
In today's world, where digital threats loom large and the stakes for business continuity have never been higher, the importance of Backup and Disaster Recovery (BDR) solutions stands out. These vital strategies not only safeguard critical data but also empower organizations to recover swiftly from disruptions, protecting their operational integrity and reputation. Yet, as companies face the complexities of modern threats, one pressing question arises: Are their current BDR strategies robust enough to tackle the unforeseen challenges of tomorrow?
As we delve deeper into this issue, it becomes clear that the landscape of cybersecurity is evolving rapidly. Organizations must recognize the unique challenges they face and understand that a proactive approach to BDR is essential. The implications of inadequate strategies can be severe, leading to data loss, operational downtime, and damage to reputation.
To effectively address these challenges, organizations must evaluate their BDR solutions critically. Are they equipped to handle the unexpected? By investing in comprehensive BDR strategies, businesses can not only protect their assets but also ensure resilience in the face of adversity. The time to act is now.
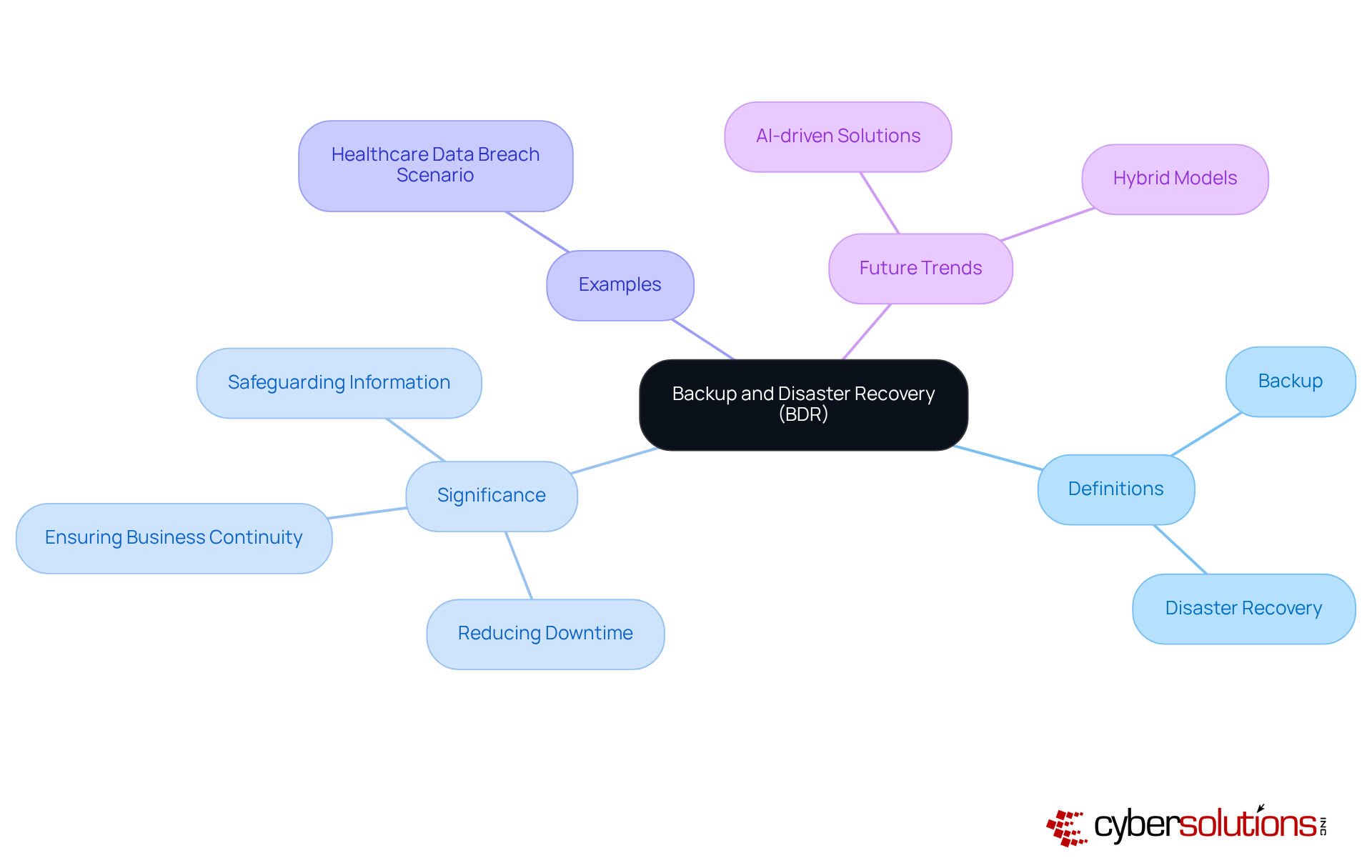
Backup and Disaster Recovery (BDR) are not just components of an IT strategy; they are essential pillars that uphold the very foundation of business resilience. In today’s digital landscape, where threats loom large, backup involves creating copies of critical information to ensure restoration in the face of loss, corruption, or disaster. On the other hand, Disaster Recovery encompasses the processes after a disruptive event, be it a cyberattack, natural disaster, or system failure.
The significance of BDR cannot be overstated. It plays a crucial role in reducing downtime, safeguarding sensitive information, and ensuring business continuity. Organizations that overlook BDR expose themselves to significant risks. For example, consider a healthcare entity that suffers a data breach without a robust BDR plan; the consequences could include hefty fines and a devastating loss of patient trust.
Thus, understanding and implementing effective backup and disaster recovery strategies is not merely a technical necessity; it is a business imperative. Regular testing of BDR plans is vital to ensure preparedness, as many organizations only discover backup failures during actual outages. As the threat landscape evolves, so too must disaster response strategies, adapting to new risks and technologies.
Looking ahead, by 2026, businesses will increasingly depend on AI-driven solutions and hybrid models to enhance their resilience. This evolution will empower organizations to swiftly recover while maintaining their operational integrity. Are you prepared to safeguard your organization against the unforeseen?
and RTO and RPO are critical metrics that define the acceptable limits for downtime and information loss in any organization. Understanding these concepts is essential for organizations aiming to prepare against disruptions.
RTO represents the maximum acceptable duration that an application, system, or process can remain unavailable following a disruption. In contrast, RPO specifies the maximum age of files that must be recovered from backup storage to resume normal operations. To effectively establish these metrics, organizations should conduct a business impact analysis (BIA). This assessment evaluates the potential impact of downtime on operations and revenue, allowing for informed decision-making.
For instance, consider a financial institution that determines its RTO must be less than one hour to prevent significant financial losses. Simultaneously, it may set its RPO to 15 minutes to ensure minimal data loss. By clearly defining RTO and RPO, businesses can prioritize their backup and disaster recovery (BDR) solutions and allocate resources efficiently. This ensures that restoration strategies meet operational needs and risk tolerance, ultimately enhancing organizational resilience.

Choosing the right BDR solutions is crucial for enhancing your disaster response strategy. With options like on-premise, cloud, and hybrid solutions, organizations face distinct advantages and challenges.
On-premise solutions require significant upfront investments and ongoing maintenance costs. Conversely, cloud solutions offer scalability and flexibility, allowing businesses to pay only for the resources they use, although they may raise concerns about security and compliance. Hybrid solutions effectively combine the strengths of both models, enabling organizations to keep essential information on-site while utilizing cloud resources.
For example, a manufacturing company might adopt a hybrid strategy to safeguard sensitive production data locally while leveraging cloud capabilities, ensuring both security and operational efficiency.
The market for BDR solutions in the cloud is set to experience substantial growth, with a compound annual growth rate (CAGR) of 10.2% from 2024 to 2032. This growth underscores the increasing recognition of BDR solutions for their ability to bolster business resilience. IT advisors emphasize that BDR solutions not only streamline restoration processes but also align with operational needs, making them a vital component of business continuity.
Alarmingly, only 32% of organizations that paid ransom successfully retrieved their data in 2024, highlighting the critical need for verified restores in disaster recovery. Additionally, the trend of automation is gaining traction, further enhancing the effectiveness of BDR strategies.
Ultimately, selecting BDR solutions should be guided by a thorough assessment of operational requirements, budget considerations, and risk management strategies. By making informed decisions, organizations can significantly improve their disaster response capabilities.

In today's healthcare landscape, the importance of BDR solutions cannot be overstated. Regular testing and updates are not just recommended; they are essential for ensuring effectiveness against ever-evolving threats. Organizations must conduct partial tests every quarter and full-scale testing annually. These simulations of disaster scenarios allow for a thorough assessment of BDR strategies, revealing weaknesses and providing opportunities for improvement.
Consider a healthcare entity that recently conducted a drill to evaluate its response to a cyber incident. This exercise highlighted critical areas where communication and recovery processes could be enhanced. Such incidents underscore the necessity for immediate action, specialized expertise, and a structured response plan when facing ransomware threats. Furthermore, it is vital for organizations to assess and revise their BDR plans at least once a year or whenever significant changes occur in the IT landscape—be it new applications, infrastructure modifications, or regulatory updates.
Documenting feedback and lessons learned after each drill is crucial for informing future improvements. By maintaining a plan that evolves with the organization, businesses can ensure they are prepared to respond effectively to disruptions, minimizing operational impact. Statistics reveal that approximately 58% of backups fail during recovery due to outdated technology or insufficient testing. This statistic highlights the importance of sustaining resilience and operational continuity.
By demonstrating a reliable and efficient response, organizations can cultivate strong partnerships with their service providers, ultimately enhancing their overall security posture. Are you ready to take the necessary steps to fortify your BDR plan and safeguard your organization against potential threats?

Backup and Disaster Recovery (BDR) solutions are not just technical components; they are essential for ensuring business resilience in a rapidly changing threat landscape. In today’s world, implementing robust BDR strategies is crucial for protecting critical data and maintaining operational continuity. This not only safeguards organizations from potential financial and reputational damage but also empowers them to thrive amidst uncertainty.
Key concepts such as Recovery Time Objective (RTO) and Recovery Point Objective (RPO) are vital in defining acceptable limits for downtime and data loss. Understanding these metrics allows organizations to tailor their BDR architecture - whether on-premise, cloud, or hybrid - to meet specific needs. Moreover, the importance of regular testing and updates to BDR plans cannot be overstated; proactive measures significantly enhance an organization’s preparedness against disruptions.
In conclusion, mastering Backup and Disaster Recovery solutions is imperative. As businesses confront escalating threats, prioritizing BDR strategies will not only mitigate risks but also enable organizations to navigate complexities with confidence. Now is the time to take action: evaluate, test, and refine your BDR plans to foster resilience and ensure long-term operational success.
What are Backup and Disaster Recovery (BDR)?
Backup and Disaster Recovery (BDR) are essential components of an IT strategy that ensure business resilience. Backup involves creating copies of critical information to restore it in case of loss, corruption, or disaster, while Disaster Recovery encompasses the strategies and processes to restore IT infrastructure and operations after a disruptive event.
Why is BDR important for organizations?
BDR is crucial for reducing downtime, safeguarding sensitive information, and ensuring business continuity. Organizations that neglect BDR risk significant financial losses, reputational damage, and regulatory penalties.
What are the potential consequences of not having a robust BDR plan?
Without a robust BDR plan, organizations may face substantial financial losses, reputational harm, and regulatory penalties. For example, a healthcare entity could incur hefty fines and lose patient trust after a data breach.
How often should BDR plans be tested?
Regular testing of BDR plans is vital to ensure preparedness, as many organizations only discover backup failures during actual outages.
How is the landscape of BDR expected to evolve by 2026?
By 2026, businesses are expected to increasingly rely on AI-driven solutions and hybrid models to enhance their BDR solutions, allowing them to navigate modern threats while maintaining operational integrity.
What types of disruptive events can BDR strategies address?
BDR strategies can address various disruptive events, including cyberattacks, natural disasters, and system failures.