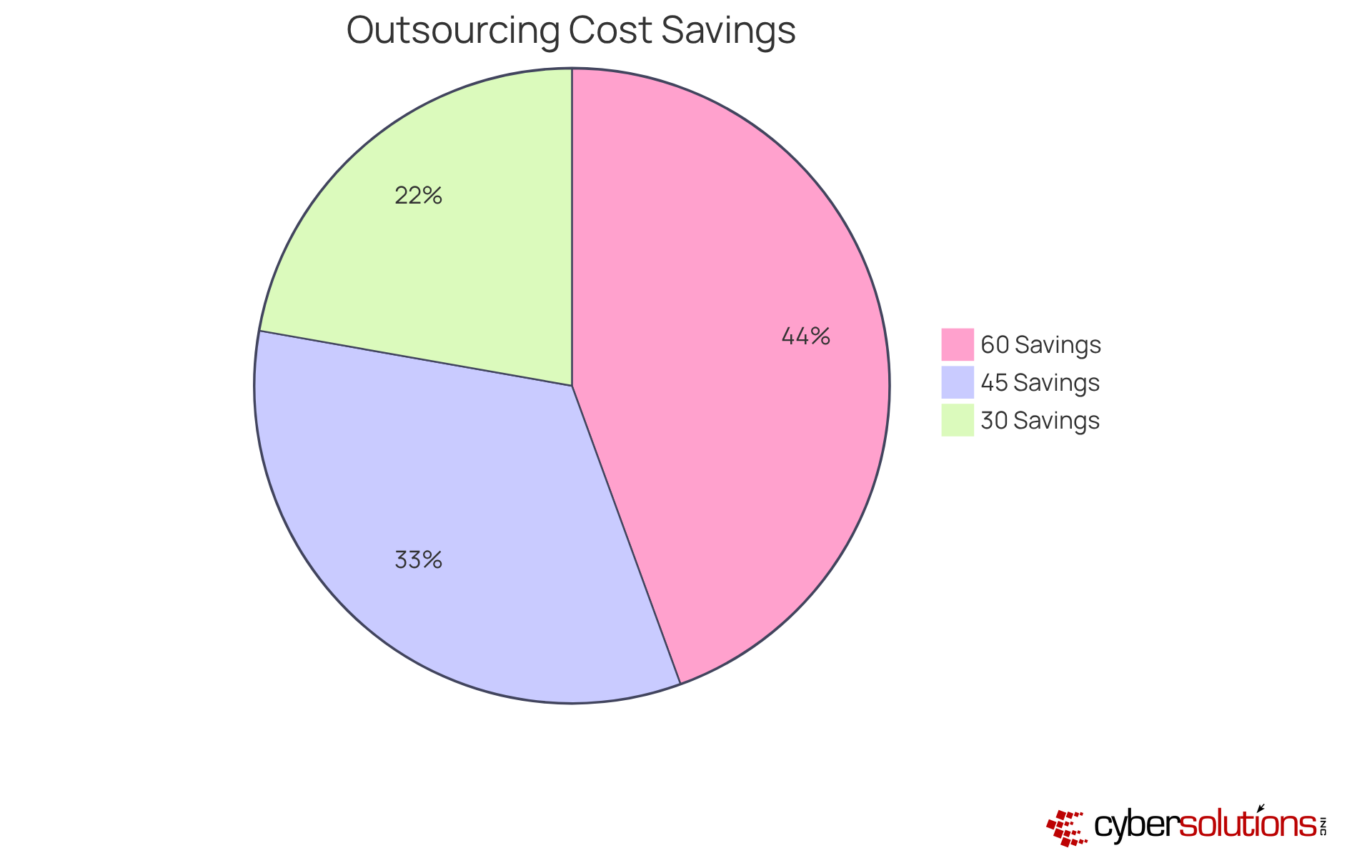
The use of outsourced support services for IT assistance is a strategic move that can lead to cost savings. By eliminating the need for an internal team, businesses can avoid the substantial overhead costs associated with salaries, benefits, and training. Recent reports reveal that companies can achieve average reductions in IT expenses ranging from 30% to 60% through outsourcing. This shift not only reduces costs but also converts unpredictable expenditures into fixed costs, making budgeting and financial planning much easier.
Cyber Solutions Inc. offers a comprehensive flat-rate pricing model that encompasses everything from email licenses to software updates. This approach helps businesses save up to 30% on their IT costs, allowing them to reallocate resources to other critical areas. CFOs across various industries have recognized that utilizing outsourced services enables a more strategic use of funds, ultimately improving efficiency and profitability.
By leveraging external expertise, companies can focus on their core competencies while benefiting from advanced technology and specialized support. This not only promotes growth and innovation but also strengthens security. For instance, through proactive measures, Cyber Solutions Inc. has successfully improved security configurations and provided staff training on identifying suspicious emails. This ensures minimal operational disruption and fosters a robust Zero Trust approach, safeguarding the organization against evolving threats.
In today's digital landscape, the importance of cybersecurity cannot be overstated, especially in sectors like healthcare. Organizations face a myriad of challenges and operational integrity issues that may not be readily available internally, enabling businesses to enhance their security posture.
Cyber Solutions Inc. employs certified professionals with extensive experience across various IT domains, including cybersecurity, cloud solutions, and compliance. This access to specialized expertise enables organizations to adopt best practices, significantly enhancing their operational capabilities. Did you know that 77% of companies now rely on external providers for IT support? This statistic underscores the growing dependence on outsourced support services expertise.
Moreover, entities that prioritize cybersecurity measures experience significant benefits. Many experience improvements from effectively implemented transformations. As the demand for specialized knowledge increases, particularly in fields like healthcare and finance, companies are recognizing the critical role of certified IT experts. These professionals not only help mitigate risks but also ensure compliance with regulations.
A proactive approach, such as application allowlisting, is essential in preventing unauthorized software from executing, thereby enhancing security and compliance. By leveraging outsourced support services, companies can foster growth, improve efficiency, and maintain a competitive edge in an ever-evolving digital environment. The question remains: can your organization afford to overlook the value of specialized IT support?

In today's digital landscape, the importance of cybersecurity cannot be overstated, especially for healthcare organizations. By utilizing outsourced support services from Cyber Solutions, a company can enhance its security posture and maximize ROI. With threat detection and incident response, organizations can effectively shield themselves from the alarming rise in cyber threats. Recent reports reveal that:
This statistic underscores the urgent need for robust cybersecurity measures.
Moreover, Cyber Solutions ensures compliance with critical industry regulations such as HIPAA and GDPR. This is particularly vital, as 79% of small and medium-sized enterprises lack adequate cybersecurity protocols. Our initial assessment and gap analysis pinpoint vulnerabilities in your current cyber defenses, offering tailored remediation strategies that encompass policy updates and system upgrades. Notably, 60% of organizations report experiencing security breaches, highlighting the pressing nature of these challenges. This proactive approach not only mitigates the risk of costly penalties and reputational damage but also fosters a culture of security awareness within the organization.
By entrusting their IT security to experts, organizations can focus on growth and innovation, assured that their data is protected against evolving threats. This strategic partnership empowers organizations to navigate the complexities of compliance while strengthening their overall security framework. Are you ready to take the next step in safeguarding your organization?

Outsourced support services are vital for ensuring operational continuity and resilience. In today's landscape, where cyber threats loom large, organizations must prioritize their disaster recovery plans. Cyber Solutions Inc. stands out by offering comprehensive managed IT and cybersecurity solutions, including services that feature 24/7 Security Operations Center (SOC) monitoring, threat response, a full security stack, and Microsoft 365 management. These offerings not only safeguard information but also enable swift recovery during unexpected events, significantly minimizing downtime and operational interruptions.
Consider this: organizations utilizing outsourced support typically experience an average of under 12 hours of downtime. This is a stark contrast to the 29% of firms that take a day or longer to resume operations. Industry leaders assert that a well-structured disaster recovery plan is not just a technical necessity; it’s a strategic imperative for maintaining business continuity.
To effectively navigate these challenges, organizations that employ outsourced support should adopt optimal strategies. The following are essential:
By implementing these strategies, companies can not only safeguard their operations but also enhance their ability to respond effectively to disruptions.
In conclusion, the importance of robust IT assistance cannot be overstated. As organizations face increasing cyber threats, partnering with experts like Cyber Solutions Inc. can make all the difference in maintaining productivity and service provision.

For companies seeking the scalability and flexibility needed to adapt to evolving demands, outsourced IT solutions are crucial. In today’s fast-paced environment, Cyber Solutions Inc. stands out by offering services that evolve alongside your business. This adaptability empowers organizations to avoid unnecessary investments in infrastructure or personnel. Consequently, leaders can focus on strategic initiatives instead of getting mired in IT complexities.
Consider this: 76% of executives affirm that outsourced IT solutions significantly enhance their operational efficiency, allowing them to respond swiftly to market changes. Furthermore, organizations that embrace outsourcing often experience a remarkable 62% increase in productivity, allowing teams to dedicate their efforts to core activities. By leveraging external expertise, companies not only streamline their operations but also enhance their position for sustainable growth in a competitive landscape.
Cyber Solutions Inc. employs a robust security framework that encompasses:
This ensures that your security configurations are not just adequate but resilient. In the event of an incident, our rapid response team is ready to act, utilizing a layered recovery strategy that minimizes damage and maintains operational continuity.
Are you ready to enhance your organization’s IT capabilities and security posture? Let Cyber Solutions Inc. guide you through the complexities of IT outsourcing, ensuring you stay ahead in a rapidly changing market.

While outsourced IT services offer significant advantages, they also present challenges that organizations must navigate effectively. Communication issues often emerge as a primary concern, with 40% of business and tech leaders acknowledging that these obstacles can hinder collaboration and project success. To mitigate these risks, establishing and enforcing service level agreements (SLAs) is essential. Companies utilizing instant messaging and video conferencing tools have reported improved communication with their outsourced teams, leading to better project outcomes.
Moreover, organizations that prioritize team building have found that promoting cultural exchange programs can bridge gaps and enhance collaboration. As Jose Alvarez, Managing Director of IT Services, states, "The right outsourcing partner will bring the newest technologies that improve efficiency, streamline operations, and enhance productivity." Effective communication is crucial for the successful integration of these technologies.
With 77% of organizations planning to utilize outsourced support in 2024, addressing communication challenges is more urgent than ever. Additionally, as 40% of industry and tech leaders anticipate increasing investments in technology, it is vital to proactively tackle these challenges. By implementing structured protocols and regular check-ins, companies can cultivate successful relationships that align with their operational needs and drive efficiency.

Effective communication and relationship management are crucial for the success of outsourced support services. Organizations must prioritize collaboration with their external partners to ensure alignment on goals and expectations. Did you know that teams fostering open communication are three times more likely to feel engaged at work? This engagement directly impacts productivity and quality. By creating a robust alliance with service providers, companies not only promote teamwork but also enhance service delivery, leading to improved outcomes.
Effective IT leaders emphasize that clear communication and established expectations are vital for navigating the complexities of outsourcing. For instance, companies that integrate Global In-house Centers (GICs) into their workforce model report increased efficiency. By focusing on these tactics, organizations can cultivate a more productive and responsive collaboration with their partners.

Implementing effective strategies is essential for organizations transitioning to outsourced IT services. A comprehensive plan must include several key elements:
As Scott Gildner emphasizes, "Effective change management is crucial." By focusing on these elements, organizations not only minimize disruptions but also facilitate a smoother integration of outsourced functions into daily operations.
Research shows that entities with robust training programs experience significantly higher adoption rates and reduced resistance during transitions. Communication plays a crucial role as well; poor communication can lead to confusion and decreased engagement. How can organizations ensure that their employees are well-informed and engaged during such critical transitions? By embracing these optimal methods, companies can ensure that their transition to outsourced IT services is both effective and successful, ultimately enhancing productivity.
It's important to recognize that change management is essential, underscoring the vital role of effective communication practices. Organizations must prioritize these strategies to successfully navigate the complexities of outsourcing.

Selecting the right IT support provider is not just a decision; it’s a pivotal strategic move that can profoundly influence an organization’s success. In today’s landscape, where technology is rapidly evolving, assessing a provider’s experience, offerings, response times, and customer reviews is crucial. Can your organization afford to overlook the importance of specialized expertise? This adaptability is essential for navigating the complexities of modern IT environments effectively.
Testimonials from clients consistently reveal satisfaction with service quality, especially when providers showcase a strong track record in managing cybersecurity risks and compliance. A critical aspect of modern IT assistance is the implementation of robust security measures. This proactive approach not only prevents malware and unauthorized software from executing but also significantly reduces the attack surface and minimizes vulnerabilities. By ensuring that only approved applications can run, organizations can better defend against threats such as ransomware and zero-day attacks, while also meeting stringent compliance requirements like HIPAA, PCI-DSS, and GDPR.
By choosing a partner like Cyber Solutions Inc., businesses can leverage tailored support that enhances operational efficiency. This positions them to thrive in a competitive landscape. As industry leaders emphasize, careful planning and due diligence in selecting an IT partner are essential for achieving return on investment. Are you ready to take the next step in securing your organization’s future?

Outsourced support services have become a strategic necessity for organizations looking to enhance operational efficiency, drive cost savings, and strengthen security. By partnering with specialized providers like Cyber Solutions Inc., companies can delegate routine IT tasks. This delegation allows internal teams to concentrate on core business functions and respond more effectively to the ever-evolving market demands.
The article has explored key benefits of outsourcing IT support, including:
Moreover, it has emphasized the significance of effective communication and relationship management in fostering successful outsourcing partnerships, alongside the critical role of change management during transitions to outsourced services.
Ultimately, the decision to outsource IT support transcends mere cost reduction; it positions an organization for sustainable growth and resilience in an increasingly complex digital landscape. Embracing outsourced support services empowers organizations to leverage external expertise, enhance their security posture, and maintain a competitive edge. As the demand for efficient and adaptable IT solutions continues to rise, one question remains: is your organization ready to embrace the strategic advantages of outsourcing?
What is managed IT support and how does it benefit organizations?
Managed IT support involves outsourcing routine IT tasks to allow internal teams to focus on essential operations. Benefits include 24/7 help desk resources, proactive monitoring, and regular upkeep, which together reduce downtime and enhance productivity.
How much can companies save by using outsourced IT support services?
Companies can achieve average reductions in IT expenses ranging from 30% to 60% through outsourcing, resulting in significant cost savings and more predictable budgeting.
What are the productivity improvements reported by companies using outsourced IT support?
Companies that utilize outsourced support services report an increase in productivity by 15-25%.
How does outsourcing IT support contribute to operational efficiency?
Outsourcing IT support helps streamline operations, allowing resources to be allocated more efficiently and effectively, which fosters a more agile work environment.
What financial model does Cyber Solutions Inc. offer for IT support services?
Cyber Solutions Inc. offers a comprehensive flat-rate pricing model that includes various IT services, helping businesses save up to 30% on their IT costs.
Why is access to specialized expertise important for organizations?
Access to specialized expertise is crucial for navigating cybersecurity threats and ensuring compliance with regulations. Outsourced support services provide certified professionals with extensive experience in various IT domains.
What impact does specialized IT knowledge have on company performance?
Organizations that prioritize specialized IT knowledge often report revenue growths of 5-15% and cost savings of 10-25% from effectively implemented transformations.
How does Cyber Solutions Inc. enhance security for its clients?
Cyber Solutions Inc. employs proactive strategies, such as network hardening and application allowlisting, to improve security configurations and mitigate risks associated with cybersecurity threats.
What sectors are particularly reliant on outsourced IT support services?
Sectors like healthcare and finance are particularly reliant on outsourced IT support services due to the need for specialized knowledge and compliance with regulatory frameworks.
How does outsourcing IT support prepare organizations for future challenges?
Outsourcing IT support enables organizations to adapt to evolving cybersecurity threats and market demands, positioning them for growth and innovation as they approach future challenges.