Introduction
In an era where cyber threats loom larger than ever, the healthcare sector finds itself particularly vulnerable, with a staggering 92% of organizations reporting cyberattacks in the past year. The importance of selecting the right cybersecurity service provider cannot be overstated; it is a critical step in safeguarding sensitive patient data and maintaining trust. This guide delves into the essential criteria for evaluating potential partners, from assessing their expertise and industry experience to understanding pricing models and client testimonials.
How can organizations navigate this complex landscape to ensure they choose a provider that not only meets their needs but also fortifies their defenses against an ever-evolving threat landscape? As the stakes rise, the need for informed decision-making becomes paramount.
Identify Your Organization's Cybersecurity Needs
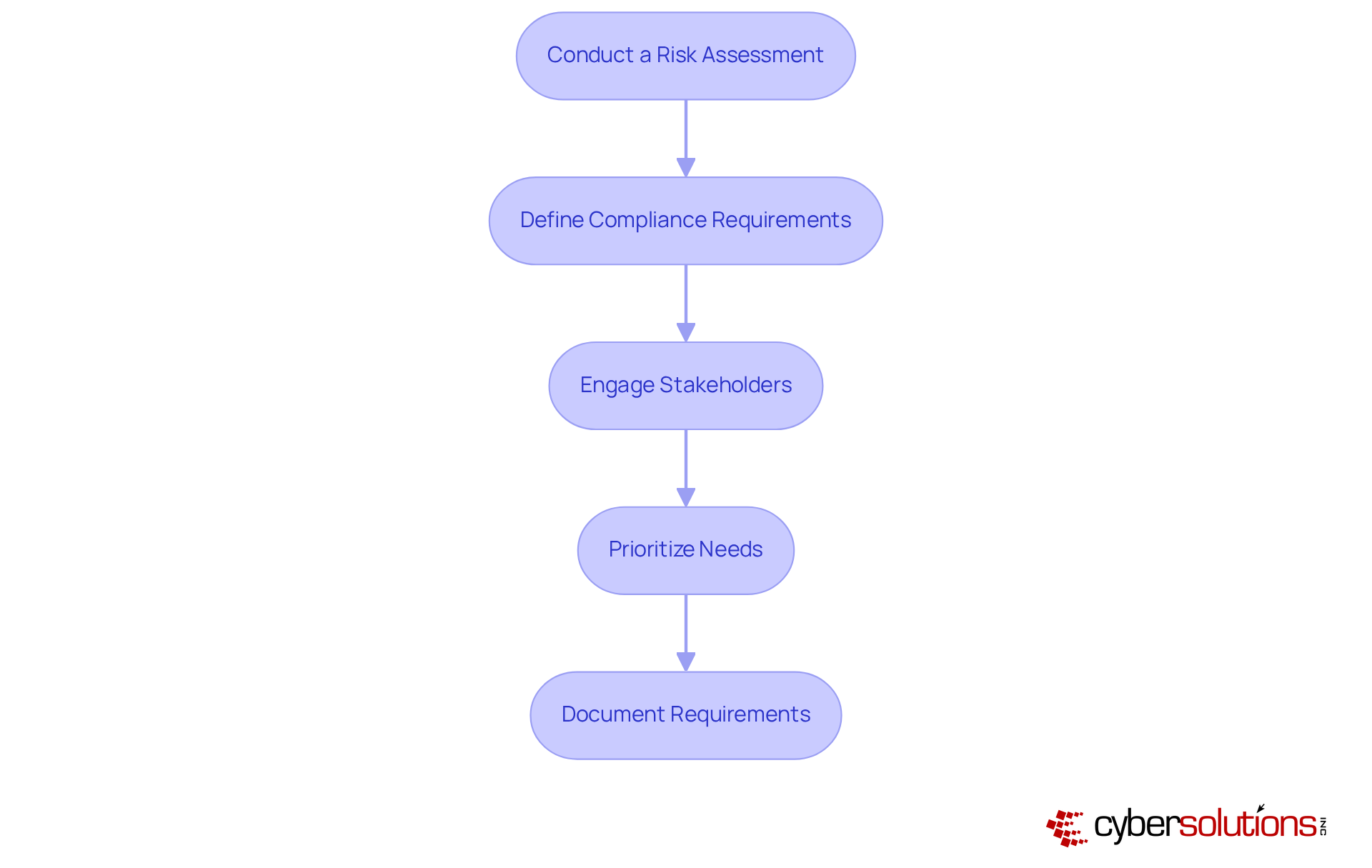
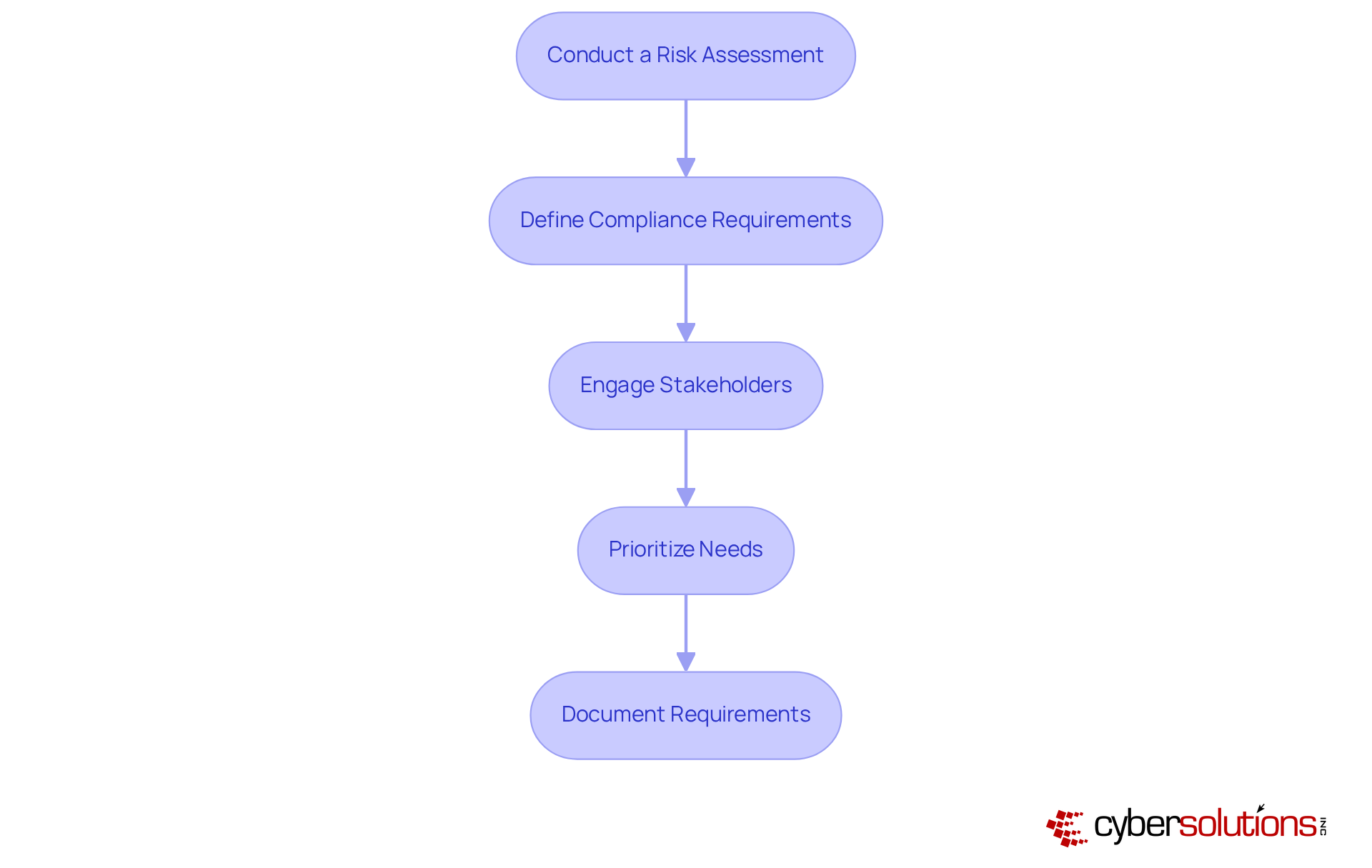
In today's digital landscape, the importance of cybersecurity in healthcare cannot be overstated. To effectively identify your organization's needs, follow these essential steps:
- Assessment: Begin by evaluating your current IT infrastructure to pinpoint vulnerabilities and potential threats. This assessment should take into account data sensitivity, regulatory requirements, and any previous incidents that may have occurred.
- Regulations: Clearly determine which regulations pertain to your entity, such as HIPAA, PCI DSS, or GDPR. Grasping these compliance requirements is crucial for implementing the necessary security measures to satisfy them. For instance, entities often implement specific protocols to safeguard patient data under HIPAA and ensure data protection under GDPR.
- Stakeholders: Involve key stakeholders from various departments, including IT, finance, and operations. Their insights will offer a thorough view of the organization's security issues and needs, ensuring that all perspectives are taken into account.
- Prioritize Needs: After completing the evaluation, prioritize your security needs. Focus on critical areas such as threat detection, incident response, and employee training, which are vital for maintaining a robust security posture.
- Documentation: Create a detailed document outlining your information security needs. This document will act as a valuable reference when selecting a provider, ensuring that your entity's specific requirements are met.
As we look ahead to 2025, a considerable portion of entities acknowledges the importance of performing assessments, emphasizing the increasing awareness of weaknesses in the online environment. Cybersecurity experts stress that identifying these vulnerabilities is crucial for developing effective strategies to mitigate risks and enhance overall security. By following these steps, organizations can better prepare themselves against the increasing threat of cyberattacks, which disrupted patient care in 70% of healthcare organizations last year.
Evaluate Provider Expertise and Experience
In today's digital landscape, the importance of cybersecurity cannot be overstated. To effectively assess the expertise and experience of potential providers, it is important to consider several key factors that are critical in navigating the unique challenges faced by organizations.
- Check Certifications: Start by looking for certifications such as CISSP, CISM, or CompTIA Security+. These credentials signify a commitment to best practices and a recognized level of expertise in cybersecurity, ensuring that the provider is well-equipped to handle sensitive information.
- Review Industry Experience: Next, assess the supplier's experience specifically within the healthcare sector. Given the heightened susceptibility of healthcare data to breaches, entities with a demonstrated history in this field will possess the skills necessary to manage pertinent regulations and tackle sector-specific challenges effectively.
- Ask About Team Qualifications: Inquire about the qualifications of the team members who will be managing your account. Their expertise should align with your security needs, particularly in understanding the unique regulations, such as HIPAA and GDPR, which are critical for maintaining patient trust and regulatory adherence.
- Evaluate Past Performance: Request case studies or examples of previous work that showcase the provider's capability to manage similar challenges. Look for measurable outcomes, such as security improvements or compliance achievements, to gauge their effectiveness and reliability in real-world scenarios.
- Evaluate Proactive Security Measures: Additionally, ask about the vendor's use of proactive security measures as part of their digital security strategy. This proactive approach not only prevents unauthorized applications from executing but also helps ensure compliance with stringent regulations. Furthermore, inquire about their continuous monitoring practices, which are essential for safeguarding against ransomware and phishing attacks.
- Conduct Interviews: Finally, arrange discussions with potential partners to explore their services and how they intend to customize their offerings to address your unique requirements. Engaging in direct conversations can provide valuable insights into their approach and commitment to client success.
By concentrating on these aspects, organizations can make informed choices when selecting a cybersecurity service provider, ensuring that they choose a partner capable of protecting their sensitive information and upholding compliance in an increasingly regulated environment.

Compare Services and Pricing Models
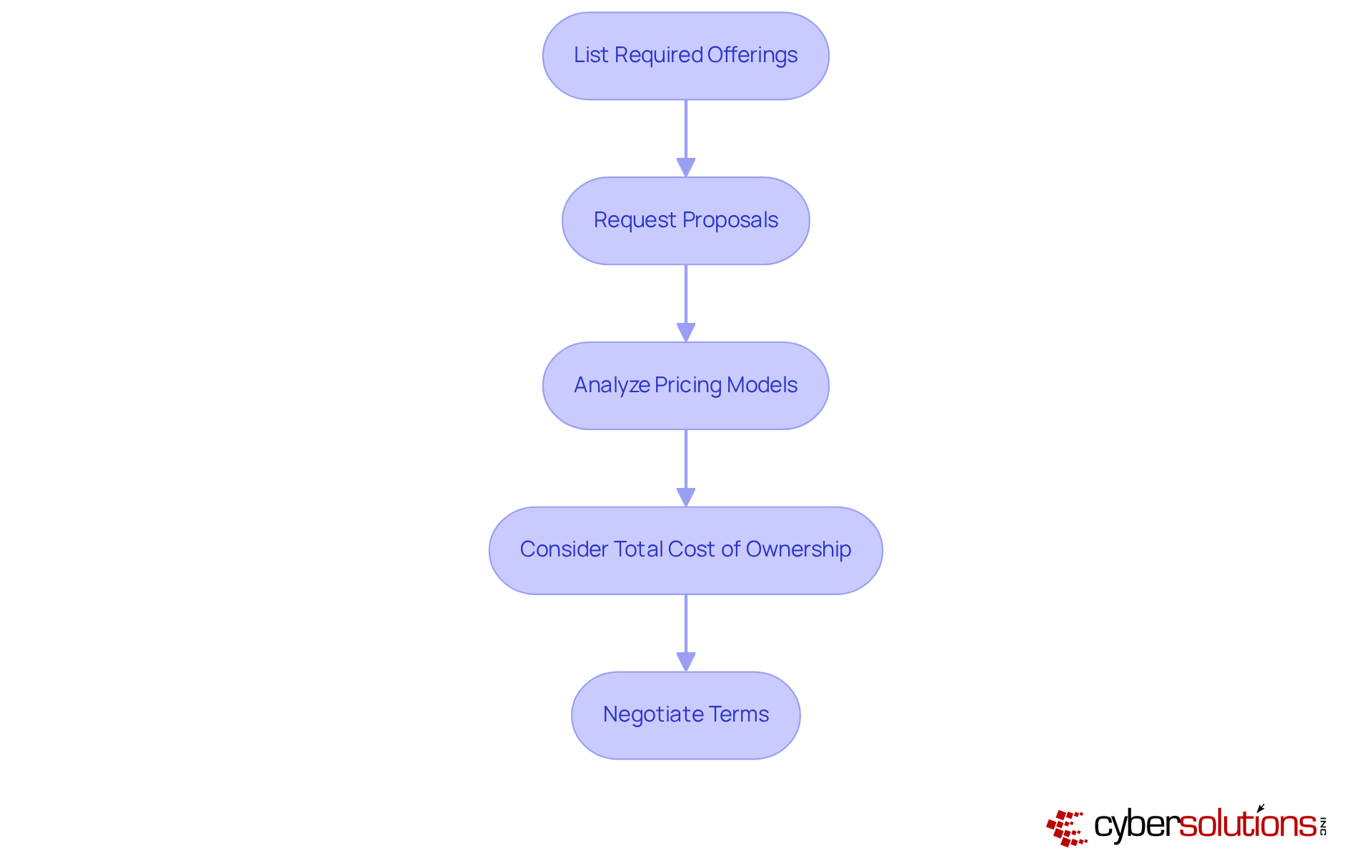
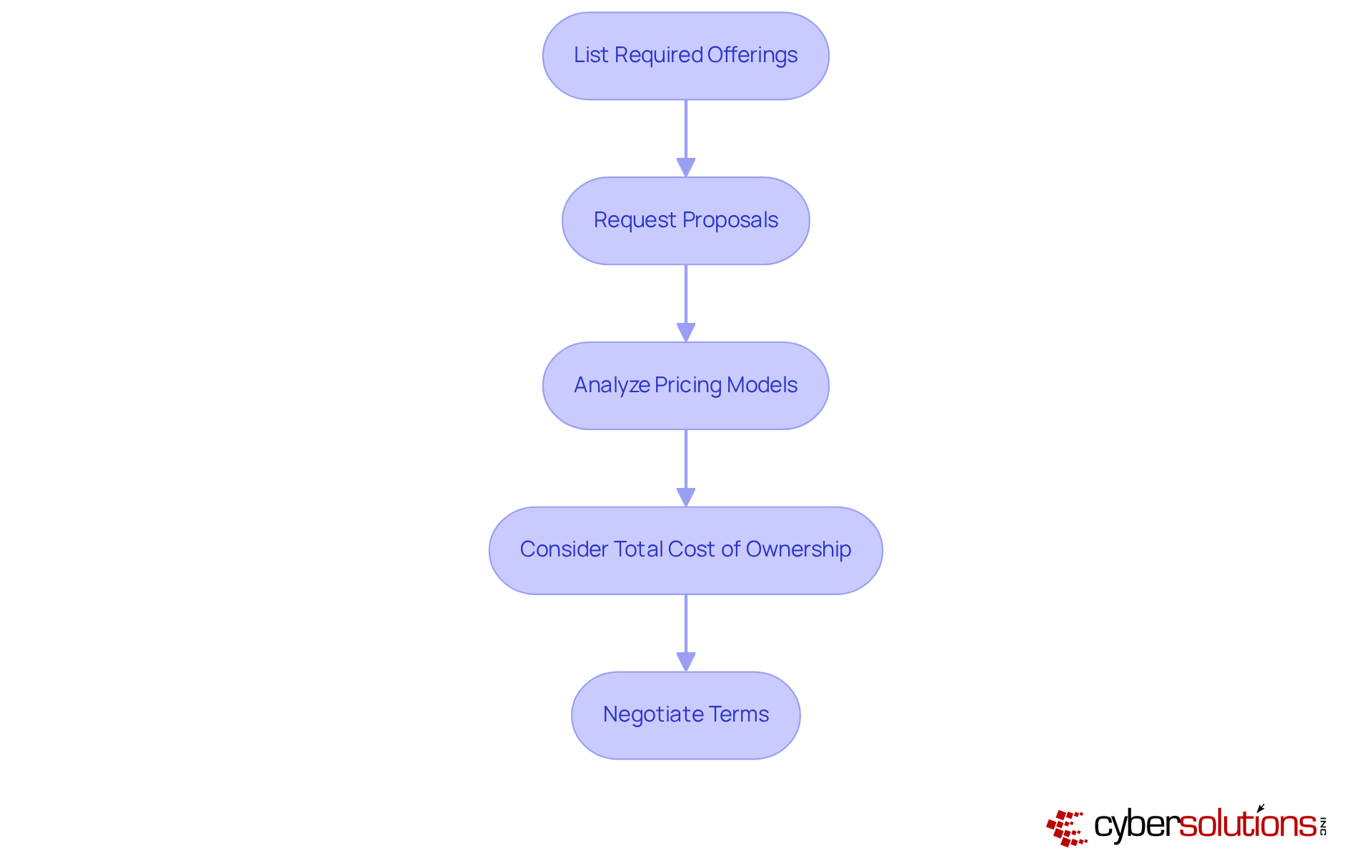
In the ever-evolving landscape of healthcare, the importance of cybersecurity cannot be overstated. With 92% of organizations experiencing breaches in the past year, selecting the right service provider is crucial. Here are key steps to guide your decision-making process:
- List Required Offerings: Begin by identifying and creating a comprehensive list of essential services tailored to your needs. This should include threat detection, incident response, risk assessment, and compliance support. Prioritizing these offerings is vital to safeguarding your organization.
- Request proposals by engaging with multiple providers and asking for detailed proposals. These proposals should clearly outline their offerings, pricing structures, and any additional fees that may apply. Understanding the market through this step ensures you receive competitive options.
- Analyze Pricing Models: Familiarize yourself with the various pricing models available, such as flat-rate, tiered, and per-device pricing. Each model presents its advantages; for instance, flat-rate pricing simplifies budgeting, while tiered pricing may offer flexibility based on your organization’s specific needs. Assess which model aligns best with your budget and support requirements.
- Consider Total Cost of Ownership: Look beyond initial costs to evaluate the total cost of ownership (TCO). This assessment should include potential hidden fees, ongoing maintenance costs, and the overall value of the services provided. Understanding TCO is essential for making informed decisions, particularly in a sector where the average cost of a data breach can soar to $9.8 million.
- Negotiate Terms: Don’t hesitate to discuss terms and pricing with potential suppliers. Many providers are willing to adjust their offerings to fit your budgetary constraints, potentially leading to more favorable agreements. Given the rising expenses associated with digital security, effective negotiation can significantly impact your organization’s financial health.
Review Client Testimonials and Case Studies
To effectively evaluate and when selecting a cybersecurity service provider, it is crucial to adopt a systematic approach:
- Gather Testimonials: Request testimonials directly from the source and seek reviews on independent platforms. Focus on feedback regarding service quality, responsiveness, and overall satisfaction to assess the reliability of the supplier.
- Analyze Case Studies: Review case studies that illustrate how the supplier has successfully tackled cybersecurity challenges in various organizations. Look for metrics, which can underscore the effectiveness of the service. For instance, the rapid response to a recent ransomware attack involved the immediate mobilization of a specialized incident response team within 24 hours, enabling real-time assessments and minimizing further spread of the threat. This is vital; effective incident response can dramatically lower breach costs.
- Contact References: If feasible, reach out to references provided by the supplier to inquire about their experiences and the results achieved. This direct feedback can yield valuable insights into the supplier's performance.
- Evaluate Consistency: Seek consistency in feedback across multiple sources. A supplier with consistently favorable reviews is more likely to deliver dependable services, as evidenced by clients where entities reported a 30% enhancement in security posture after collaborating with the supplier.
- Consider Industry Relevance: Ensure that the testimonials and case studies are relevant to your industry. Providers with experience in healthcare, like those specializing in medical cybersecurity, possess a deeper understanding of the specific regulatory requirements and security challenges faced by healthcare organizations. Cybersecurity analysts emphasize that examining past performance is essential for assessing a company’s ability to meet industry-specific demands, as it showcases their history in comparable settings. As noted by industry experts, "it is crucial to ensure they can meet the unique challenges of your sector."

Conclusion
Selecting the right cybersecurity service provider is not merely a choice; it is a critical decision that can define the security landscape of organizations, particularly in the healthcare sector where data protection is of utmost importance. Understanding and articulating specific cybersecurity needs empowers organizations to navigate the complexities of selecting a provider that aligns with their unique requirements and regulatory obligations.
This article outlines essential steps in this decision-making process:
- Conducting thorough risk assessments
- Engaging stakeholders
- Evaluating provider expertise
- Comparing services and pricing models
- Reviewing client testimonials
Each step ensures that the selected provider possesses the necessary qualifications, industry experience, and a proven track record in addressing cybersecurity challenges specific to healthcare organizations.
The significance of making informed decisions when selecting a cybersecurity service provider cannot be overstated. Organizations must prioritize their unique security needs and approach potential partners equipped with a comprehensive understanding of the requirements to safeguard sensitive information. By doing so, they not only protect themselves against the rising tide of cyber threats but also contribute to the overall integrity and trustworthiness of the healthcare system. Investing time and resources into this selection process is essential for fostering a secure digital environment capable of withstanding the challenges of the modern landscape.
Frequently Asked Questions
Why is cybersecurity important in healthcare?
Cybersecurity is crucial in healthcare due to the sensitivity of patient data and the growing number of cyberattacks targeting healthcare organizations, which can disrupt patient care.
What is the first step in identifying an organization's cybersecurity needs?
The first step is to conduct a risk assessment to evaluate the current IT infrastructure, pinpoint vulnerabilities, and identify potential threats.
How should compliance requirements be determined?
Compliance requirements should be clearly defined by understanding which regulations apply to the organization, such as HIPAA, PCI-DSS, or GDPR, to implement necessary security measures.
Who should be involved in the cybersecurity needs assessment?
Key stakeholders from various departments, including IT, finance, and operations, should be engaged to provide a comprehensive view of the organization's security issues and needs.
What should organizations prioritize after assessing their cybersecurity needs?
Organizations should prioritize critical areas such as threat detection, incident response, and employee training to maintain a robust security posture.
Why is it important to document cybersecurity requirements?
Documenting cybersecurity requirements creates a detailed reference that helps assess potential service providers and ensures that the organization's specific needs are met.
What trend is noted regarding risk evaluations related to digital security?
A considerable portion of entities acknowledges the importance of performing risk evaluations related to digital security, highlighting an increased awareness of vulnerabilities in the online environment.
List of Sources
- Identify Your Organization's Cybersecurity Needs
- diligent.com (https://diligent.com/resources/blog/top-20-quotes-cyber-risk-virtual-summit)
- cybersecuritydive.com (https://cybersecuritydive.com/news/healthcare-cybersecurity-risks-report-fortified/753077)
- 38 Must-Know Healthcare Cybersecurity Stats (https://varonis.com/blog/healthcare-cybersecurity-statistics)
- Healthcare Cybersecurity Statistics 2024 (https://ispartnersllc.com/blog/healthcare-cybersecurity-statistics)
- 205 Cybersecurity Stats and Facts for 2026 (https://vikingcloud.com/blog/cybersecurity-statistics)
- Evaluate Provider Expertise and Experience
- 70 Cybersecurity Quotes Every Leader Should Know (https://deliberatedirections.com/cybersecurity-quotes)
- brightdefense.com (https://brightdefense.com/resources/cybersecurity-statistics)
- solutionsreview.com (https://solutionsreview.com/security-information-event-management/cybersecurity-awareness-month-quotes-from-industry-experts)
- 51 Powerful Cybersecurity Quotes to Protect Your Business (https://cyburanus.com/blog/51-powerful-cybersecurity-quotes)
- 38 Must-Know Healthcare Cybersecurity Stats (https://varonis.com/blog/healthcare-cybersecurity-statistics)
- Compare Services and Pricing Models
- 41 Cybersecurity Quotes to Protect Your Digital Life (https://acecloudhosting.com/blog/cybersecurity-quotes)
- 38 Must-Know Healthcare Cybersecurity Stats (https://varonis.com/blog/healthcare-cybersecurity-statistics)
- 25+ Best Cybersecurity Quotes (https://atera.com/blog/best-cybersecurity-quotes)
- Healthcare Cybersecurity Statistics 2024 (https://ispartnersllc.com/blog/healthcare-cybersecurity-statistics)
- Review Client Testimonials and Case Studies
- 25+ Best Cybersecurity Quotes (https://atera.com/blog/best-cybersecurity-quotes)
- 160 Cybersecurity Statistics: Updated Report 2026 (https://getastra.com/blog/security-audit/cyber-security-statistics)
- secureframe.com (https://secureframe.com/blog/data-breach-statistics)
- 205 Cybersecurity Stats and Facts for 2026 (https://vikingcloud.com/blog/cybersecurity-statistics)
- Key Cyber Security Statistics for 2026 (https://sentinelone.com/cybersecurity-101/cybersecurity/cyber-security-statistics)