
In today’s fast-paced digital landscape, the distinction between Managed Service Providers (MSPs) and Managed Security Service Providers (MSSPs) is more critical than ever for businesses. With cyber threats escalating at an alarming rate, understanding the unique roles of these service providers is essential for safeguarding assets and ensuring operational continuity.
How can organizations effectively assess their needs to choose the right partner for their IT and cybersecurity requirements? This article explores the nuances of MSP and MSSP services, providing insights that empower organizations to make informed decisions in a complex environment.
In the IT ecosystem, MSP or MSSP play crucial yet distinct roles. In today’s digital landscape, services like network management, data backup, and monitoring are essential, ensuring that systems run smoothly and efficiently. This is critical, as downtime can cost up to $9,000 per minute. On the other hand, MSSPs, or Managed Security Service Providers, specialize in cybersecurity, providing services such as threat detection and incident response. With these capabilities, businesses can enhance their security posture. By understanding these differences, businesses can align their needs with the right service provider, ensuring tailored support and robust protection against evolving threats.

Selecting between an MSP or MSSP is crucial for safeguarding your organization’s assets. Cybersecurity is not just an option; it’s a necessity. Begin by identifying your critical assets and sensitive data that require protection. The potential impact on business operations can be staggering. In 2025, the average cost of a data breach soared to $10.22 million, underscoring the urgent need for cybersecurity measures.
Next, evaluate your existing security protocols to uncover any vulnerabilities. Did you know that 60% of all breaches in 2025 involved human elements such as errors and social engineering? This statistic highlights the importance of employee training. Additionally, consider the regulations relevant to your sector. For instance, healthcare entities must adhere to HIPAA, while those in finance must comply with PCI DSS. Managed security services can be particularly advantageous, offering businesses end-to-end solutions to meet these regulatory requirements, including continuous monitoring, proactive risk assessments, and tailored remediation strategies.
Conducting a thorough evaluation of your security requirements will clarify whether your organization needs the extensive IT support provided by an MSP or MSSP. Organizations that have implemented security frameworks have reported significant advantages in breach response, demonstrating the value of customized protection strategies. By understanding your unique operational landscape and security needs, you can make an informed decision that aligns with your business objectives.

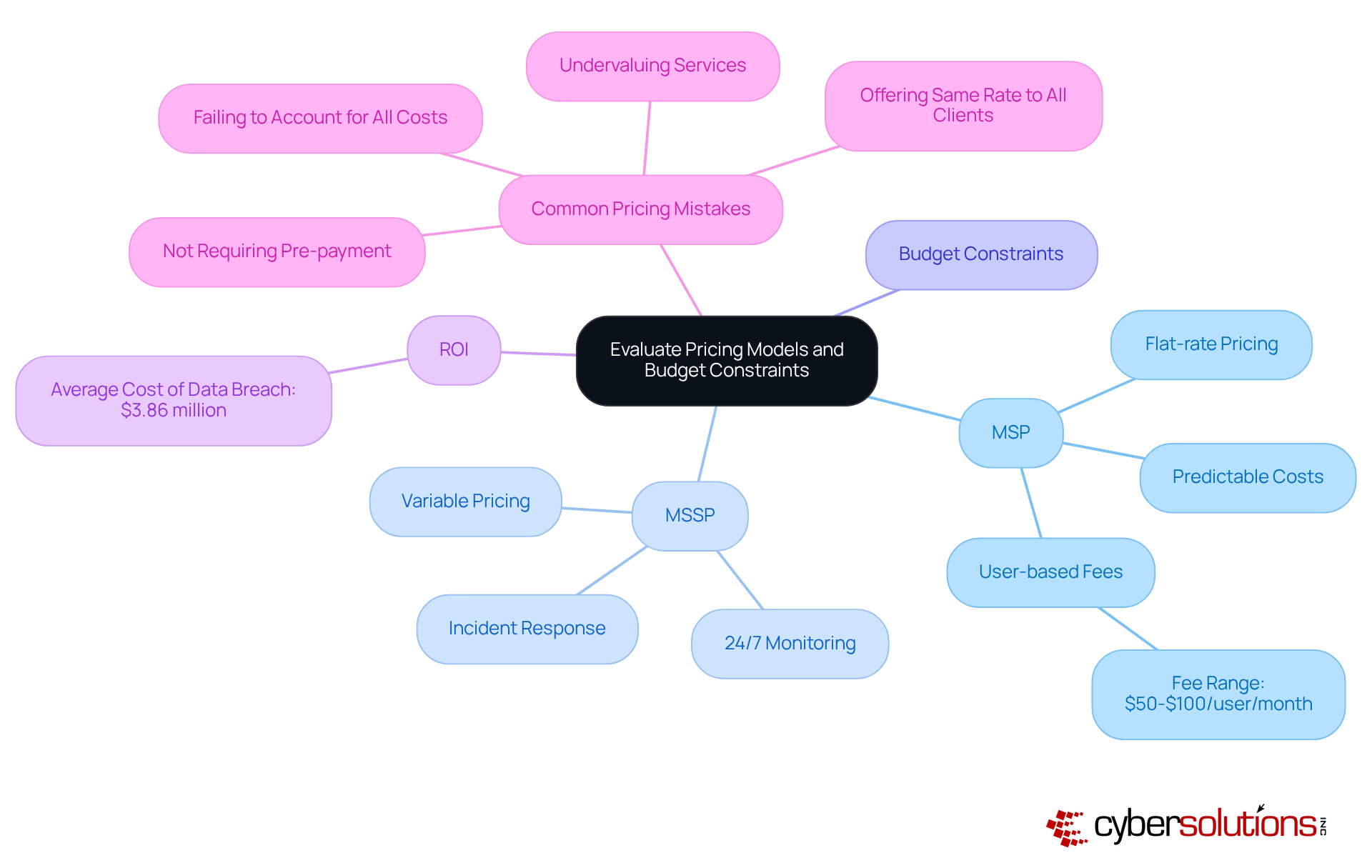
Choosing between an MSP or MSSP is a critical decision that demands a thorough evaluation and analysis. In today’s landscape, where threats are ever-evolving, organizations must prioritize their security strategies. MSPs, such as Cyber Solutions, typically offer managed services, often employing a flat-rate model that simplifies budgeting and eliminates unexpected IT expenses, making them a reliable choice for businesses looking for MSP or MSSP solutions. This model encompasses everything from email licenses to advanced cybersecurity services, allowing organizations to forecast IT expenses with greater accuracy. Monthly costs generally range from USD $50 to $100 per user per month, providing peace of mind in one comprehensive package. Conversely, the pricing of MSPs or MSSPs may present more variability due to the specialized nature of their services, which often include comprehensive security assessments.
Organizations must carefully assess their security needs while considering the potential return on investment (ROI) associated with each option. Investing in cybersecurity measures can significantly mitigate the risks of data breaches, which can far exceed the costs of implementing robust protective solutions. Analysts indicate that the average financial consequence of a data breach hovers around $3.86 million, underscoring the importance of prioritizing investment in cybersecurity protection. By reducing the frequency of emergencies, proactive measures can lead to fewer ransomware incidents and data loss situations, further emphasizing the necessity of these investments.
By examining the pricing structures and aligning them with their financial resources, companies can make informed choices that not only meet their operational needs but also enhance their security posture. This strategic evaluation is essential for navigating the complexities of modern IT environments and ensuring long-term success. Additionally, C-suite leaders should remain vigilant about common pricing mistakes made by MSPs, such as undervaluing services and failing to account for all costs, to avoid missteps in their decision-making process. Cyber Solutions’ commitment to a flat-rate pricing structure and rapid incident response strategies exemplifies how organizations can effectively bolster their cybersecurity while maintaining budgetary control.
Organizations must critically assess their in-house capabilities and staffing needs when deciding on an MSP or MSSP. With 61% of entities reporting a skills gap, expertise is essential. Do they possess the expertise needed to manage cybersecurity effectively?
Consider the complexity of your IT environment and the potential risks. If your organization lacks the resources or expertise to manage cybersecurity internally, outsourcing may be the most sensible option. Conversely, if you have a proficient IT team that can handle general IT tasks but requires specialized support, an MSP or MSSP may suffice.
This evaluation ensures that your organization is adequately equipped to address its IT and security challenges, ultimately enhancing protection and compliance. By making informed decisions, you can strengthen and maintain a robust security framework.

Choosing the right service provider - be it a Managed Service Provider (MSP) or a Managed Security Service Provider (MSSP) - is a pivotal decision that can significantly impact a business's operational efficiency and security posture. In today’s landscape, where cyber threats are increasingly sophisticated, understanding the distinct roles of MSPs and MSSPs is essential for aligning organizational needs with the appropriate services. While MSPs focus on general IT support to ensure smooth operations, MSSPs specialize in cybersecurity, addressing the critical need for robust protection against evolving threats.
Key insights emphasize the importance of assessing business needs, security requirements, and in-house capabilities. Organizations must evaluate their current security measures, identify vulnerabilities, and consider compliance obligations. This evaluation helps determine whether the comprehensive support of an MSP or the specialized protection of an MSSP is necessary. Additionally, understanding pricing models and budget constraints plays a crucial role in making an informed decision. Proactive investments in cybersecurity can mitigate the staggering costs associated with data breaches.
Ultimately, the choice between an MSP and MSSP should be guided by a thorough evaluation of operational needs, security requirements, and financial resources. Businesses must prioritize their cybersecurity strategies to safeguard assets and ensure long-term success. By making informed decisions and investing in the right services, organizations can effectively navigate the complexities of modern IT environments and bolster their defenses against potential cyber threats.
What does MSP stand for and what is its primary role?
MSP stands for Managed Service Provider. Its primary role is to deliver essential IT services such as network management, data backup, and help desk support, ensuring that systems run smoothly and efficiently.
What does MSSP stand for and how does it differ from MSP?
MSSP stands for Managed Security Service Provider. Unlike MSPs, MSSPs specialize in cybersecurity, providing services such as threat detection, incident response, and compliance management.
Why is cybersecurity considered a necessity in today's digital landscape?
Cybersecurity is considered a necessity because of the increasing frequency and sophistication of cyberattacks. With 43% of all cyberattacks targeting small enterprises, organizations must prioritize safety and regulatory compliance.
What are the potential costs associated with downtime for businesses?
Downtime can cost businesses up to $9,000 per minute, making operational continuity vital for maintaining productivity and revenue.
How can businesses benefit from understanding the differences between MSPs and MSSPs?
By understanding the differences, businesses can align their needs with the right service provider, ensuring tailored support and robust protection against evolving threats.