
In today's fast-paced digital landscape, the security of cloud applications stands as a paramount concern for organizations striving for success. C-suite leaders are tasked with the formidable challenge of navigating intricate cybersecurity threats while safeguarding sensitive data and ensuring operational integrity. By adopting essential cloud app security best practices, executives can not only mitigate risks but also bolster compliance with ever-evolving regulations. With the stakes higher than ever, how can leaders fortify their strategies to withstand the relentless surge of cyber threats?
The current cybersecurity landscape is fraught with complexities that demand immediate attention. Organizations face a barrage of sophisticated attacks that threaten their very foundation. For C-suite executives, the implications are profound: a breach can lead to significant financial losses, reputational damage, and regulatory penalties. Therefore, understanding these challenges is crucial for effective leadership in today’s environment.
To address these pressing issues, Cyber Solutions offers a comprehensive approach that empowers organizations to enhance their security posture. By implementing robust security measures and fostering a culture of cybersecurity awareness, leaders can navigate this tumultuous landscape with confidence. The time to act is now-ensuring that your organization is not just compliant but resilient against the evolving threats that lie ahead.
In the current digital landscape, the protection of online applications is not just important; it’s essential. Organizations are increasingly dependent on internet services for operational efficiency and scalability, making cybersecurity a top priority. C-suite leaders must recognize that security measures are intricately linked to protecting and ensuring the integrity of business operations. A breach can lead to staggering financial repercussions, with the potential loss of revenue, not to mention potential legal penalties and reputational harm.
As regulatory frameworks like GDPR and HIPAA evolve, compliance becomes critical. Alarmingly, half of organizations reported an increase in cyber threats. By prioritizing security measures and adopting strategies such as risk assessments, leaders can take proactive steps to thwart attacks, effectively reducing risks and bolstering customer trust. Implementing robust security protocols not only minimizes the attack surface but also aids organizations in meeting stringent compliance requirements, ensuring adherence to regulations.
Real-world incidents, such as the data breach that compromised data from over 165 prominent clients, underscore the urgent need for enhanced security practices. Looking ahead to 2026, organizations that proactively tackle online security challenges will be better equipped to navigate the complexities of modern IT environments and maintain stakeholder confidence.

To effectively secure cloud applications, C-suite leaders must prioritize security measures. With the increasing frequency of cyber threats, it’s crucial to adopt best practices that not only protect sensitive data but also enhance organizational resilience against attacks.
By embracing security best practices, organizations can significantly enhance their online protection stance and decrease the likelihood of successful cyberattacks.

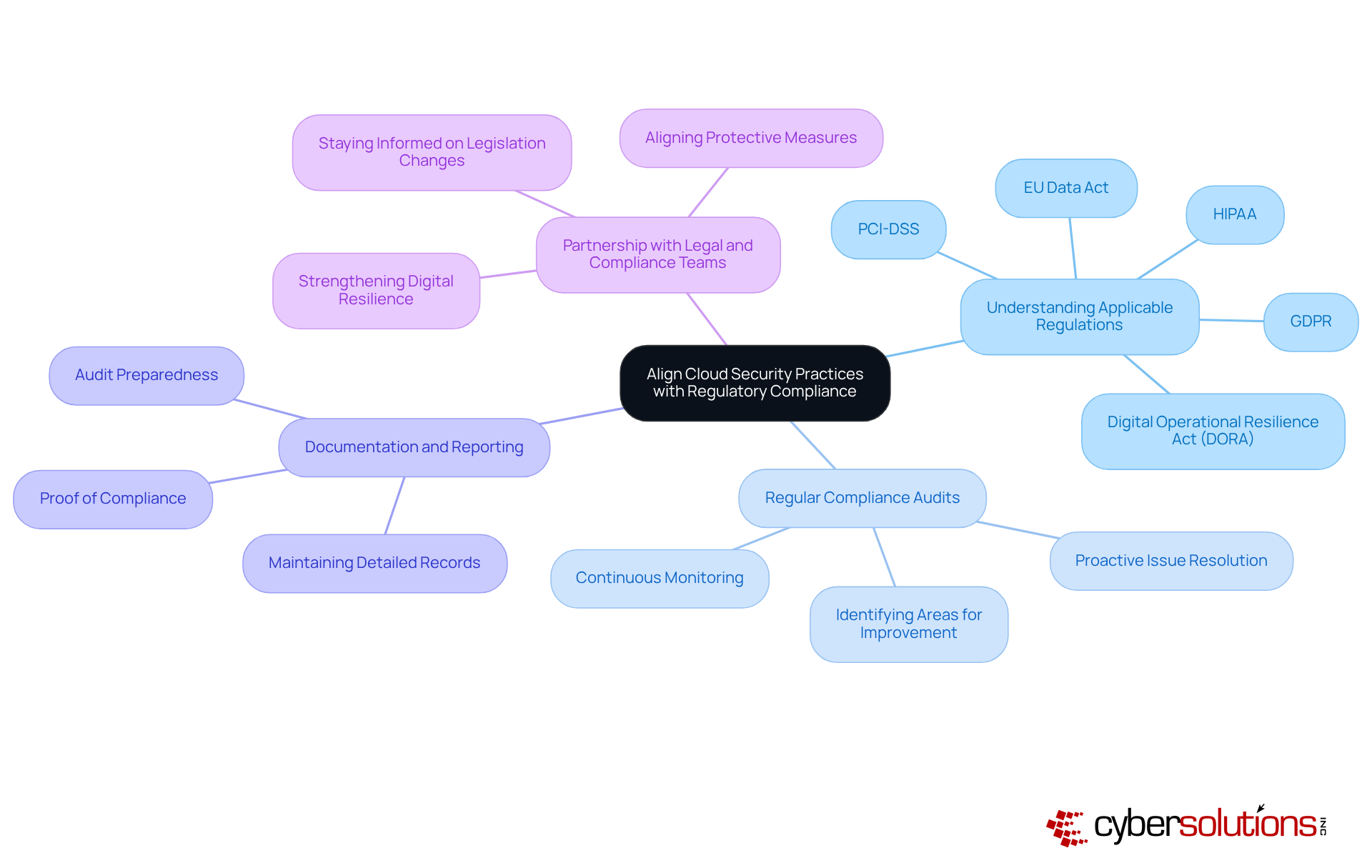
C-suite executives must prioritize aligning their online protection practices with relevant regulations to safeguard their companies. In today’s digital landscape, the stakes are high, and understanding the implications of cybersecurity is crucial.
Understanding Applicable Regulations: First, identify which regulations impact your organization, such as GDPR, HIPAA, or PCI DSS. Designing online security measures that meet these standards is essential; non-compliance can lead to significant penalties. Did you know that the typical expense of a security incident in a hybrid computing environment is around $3.61 million? Public computing incidents can cost 28.3% more, underscoring the urgency of compliance.
Next, conducting regular audits is vital. These assessments help gauge compliance with regulatory requirements and pinpoint areas for improvement. Organizations that implement best practices can proactively address issues before they escalate into major breaches, thereby following cloud app security best practices to ensure a secure cloud environment.
Keeping detailed records of protective practices and compliance efforts is essential. This documentation serves as proof of compliance during audits, which is increasingly significant as half of organizations reported a rise in compliance violations last year. Are your records up to date?
Finally, close cooperation with legal and compliance teams ensures that protective measures align with regulatory expectations. Staying informed about changes in legislation, such as the CCPA, is crucial for maintaining compliance and strengthening digital resilience for financial entities.
By incorporating compliance into online protection strategies, organizations can effectively reduce risks and evade costly penalties linked to non-compliance. This proactive approach not only enhances security but also safeguards sensitive information.
To effectively manage security risks, C-suite leaders must recognize the critical importance of establishing incident response protocols. In today’s rapidly evolving digital landscape, the stakes are higher than ever. Cyber threats are not just a possibility; they are a reality that organizations must confront head-on.
Continuous Monitoring: Deploying advanced tools for real-time observation of online environments is essential. This proactive strategy enables early detection of anomalies and potential threats, allowing organizations to take prompt action and significantly reduce risk exposure. In 2024, cyber incidents are expected to increase, impacting 73% of organizations. This statistic underscores the necessity for vigilant monitoring. Cyber Solutions offers tools that detect anomalies and potential vulnerabilities, ensuring that suspicious activities are halted before they escalate into serious threats.
Incident Response Plan: Developing a comprehensive incident response plan is crucial. This plan should clearly define roles and responsibilities, outline communication strategies, and establish recovery procedures to ensure a coordinated response. The significance of having an incident response team ready to act swiftly cannot be overstated. Case studies reveal that rapid deployment of such teams leads to improved protective measures and reduced damage.
Drills and Simulations: Implementing routine drills and simulations is vital for evaluating the effectiveness of incident response strategies. These exercises ensure that all team members are well-acquainted with their roles and can respond efficiently during an actual incident. Organizations that regularly review their incident response strategies can significantly reduce recovery time from breaches.
Post-Incident Evaluations: After any incident, conducting post-incident evaluations is essential for enhancing future response efforts. This practice not only improves an organization’s preparedness but also fosters a culture of ongoing enhancement in protocols. For instance, entities with structured response plans and specialized expertise often recover ahead of schedule while simultaneously strengthening their security measures against future threats.
By instituting these protocols in line with best practices, organizations can bolster their resilience against cyber threats and ensure a swift, effective response to incidents, thereby minimizing potential damage. The time to act is now—don’t wait for a breach to highlight the gaps in your security strategy.

C-suite leaders must understand that effective cloud application security is no longer optional; it’s a critical necessity for safeguarding sensitive data and maintaining the integrity of business operations. As organizations increasingly rely on cloud services, adopting best practices in cybersecurity is essential to prevent costly breaches and ensure compliance with evolving regulations.
To enhance cloud app security, executives should implement several key strategies:
Each of these practices plays a vital role in minimizing vulnerabilities and ensuring that organizations can defend against the rising tide of cyber threats. Moreover, aligning security measures with regulatory compliance not only mitigates risks but also strengthens operational resilience.
The importance of prioritizing cloud app security cannot be overstated. As cyber threats continue to evolve, leaders must take proactive measures to protect their organizations. By embracing the outlined best practices and fostering a culture of continuous improvement, businesses can safeguard their assets and build trust with stakeholders. The time to act is now-investing in cloud security is an investment in the future stability and success of the organization.
Why is cloud application security important?
Cloud application security is essential because organizations rely heavily on internet services for operational efficiency and scalability. Protecting online applications helps safeguard sensitive data and ensures the integrity of business operations.
What are the financial consequences of a data breach?
The average cost of a data breach exceeds $4.4 million globally. In addition to financial losses, organizations may face legal penalties and reputational damage.
How do regulatory frameworks affect cloud application security?
Evolving regulatory frameworks like GDPR and HIPAA make compliance non-negotiable. Organizations must prioritize cloud app security to avoid compliance violations, which have reportedly increased for half of organizations in the past year.
What strategies can organizations adopt to enhance cloud app security?
Organizations can adopt strategies such as application allowlisting, which helps to thwart malware and unauthorized software, reducing risks and enhancing customer trust.
How does application allowlisting contribute to compliance?
Application allowlisting minimizes the attack surface and helps organizations meet stringent compliance requirements, ensuring adherence to data protection protocols like HIPAA and GDPR.
Can you provide an example of a security incident that highlights the need for cloud app security?
The Snowflake hacking campaign is an example where data from over 165 prominent clients was compromised, emphasizing the urgent need for robust protective measures in cloud application security.
What should organizations focus on to prepare for future security challenges?
Organizations should proactively tackle online security challenges to navigate the complexities of modern IT environments and maintain stakeholder confidence as they look ahead to 2026.