
In today’s perilous digital landscape, creating a robust security training program is not just a luxury; it’s a necessity for organizations. As cyber threats become increasingly sophisticated, it’s crucial for employees to be well-versed in security protocols and practices. This article explores four best practices that not only enhance security awareness but also empower employees to act as the first line of defense against potential breaches. How can organizations ensure their training programs are effective and adaptable to the ever-changing threat environment?
The current landscape of cybersecurity threats poses unique challenges for organizations. With the rise in data breaches and cyberattacks, the implications for businesses are profound. Organizations must recognize that their employees are often the first line of defense. By investing in comprehensive training programs, they can equip their workforce with the knowledge and skills needed to mitigate risks effectively.
To address these challenges, Cyber Solutions offers tailored training programs designed to enhance security awareness and foster a culture of vigilance. By implementing these best practices, organizations can not only protect their assets but also build a resilient workforce ready to tackle the evolving threat landscape.
Creating an effective security awareness training program is crucial for organizations aiming to mitigate risks. Cybersecurity threats are evolving, and understanding these risks is essential for every employee.
Employee training is a top priority. Employees must learn to identify phishing attempts, which rank among the most prevalent cyber threats. Training should incorporate real-world examples and simulations to sharpen recognition skills.
Next, password security cannot be overlooked. Educating employees on crafting strong passwords and the significance of password management is vital. This includes implementing multi-factor authentication (MFA) to bolster security.
Furthermore, data protection understanding is imperative. Employees should be trained on how to handle sensitive information securely, including practices like data encryption and secure sharing.
Incident reporting is another critical component. Training should stress the importance of promptly reporting security incidents, fostering a culture of vigilance within the organization.
Lastly, regulatory compliance is essential. Employees need to be aware of relevant regulations, such as GDPR and HIPAA, and understand how their actions can impact compliance.
By integrating these elements, companies can develop a robust security awareness training program that effectively addresses the most pressing security challenges.

To maximize the effectiveness of company security training, organizations must recognize the critical importance of security awareness in today’s landscape.
By tailoring company training programs, companies can effectively equip their staff to manage the security challenges they face, ultimately reducing the likelihood of incidents and enhancing their overall safety posture.

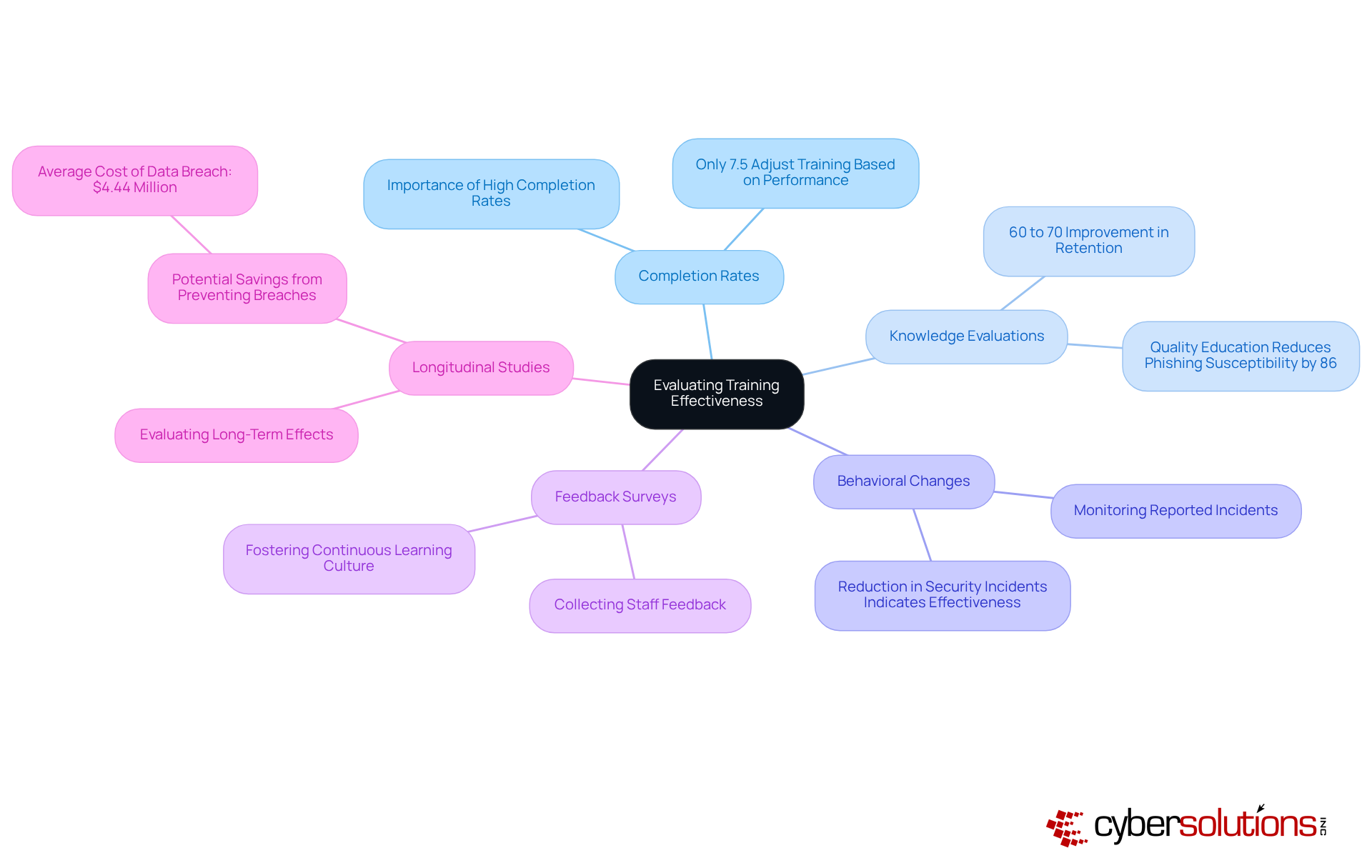
To effectively evaluate the success of security training, organizations must implement the following metrics:
By employing these metrics, organizations can obtain a clearer understanding of their educational program's effectiveness and make data-informed choices for future enhancements. As Zig Ziglar wisely noted, "The only thing worse than educating employees and losing them is not educating them and retaining them," highlighting the essential importance of investing in training programs.
To ensure that training remains effective, organizations must take decisive action:
By committing to these regular updates, organizations can ensure that their company security training remains effective and relevant, effectively addressing the ever-evolving landscape of cybersecurity.

Creating a robust security training program is not just essential; it’s a strategic necessity for organizations aiming to protect their assets against evolving cyber threats. By prioritizing key components such as:
companies can cultivate a workforce that is well-equipped to recognize and respond to potential security risks.
Customizing training programs to address specific organizational needs is crucial. By assessing unique threats and tailoring content to reflect real-world scenarios, organizations can engage employees through interactive elements and continuously seek feedback. This approach enhances the relevance and effectiveness of security training initiatives. Moreover, implementing metrics for evaluating training success - like completion rates, knowledge evaluations, and behavioral changes - ensures that programs remain impactful and aligned with the organization's security objectives.
Ultimately, investing in effective security awareness training transcends mere compliance; it’s a strategic imperative. Organizations must commit to regularly updating training content to address emerging threats and keep staff informed of the latest cybersecurity trends. By fostering a culture of vigilance and continuous learning, companies can significantly reduce the likelihood of security incidents, thereby safeguarding their operations and reputation in an increasingly complex digital landscape.
What is the purpose of security awareness training in organizations?
The purpose of security awareness training is to safeguard an organization's assets by educating employees about evolving cybersecurity threats and how to recognize and mitigate these risks.
Why is phishing awareness a priority in security training?
Phishing awareness is a priority because phishing attempts are among the most prevalent cyber threats. Training helps employees learn to identify these attempts through real-world examples and simulations.
What should employees learn about password security?
Employees should learn how to create strong passwords, the importance of password management, and the implementation of multi-factor authentication (MFA) to enhance security.
Why is data protection important in security training?
Data protection is important because employees must understand how to handle sensitive information securely, including practices like data encryption and secure sharing.
What role does incident reporting play in security awareness training?
Incident reporting plays a critical role by emphasizing the importance of promptly reporting suspicious activities and incidents, which helps foster a culture of vigilance within the organization.
What regulations should employees be aware of in security training?
Employees should be aware of relevant regulations such as GDPR and HIPAA, understanding how their actions can impact compliance with these regulations.
How can companies develop an effective security training program?
Companies can develop an effective security training program by integrating components such as phishing awareness, password security, data protection, incident reporting, and regulatory compliance to address pressing security challenges.